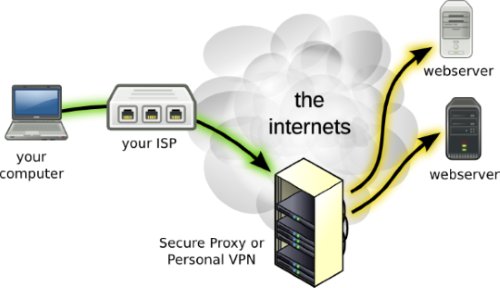
Most of you will have heard of virtual private networks, or VPNs. Many businesses utilize VPNs to create secure links between offices, or to allow employees to connect into the office server remotely. Many internet users also utilize VPNs to get around their country’s restrictive internet firewalls or in order to bypass geographical limitations of online streaming applications (like Netflix). This article will explore the different types of VPN connections, and what they all mean. Each protocol has distinct advantages and disadvantages – generally related to the level of encryption, device compatibility and their ease of use / configuration.
PPTP
Point-To-Point-Tunneling Protocol (PPTP) is the most popularly VPN protocol and is supported by the most devices. PPTP stands for point to point protocol, is by far the easiest to configure and has low overhead that makes it faster than other VPN protocols. Firewalls such as ISA Server, Cisco PIX and Sonic Wall recognize the protocol.
PPTP encrypts data using a 128-bit key which puts it in the “weakest” category of VPN protocols. It has also had other weaknesses in the past, such as clear-text authentication prior to a connection being established and as such it is rarely used in sensitive business environments. However, the most recent implementations of this protocol have resolved some of the security issues – for example, the implementation of EAP authentication.
L2TP/IPSec
Layer 2 Tunneling Protocol (L2TP) came about through a partnership between Cisco and Microsoft with the intention of providing a more secure VPN protocol. L2TP is considered to be a more secure option than PPTP, as the IPSec protocol which holds more secure encryption algorithms, is utilized in conjunction with it. It also requires a pre-shared certificate or key. L2TP’s strongest level of encryption makes use of 168 bit keys, 3 DES encryption algorithm and requires two levels of authentication.
L2TP has a number of advantages in comparison to PPTP in terms of providing data integrity and authentication of origin verification designed to keep hackers from compromising the system. However, the increased overhead required to manage this elevated security means that it performs at a slower pace than PPTP.
SSTP
Secure Socket Tunneling Protocol (SSTP) is viewed as the VPN protocol with the highest security due to authenticating with 2048 bit key certificates and encrypting with 256 bit key. SSTP can be used in place of other VPN protocols (PPTP, L2TP), and is effective in locations where network access is restricted as it uses TCP port 443, the same port used by Secure Socket Layer (SSL) transmissions.
SSTP VPN is viewed as quicker and more reliable than OpenVPN. However, your operating system needs to be relatively up to date in order for it to function properly with SSTP.
The major disadvantage of SSTP is that since it was developed by Microsoft it only functions on Windows Vista / Windows 7 / Windows 8. Currently, there are no intentions to make the protocol available to users of Mac OS, Linux and older versions of Windows.
OpenVPN
OpenVPN was developed by Open Source software as a free alternative to Microsoft’s SSTP protocol. One major advantage of this particular protocol is that it functions on a variety of operating systems, such as, Mac OS, Windows, Linux and some IP phones. Similar to SSTP, OpenVPN has a higher encryption level than L2TP as it operates on both Layer 2 and Layer 3. Furthermore, it is accompanied with extra features such as transporting Ethernet frames, IPX packets and providing NETBIOS functionality.
A minor disadvantage with OpenVPN is that it provides insufficient support for mobile devices and the requirement to install a 3rd party client. This is not the case for SSTP.
A major disadvantage with VPN is the high overhead associated with the protocol due to its level of encryption. It may also be quite challenging to configure.
Final thoughts
The VPN protocols illustrated above all have distinct advantages and disadvantages. The easiest protocol to configure with the best device compatibility would be PPTP. SSTP and OpenVPN are the protocols least likely to be blocked by servers or firewalls and generally thought to be the most secure. In terms of speed, generally speaking, less encryption means greater speed but at the cost of less security. However, if your devices are of reasonable speed this should not be a major factor. Best to consider your security requirements and pick a protocol accordingly.