Apache is one of the most widely used and popular web servers in the world, and it powers almost 40% of all the servers in the world. If you are a webmaster or administrator maintaining an Apache server, it is important for you to know how to secure Apache and prevent it from being hacked. In this article we will describe some tips and tricks that you can use to secure your Apache server.
Note: we are using Ubuntu 14.04 for this tutorial.
Install and Update Apache
First, you need to update and install Apache to your system.
For this, run the following command:
sudo apt-get update sudo apt-get install apache2
Hide Apache Version
By default, Apache displays the version of your Apache web server installed on your system with the name of the operating system of your server.
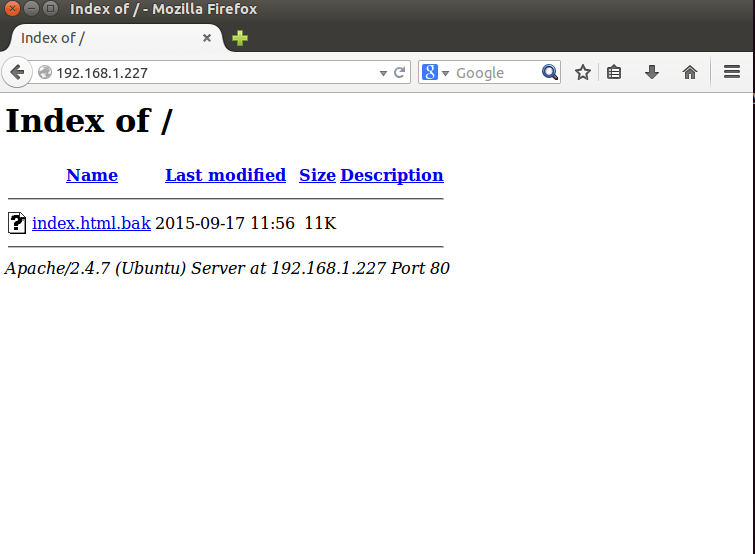
In the screenshot above you can see the Apache version and the operating system installed in your server. This can be a major security issue for your web server. To hide this information, you need to edit Apache’s main configuration file (“/etc/apache2/conf-enabled/security.conf”).
sudo nano /etc/apache2/conf-enabled/security.conf
Add/edit the following line:
ServerSignature Off ServerTokens Prod
Save the file and restart apache service.
sudo /etc/init.d/apache2 restart
Turn Off Directory Browsing and Disable Symbolic Links
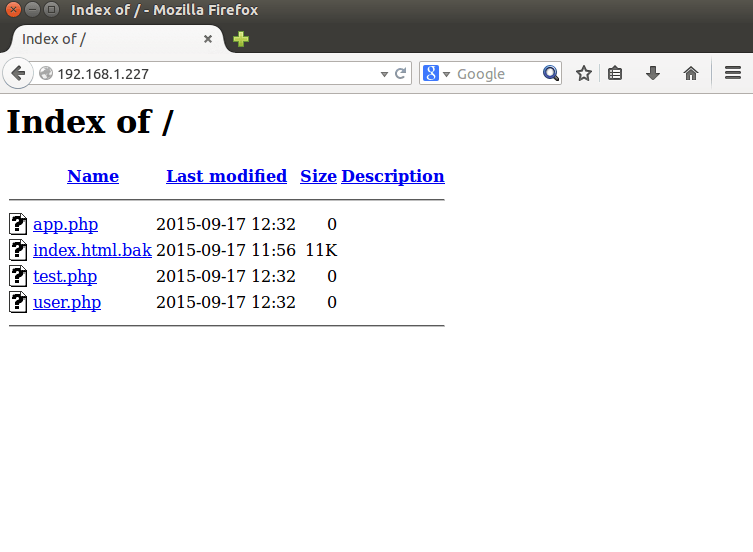
By default directory listing is enabled in the Apache server. Directory listing displays all of the directory with all the files from the Apache server. If this is enabled, an attacker can easily view any file, analyse it and obtain sensitive information about an application.
You can see the default directory listing in the image below.
You can disable this setting by editing the Apache configuration file.
sudo nano /etc/apache2/apache2.conf
Add/edit the following line:
Options -FollowSymLinks
AllowOverride None
Require all granted
Note: the above code assumes that your web pages are served from the “/var/www/html” folder. If you have changed the public folder to a custom location, change the Directory path in the above code.
The line Options -FollowSymLinks also disables symbolic links. If you want to enable symbolic links, remove the “-” sign in front of FollowSymLinks, so it becomes Options FollowSymLinks.
Save the file and restart the Apache server.
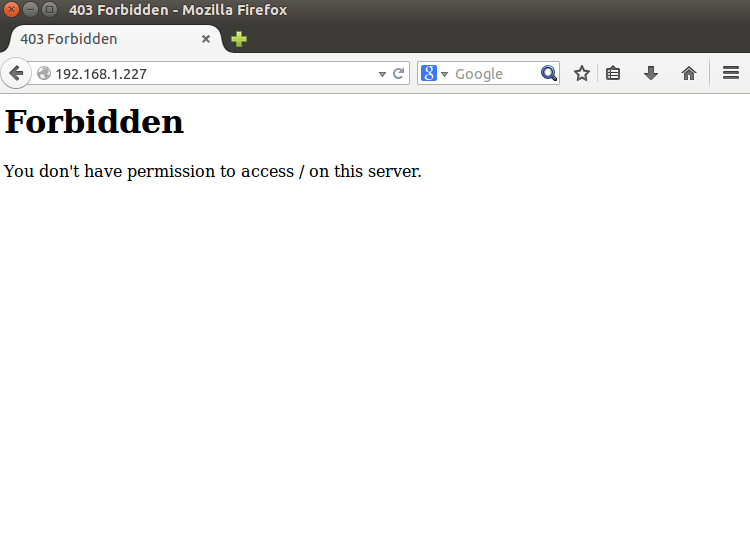
After this try to visit the Web in a browser, and you will get a forbidden error displayed in the below image.
Disable Unnecessary Modules
By default Apache comes with several installed modules that are unnecessary for normal usage. It is recommended to trim the fat and disable all those unnecessary modules. You can list all enabled modules on your server using the following command:
sudo ls /etc/apache2/mods-enabled/
This will display the output as shown in the below image.
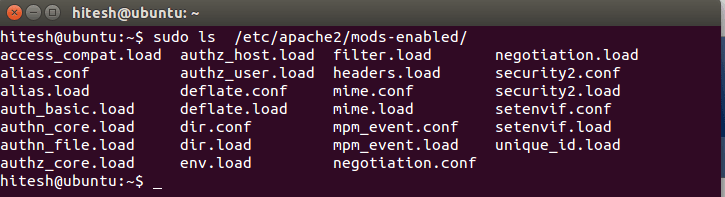
From the above-listed modules, some modules like “status” and “autoindex” are enabled but not needed.
You can disable this modules using the following command:
sudo a2dismod autoindex sudo a2dismod status sudo /etc/init.d/apach2 restart
Make Use of ModSecurity
Mod security is a free Apache module used to protect your web server from various attacks like SQL injection, cross site scripting, session hijacking, brute force and a lot of other exploits. It also allows you to monitor traffic on a real-time basis.
You can install mod security using the following command:
sudo apt-get install libapache2-modsecurity
To check if the mod_security module is running, use the following command:
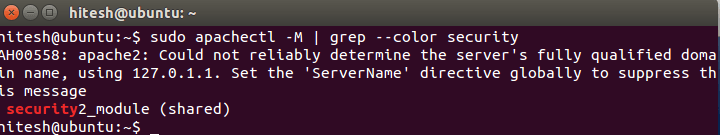
sudo apachectl -M | grep --color security
The image shown below indicates that the module was loaded.
To enable the mod_security rules, you need to rename and edit the mod security recommended configuration file and set the SecRuleEngine option to On.
For this run the following command:
sudo mv /etc/modsecurity/modsecurity.conf-recommended /etc/modsecurity/modsecurity.conf sudo nano /etc/modsecurity/modsecurity.conf
Add/edit the following line:
SecRuleEngine On
Now restart Apache for the changes to take effect.
There are lot of security rules that come with Modesecurity (called the Core Rule Set) that are located in the “/usr/share/modsecurity-crs” directory. Now you need to enable these rules to get it working with Apache.
You can do this by editing the “/etc/apache2/mods-enabled/security2.conf” file.
sudo nano /etc/apache2/mods-enabled/security2.conf
Add/edit the following line:
IncludeOptional /etc/modsecurity/*.conf
IncludeOptional "/usr/share/modsecurity-crs/*.conf"
IncludeOptional "/usr/share/modsecurity-crs/base_rules/*.conf
Save the file and restart Apache.
Turn Off Server Side Includes and CGI Execution.
It is recommended to disable server side includes and CGI execution if not needed.
To do this you need to edit the Apache main config file.
sudo nano /etc/apache2/apache2.conf
Add/edit the following line:
Options -FollowSymLinks -Includes -ExecCGI
AllowOverride None
Require all granted
Save the file and restart Apache.
You can also do this for a specific directory. For example, to turn off server side includes and cgi file executions for the “/var/www/html/webdir1” directory, ddd/edit the following line:
Options -Includes -ExecCGI
Save the file and restart Apache.
Limiting Large Requests
By default Apache has no limit on the size of the HTTP request. This will allow an attacker to send a large amount of data. Apache has several directives that allow you to set a proper request size. This will protect your web server from a denial of service attack.
You can set the value from 0 (unlimited) to 2147483647 (2GB) in the Apache main config file.
For example, limit the request size of the “/var/www/html/webdir1” directory to 200K.
sudo nano /etc/apache2/apache2.conf
Add/edit the following line:
LimitRequestBody 204800
Save the file and restart Apache.
Disallow Browsing Outside the Document Root
It is recommended for Apache to be able to access only the document root directory. You can secure the root directory (/) by setting the following line:
sudo nano /etc/apache2/apache2.conf
Add/edit the following line:
Options None Order deny,allow Deny from all
This is what the code does:
Options None: This will turn off all options.Order deny,allow: The order in which the allow and deny commands are applied.Deny from all: This will deny a request from all to the root directory.
Save the file and restart Apache.
Keep Apache Up to Date
New Apache updates will contain new fixes and patches that will reduce the vulnerability of your Apache server, so it is recommended to use the latest version of the Apache server.
You can update your Apache to the latest version using the following command:
sudo apt-get install apache2 --reinstall
Conclusion
I hope this post will help you in securing your Apache server. You will find more advance security tips and tricks for securing the Apache server in my next post. Feel free to comment below if you have any questions.







