Dig is a simple yet powerful tool in Linux that looks up Domain Name System (DNS) information about a specific remote server. Unlike tcpdump, it allows you to gain an insight on how a machine interacts with name servers. This tutorial will teach you the the basics of how to use the dig utility in Ubuntu and how to use the dig utility to understand how DNS works.
Tip: Learn how to use Traceroute to diagnose network issues.
What Is DNS and How Does dig Work?
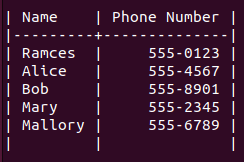
At its core, DNS is a system that allows a machine to seamlessly translate a human-readable domain name to its appropriate IP address. In that regard, DNS is similar to a phone directory where it lists a machine’s address along with an easy-to-remember label.
The Domain Name System works by storing domain records on a set of hierarchical name servers, which announce these records whenever a user attempts to resolve a domain name.
For example, whenever you access “maketecheasier.com,” your computer first connects to a known name server, then asks the server if it knows the IP address for the domain you are looking for. Once your computer knows the appropriate address, it uses that information to connect to the MakeTechEasier website.
The dig utility unmasks this process by showing you how your computer communicates with name servers. It labels and prints every step that it takes from the initial connection to name resolution. This makes dig helpful in understanding any potential DNS issues with your server.
Installing dnsutils on Linux
The dig command is preinstalled in most Linux distributions. If it is not found in your system, you need to install the dnsutils package to access the dig command.
On Ubuntu and Debian systems, install it with the command:
sudo apt install dnsutils
On Fedora:
sudo yum install bind-utils
On Arch Linux and its derivatives:
sudo pacman -S bind-tools
Querying DNS Servers With dig in Linux
One of the most basic actions you can do with dig in Linux is to query the A record for a Web address. The A record contains the primary IPv4 address for a domain name and is what your web browser queries whenever it tries to access a website.
To query the A record using dig, run the following command:
dig maketecheasier.com
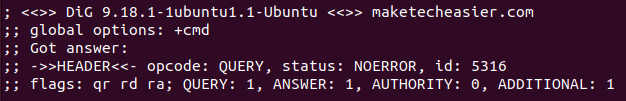
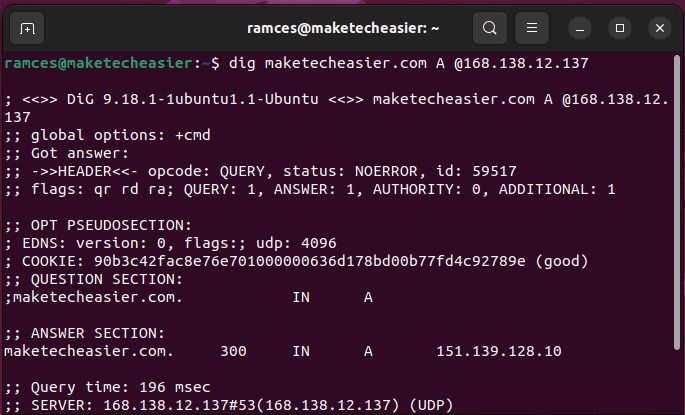
This will print a long string of text that will show the actions that dig took to resolve the domain. For the most part, you can divide this string into four sections: the header, question, answer and nameserver.
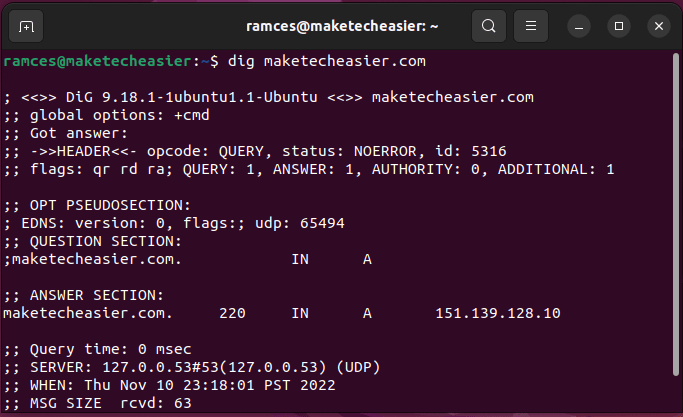
The header section shows a brief summary of the command that you ran. The “opcode” value shows the action that dig did. Meanwhile, the “status” value prints overall result of the query.
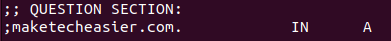
The question section shows a list of queries that you made through dig. The first column prints the complete domain name followed by the query class and DNS record type.
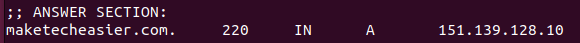
The answer section shows the result of your query. The first column contains the complete domain name followed by its “Time To Live” value. The third and fourth columns show the query class and DNS record type, while the fifth column prints the result.
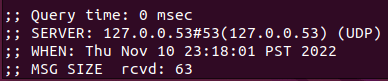
The nameserver section contains details about the DNS server that dig used for this command. The “QUERY TIME” is the amount of time that it took for the server to process the query. The “SERVER” value is the IP address of the name server, and the “MSG SIZE” shows the size of the query in bytes.
If you just want to quickly find the IP address of a website, include the +short option for it to only return the IP addresses.
dig +short maketecheasier.com
Querying a Custom DNS Record Type
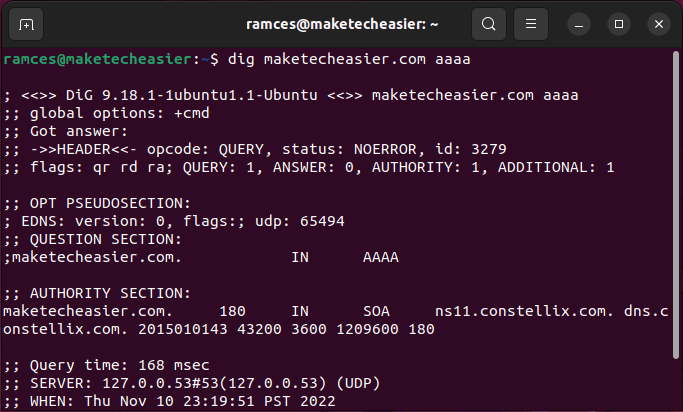
Aside from doing A queries, it is also possible to use dig for looking up other DNS types. You can run the following command to check whether the domain has any IPv6 record:
dig maketecheasier.com aaaa
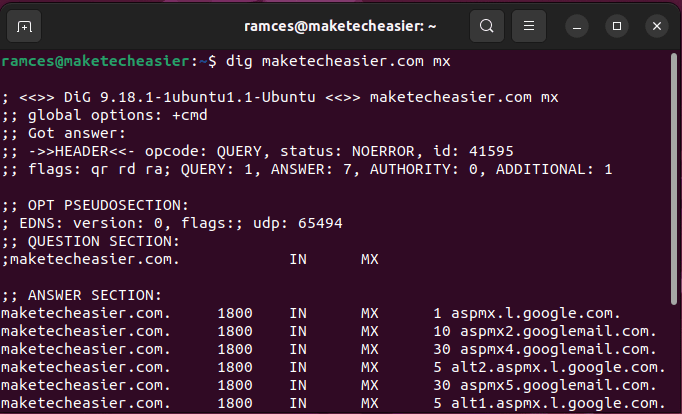
Querying a custom DNS type is also helpful if you are doing reconnaissance work during a penetration test. For example, you can use dig to check whether a domain name is also being used in a mail server:
dig maketecheasier.com mx
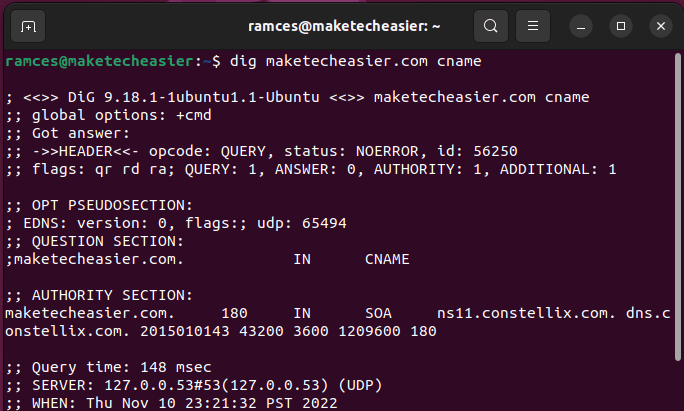
Lastly, dig can also be incredibly useful in learning more about the upstream services for a domain. Both the “CNAME” and the “NS” records will show more details about the server and the nameserver it is using:
dig maketecheasier.com cname dig maketecheasier.com ns
Tip: learn how to enable DNS over HTTPS in various browsers.
Custom Dig Queries in Linux
By default, dig works by connecting to a name server and asking it for a domain name’s details. However, the program also provides a number of additional features that can help in resolving DNS issues.
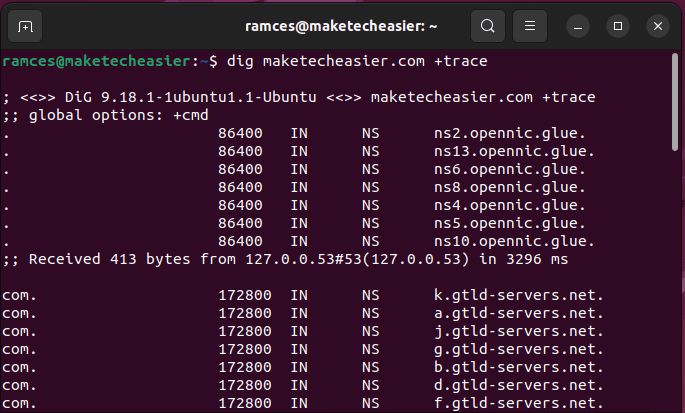
One of the most useful features of dig is +trace. Similar to traceroute, it looks at all the hops that your machine makes whenever it connects to a domain.
For example, running the following command will trace every hop that your machine makes before loading “maketecheasier.com.”
dig maketecheasier.com +trace
You can also customize the name servers that dig uses to poll a specific domain name. This is useful if you have a name server and want to check if it is working correctly.
To force a custom name server, run the following command:
dig maketecheasier.com A @168.138.12.137
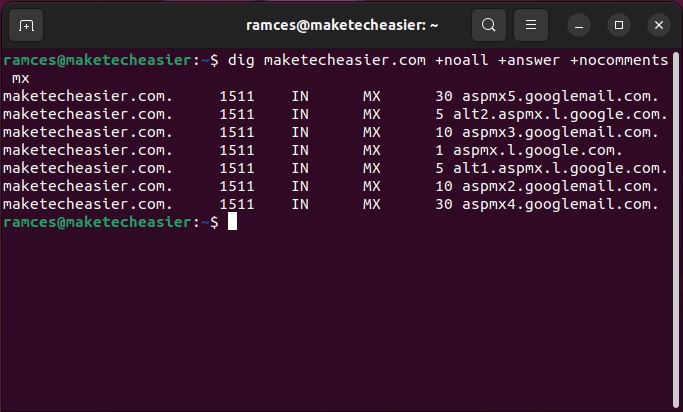
Lastly, dig is also a highly flexible program that can work in a Bash script. To do this, force dig to only print the result of your query:
dig maketecheasier.com +noall +answer +nocomments mx
Note: there are times when the retrieved result is not the correct updated one due to a DNS cache issue in your system. To fix this, flush the DNS cache in your Linux system.
Batch Processing dig Queries
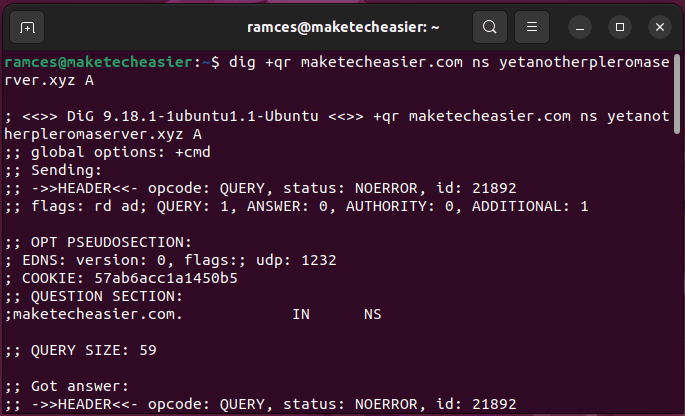
Aside from processing individual domain names, it is also possible to use dig to resolve multiple web addresses. This is especially helpful if you are a network engineer and want to check on multiple domains at once.
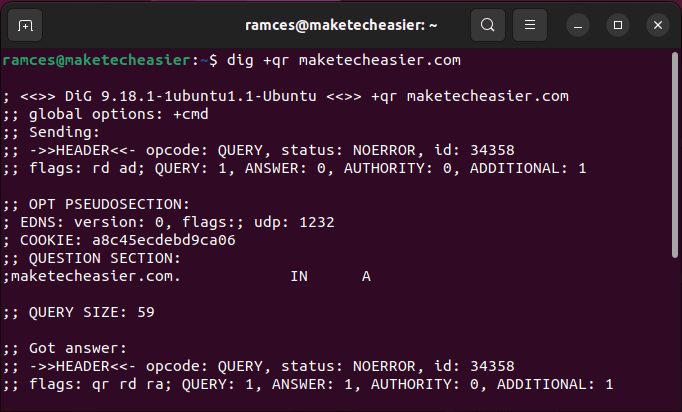
For example, the following command will look for both the NS record of “maketecheasier.com” and the A record for “yetanotherpleromaserver.xyz.”
dig +qr maketecheasier.com ns yetanotherpleromaserver.xyz a
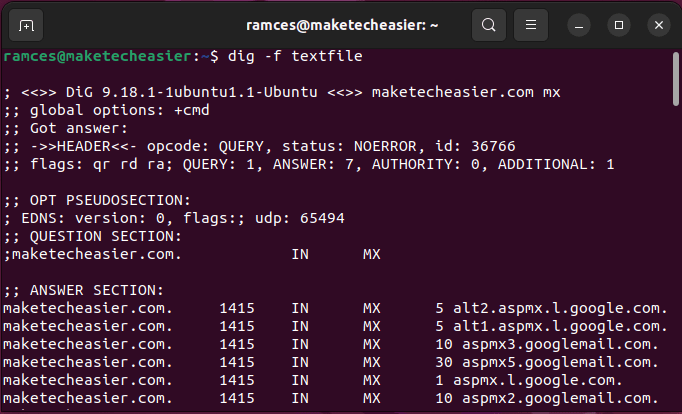
You can also use the -f option to tell dig to get its instructions from an external file. However, you should only write this file in a “dig query” format. Knowing that, consider the following lines of text:
maketecheasier.com mx maketecheasier.com ns -x maketecheasier.com
Saving this in a text file and running dig -f textfile will perform an MX, NS and reverse lookup queries on the “maketecheasier.com” domain.
Frequently Asked Questions
Is it possible to use dig on a local network?
Yes. In most cases, these queries will only be resolved in your local DNS server. This can be helpful if you have an internal DNS server and want to see if it is being recognized in the network.
Is it possible to hack websites and Linux servers using dig?
While dig is a highly useful tool, it is only a small part of a penetration tester’s toolkit. Its primary role is in helping you understand how a machine and its domain name interact with DNS servers. If you are concerned about server breaches, check out securing a Linux server.
My ISP does not support IPv6. Can I run dig purely in IPv4?
It is possible to run dig in either IPv4-only or IPv6-only modes. To do this, you need to add either -4 or -6 options to your dig command. For example, running dig -4 +qr maketecheasier.com mx will force dig to only use IPv4 in its queries.
What’s the difference between dig and nslookup?
Both dig and nslookup are command-line tools that will query DNS servers. The main difference between them is that dig is a much more powerful tool with many more options. Nslookup is simpler to use but does not have as many features. However, for most basic DNS queries, either tool will work just fine.
Image credit: Unsplash. All alterations and screenshots by Ramces Red.








