If you use Linux, there will probably come a time when you need to know more about your network. Several tools can help you do this, and some are more complicated than others. The ss command is something you can rely on being installed on many machines, so it’s handy to know.
What Is the ss Command?
While the two-letter command’s name may seem arcane, it’s actually quite simple. Like many Linux/Unix commands, the name is an abbreviation of what the command does. Here, ss stands for Socket Statistics.
Socket Statistics is a replacement for the old netstat tool, aimed at being easier to use and understand. It simply displays information about sockets. This includes not only TCP and UDP sockets, the most commonly used types, but also DCCP, RAW, and Unix domain sockets.
Basic Usage
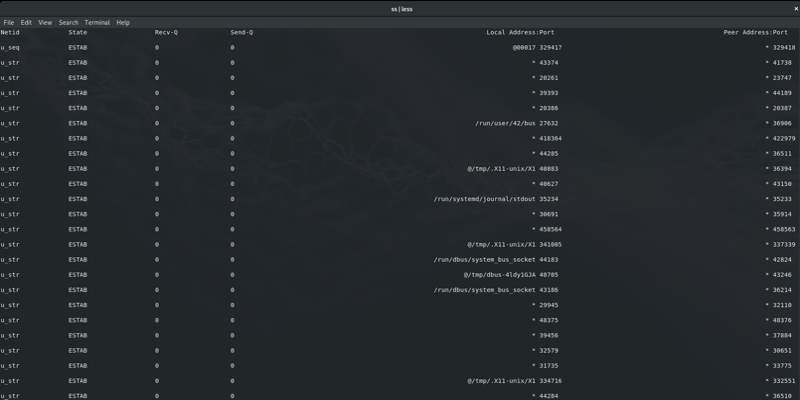
The simplest way to use the ss command is to simply run it without arguments. This will display quite a lot of data, so you probably want to pipe it through less for easier reading.
ss | less
As it is, this isn’t especially useful. It displays a ton of information, but there’s so much that it’s hard to read. To make it easier, you can filter certain types of sockets.
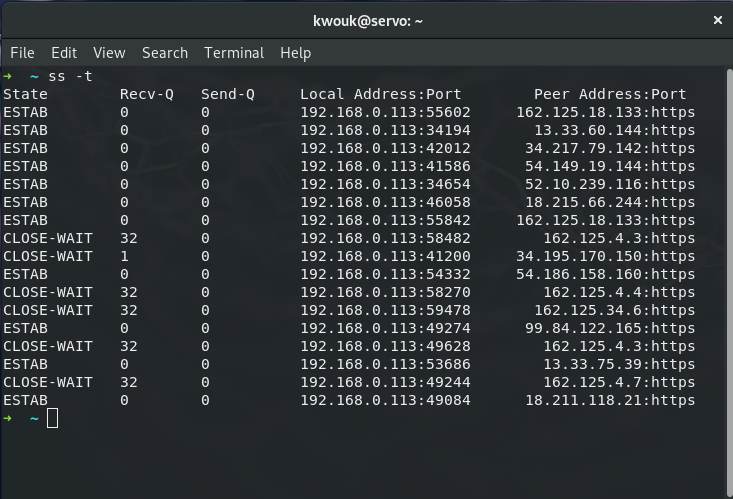
For example, you can list only TCP sockets.
ss -t
Or, you can list UDP sockets instead.
ss -u
By default, these options only list sockets that have established connections. To list all the TCP sockets that are either listening or connected, you can run the following:
ss -t -a
So far, this all seems pretty simple. Let’s learn more.
Useful Things You Can Do With the ss Command
Now that you’re familiar with the basics, it’s time to start using the ss command to monitor your network. There are many things you can do, but here are a few ideas to get you started.
Monitoring TCP States
If you’re familiar with networking, you already know this, but TCP connections have different stages. These detail the entire lifespan of a connection. We can drill down to certain types of stages using the ss command.
In addition to the standard TCP states like “established” and “closed,” the ss command supports a few custom filters. For example, the “connected” state is simply every TCP state with the exception of “listening” and “closed.” To use this, run the following:
ss state connected
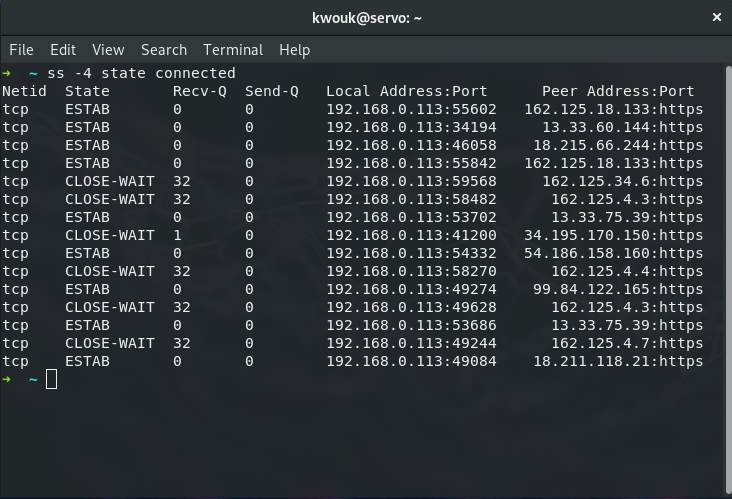
IPv4 and IPv6
If your network uses a combination of IPv6 and IPv4 addresses, you can filter them using the ss command. Just use the -4 or -6 flags. If you want to see all IPv4 connections, you can tie in TCP state.
ss -4 state connected
If you wanted to see all IPv6 sockets, you would simply run the following:
ss -6
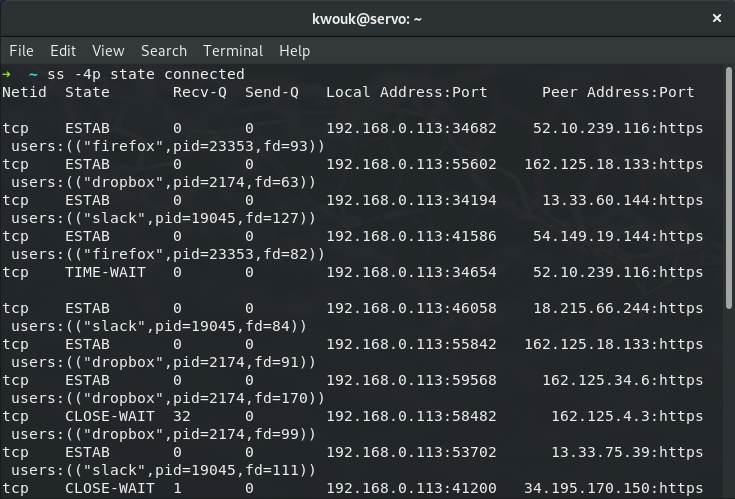
What Process Is Using this Socket?
If you know a socket is listening but don’t know why, you can easily track this down. Running the following will show you the name and process ID of all connected IPv4 TCP sockets.
ss -4p state connected
Displaying a Summary
Sometimes you just want a brief rundown of the sockets on a given machine. This is also one of the easier commands to run, as it consists entirely of the letter “s” and one dash:
ss -s
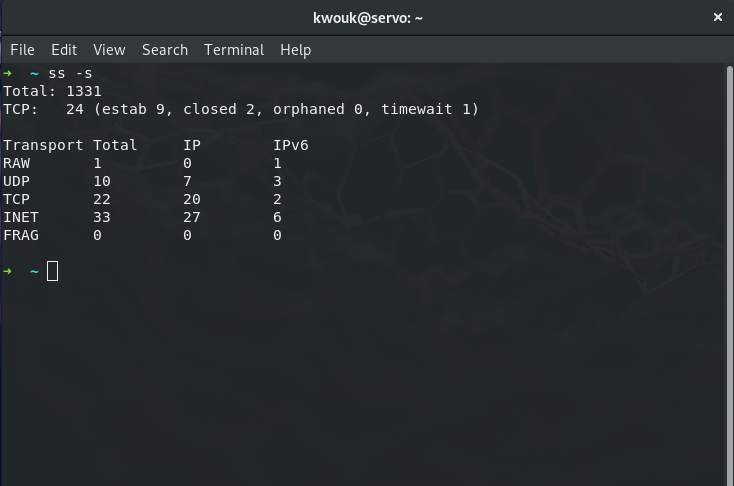
This gives a summary of all the sockets on your machine and displays whether they’re IPv4 or IPv6.
Want to Know More About Your Network?
This is just the beginning of what you can do with the ss command. It’s a powerful tool and one well worth learning. To dig deeper, open a terminal and look over the documentation in the tool’s man page. Just run man ss to get started.
If you’re looking to secure your machine, ss is handy, but it’s not the only tool available. Take a look at our guide to checking open ports on Linux to learn more.