SSH (Secure Socket Shell) is a command line interface and protocol for securely getting access to a remote Linux server. It provides a secure and encrypted communication over a network and allows data to be exchanged over a secure channel between two servers. It is widely used by system admins to control and manage their web servers remotely. This tutorial shows you how to secure your SSH server.
Note: while the tutorial here is done on Ubuntu, the steps will apply for most Linux distributions.
Install and Update SSH
First, update your system and install necessary packages to your system.
To update the system and install the SSH server on the server and client machines, run the following command:
sudo apt update && sudo apt upgrade sudo apt install ssh
Configure SSH for Passwordless Login
There are two different methods of logging in to an SSH server: password authentication and public key authentication. Password authentication is a very basic method that is easy to use and crack. Using password authentication is very insecure, especially if a weak password is used. On the other hand, SSH keys provide an easy and secure way of logging into a remote server, and this method is recommend for all users.
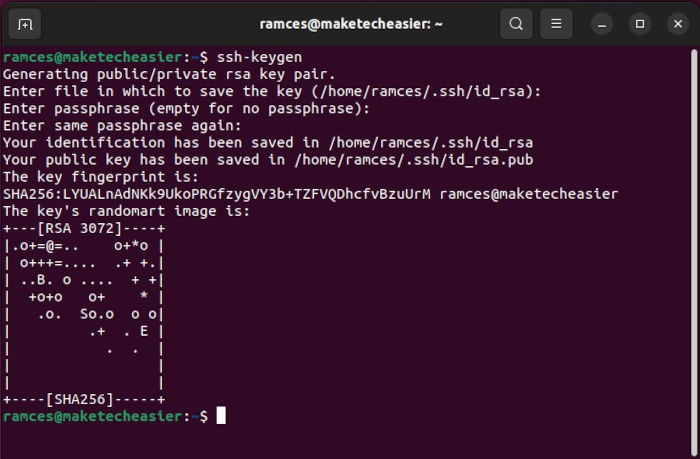
On your client machine, generate SSH keys with the following command:
ssh-keygen
Press the Enter key at every prompt. This will produce two files: “id_rsa.pub” (public key) and “id_rsa” (private key).
On your server, create the following folder (if it doesn’t exist):
mkdir -p ~/.ssh/
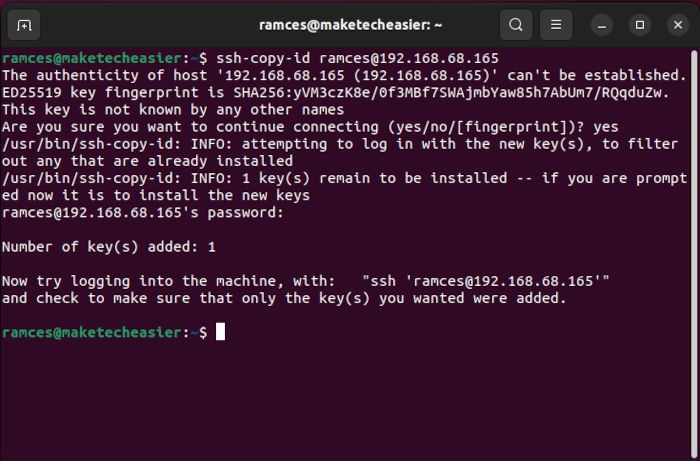
Back to your client machine, copy the SSH key to your server using the following command:
ssh-copy-id [email protected]
On your server machine, make sure that the “.ssh” folder has the right file permissions.
chmod 700 ~/.ssh chmod 600 ~/.ssh/authorized_keys
To test whether the public key authentication method works, try connecting to your SSH server from the client machine:
ssh [email protected]
If you are able to connect without entering a password, then the public key authentication method works.
Note: if you are using Windows, use the instructions here to generate SSH public/private keys.
Secure SSH Configuration File
The “/etc/ssh/sshd_config” file is the system-wide configuration file for SSH that allows you to set different options to improve the security of an SSH server. The default configuration in the config file is very insecure, so you need to edit it first and set proper options to improve the security.
To edit the “/etc/ssh/sshd_config” file, run:
sudo nano /etc/ssh/sshd_config
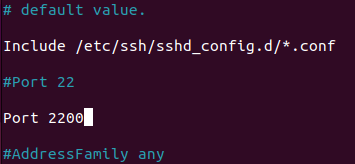
Change the SSH Listening Port
By default, SSH listens on port 22. Attackers use port scanners to see whether an SSH service is running or not. It is good practice to change the default port.
To change the default port to 2200, change:
Port 22
to
Port 2200
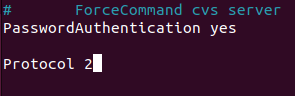
Only Use Protocol 2
Version 1 of the protocol contains security vulnerabilities. Protocol 2 is the default entry on Ubuntu.
Change the line shown below:
Protocol 2
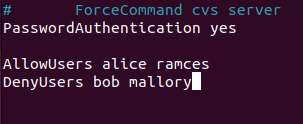
Limit User Access
It is necessary to allow only specific users to log in to SSH. It can improve your security. By default, this option is not available in the SSH configuration file.
To allow “user1” and “user2,” add the following line:
AllowUsers user1 user2
To deny “baduser1” and “baduser2,” add the following line:
DenyUsers baduser1 baduser2
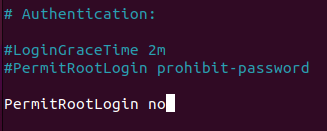
Disable Root Login
It is not necessary to log in as root via ssh over a network. Normal users can also use su or sudo to gain root level access. Most attackers will try to use root user to log in. It’s a big security risk, so it is good practice to deny the root login.
To disable root login, change the line
PermitRootLogin prohibit-password
to
PermitRootLogin no
Hide Last Login
You can hide who logged in last when a user logs in.
Change the line
PrintLastLog yes
to
PrintLastLog no
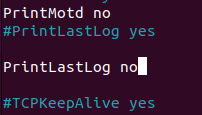
You can still view all active SSH connections with the methods in this list.
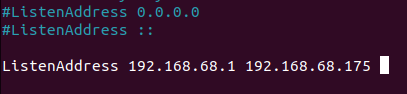
Restrict the Interface to Log In
By default, SSH will listen on all network interfaces. If you want to allow an SSH connection from a specific IP address, you can change the line:
#ListenAddress ::
to
ListenAddress 192.168.68.175
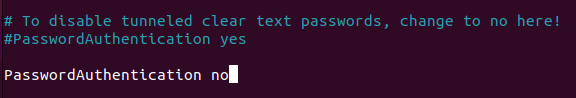
Disable Password Authentication
Using password authentication is a big security risk if a weak password is used. Using “ssh keys” is good practice. An “ssh key” can contain over 600 random characters and be difficult to break.
For this, change the line
# PasswordAuthentication yes
to
PasswordAuthentication no
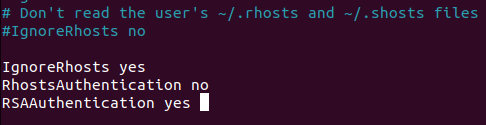
Disable .rhosts Files
The .rhosts files specify which users can access the r-commands (rsh, rcp, rlogin, etc.) on the local machine without a password. By default, an .rhosts file is disabled; if not, change the lines as shown below.
IgnoreRhosts yes RhostsAuthentication no RSAAuthentication yes
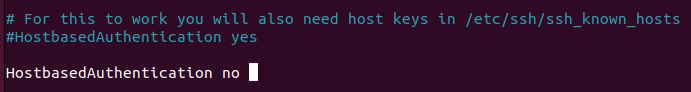
Disable Host-Based Authentication
SSH’s host-based authentication is more secure than .rhosts authentication. However, it is not recommended that hosts trust one another. By default, this option is disabled.
If not, change the line as shown below:
HostbasedAuthentication no
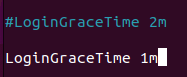
Set a Login Grace Timeout
The “LoginGraceTime” specifies how long after a connection request the server will wait before disconnecting. It is good practice to reduce it to 60 seconds.
For this, change the line
LoginGraceTime 2m
to
LoginGraceTime 1m
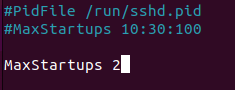
Set Maximum Startup Connections
Setting up a proper maximum number of concurrent connections to the SSH daemon can be helpful against a brute-force attack.
For this, change the line
#MaxStartups 10:30:100
to
MaxStartups 2
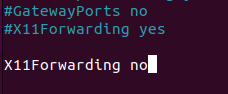
Disable Forwarding
The port forwarding technique is used by attackers to tunnel network connections through an SSH session to log into systems. Because of that, it is good practice to disable this option.
For this, change the line
X11Forwarding yes
to
X11Forwarding no
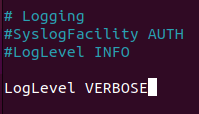
Log More Information
By default, SSH logs everything. If you want to log more information like failed login attempts. change the value of this to “VERBOSE.”
For this, change the line
LogLevel INFO
to
LogLevel VERBOSE
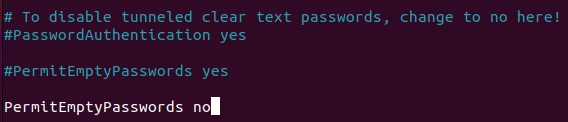
Disable Empty Passwords
It is necessary to deny users with empty passwords on your server. By default, PermitEmptyPasswords is disabled in Ubuntu.
If not, change the line as shown below.
PermitEmptyPasswords no
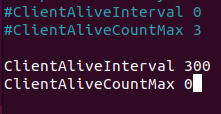
Set Idle Timeout Interval
By default, this option is not available in the default SSH configuration file, so it is good practice to set a proper idle timeout to avoid an unattended session.
For this, add the following lines.
ClientAliveInterval 300 ClientAliveCountMax 0
Strict Mode
This will prevent the use of insecure home directory and key file permissions. By default, this option is enabled.
If not, change the following line:
StrictModes yes
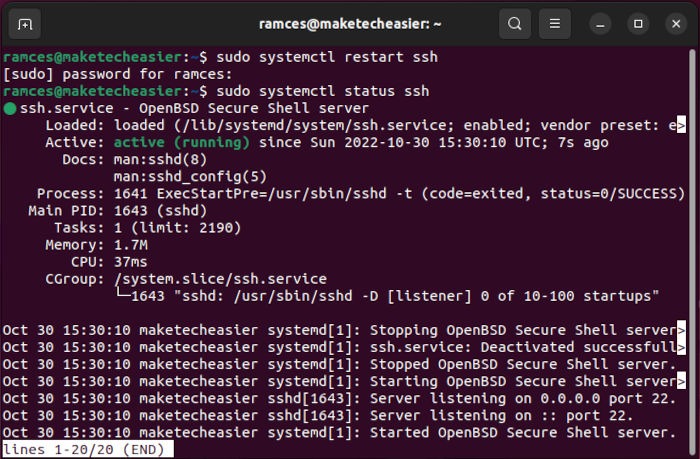
Save and exit the “/etc/ssh/sshd_config” file and restart the SSH server.
sudo systemctl restart ssh
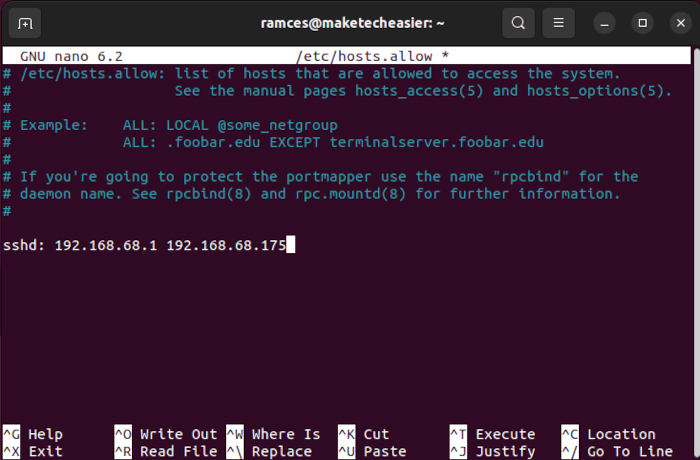
Secure SSH Using TCP Wrappers
A TCP wrapper provides host-based access control to network services used to filter network access to the Internet. Edit your “/etc/hosts.allow” file to allow SSH only from “192.168.68.1” and “192.168.68.175.”
sudo nano /etc/hosts.allow
Add the following line:
sshd : 192.168.68.1 192.168.68.175
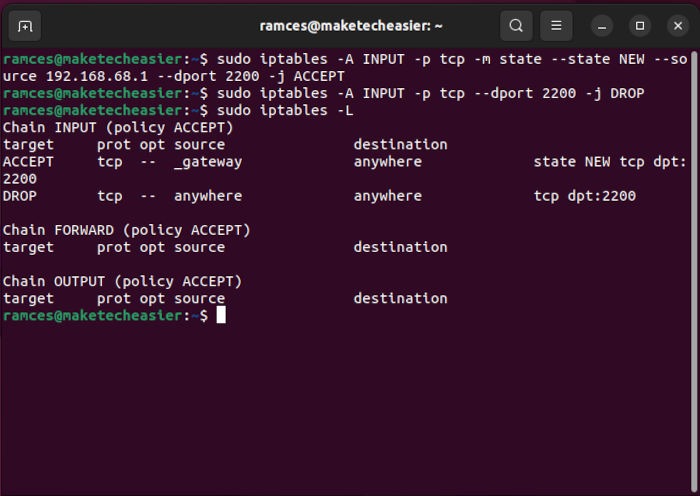
Secure SSH Using iptables
By default, an SSH server must only accept connections from your LAN or other remote sites. It is good practice to allow only specific IP addresses to access SSH and block access to SSH to unauthorized IP addresses.
To only allow SSH connections from “192.168.68.1,” set the rules in iptables:
sudo iptables -A INPUT -p tcp -m state --state NEW --source 192.168.68.1 --dport 2200 -j ACCEPT
Disable SSH connections from all other hosts by running the following command:
sudo iptables -A INPUT -p tcp --dport 2200 -j DROP
Customize SSH Connections on Local Machine
On your local machine (the machine you used to connect to the remote server), add a config file to simplify the command line option.
- Create a “config” (no file extension required) file in your “/home/user/.ssh” folder.
- Open the file and add the following lines:
Host sshserver
HostName remote.server.ip.address.com
Port 2200
User foobar
IdentityFile ~/.ssh/remote.server.key
Change the details of your own remote server’s configuration.
- Save and exit the text editor. To connect to your remote server, type the following command:
ssh sshserver
In addition to securing your SSH server, you should also make use of these tools to secure other parts of your server, too.
Frequently Asked Questions
The IP address of my local machine changed. Is it still possible to access my server through SSH?
If you have enabled IP filtering, then you won’t be able to access your server once your IP address changes.
What you can do to mitigate this issue is configure your remote server to accept a range instead of a specific address. Just configure your firewall to accept an IP range for SSH connections: sudo iptables -A INPUT -p tcp -m state --state NEW --source 192.168.1.0/24 --dport 2200 -j ACCEPT.
My server is filtering through the hosts file. Is it better to also use iptables to protect my system?
For the most part, you only need to set up a single filter for your SSH server. Using multiple IP filters will make it difficult for you to troubleshoot any issues that may come up during production.
Make sure that both your firewall and IP filter work hand in hand to protect your server’s network interfaces. For example, it is good practice to block any unused ports through your firewall and only filter connections through your “/etc/hosts” file.
I lost the private key for my local machine. Is it still possible to log in to my server through SSH?
No, you won’t be able to access your server if you lost the private key. The best way to deal with this issue is to access either the physical server or via a VPS root console. Re-enable Password Authentication by setting the PasswordAuthentication variable to “yes,” then restart your ssh daemon by running the command sudo systemctl restart ssh.
Image Credit: Unsplash. All alterations and screenshots by Ramces Red.








