Capturing packets is a very useful way of analyzing the inner workings of a network. There’s a variety of different tools available that are developed for this purpose. One of them is tcpdump. Here we show you how to make the best use of this great tool for network engineers and penetration testers alike.
What Is tcpdump?
tcpdump is a network packet analyzer tool that was developed and released in 1988 by a team of computer scientists working at the Lawrence Berkeley Laboratory and its Network Research Group. It is used to display the contents of packets that a computer sends and receives. The utility comes with a variety of options to make the packet capture more specific and focused. Some of these options include different networking protocols and network interfaces.
Installation
Many Linux distributions come with the utility installed straight out of the box. However, if your distro of choice doesn’t, installation is luckily quick and simple.
If you are using Ubuntu or Debian, for example, it can be installed using apt:
sudo apt install tcpdump
On CentOS, the same is done using yum:
sudo yum install tcpdump
And on Arch Linux by using pacman:
sudo pacman -S tcpdump
The Basics
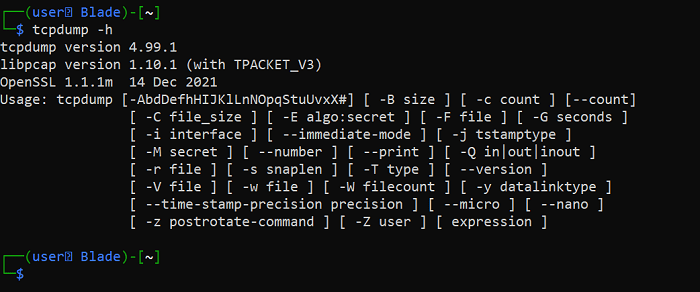
With tcpdump installed, you can take a look at the manual by using the -h flag:
tcpdump -h
This shows you a list of the flags you can utilize when using the tool.
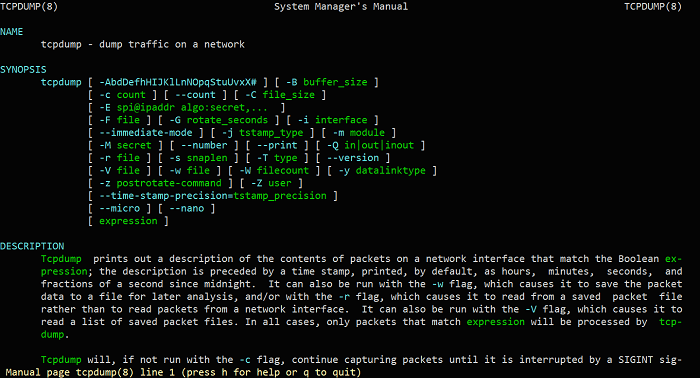
If you want to have a look at a more comprehensive and detailed manual, you can view the man page (manual page) by using the man command:
man tcpdump
You can run a basic packet capture by typing:
tcpdump
Using the command by itself and by not specifying a network interface, the tool will choose one out of the available interfaces on your system.
If you don’t want tcpdump to resolve the hostnames and instead want it to output only IP addresses, you can use the -n flag:
tcpdump -n
If you want to specify the number of packets you want to capture, use the -c flag:
tcpdump -c [number of packets]
Specifying a Network Interface
You can specify your choice of network interface by using the -i flag:
tcpdump -i [interface]
Two of the most common network interface names on most systems are eth0 and wlan0:
tcpdump -i eth0 tcpdump -i wlan0
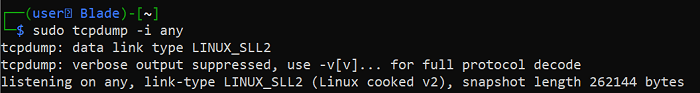
If you want to capture data on all interfaces, you can use the any option:
tcpdump -i any
Also read: Ethernet Switch vs. Hub vs. Splitter: What’s the Difference?
Specifying a Port/Port Range
If you only want to capture data that uses a specific port number, use the command:
tcpdump -i [interface] port [port number]
Let’s say you want to capture traffic on the eth0 interface and for port 443 (HTTPS). Type the following:
tcpdump -i eth0 port 443
Additionally, tcpdump allows you to specify a range of ports:
tcpdump -i [interface] portrange [port range]
Specifying a Host or Subnet
There will be times where you want to limit the captured packets only to the ones sent/received from a specific host or subnet. Luckily, tcpdump allows you to do so.
You can specify a host by using the following format:
tcpdump -i [interface] host [host]
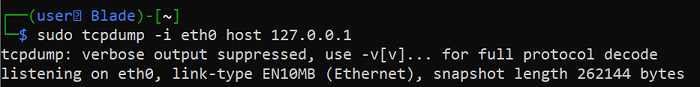
As an example, capture traffic on the eth0 interface and specify the host as 127.0.0.1 (your own loopback IP address):
tcpdump -i eth0 host 127.0.0.1
If you want to specify a network subnet using the CIDR notation, you can use the following format:
tcpdump -i [interface] net [subnet]
For example:
tcpdump -i eth0 net 10.0.0.0/8
You can also directly specify a source host:
tcpdump -i [interface] src [host]
And a destination host:
tcpdump -i [interface] dst [host]
Also read: How to Run Nmap without Root or Sudo
Specifying Verbosity
tcpdump allows you to specify the verbosity of the packet capture. This is very useful when you don’t want to be overwhelmed by the amount of information during a capture.
There are three incremental options for verbosity, the flags -v, -vv and -vvv:
tcpdump -i [interface] -v tcpdump -i [interface] -vv tcpdump -i [interface] -vvv
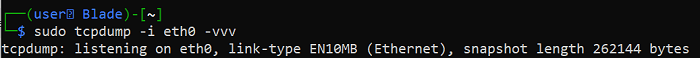
The first option specifies the least verbosity, while the third option specifies the most.
Saving the Capture to a File
It is often useful to save the captured data to a file, so it can be further analyzed and interpreted.
This is done by using the -w flag:
tcpdump -i [interface] -w [filename]
As an example, you can save the captured data to a file called “capture.txt”:
tcpdump -i eth0 -w capture.txt
Also read: How to Open Ports and Set Up Port Forwarding on Your Router
Frequently Asked Questions
1. I received an “Operation not permitted” error. How do I resolve it?
The following is a common error users might receive when trying to use tcpdump:
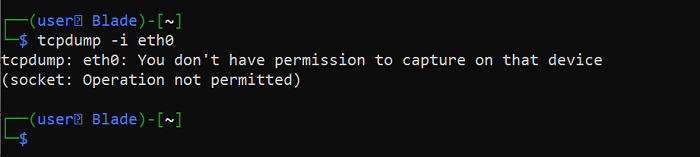
tcpdump gives you this error when you don’t have the necessary permissions to perform packet capture. In most scenarios, you can resolve this by using sudo. For example:
sudo tcpdump -i eth0
2. How do I know which network interfaces are available?
tcpdump has a built-in functionality that allows you to check the available network interfaces on your system.
To check the interfaces, use the -D flag:
tcpdump -D








