While browsing the Internet, you may have heard the term “quantum computer” at one point or another. It all sounds so sciency! What they bring to the table is very simple: It’s something better than what we currently have or else we wouldn’t be working on bringing about this tech revolution.
But there’s one thing cryptographers have been asking themselves for a while: What use are encryption algorithms like RSA if quantum computers will be able to break them within seconds? Can they even do that? It’s a terrifying question that many people probably would rather not know the answer to.
How Encryption Currently Works

There are tons of encryption algorithms, each with their own quirky methods for working out how to best protect your data. If we were to spend time talking about how all of them work, we’d probably have to write a couple thousand pages of material.
The gist of it is that our current methods of encryption take your data and pass it through a series of mathematically-programmed “steps” to jumble it up in such a way that you can later “un-jumble” it with the right variables. These variables are known as “keys.”
Modern-day algorithms like RSA, SHA-512 and even elliptic curve cryptography function in much the same manner. They take a convoluted approach to concealing your data in such a way that normal computers would take millennia to break their algorithms.
But what about quantum computers?
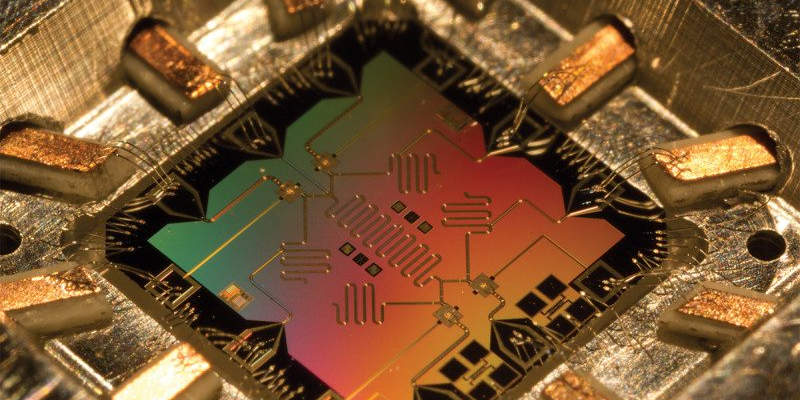
Why Quantum Computers Are So Scary
When you sit down and log on to Facebook or whatever you use on the Web, you probably take for granted the amount of technology and computing power that’s dedicated to protecting everything you’re doing. It really takes a mind-blowing amount of labor from extraordinarily expensive hardware to even begin to break the barrier that these services place between you and intruders. It’s why we’re not getting our accounts hacked, because someone broke the encryption. That only happens in movies. Most of the reasons why we end up the victims of hackers can be summed up as human stupidity, not the lack of integrity in our strongest encryption.
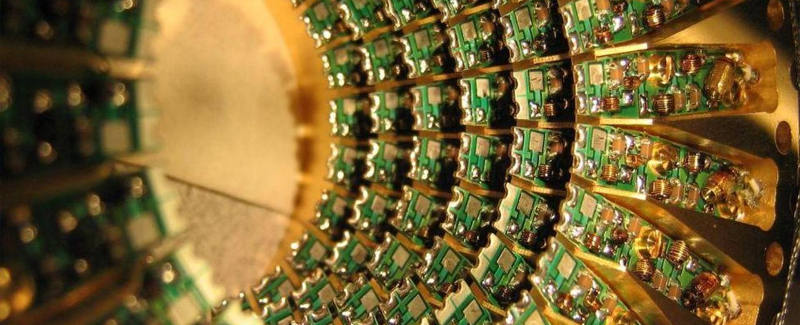
Quantum computers kind of turn all of this upside down. Because they can process information so quickly and do math like it’s no one’s business, they kind of make encryption a bit useless. In fact, Google has been hard at work on implementing a new type of cryptography in anticipation of eventual quantum computer attacks.
A quantum computer can theoretically solve RSA puzzles and anything using SSL encryption in a matter of seconds. This means that HTTPS is basically useless at this point if someone had a massive quantum rig and fired it up to snoop around on your traffic. They could do this in less time than it takes for you to take a sip of your coffee or pronounce the word “Mississippi.”
What We Can Do About It
There’s really nothing much you can do yourself to prevent the quantum “apocalypse” except for hoping that the mathematical difficulty of “solving” encryption keeps up the pace before these computers become commonplace items in everyone’s homes. If that doesn’t happen, then you might as well unplug yourself from the Internet. Every database in the world, every WiFi hotspot out there, and even your very own home could all become potential snake pits.
Fortunately, a lot of intelligent people have already begun working on a solution. For every uncharted territory we cross in technological advancement, we will always face problems like these. As mentioned earlier, Google is working on something called “ring learning with errors.” As unflattering as the name sounds, it’s complicated enough that it isn’t readily solvable by quantum computers but simple enough that ordinary computers can still use the algorithm to communicate.
The buck doesn’t stop here. Google is just one of the first companies to announce that it is working on a solution. There are very likely many other folks already working on quantum-computer-proof algorithms that will up the ante in the battle between cryptography and computing power.
Do you think that quantum computers will gain the upper hand? Or is there hope that new forms of encryption will save the day and our ordinary computers will be able to handle the processing requirements? Tell us what you think in a comment!