Ancient Norse legends speak of a massive serpent named Jörmungandr, so large that it encircles the world and holds its own tail within its teeth.
Fantastic legends like these are often only spoken of in myths, but last Friday we witnessed the birth of a real-life digital “world serpent,” a worm that spread so far that it has encompassed the globe, infecting services like the United Kingdom’s National Health Service and large companies in other parts of the world like Telefónica in Spain.
Although experts are still trying to figure out how this worm continues to spread and how to counter the threat, we have a good idea of what happened and how you can take action to prevent harm to your system.
What Happened?
On 12 May 2017, a massive cyber attack took place by an unknown piece of ransomware (read more about ransomware here). Eventually named WannaCry, it managed to infect an unprecedented 230,000 systems spread across 150 countries using a combination of phishing and exploitation of unpatched systems through local server message blocks (SMBs).
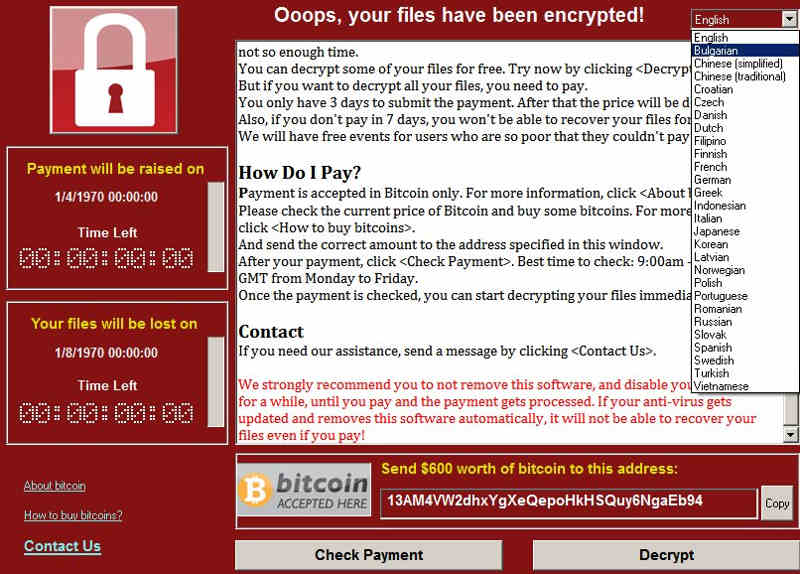
The ransomware would lock you out of your files and show you a screen (shown below) that demanded $300 in Bitcoin within three days to regain access to them or else the price would double.
Although this is how ransomware typically operates, there was a little hitch that made it spread even faster. WannaCry took advantage of a flaw in SMB (which is responsible for file and printer sharing) that allowed it to spread onto other computers within the same subnet. It only took the infection of one single computer to sack the whole network. This is basically what made the infection a nightmare for the NHS and other large institutions.
Perhaps one more noteworthy thing to mention here is the fact that the SMB exploit was taken from the NSA hacking toolkit leak over a month ago. We’ve reported on a similar leak of the CIA’s Vault 7 files, which also contained a variety of functioning exploits that could be used at any given moment by hackers to write similar malware.
The Kill Switch

Some unknown security researcher who goes by the nickname “MalwareTech” registered a domain that was found within WannaCry’s code which stopped the spread of the software. You see, every time the malware would run on a computer, it would check to see if the domain exists (it’s iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com, by the way). Should it be registered, the malware would be able to connect to it and upon doing that would immediately cease spreading. It seems that the hacker who wrote it wanted to test the waters and have a contingency plan in case things go absolutely haywire. This serendipitous moment halted the ransomware from wreaking more havoc … at least for now.
Here’s the grim truth: There is no happy ending here. Decompile the code, and you can easily find the pieces where the application calls the WinAPI functions “InternetOpenURLA()” or “InternetOpenA().” Eventually, you’ll be able to edit out the snippet where it tries to connect to the kill switch domain. It doesn’t require an extraordinarily skilled programmer to do this, and if some hacker gets the bright idea to make a new version of WannaCry with the kill switch edited out before everyone patches their systems, the spread will continue. More enterprising hackers will even edit the Bitcoin account that payments must go to and make a hefty profit.
Versions of WannaCry with different kill switch domains have already been spotted in the wild, and we have yet to confirm whether a version without a kill switch has appeared.
What Can You Do?
In light of what happened, Microsoft has responded rapidly with patches, even covering unsupported operating system versions like Windows XP. As long as you keep your system up to date, you should not experience the SMB-level infection. However, you can still suffer infection if you open a phishing email. Remember never to open executable files sent as email attachments. As long as you exercise a little bit of prudence you should be able to survive the onslaught.
As for the government institutions that got hacked, this wouldn’t happen if they would simply air-gap their mission-critical systems.
Should we expect more daring attacks after hackers implement exploits found in the recent U.S. security leaks? Tell us what you think in a comment!








