SELinux can help you secure your server from malfunctioning processes or applications. Developed by the NSA (National Security Agency) to secure government devices from attackers, the security enhanced (SE) Linux architecture uses security protocols to restrict access to system resources. Find out how you can use it for your server.
Also read: What Is the Rc Shell and How to Install It in Linux
SELinux Architecture
SELinux is a kernel module that can be enabled or disabled by the system admin. As the access to files and network ports is limited following a security policy, a faulty program or a misconfigured daemon can’t make a huge impact on system security.
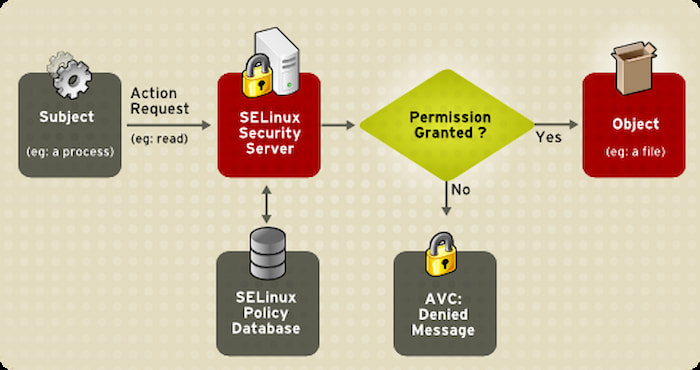
When an application or process requests file access in the SELinux system, it first checks the access vector cache (AVC). If permission is previously cached, then it returns with the file for the requested application. If the permission is not cached, then it sends the request to the security server. The security server checks all the security policies in its database. Depending on the security policy, permission is then granted or declined.
There is no concept of root or superuser in SELinux. The security of an unmodified Linux distribution without SE Linux depends on kernel correctness, all of the privileged applications, and their configurations. fault or bug in any of these components can create an attacking surface and compromise the system.
On the other hand, a modified Linux system with SELinux primarily depends on the correctness of the kernel and security policies.
Also read: How to Use Rm Command in Linux
How to Install or Enable SELinux
SELinux stands for Security Enhanced Linux. SELinux has been a part of the Linux kernel since 2003. Therefore, you don’t have to install it separately. In most desktop Linux distributions, however, it’s disabled by default.

SELinux has three main modes: Enforced, Permissive, and Disabled. Let’s discuss them briefly:
- Enforced: This activates and protects the Linux system using security policies.
- Permissive: It doesn’t enforce the security policies but logs everything. This mode is useful for troubleshooting purposes.
- Disabled: It deactivates SELinux. This option is not recommended, and if you re-enable the SELinux in your system, this leads to errors due to changes in labeling.
Note: Ubuntu is shipped with AppArmor, an alternative to SELinux. While SELinux is available on Ubuntu, it is not compatible with AppArmor and may break your system if enabled. If you really need to use SELinux in Ubuntu, make sure you disable AppArmor and do intensive testing (start with permissive mode first) before using it for production use.
- To activate SELinux in your system, you have to edit the “/etc/selinux/config” file. Open this file in your text editor.
sudo nano /etc/selinux/config
- Inside the config file, set
SELINUX=permissive. Press Ctrl + O and hit Enter to save the file and press Ctrl + X to exit the editor. SELinux is now activated in your system.
Note: if you try to enforce SELinux directly before making it permissive, it may mislabel files and processes and prevent you from booting.
- To automatically relabel the filesystem, make a file called “.autorelabel” in your root filesystem. Now when you boot your system, SELinux will automatically relabel your filesystem. To reduce errors, keep the
SELINUX=permissiveoption as it is in the config folder. After everything is relabeled, set SELinux toSELINUX=enforcingin “/etc/selinux/config” and reboot.
SELinux will be successfully enforced in your system.
Also read: How to Customize Your Linux Terminal Prompt Using Starship
How to Configure SELinux
SELinux is an architecture that allows system admins to control what can access the system resources. SELinux limits access to the system by using security policies. There are many ways to configure SELinux to protect your system, with the most popular being “targeted policy” and “multi-level security” (MLS).
A targeted policy is the default security policy. It covers a range of security policies, like file access, tasks, services, etc. Multi-level security (MLS) is generally used by government and large organizations, is very complicated to set up and requires a dedicated team to manage it.
You can check your current SELinux mode with the command getenforce and sestatus.
If you only need to change SELinux mode in the current session, you can run the following two commands.
sudo setenforce 0: Setting SELinux to the permissive mode for the current session.sudo setenforce 1: Setting SELinux to enforcing mode for the current session.
SELinux Policies
SELinux works as a labeling system. It associates every file, port, and process with a label. Labels are a logical way of grouping things together. The kernel is responsible for managing the label during boot.
SELinux policies can be managed by booleans. For example, let’s set boolean to a daemon called httpd. httpd is an Apache HTTP server daemon that we use to run web servers in Linux.
To list all the modules specific to httpd, run the following command in your terminal:
getsebool -a | grep httpd
Here, the -a option lists all the booleans, and we use grep to filter out boolean related to only httpd. Read this article to know more about grep in Linux.
The output from the above command looks like the below image.
httpd_builtin scripting --> on httpd_can_check_spam --> off httpd can connect ftp --> off httpd_can_connect_ldap --> off httpd_can_connect_mythty --> off httpd_can_connect_zabbix --> off httpd_can_network_connect --> off httpd_can_network_connect_cobbler --> off httpd_can_network_connect_db --> off httpd_can_network_memcache --> off httpd_can_network_relay --> off httpd_can_sendmail --> off httpd_dbus_avahi --> off httpd dbus sssd--> off
From the list above, we take the httpd_can_connect_ftp boolean and change its value. First, read the value of httpd_can_connect_ftp, whether it is on or off:
getsebool httpd_can_connect_ftp
Let’s set the value of httpd_can_connect_ftp to allow.
setsebool -P httpd_can_connect_ftp 1
Here, 1 represents allow or on. The -P tag is used to make the change permanent. If you list the booleans related to httpd again, then we can see the change in the httpd_can_connect_ftp value to on.
httpd_builtin_scripting --> on httpd_can_check_spam --> off httpd can connect ftp --> on httpd_can_connect_ldap --> off httpd_can_connect_mythty --> off httpd_can_connect_zabbix --> off httpd_can_network_connect --> off httpd_can_network_connect_cobbler --> off httpd_can_network_connect_db --> off httpd_can_network_memcache --> off httpd_can_network_relay --> off httpd_can_sendmail --> off httpd_dbus_avahi --> off httpd dbus sssd--> off
Also read: How to Set Up WordPress Using Docker in Ubuntu
How to Handle SELinux Errors
SELinux has 4 types of errors in general:
- The system has been broken: SELinux protects your system by restricting access, ut sometimes, this is not enough. If you get these errors, then your system may be compromised. Take necessary action as fast as possible.
- Bug in the policy: if there is a bug in the policy that needs to be fixed, this error appears.
- The labels are wrong: This error message appears during customization of labeling by the user or when auto labeling by SELinux goes south. There are many tools on the market to fix these label errors.
- A policy needs to be fixed: These errors originate when you make some changes to the system and don’t inform SELinux about it. You can fix this error using boolean or policy modules.
How to Disable SELinux
Disabling SELinux is never a good option for enterprise and government servers and public-facing devices that are very much prone to attack. But if you want to disable SELinux in your system, follow these instructions.
- Go to the SE Linux config file in “/etc/selinux” and change the SE Linux configuration mode from
enforcingtopermissive, then reboot your system. - Change SELinux mode from
permissivetodisabled.
After the next reboot, SELinux in your system is disabled and becomes a normal Linux machine.
Also read: How to Set Up a Firewall in Linux
Frequently Asked Questions
Is SELinux present in Android?
Yes, SELinux is implemented in Android from version 4.3. It enhanced the Android security to protect Android users from cyber attacks.
Is SELinux a firewall?
SELinux is not a firewall. The firewall controls the traffic between the computer and the network. While SELinux controls and governs the filesystem and network access of different programs inside the system, we can think of SELinux as an internal firewall to protect the system from its programs.
Is SELinux an operating system?
SELinux is not an operating system. It is a kernel security module that exists in the Linux kernel. It provides support for access control security policies and mandatory access controls (MAC). To call it an operating system, it needs more than the kernel itself. In most of the Linux-based operating systems, you can use SELinux.
Should you use SELinux?
If you are a sysadmin and know the Unix system you should use SELinux, as it enhances the security of your server and minimizes the attacking surface. If you are not very familiar with Unix systems, you can also use Apparmour. This is relatively easier than SELinux. If you are a home user and use Linux only on your desktop computer, there is no need to use SELinux. It will just give you a headache to configure and reduce your productivity.