It’s old news, the US internet privacy rules preventing your ISPs from selling off your browsing data and history to advertisers have been repealed. Now your ISP can monetize your behavior online better. Just what can they monetize and how? That’s what we’ll find out from this article. Read on.
What can your ISP see?
Unencrypted websites give ISPs (i.e. Internet Service Providers) the most detailed pieces of data about their users. Unencrypted websites use Hypertext Transfer Protocol (HTTP) without a Secure Sockets Layer (SSL), leaving the connection unencrypted. Encrypted websites use Hypertext Transfer Protocol Secure (HTTPS) which works with an SSL. Your ISP sees data from unencrypted websites and some data from encrypted websites.

Data from unencrypted websites: ISPs see the full URLs (Universal Resource Locators) of all web pages visited by their users on unencrypted websites. The former counselor to Tom Wheeler, FCC Chairman, Gigi Sohn says that ISPs “have access to everything you do online.”
According to Sohn, ISPs “know every website you visit, how long and during what hours of the day you visit websites, your location, and what device you are using.” Of the top 50 health, news and shopping websites, more than 42 are unencrypted. That’s over 85% of these top 50 websites, including Target.com, WebMD, the Huffington Post, IKEA and more.
Data from encrypted websites: Half of the websites are using HTTPS to reduce the amount of information that ISPs access from their visitors. When visitors use encrypted sites, ISPs are not able to access their full URL and content from pages visited.

However, ISPs still know what site you’re visiting even if they don’t know what pages you used on that site. That knowledge is still useful to them. Knowing what websites you use helps them make educated guesses on what your interests might be, in estimating your age range, your internet usage habits, when you are online or offline and more.
A broadband privacy attorney, Dallas Harris, says that “The fact that you’re looking at a website can reveal when you’re home, when you’re not home” Harris contends that “The level of information that they can figure out is beyond what even most customers expect.”
ISPs are desperate to see and track your data
The repeal of ISP privacy rules in the US effectively opens the doors for creepy ISP data collection practices. It calls for caution that ISPs have a standing history of breaching user privacy. Let’s examine a few of these practices.
Snooping through your traffic and inserting ads: ISPs use your browsing history to inject and serve you ads. AT&T, Charter, and CMA have reportedly done this in the past. According to the Electronic Frontier Foundation, the FCC’s repeal of privacy rules officially grants ISPs the legal grounds to sell your traffic in this manner, going forward.
Selling your data to marketers: AdvertisingAge says that Consumer Insight 365, a service offered by SAP “ingests regularly updated data representing as many as 300 cellphone events per day for each of the 20 million to 25 million mobile subscribers.”

According to the AdvertisingAge report, “The service also combines data from telcos with other information, telling businesses whether shoppers are checking out competitor prices. It can tell them the age ranges and genders of people who visited a store location between 10 a.m. and noon, and link location and demographic data with shoppers’ web browsing history.”
SAP, as reported by AdvertisingAge, refused to disclose the carriers supplying them this data. Essentially, this means that ISPs are seeing, tracking and even selling off their users’ data on demographics, location and browsing history.
ISPs inject undetectable, indelible tracking cookies into your HTTP requests: ISPs like Verizon and AT&T have been reported to use “supercookies” to track their users. The EFF says that “Initially, there was no way for customers to turn this “feature” off. It didn’t matter if you were browsing in Incognito or Private Browsing mode, using a tracker-blocker, or had enabled Do-Not-Track: Verizon ignored all this and inserted a unique identifier into all your unencrypted outbound traffic anyway.”
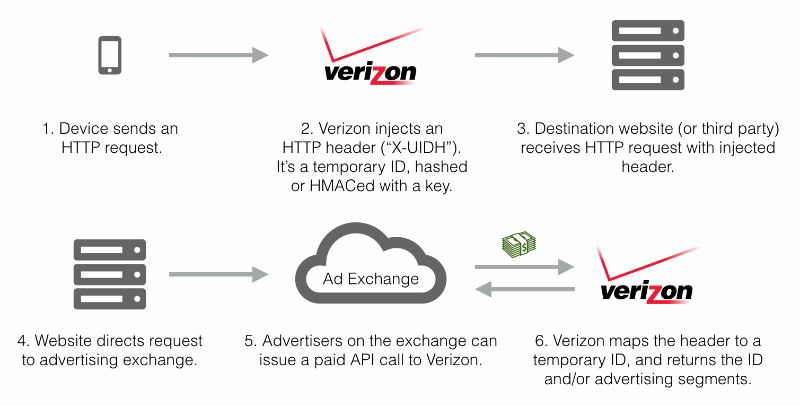
Supercookies or UIDH makes it possible for anyone (including advertisers) to track your web browsing. Advertisers could turn your cookies into “zoombie cookies” by using Verizon UIDH to resurrect them, even if you cleared them. FCC says Verizon kept the supercookies running for two years before updating its privacy policy to allow users turn off the feature if they so desired.

Search hijacking: According to EFF, in 2011, a number of ISPs were caught using a service by Paxfire to hijack their users’ search queries to Bing, Yahoo!, Google and other search engines. ISPs used this to drive traffic to specific sites while presumably earning some money from this practice.
Pre-installed software that logs app usage and URLs that you visit: Sprint, T-Mobile and AT&T were found to be logging their users’ URLs visited and the apps used. Using Carrier IQ, ISPs tracked your apps usage and websites visited. Trevor Eckhart of Electronic Frontier Foundation conducted research to reveal how the Carrier IQ worked.

Although Carrier IQ lead to a class action lawsuit in the past, the repeal of the FCC privacy rules would encourage (and even legalize) the use of such tracking software by ISPs.
How to stay safe online
Due to the overwhelming tracking technologies, information collection and usage by ISPs, it’s best to use Tor or VPN secured connections to access the internet. VPNs or virtual private networks effectively mask your identity, encrypt your data and significantly limit what information flow your ISPs get. Since the FCC granted ISPs freedom to use and sell your internet traffic data without your consent, using a VPN is probably a necessity now than ever.








