You have probably heard of AppArmor while using Ubuntu, but since it is not an application that shows up in the Application Menu and doesn’t appear in any graphical form, some may not know what it does and why it is essential for your system. In short, AppArmor is a security module that confines individual programs to a set of listed files and capabilities so that they don’t wreak havoc on your system.
Learn the difference between SELinux and AppArmor to secure your Linux system.
What Is AppArmor?
AppArmor is a Mandatory Access Control (MAC) system that confines programs to a limited set of resources. It restricts programs to a set of files, attributes and capabilities so that it does not go deep into the system and wreak havoc (unless it is given permission to). Instead of Windows’s User Account Control (UAC) model that gives control to users, AppArmor binds the access control attributes to the program itself.
How AppArmor Works
AppArmor works at the kernel level (check out these tips if you are compiling your own kernel) and loads during the initial bootup. AppArmor handles the permission via Profiles: a set of rules that determines what the program can and cannot do.
There are two modes that the Profiles can run: Enforcement and Complain. The Enforcement mode is a strict enforcement of the policy, which is defined in the profile, and reports policy violation attempts. Complain mode will only report the policy violation attempts and does not enforce the policy. Most profiles are loaded in Enforcement mode, though there can be a good number of third-partiy profiles loaded in the Complain mode as well.
Checking Out Your AppArmor Status
If you are using Ubuntu 7.04 or above, AppArmor is installed by default and loads when you boot up your computer. To check the AppArmor status, type the following command into the terminal:
sudo apparmor_status
The image below shows what you will see.
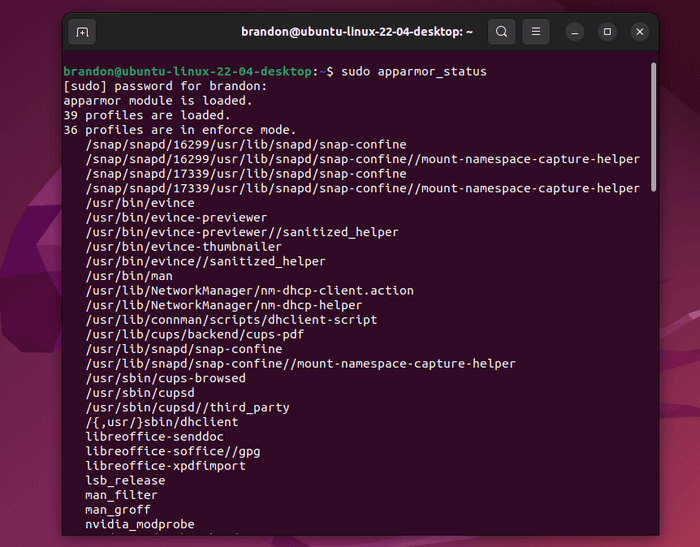
In my system, you can see that there are 36 profiles loaded in Enforcement mode.
Finding Disabled AppArmor Profiles
AppArmor has several preloaded profiles, some of which are disabled by default. You can check these out in the “/etc/apparmor.d/disable” folder. In the latest version of AppArmor, you can see that the rsyslogd profile is not enabled.
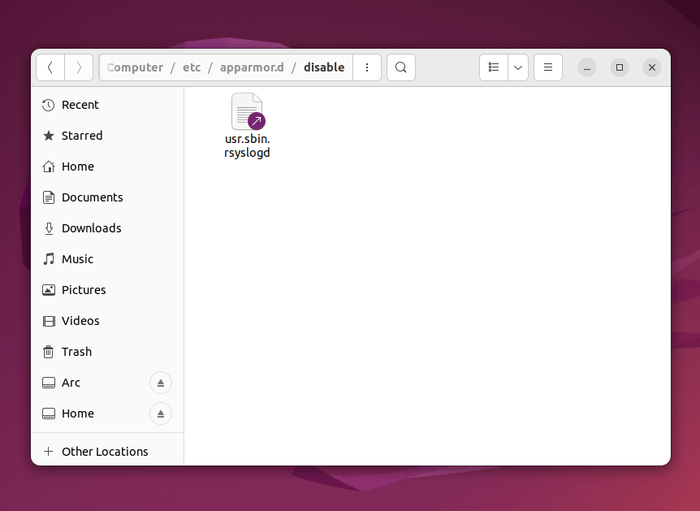
This profile is disabled by default, as users often make configuration changes to rsyslogd that make it incompatible with AppArmor.
Tip: learn how you can manage your Ubuntu machine remotely with Webmin.
Enabling and Disabling AppArmor Profiles
While you can have multiple profiles loaded on your system, each profile can either be enabled or disabled individually. For instance, you can enable the rsyslogd profile mentioned earlier. Follow the instructions below to learn how.
Open a terminal and enter:
sudo apt install apparmor-utils
That will install the tools needed to run subsequent commands in this tutorial. To enable the profile, enter:
sudo aa-enforce /etc/apparmor.d/usr.sbin.rsyslogd
To disable it again:
sudo ln -s /etc/apparmor.d/usr.sbin.rsyslogd /etc/apparmor.d/disable/ sudo apparmor_parser -R /etc/apparmor.d/usr.sbin.rsyslogd
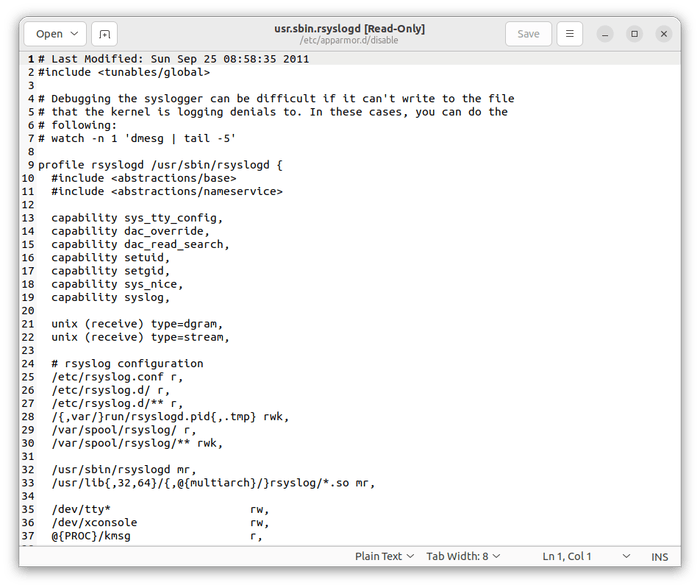
What Does an AppArmor Profile Look Like?
While the AppArmor profiles sound like complicated software, they are actually a simple text file with file paths stating which folders and directories the application can access. You can easily double-click on any profile in the “/etc/apparmor.d” folder to open it in your text editor.
The Rsyslogd profile will look like the below image.
Creating Your Own Profiles to Lock Down Applications
Ubuntu already does a pretty good job to protect you, but if you want to restrict a custom application that is not protected by Ubuntu, you can create your own AppArmor profile to lock down the application. This is particularly useful in a server where applications may be running in the background.
Note: before you create your own profiles, it is best to first look into the existing AppArmor profiles library to check whether the profile for your application is available. You can also install apparmor-profiles to get an extra list of profiles.
Run the following command to start the profiling:
sudo aa-genprof /path/to/application
/path/to/application is the file path to the application that you want to profile. The default application folder is “/usr/bin,” but it could be different depending on the application and install method, such as “/snap/bin.”
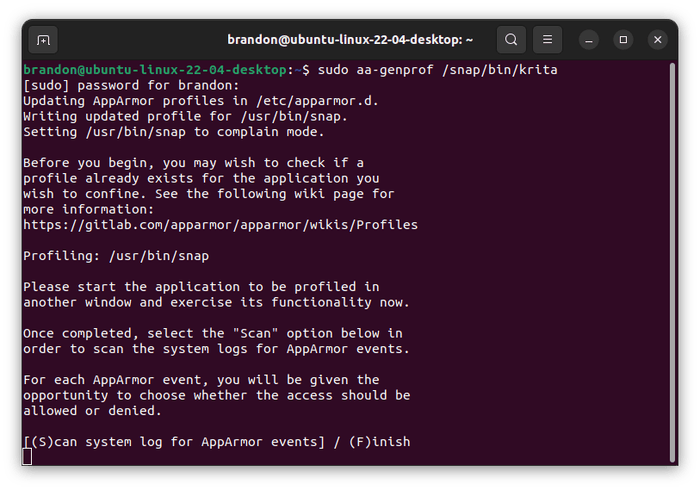
Leaving the terminal running, start the application you are going to Profile. For this example, I am using Krita. Use the application as you normally would.
For every action you perform on the application, return to the terminal and press Shift + S to get it to scan for changes.
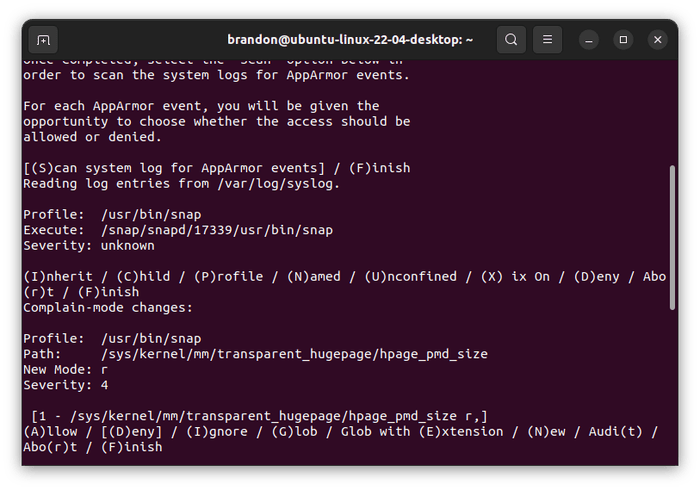
From here, you can see the path that the application is accessing and the severity of the action. Choose to “Allow (A)” or “Deny (D)” the action.
Keep doing this for the rest of the actions performed on the application. To get the best result, it is best that you plan out your list of actions before you start profiling.
Lastly, when you are done, press Shift + F to finish the profiling and Shift + S to save the profile.
Once created, the profile will be saved in the “/etc/apparmor.d” folder and will be loaded in Enforcement mode.
Edit Profiles
To edit your newly created profile, use the following command:
sudo aa-logprof /etc/apparmor.d/
In this case, aa-genprof command earlier.
AppArmor will scan the log entries and allow you to make changes to the profile.
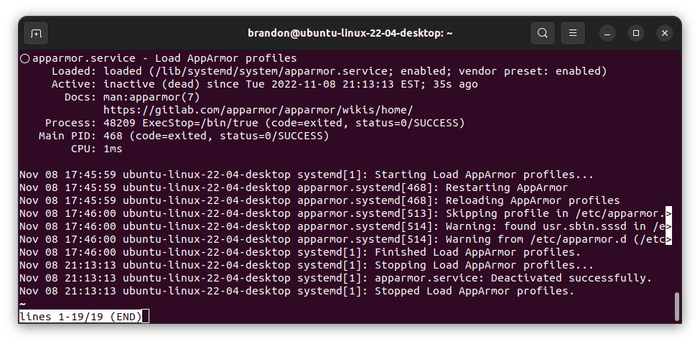
Stopping and Restarting AppArmor
If, for some reason, you need to stop AppArmor, you can easily do it with:
sudo service apparmor stop
You can confirm it was stopped by checking the status with this command:
systemctl status apparmor
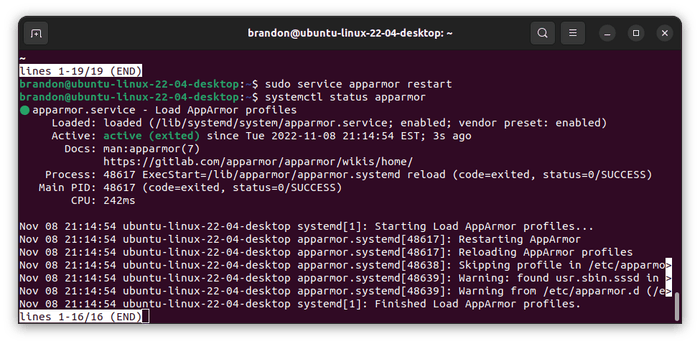
And to start AppArmor again:
sudo service apparmor restart
If you check the status again, you will see a green light indicating that AppArmor is running.
If you are running your own server, check out these tips to secure your Linux server.
Frequently Asked Questions
Why does AppArmor disable rsyslog by default?
rsyslog is configurable software that handles system logging, including receiving, transforming, and delivering log messages to different destinations. Its AppArmor profile, “usr.sbin.rsyslogd,” is included but disabled by default.
According to Canonical engineer Jamie Strandboge, this happens because rsyslog is so highly configurable that the profile may not always work properly.
What is the difference between AppArmor versions 2 and 3?
AppArmor 3.x is the latest version of AppArmor and was released on October 1, 2020, and is a major expansion. AppArmor 2.x is very old, having been released around 2007. It appears there will no longer be any active development on the 2.x series. The latest version, 2.13.6, was released back in December 2020, and AppArmor 2.14 is listed as “cancelled” on the development website. AppArmor 3.0.7 was released on August 9, 2022.
If I have AppArmor, do I still need an antivirus?
Yes, you still need an antivirus program even if you have AppArmor running. The two perform completely different operations and complement each other. It’s good to have an antivirus on Ubuntu, even though Linux systems are less targeted by creators of malware.
What are binary blobs and why are they a security risk? Learn the answer and how Linux-Libre can offer your better protection than plain Linux.
All screenshots by Brandon Li.