XDP (or Express Data Path) is a networking utility available in the Linux kernel. XDP is used in many popular companies to solve some serious networking issues they face while handling millions of requests per second. This is an MIT licensed open source program merged in the Linux kernel from version 4.8.
XDP is a performance and programmable network data packet processor. It comes into existence to mitigate some serious server-side issues like DDoS (Distributed Denial-of-Service) attacks or as a load balancer.
Also read: 5 Useful Tips When Compiling Your Own Linux Kernel
Need for XDP
The need for a performant networking data path is always a required feature for Linux servers. But the programmability of those data paths should also be there so that developers make something usable out of it. Although XDP has quite a steep learning path, due to the recent development of many tools and frameworks, writing XDP code is quite approachable nowadays.
The huge advantage of XDP is its speed. The primary functionality of XDP is that developers can build new functionality to filter out packages without modifying the kernel itself.
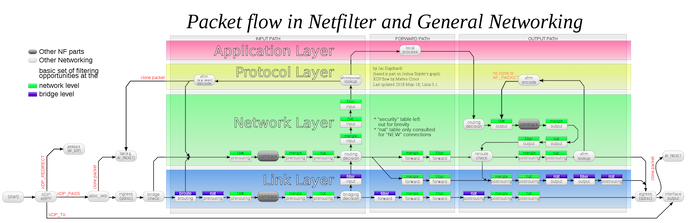
There are some scenarios when some package need not have to travel through the entire network stack to just decide either to forward or drop the packet. It should be done on the first layer of the networking stack by placing some filters. These filters should be programmed in such a way that they can easily recognize a malicious packet and drop it right at the beginning of the stack. This can save a lot of processing power and time.
With XDP, this filtration is possible right at the front of the networking stack.
Now using XDP, the developer can filter out any packets which may be sent by any hacker to make a DDoS attack. This can reduce much of the overhead in the normal kernel networking stack. This feature is recently demonstrated by Cloudflare in their DDoS protection demonstration.
Some notable feature of XDP is as follows :
- It doesn’t require any specialized hardware: XDP can run any hardware you throw at it. Yes, speed may be compromised if you don’t have the optimized device or its drivers, but for testing purposes, you don’t need any specialized hardware.
- It doesn’t require kernel bypass: XDP runs before the packet hit the kernel networking stack. A callback function is fired when a packet is received and XDP process it as fast as possible.
- It doesn’t replace the TCP/IP stack: XDP is present at the lowest level of the networking stack. When it passes the packet, then the packet enters the normal kernel networking stack which includes the TCP/IP stack.
- It works in conjunction with TCP/IP with all the BPF (Berkeley Packet Filter) features: XDP doesn’t replace anything. It even uses eBPF to process packets and give the developer an easier time writing code.
Also read: How to Build and Install a Custom Kernel on Ubuntu
Why XDP Is Very Fast
XDP is an eBPF-based programmable, high-performance network data path in the Linux kernel. The performance gain of XDP is because of the bare metal packet processing at the lowest level of the software stack. It means that the data packet coming from the network hit the XDP first before any other process of the kernel.
Therefore, engineers can program the XDP to optimize it for various use cases. From DDoS protection to the load balancer.
XDP is loaded directly on the networking stack. When a packet is received by the networking stack, it gets a callback and processes the packets as fast as possible. XDP can drop 26 million packets per second per core in commodity hardware.
The primary reason why XDP is very fast is, that the user is allowed to directly read or make changes to network packet data and take decisions on how to handle the packet at an earlier stage. This requires a very less process overhead and resulting better speed.
Connect Networking Stack With XDP
You can connect to networking with XDP by various means, but I am mentioning some popular methods here.
- Generic XDP: In this process, XDP is loaded in the kernel, but gets very little performance benefit. This is the easy way to run an XDP program without any support from the hardware.
- Native XDP: Native XDP is loaded by the networking driver itself. It requires the support from network card driver.
Also read: How to Fix the Kernel Data Inpage Error in Windows
Types of Operation XDP Performs
Some of the operations XDP can perform once a packet is received by the networking interface are:
- XDP_DROP: It drops the packets and doesn’t process them. Using an eBPF program to analyze the traffic pattern and can drop packets in real-time.
- XDP_PASS: It forwards the packets to the networking stack for further processing. It can modify the content of the packet before it happens.
- XDP_ABORTED: It drops the network data packet, leaving a tracepoint exception.
- XDP_TX: forward the packets to the same networking interface that receives them. The packets can be modified on unmodified.
- XDP_REDIRECT: Redirect the packet to another NIC (network interface controller).

XDP and eBPF
eBPF is the extended version of Berkeley Packet Filter. It is like an abstracted virtual machine running inside the Linux kernel. eBPF is used to run a user-defined program inside a sandbox environment in the Linux kernel. Generally, it is used to run networking and monitoring tools in Linux servers to ensure optimal performance.
XDP is a framework used to write very high-speed packet processing in BPF applications. To make it even faster, XDP runs BPF immediately after a packet is received by the networking stack.
XDP has a very steep learning curve. Therefore developers are making tools and frameworks to make it easy to program using eBPF. It makes it very easy to write code for processing very high-frequency network processing using XDP and eBPF. The core advantage of XDP is that it doesn’t require you to modify the kernel, which was a huge headache for the engineers.
But as people said, great power comes with great responsibility. As XDP runs eBPF as early as possible before packets are parsed by the kernel itself, eBPF programs have to do all the parsing themself and can’t rely on the kernel to do anything for them.
As a programmer, most of your time you are working with terminal. This is a guide to decorate your terminal prompt. Do check it out.
Also read: How to Downgrade the Kernel in Linux
Common Use Cases of XDP and eBPF
- DDoS attack: The primary use case of XDP is DDoS (Distributed Denial of Service) protection. During the DDoS attack, the attacker tries to use as many resources of the server as possible by not leaving any process for the end user. Using XDP as the very fast layer of the networking stack, there is no processing cost associated to drop a network data packet. After XDP filtering, the packet goes through all the other filtering methods that the Linux kernel provides.
- Load balancer: XDP is also used as a load balancer to handle a huge amount of traffic to the server. Including Facebook, many giant tech companies use this technology. Earlier, engineers use a dedicated server as a load balancer. Which is very hard to manage and has to perform very well to serve millions of customers. But imagine using the XDP layer as a load balancer with no central server, as a result, no single point of failure.
- Firewall: XDP with eBPF can be used to write various firewall rules to protect the system with very minimal overhead.
Also read: How to Use Rm Command in Linux
Frequently Asked Questions
What is BCC is eBPF?
BCC is built upon eBPF. It is a toolkit or framework for kernel tracing and manipulation programs that comes with a very useful command line interface. BCC help to write Kernal instruction in C. It also includes a wrapper around LLVM.
What is libBPF?
LibBPF is an alternate set of tools to make a BPF application. It is written in the C programming language.