Linux servers are the backbone of the modern Internet. Today, nearly every website and service that you can access through a web browser runs on a Linux distribution. Here we show you how you can secure your Linux server.
Note: this tutorial was created using a Ubuntu server, but it should apply for other Linux distributions too, including your local web server.
1. Remove the Root SSH Access
One of the quickest ways to secure your Ubuntu server is to secure your SSH daemon by disabling your Root SSH access. By default, the OpenSSH server allows any incoming connection to log in as the root user.
For example, running the following command in an insecure server will provide a login prompt:
ssh [email protected]
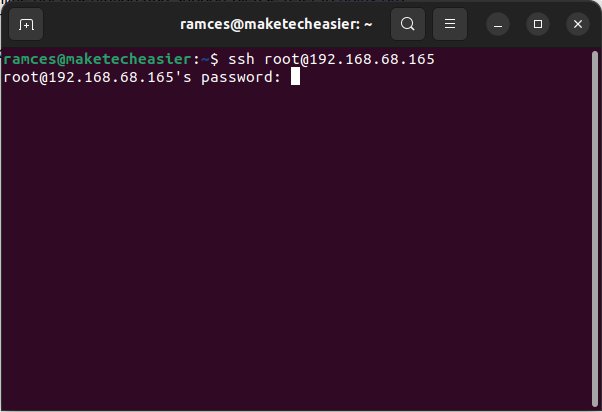
This can be an issue, as this leaves your server open and vulnerable to a password brute force attack. To fix this, log in to your Linux server and update your SSH daemon’s configuration file.
Once you are inside your Linux server, edit the SSH config file:
sudo nano /etc/ssh/sshd_config
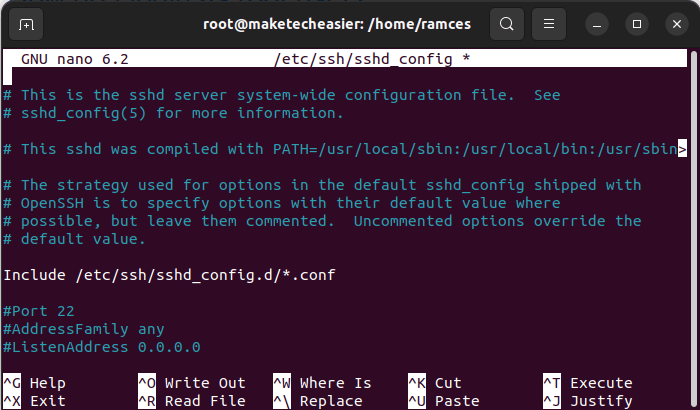
Search for the PermitRootLogin variable in GNU Nano by pressing Ctrl + W and typing PermitRootLogin.
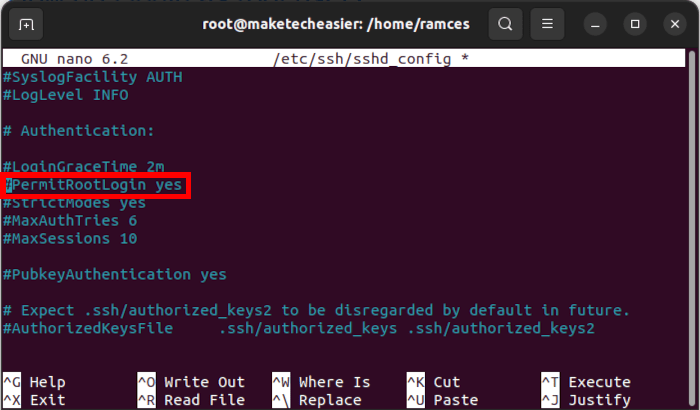
Change the value of PermitRootLogin from “yes” to “no,” then save the file by pressing Ctrl + o, then Ctrl + x.
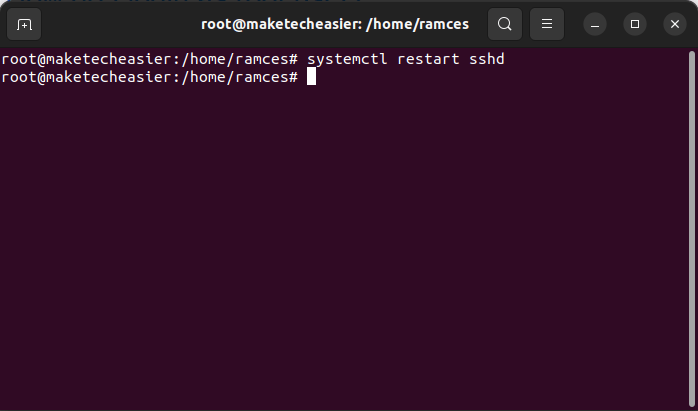
To apply the new setting, reload the server’s SSH daemon through systemctl:
sudo systemctl restart ssh
2. Use a Public Keypair for SSH Access
Another quick way to secure your Linux server is to create a public keypair between your local and SSH user account. This approach skips the password login process and automatically authenticates you to your remote server.
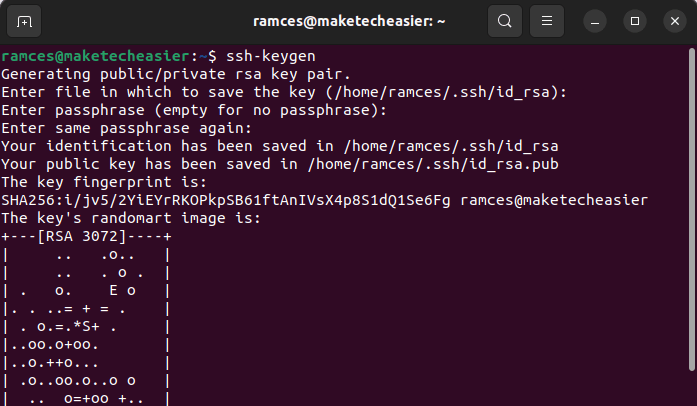
To create a public keypair, you need to first run the following command in your local machine:
ssh-keygen
The keygen program will ask you for a number of details about the key you want to make. You can safely leave these options on default by pressing Enter three times.
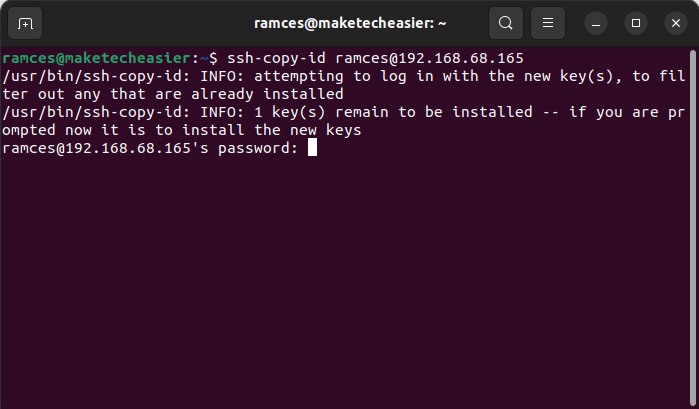
Export your new public keypair to your remote server by using the ssh-copy-id program. This is a simple utility that prepares both the local and remote machines for public key authentication over SSH.
ssh-copy-id [email protected]
Log in to your remote machine by running the following command:
ssh [email protected]
It is also possible to further secure your Linux server by removing the login prompt in SSH. Open your daemon’s configuration file with the following command:
sudo nano /etc/ssh/sshd_config
Find the PasswordAuthentication variable and change its value from “yes” to “no.”
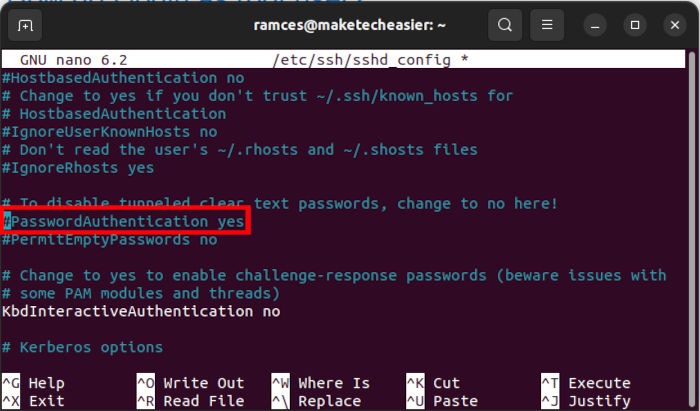
Reload your SSH daemon by running the following command:
sudo systemctl restart sshd
3. Harden the Firewall of Your Linux Server
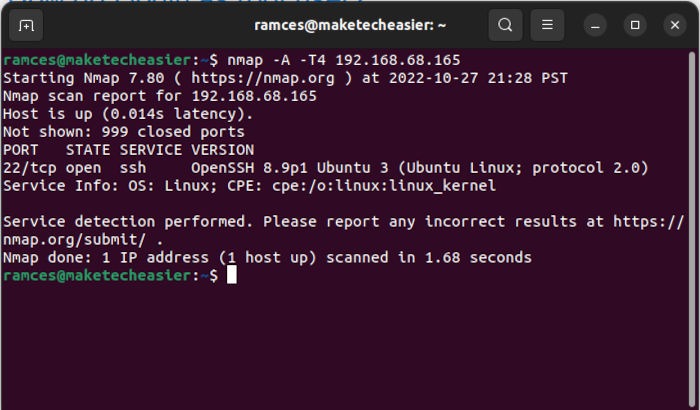
Aside from restricting SSH access, you can also improve your Linux server’s security by configuring your firewall. By default, a new Linux machine will accept all incoming connections from any port.
This can be an issue, as it leaves your server vulnerable to a port scanning attack. For example, a bad actor can scan your machine for any insecure ports and use that to find a suitable exploit.
One way to fix this is by installing ufw, a simple firewall client that can control the ports and addresses that are available to the outside world.
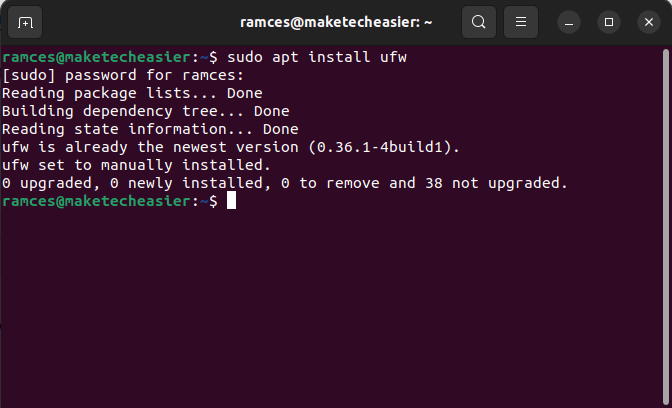
Run the following command to install ufw in Ubuntu:
sudo apt install ufw
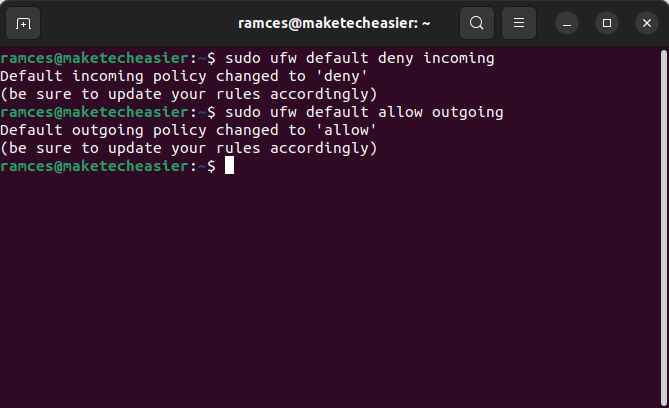
Set the default rules for ufw. These are the policies that your firewall will follow for any port that you do not customize. It is good practice to make sure that you are blocking all incoming connections:
sudo ufw default deny incoming sudo ufw default allow outgoing
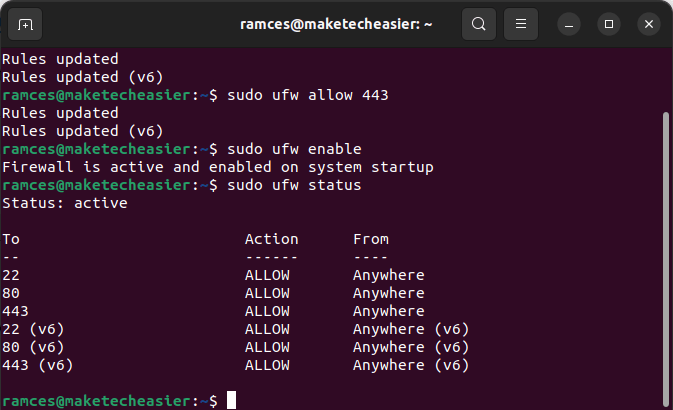
Configure your firewall for the services that you want to run in your machine. For example, running the following commands will allow you to log in through SSH and host a web server:
sudo ufw allow 22 sudo ufw allow 80 sudo ufw allow 443
Lastly, you need to enable your new firewall configuration by running sudo ufw enable. Further, you can check whether your firewall is online by running this command:
sudo ufw status
4. Create a New User for Every Service
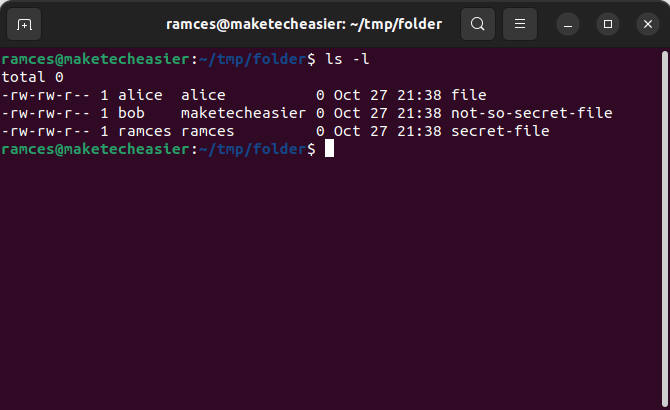
By default, every file and program in a Linux system belongs to a particular user and group. To modify the system, you need to have the right permissions for the right folders.
One way to increase the security of your Linux server is to create a new user account for every new service. This approach allows you to contain the privileges for each service to their own user account.
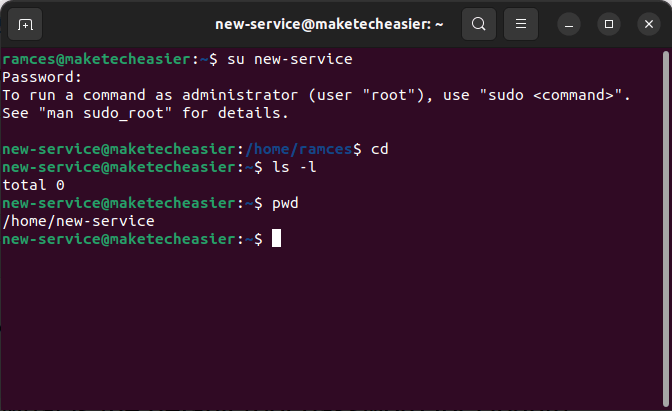
To do this, run the following commands:
sudo useradd -s /bin/bash -d /home/new-service -m -G sudo new-service sudo passwd new-service
- The
-sflag sets the system shell for the new user account. In my case, my new account uses Bash for its shell. - Both the
-dand-mflags set the default user directory for the new account. - The
-Gflag, on the other hand, adds the new account to any secondary groups that you specify. For example, adding the new account to the sudo group will allow it to run superuser commands. - The
passwdcommand allows you to set a new password for the new user account.
Once done, you can use your new user account by either logging off your current account or running su new-service.
5. Harden the Kernel of Your Server
The kernel is one of the most important parts of a Linux system and is the glue that links your machine’s hardware to your software. For example, compiling your own Linux kernel allows you to enable support for exotic hardware and features.
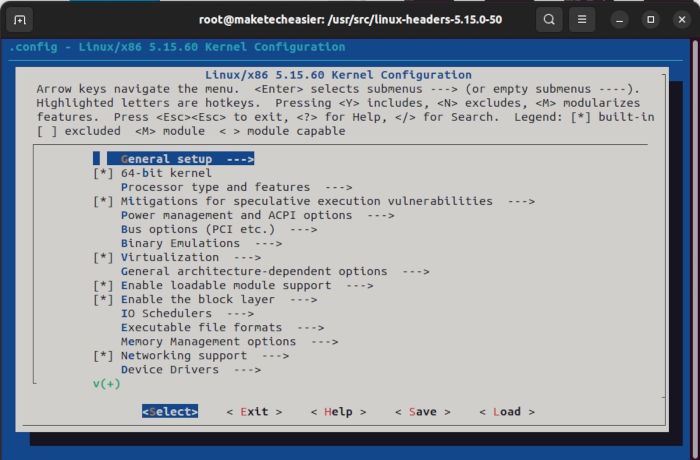
Aside from that, the kernel also serves as the root process of the operating system. Securing the kernel is one of the most vital parts of securing your Linux server.
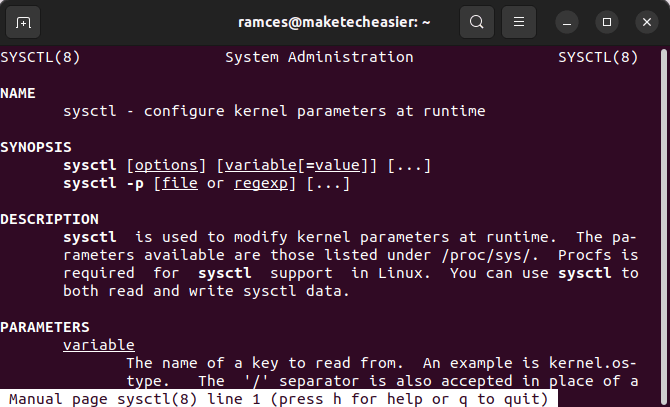
One of the quickest ways to secure your kernel is through sysctl. This is a built-in utility that allows you to tweak the Linux kernel’s runtime options.
However, it is important to note that sysctl will not cover the entire kernel hardening process, as securing the kernel will largely depend on what you need from it.
Knowing that, you can run the following commands to prevent your kernel from reporting any diagnostics information:
sudo sysctl kernel.kptr_restrict=2 sudo sysctl kernel.dmesg_restrict=1 sudo sysctl kernel.kexec_load_disabled=1
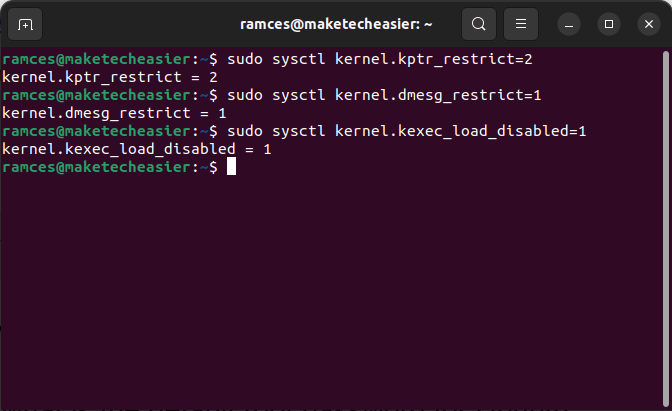
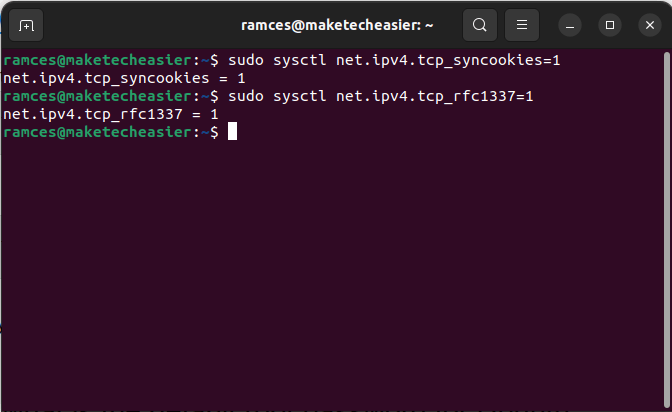
You can also run the following commands to tell your kernel to drop any fake connection requests made to your server:
sudo sysctl net.ipv4.tcp_syncookies=1 sudo sysctl net.ipv4.tcp_rfc1337=1
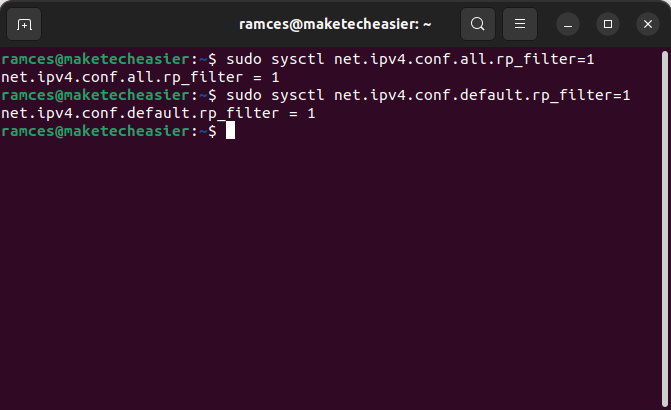
These commands, on the other hand, will force the kernel to validate each incoming connection to the machine:
sudo sysctl net.ipv4.conf.all.rp_filter=1 sudo sysctl net.ipv4.conf.default.rp_filter=1
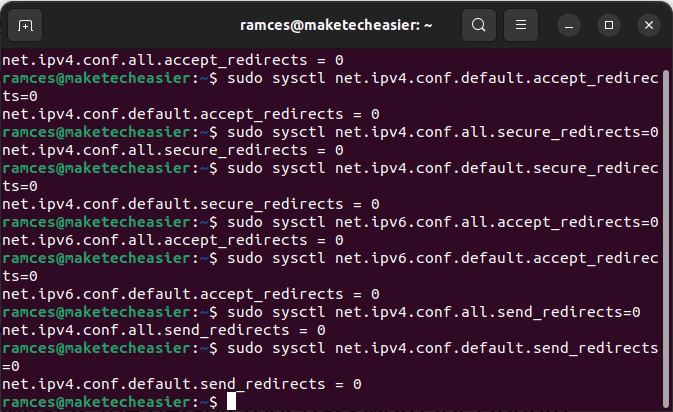
Lastly, the following set of commands will prevent any incoming connection to redirect the network traffic to a different gateway. Doing this will prevent your machine from falling foul to a man-in-the-middle attack.
sudo sysctl net.ipv4.conf.all.accept_redirects=0 sudo sysctl net.ipv4.conf.default.accept_redirects=0 sudo sysctl net.ipv4.conf.all.secure_redirects=0 sudo sysctl net.ipv4.conf.default.secure_redirects=0 sudo sysctl net.ipv6.conf.all.accept_redirects=0 sudo sysctl net.ipv6.conf.default.accept_redirects=0 sudo sysctl net.ipv4.conf.all.send_redirects=0 sudo sysctl net.ipv4.conf.default.send_redirects=0
Tips: other than the above tips, you can also make use of these open-source tools to secure your Linux server.
Frequently Asked Questions
I lost my local machine. Is it still possible to log in to my Ubuntu server through SSH?
For the most part, it should not be possible to log in through SSH if it is only using public key authentication. However, it may still be possible to access the SSH prompt if you did not disable the PasswordAuthentication variable.
Aside from that, you could either physically access the machine and update “/etc/ssh/sshd_config” or access the root console from your VPS provider.
My server has both iptables and ufw. Do I need to configure both for my firewall?
No! Both iptables and ufw are firewall software that take control over the same address ranges and ports. You only need to configure one of them to have a working firewall in your Linux server.
Is it possible to remove the superuser privileges of a user that I made?
Yes! It is possible to remove an existing user from a group. Use the usermod utility. For example, running usermod -G video new-service will remove the “new-service” user from the “sudo” group and add it to the “video” group.
Image credit: Unsplash. All alterations and screenshots by Ramces Red.








