If you have heard a young would-be hacker talking about penetration testing, chances are, you would inevitably hear what Kali Linux is. It is a Debian-based Linux distribution that aims to be a complete toolkit for security professionals.
Kali Linux includes a lot of penetration testing and security auditing tools by default. In that regard, Kali delivers, too. Many of the best open-source tools for conducting security tests are in here and ready to use.
Why Use Kali Linux?
One of the biggest selling points of Kali Linux is that it is a convenient all-in-one solution. For the most part, Kali doesn’t require you to maintain a Linux machine and collect your own software. All of the set-up work is out of the way, and you can fully focus on testing the system you’ve set out to audit.
Aside from that, Kali is also being developed and maintained by Offensive Security. They’re a well-known and trusted institution in cybersecurity. You can be confident that the tools that Kali Linux provides are both trustworthy and highly effective.
What Tools Are Available in Kali Linux?
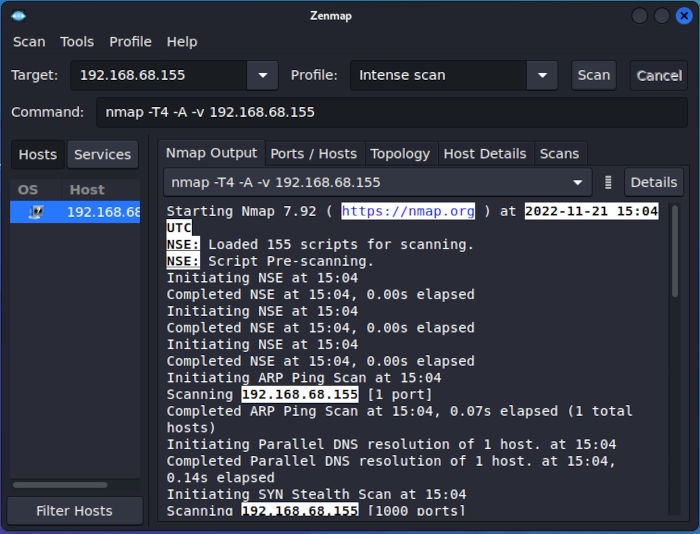
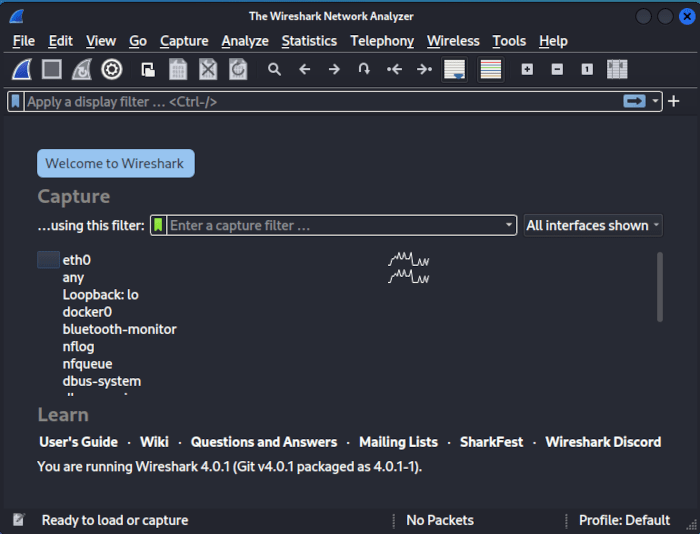
Kali Linux has many security tools. It has classic information-gathering tools, like NMap, Wireshark and dig.
Kali also has WiFi-centered tools like Aircrack-ng, Kismet, and Pixie.
For attacking passwords, there are tools like Hydra, Crunch, Hashcat, and John the Ripper.
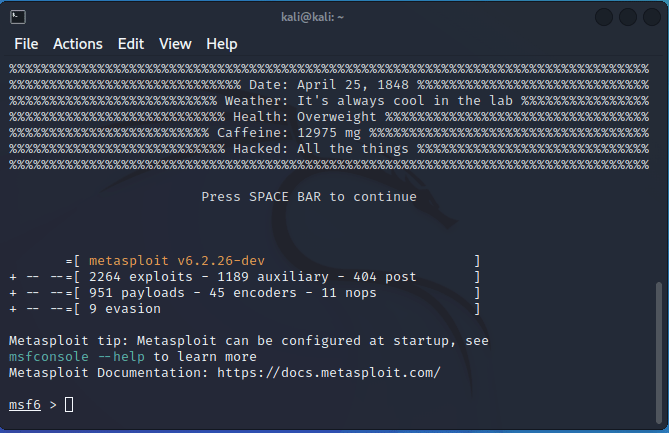
Then there are more complete suites of tools. For example, you can use the Metasploit Framework and Burp Suite out of the box.
That’s only a small percentage of the security tools available in Kali. It would take a long time to go through all of them, but you can clearly see that many of the more popular tools are represented.
Installing Kali Linux
Kali is a Linux distribution. Like any other, you can install it permanently on a hard drive or virtual machine. That works fine, but you don’t want to use Kali as a daily driver operating system. It’s purposely built for penetration testing, and that’s about all that you should use it for.
Note: you can also install Kali Linux on your Android phone.
Kali’s System Requirements
Before you can install Kali Linux, have the following resources available:
- Ample amount of disk space in your machine. In most cases, Kali should work well on a 32 GB flash disk.
- 64-bit processor and 2 to 4 GB of onboard memory, as Kali Linux uses a number of resource-intensive programs in its toolkit.
- Your machine needs to have the ability to either do virtualization or external media booting.
It is important to note that Kali works best as a live distribution. You can either burn it to a USB driver or run it off of a virtual machine. You don’t need to install anything on Kali or save any files, so spinning it up on the occasion where you need to test a system is great. It also affords the flexibility to get a Kali machine running anywhere on whichever network you’re looking to test.
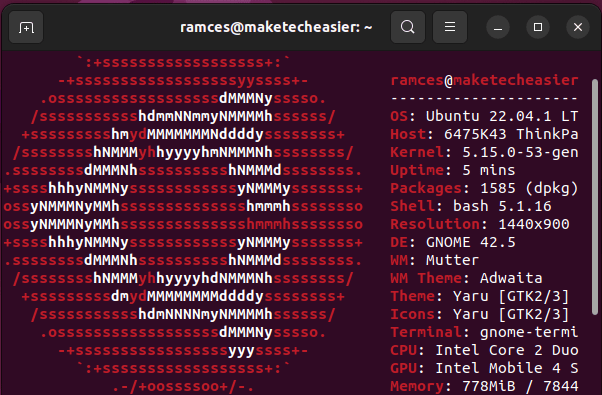
This article focuses on installing Kali Linux on VirtualBox as a live system in Ubuntu 22.04 LTS.
Installing Kali Linux on VirtualBox
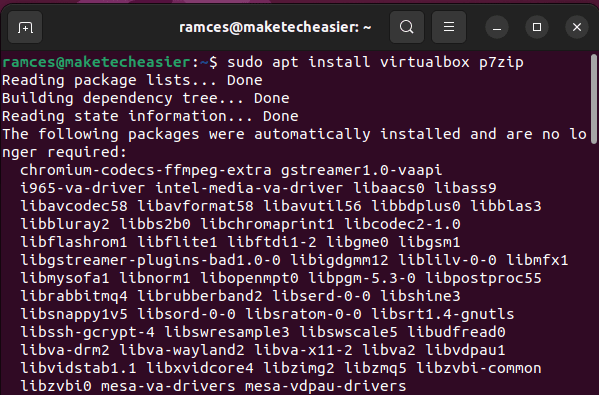
To install Kali Linux, obtain the virtualization client you want to use. In this case, I am installing VirtualBox:
sudo apt install virtualbox p7zip
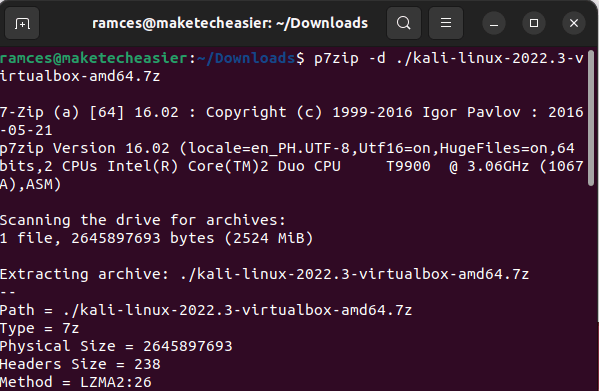
Obtain a copy of Kali Linux from its official website. For example, you can run the following command to download it from the terminal:
wget https://kali.download/virtual-images/kali-2022.3/kali-linux-2022.3-virtualbox-amd64.7z p7zip -d ./kali-linux-2022.3-virtualbox-amd64.7z
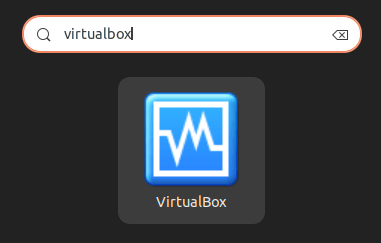
Install Kali Linux as a virtual machine by pressing Win, then typing “virtualbox.”
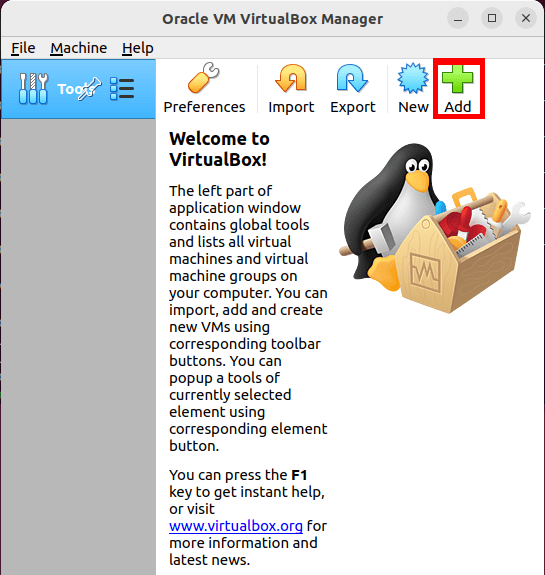
Once VirtualBox is up and running, import the Kali Linux virtual machine to the client by either clicking “Add” or pressing Ctrl + A.
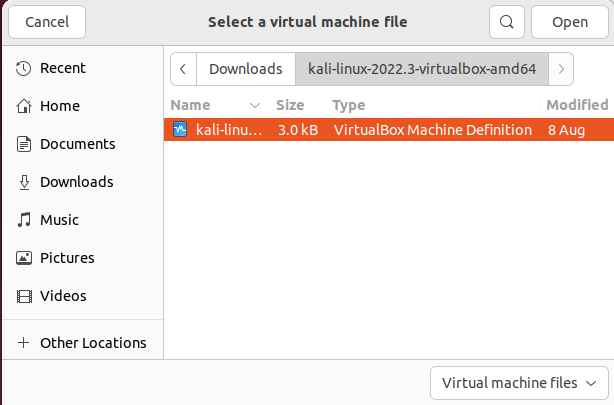
VirtualBox will open a small file browser where you can look for the virtual machine definition for Kali. In my case, I am saving this file to my Downloads folder.
Using Kali Linux
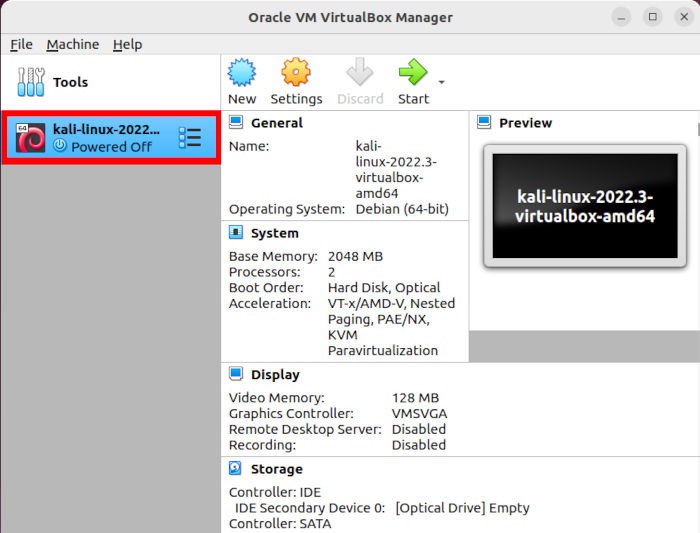
Run Kali as a virtual environment in your machine. Double-click on the Kali Linux entry on VirtualBox’s left sidebar.
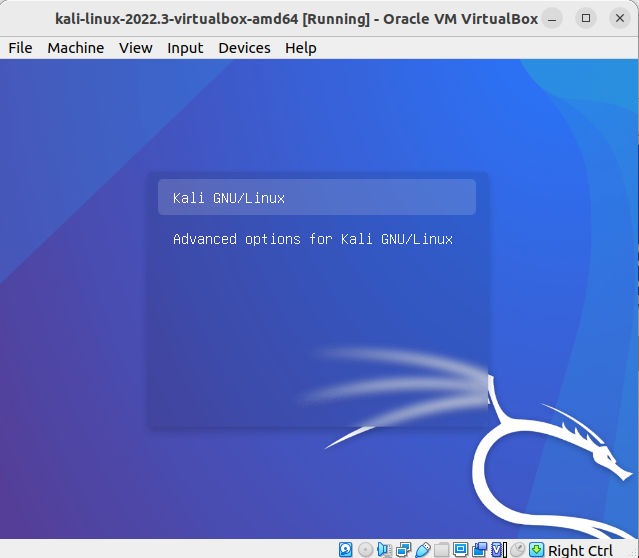
A small window will open and immediately boot the virtual machine in your system.
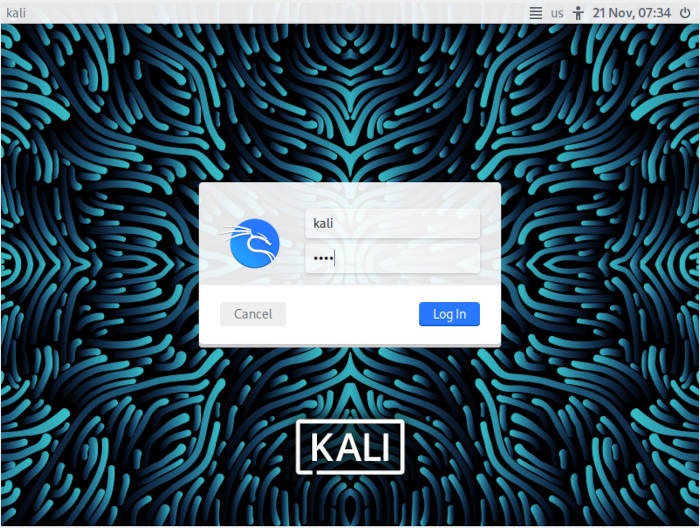
Kali will load to a simple login screen. By default, the username and password for the system should be “kali.”
Tips: learn how you can access an Android phone using Kali Linux.
Finding and Running Tools in Kali
Once you are logged in, use the tools available in Kali to conduct security auditing. For example, press the Kali logo on the desktop’s upper-left corner to get an organized list of programs in the system.
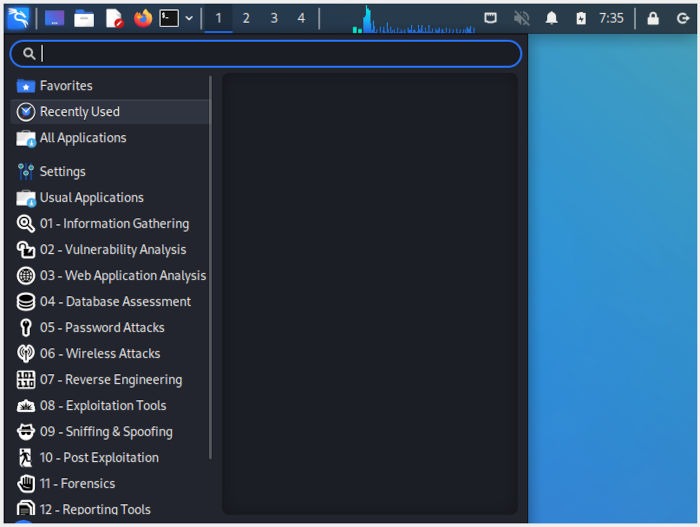
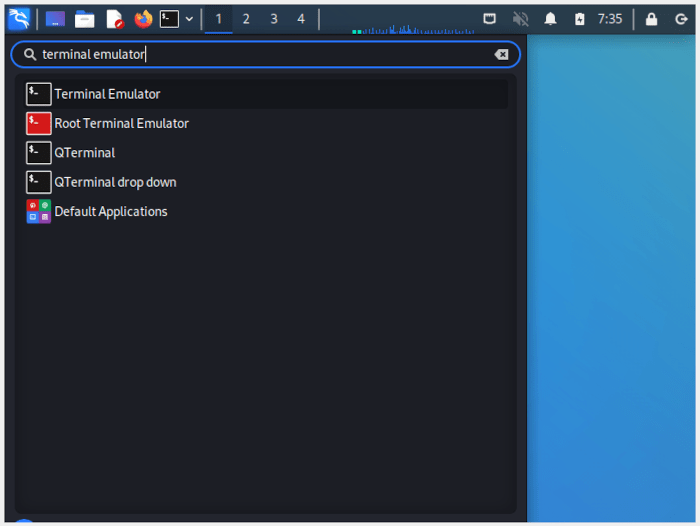
One of the most basic tools you will use in Kali is nmap (more details on using nmap here). This is a small utility that allows you to do a comprehensive scan of machines in a network. To use this, click the “Terminal Emulator” entry in the Kali menu.
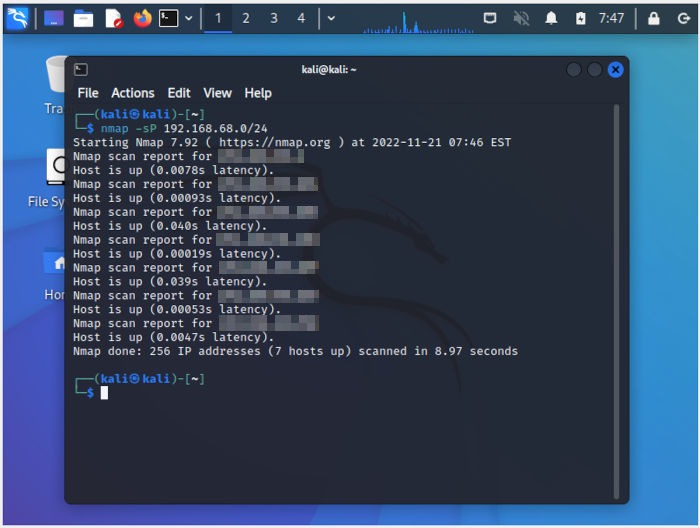
Run nmap -h to print a brief overview of the available options and flags for the program. Knowing that, run the following command to scan the entire subnet for any online clients:
nmap -sP 192.168.68.0/24
Lastly, Kali Linux also provides powerful data processing tools, such as Hashcat, that you can use to crack hashes. For example, you can run hashcat -h to look at some of the program’s options.
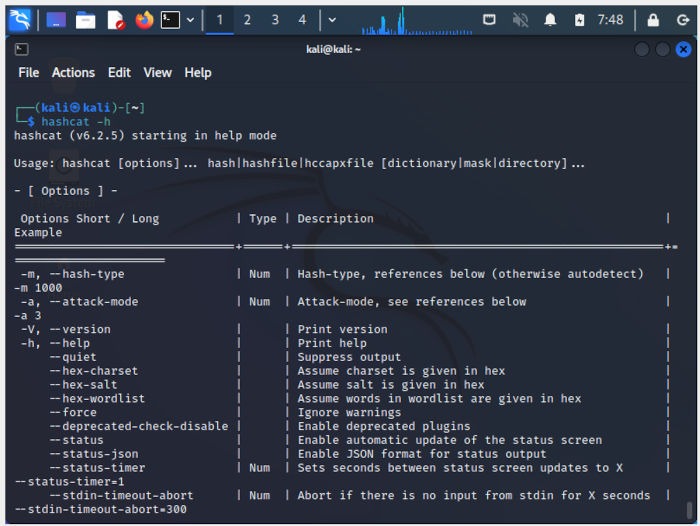
Aside from that, you can also run the following command to test whether your machine can run Hashcat on a reasonable speed:
hashcat -b
Is Kali Linux For You?
Kali is not for everyone. It’s not a regular Linux distribution to run on your laptop to think you’re cool for running a “hacker OS.” If you do so, you’re running a potentially insecure system. Kali is designed to run as root. It’s not secured and configured like a regular Linux distribution. It’s an offensive tool, not a defensive one.
Kali isn’t a joke, either. You can do some real damage with the tools that it comes bundled with and can get you into real trouble. It’s all too easy for an uneducated user to do something seriously illegal and find themselves in a situation no one wants to be in.
With all that having been said, Kali is a great tool for professional use. If you’re a network admin and want to conduct real-world tests on your network, Kali might be just what you need. Kali also has some excellent tools for developers (especially web devs) to audit their applications before they go live.
Of course, if you want to learn more about security the right way, you can certainly use Kali in a virtual environment to teach yourself or follow any number of great courses.
Kali Linux is a bundle of many of the best security tools. It’s an incredible asset for professionals, but it can also be a big problem in the hands of the uninitiated. Use Kali with care and take advantage of its awesome potential. If you don’t, you’re going to end up having a really bad time.
Frequently Asked Questions
Is it safe to browse the internet using Kali Linux?
While you can use the Internet in Kali, the developers of the distribution did not design the system for casual Web browsing, so there are many missing multimedia tools and codecs in the default install, and some websites may not function properly when viewed in Kali Linux.
Is it possible to install third-party programs in Kali?
Similar to a regular Debian installation, you can install any third-party application through the apt program.
Aside from that, you can also use both snap and flatpak packages in Kali.
Are there any disadvantages to installing Kali Linux on a virtual machine?
One of the biggest issues with running Kali on a virtual machine is that it will not have any direct hardware access. Any program that depends on hardware acceleration will either run poorly or not work at all. For example, both Hashcat and John the Ripper are tools that heavily rely on direct hardware access.
Image credit: Unsplash. All alterations and screenshots by Ramces Red.








