If you’ve been using Linux for any amount of time, you undoubtedly have heard about a tool known as SSH. Secure Shell, commonly known as SSH, is a network protocol for establishing secure connections between a client and a remote server. It is designed to allow users to log in securely to various different types of computers remotely over a network. Here we show you how to set up and copy the SSH keys to your server easily.
Also read: How to Show All Active SSH Connections in Linux
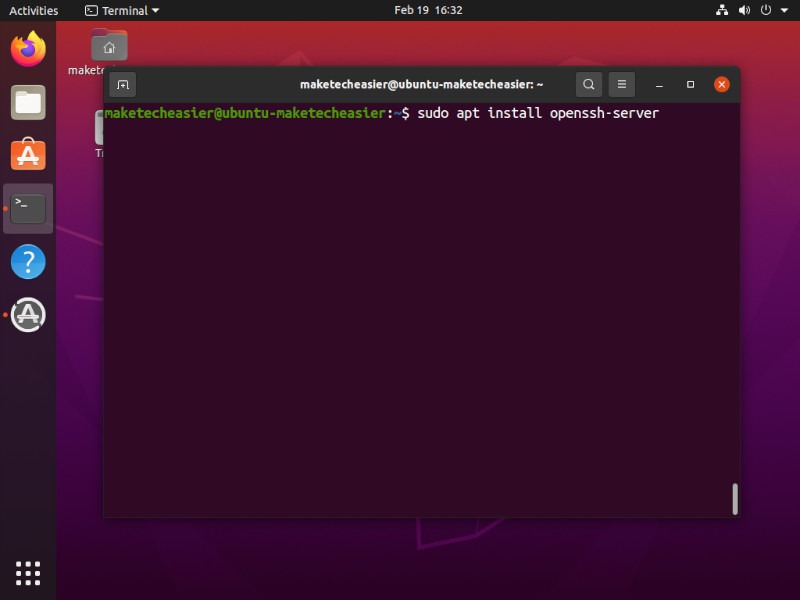
Installing SSH
To get started, we have to install the SSH server. You can find and install the openssh-server package in Software Center or your package manager. Alternatively, if you’re on a server (or just prefer to use the terminal), open a terminal and type the following command:
# Ubuntu/Debian sudo apt install openssh-server # Fedora/CentOS/REHL sudo dnf install openssh-server
Also read: How to Create an SSH Honeypot to Catch Hackers in Your Linux Server
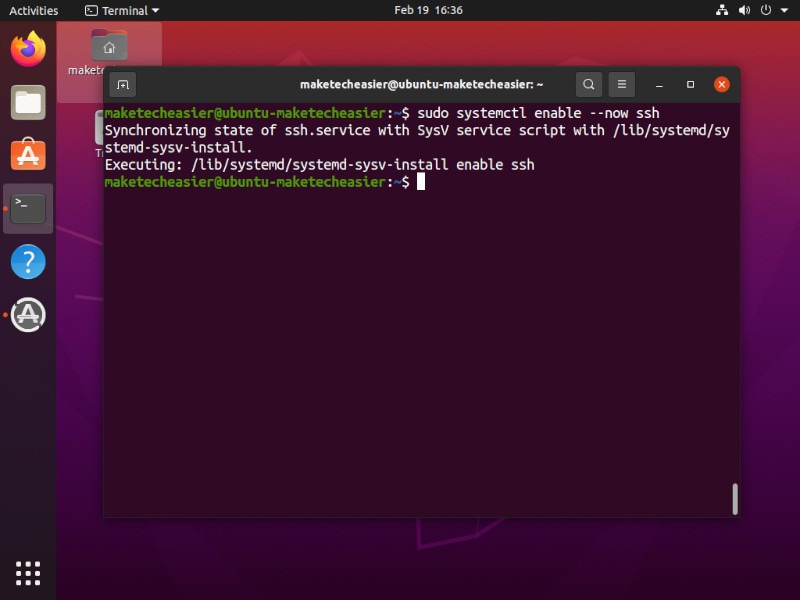
Enable SSH in Linux
Once the OpenSSH server has been installed on your machine, you’ll need to start and enable the systemd unit. To do that, you can simply type the following command into the terminal:
sudo systemctl enable --now ssh
Good to know: you can connect programs in Linux using SSH pipes.
Generating SSH keys
Once you have installed the openssh server, you can start to generate SSH key pairs. Before proceeding, ensure you do not have an existing key pair, as this process will overwrite the existing one.
To check whether you have an existing key pair, use the command:
ls -la ~/.ssh
If you have an existing key pair, the command above should display the “id_rsa” and “id_rsa.pub” files.
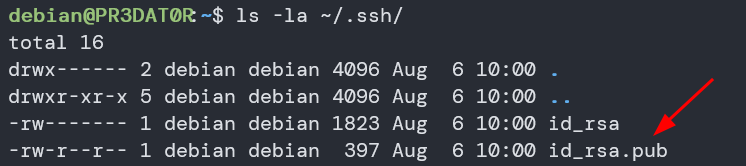
Once you verify you do not have an existing SSH key pair, you can proceed to generate a new one. Otherwise, backup your old keys to avoid losing them.
To generate a new key, use the command:
ssh-keygen -t rsa -b 4096
The command above invokes the ssh-keygen utility to interactively generate an SSH key pair. Using the -t option, we specify the key type to generate. In this case, we generate an RSA key.
We also use the -b option to specify the number of bits in the key. If you use an RSA key, the minimum bit size is 1024. If not specified, it will generate the key with 3072 bits.
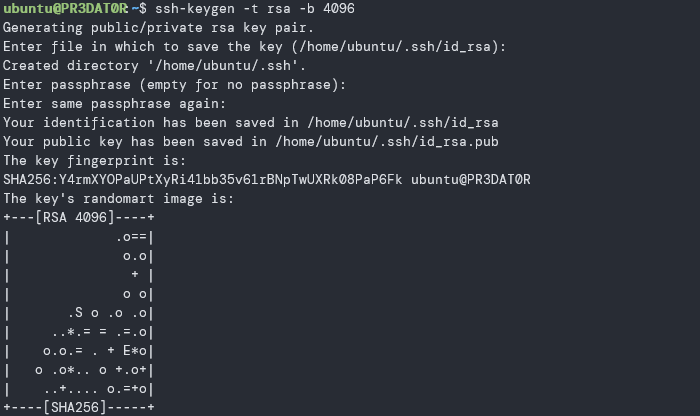
It is good to use the default location to store the SSH keys to avoid typing the path when connecting to SSH using the keys.
If you do not want to encrypt your key with a passphrase, press Enter to skip.
Copy Key to Remote Server
Now that we have generated a new SSH key pair, we need to upload it to the remote machine we want to manage.
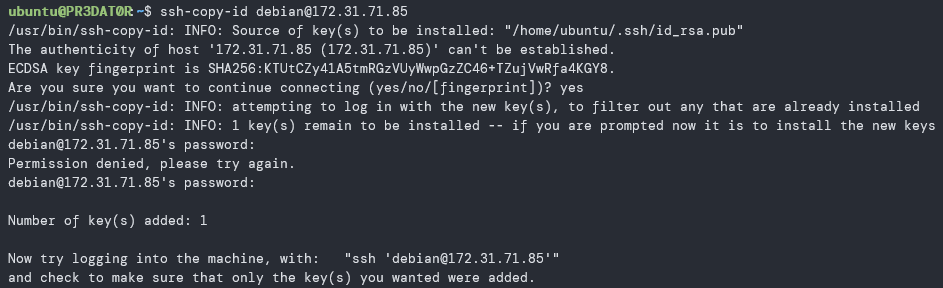
The most efficient way to do this is to use the ssh-copy-id command. Use the command as:
ssh-copy-id remote_user@remote_IP
If you are using a keyfile with a separate filename, you can use the following command to specify the path to the keyfile.
ssh-copy-id -i ~/.ssh/id_rsa remote_user@remote_IP
If you are logging in to the remote machine for the first time, you will need to accept the fingerprint.
Next, enter the SSH password for the remote user.
Once authenticated, the ssh-copy-id command will append the contents of your id_rsa.pub key to the “~/.ssh/authorized_keys” file on the remote machine and close the connection.
Log in to Remote Machine
Once you have successfully completed all of the above steps, you can now log in to the remote server without the need for a password.
You can test this by using the command:
ssh remote_user@remote_ip
Unless you have a passphrase enabled for your key, you will be logged in automatically.
Frequently Asked Questions
1. Is SSH secure?
SSH is a powerful security tool that allows authenticated users to log in to a remote system. However, it is only as secure as its configuration file allows. An unconfigured/misconfigured SSH server can be vulnerable to hackers and third-party access too. Make sure you secure the SSH configuration right after you install it.
2. Where is the SSH authorized keys?
The SSH authorized_keys file holds the public keyfile of each user and specifies which users are allowed to log in to a server. In Linux, the authorized_keys file is usually found in the “.ssh” folder in the user’s Home directory.
3. How can I fix the ssh-copy-id permission denied issue?
This only happens when you already have a public key set up in your remote server and have disabled password authentication. To fix this issue, first log in to your server, enable the password authentication in the “/etc/ssh/sshd_config” file, then run the ssh-copy-id command again.
Once you have copied the new keyfile over, remember to disable the password authentication option again.








