I doubt any of you reading this article subscribe to the idea that men at keyboards wearing Guy Fawkes masks can take over the world with some keystrokes. However, digital security is still extremely important, especially where smartphones are concerned.
While Android devices are more likely to be infected, infection is still very much possible on iOS devices, especially if you’re running an older version of iOS (say, on an old device) or the device happens to be jailbroken. As much as Apple loves its walled-garden approach, and Google has tightened up in terms of malicious software in its own Play Store, things can still slip through those cracks or evade those fronts entirely.
No matter what platform you use, you should listen up.
Smartphone Malware: What is it, and what can it do?
By definition, malware is software made to damage or disable your device. Viruses are technically a subset of malware that work by infecting already-existing files, like an actual, well, virus. Personal computers are the usual targets of malware attacks, but in more recent years smartphones have become more common targets, as they have become an everyday consumer electronic, much more so than the PC ever really was.
So what can malware really do to your phone? Your smartphone is a treasure trove of personal information such as the passwords to your emails, the names and contact numbers of your closest friends and family, where you browse online, where you go in real life, etc. Now, what if this information was leaked and got onto the hands of the hacker? I am sure you can imagine the consequence.
Smartphone Malware: Transmission
That is a scary word, isn’t it? Transmission, I mean. It makes you think of swine flu or something.
Now, despite malware and viruses being referred to as such, most of them aren’t exactly contagious, per se. Some spread out and infect a wide variety of host machines, but before that can happen, those machines all need to be individually vulnerable. Many smartphones (all of Apple’s and most new Android devices) already support device encryption, and the application storefronts through which malware may be distributed are usually watched carefully for that kind of behavior.
In the past, the Android Market and App Store have both faced malware disguised as friendly applications. Both Google and Apple have since started more tightly moderating their services, but while the chance of risk may be slimmer, that doesn’t mean it’s impossible. Play and App Store moderation isn’t necessarily enough to prevent infection, however, because smartphone malware usually gets around by evading those fronts entirely.
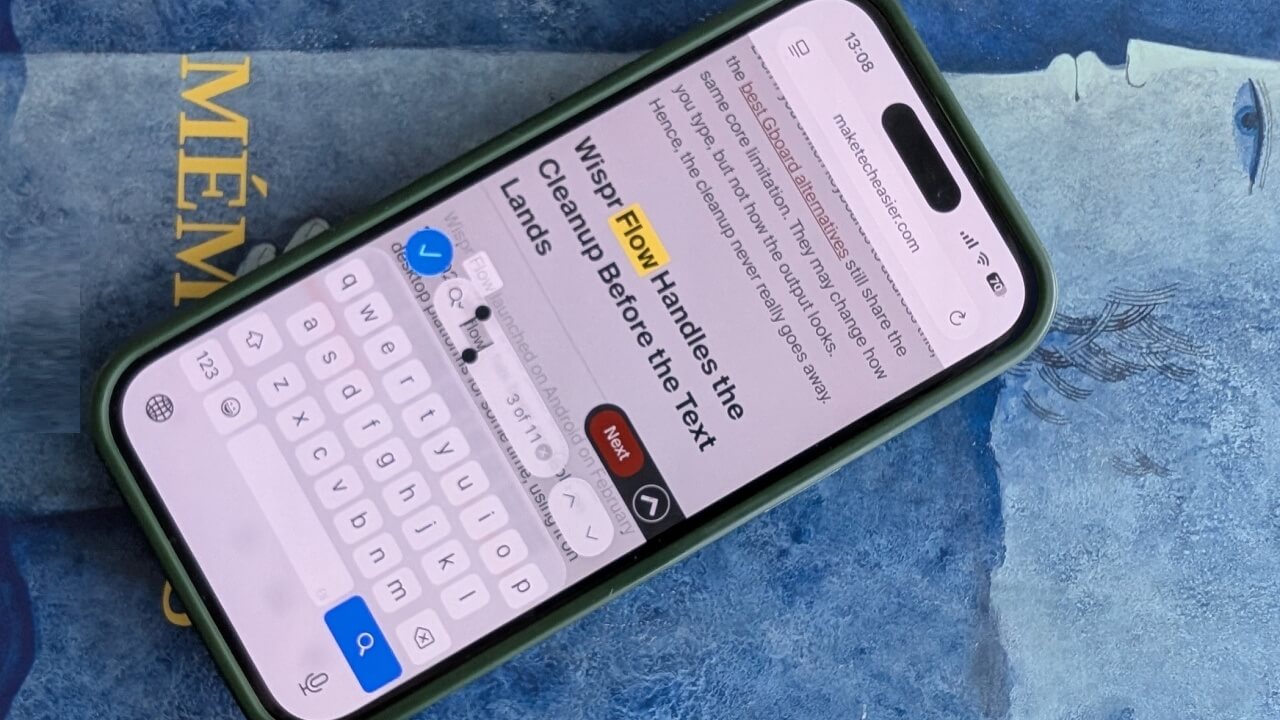
Some websites, for instance, may give you a pop-up of a false version of your device’s Store, attempting to bait you into downloading an application you think is safe but is actually malware.
Smartphone Malware: Removal
iOS users have it a bit rough here, unfortunately. If you can’t update your version of iOS, or if the exploit in question hasn’t yet been fixed, your options are unfortunately limited to either uninstalling the application (if that even works or is possible, which it isn’t in some cases) or performing a full wipe of the device and restoring your applications from the App Store.
Android users have a wide variety of anti-malware applications, usually backed by the big names in PC security, like Avast or Malwarebytes. These applications are usually perfectly dependable for removing infections from the machine, but if uninstalling the offending application or removing the infection with an anti-malware app isn’t possible, you’re faced with the same nuclear option that iOS users are: you might just need to do a factory reset of your device.
Rooted Android users should be particularly cautious – if the infection happened due to you granting Superuser access to your device, you may just need to install a custom recovery, wipe your entire phone and flash a completely new ROM, factory or custom. Infections caused by Superuser access can sometimes avoid even a factory reset removal attempt.
So let’s say you’ve recovered from an infection, or you haven’t been infected at all and just want to be secure – what do you do?
Smartphone Malware: Prevention
Like any good paranoid old man, I have a solution for you.
Be careful.
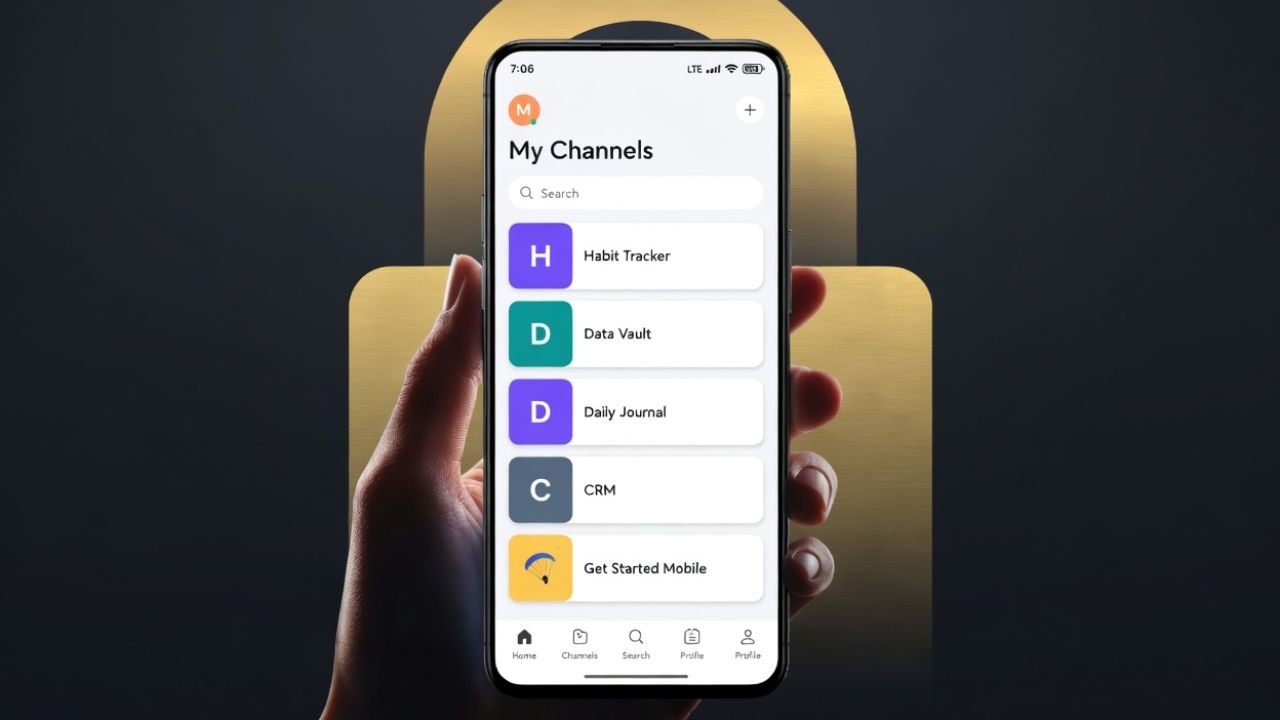
This means you can’t install applications from unknown, untrusted sources. Jailbroken iPhone users are typically exploited in this way and usually won’t get help from Apple if it doesn’t affect non-jailbroken users, while Android users have to manually enable installing non-Play Store applications in Options. If you aren’t completely sure of what you’re installing on either device, DO NOT INSTALL IT. Don’t go to shady websites, especially not ones that plague you with pop-ups in an attempt to trick you into making the wrong move. Like PCs, smartphones are still computers, and anything that can be called a computer is vulnerable to some form of exploitation.
Even if you aren’t installing non-Store applications, keep a careful eye on the permissions for the ones you do install.This applies especially to Rooted and Jailbroken users. That hot new game you installed – why does it want access to virtually everything on your phone? Security and privacy have many intersections, so take into consideration what privacy you’re giving away at all times, because by definition the opposite of security is insecurity, and insecurity means you’re more open to attack.
Following these steps, you should be perfectly safe and sound.
If you want added security, however, consider installing security applications like Malwarebytes or Avast – there’s plenty of trustworthy, free security solutions for Android.
If you want go the extra mile, you could always buy the Blackphone. I mean, I wouldn’t personally recommend it unless you work for NSA, but if you work for NSA you probably already know a thing or two about privacy-violating malware.
Let us know what you think about mobile malware and how you deal with it.