A major part of securing a Linux system is locking down unused ports to stop them from being accessed and ultimately hijacked by attackers.
Linux systems are built to be servers, so attackers would attempt to use a compromised system that way, even if that system was set up to be a desktop.
Through the use of tools like NMAP, you can figure out which ports are open on your Linux system, stop unwanted and unused services, and possibly close those ports altogether with iptables.
Install NMAP
First, you need to install NMAP. It’s a well-known and respected security tool, so it’s available in just about every distribution’s official repositories. To install it on Ubuntu, run the following.
sudo apt install nmap
Perform a Scan
Despite being such a simple command-line tool, NMAP has tons of options to perform a multitude of different scans under varying circumstances. You’re not going to need them all for this, but they might be worth experimenting with on your own network for learning purposes.
All that you need to do here is perform a simple scan of your own computer. NMAP will search through the most common ports on your computer and see which ones are open and in use.
In order to scan your computer you’re going to need its IP address. If you don’t know it, run ifconfig in a terminal to find it.
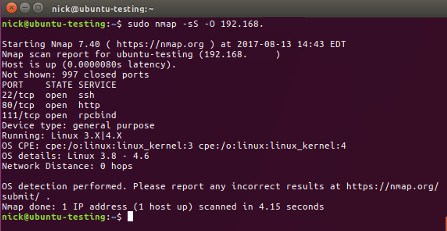
Once you have your computer’s IP, you can use it to scan with NMAP.
sudo nmap -sS -O 192.168.1.100
Substitute your computer’s IP into the command. NMAP will take a few seconds while it scans your computer, it’ll show you which services are running on which ports and whether or not those ports are open. (They’ll all be open.) It’ll also try to tell you what service is using that port. That’s a very important piece of information. Make note of it if NMAP can discover the service.
If you want more information about your computer from NMAP, try using the -A flag to aggressively scan it.
sudo nmap -A 192.168.1.100
You’ll see a ton more information, most of which you really won’t need, unless you see something potentially suspicious.
Finally, if you want to be super paranoid, you can scan every port on your computer. It will take a long time. There are thousands of them.
sudo nmap -sS -O -p- 192.168.1.100
Ports
Take a look at the open ports that NMAP discovered. Do you know what they all are? Are you using all of them regularly? If you answered “No” to either question, it’s worth investigating.
First, Ubuntu and other Debian-based distributions handle services in a weird way. They start every program that runs as a service automatically as soon as it’s installed. While that might seem convenient, it really doesn’t make sense. You’re never going to want to run an un-configured service on a server, so you’ll have to take the service down immediately to configure it for regular use anyway.
It also creates a problem with “phantom” services running without the owner’s knowledge. Package managers pull in tons of dependencies when they install a program. Most of the time you don’t read through all of them, especially if you’re in a rush. That means that you can have services running in the background on your computer without your knowledge or consent. That may be the cause for any unknown open ports that you discovered.
Here are some of the most common ports in use on Linux systems:
- 21 – FTP
- 22 – SSH
- 25 – SMTP (sending email)
- 53 – DNS (domain name service)
- 80 – HTTP (web server)
- 110 – POP3 (email inbox)
- 123 – NTP (Network Time Protocol)
- 143 – IMAP (email inbox)
- 443 – HTTPS (secure web server)
- 465 – SMTPS (send secure email)
- 631 – CUPS (print server)
- 993 – IMAPS (secure email inbox)
- 995 – POP3 (secure email inbox)
There are more, of course, and if you find one totally out of the ordinary, look it up online. If you find any one of these running when you’re not intentionally running that service, shut it down.
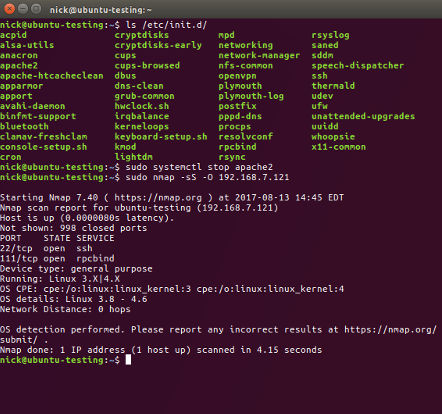
Shutting Down Services
So you’ve uncovered a couple of unwanted services running on your computer. That’s not a big deal. You can use Systemd to shut them down and disable them so they don’t run on startup the next time you boot up your computer.
sudo systemctl stop apache2
The command above stops the apache2 web server. Then, if you want to disable it on startup, run the next command.
sudo systemctl disable apache2
Do that for each service that you prevent from running. If you have a hard time figuring out the exact name of the service, you can list what’s in the service directory.
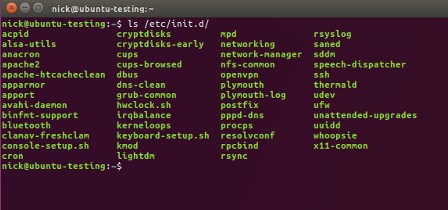
sudo ls -lah /etc/init.d
Block Ports With Iptables
If you want to take things a step further and lock down the ports that you’re not using, you can set up rules in the iptables firewall to allow only the ports that you use and block all other traffic.
That’s a whole separate process, that, if you’re not familiar, will take some time. To learn more about securing your Linux desktop with iptables, check out our article on the subject.
If Something Seems Wrong
You might have stumbled onto something really suspicious. It happens. Sometimes it’s nothing to be concerned about, other times it can be. To make sure that it’s not something that’ll harm your computer or do something about it if it is, you’ll need to scan your computer for viruses and rootkits.
Before you doubt the possibility, Linux machines can get infected with malware. To learn how to scan your machine, drop by our Linux malware guide.
Going Forward
No matter what the results of your scans were, you should check your computer regularly with NMAP to see if there is anything suspicious or simply unwanted running. Remember that unwanted services are also a potential attack surface for would-be intruders. A lean machine is a more secure machine.