SCP (Secure Copy) and SFTP (Secure File Transfer Program) are alternatives for FTP (File Transfer Protocol), which is useful for non-scheduled file transfers. All three can help accomplish moving files from one location to another over a network medium. However, FTP sends data in plain text, while the other two use the SSH File Transfer Protocol (SFTP) for communication.
What is SCP?
SCP is a non-interactive file transfer program that first appeared in 4.2 BSD. Historically, it used rlogin and SSH to transmit files between two computers. This made it prone to remote exploits since it ran commands on the remote host to start a data transfer.
File and directory transfers in SCP can either be between a local machine and a remote host or two remote hosts. This allows it to be more flexible when working with different UNIX-like distributions.
SCP can also be used with a wildcard character to aid in transferring multiple files based on partial-string criteria. Similar to direct transfers, these wildcards can also be used to send and receive files and directories.
Also read: How to Securely Transfer Files in Linux Using SCP
What is SFTP?
Unlike SCP, SFTP is a file transfer program that works similarly to an FTP prompt and a remote shell. It provides an interactive prompt that allows you to navigate a remote machine’s file system and manipulate its contents.
SFTP also uses several SSH features, such as compression or public key authentication, to connect to hosts and enter interactive mode. This makes it a robust remote filesystem browser for headless UNIX machines.
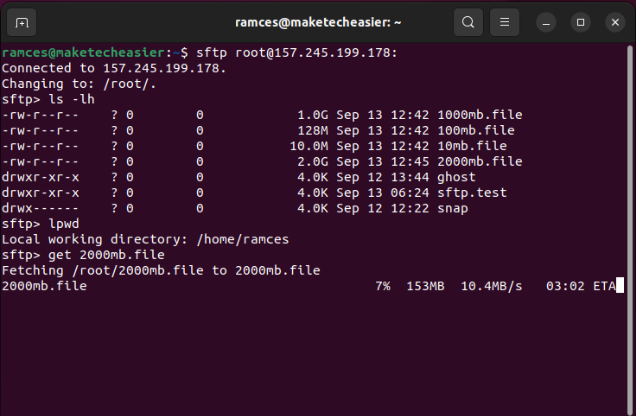
SFTP can also be used to automatically retrieve files if you use a non-interactive authentication method; otherwise, it retrieves them after successful interactive authentication.
Note: SFTP isn’t FTP over SSH but is a new protocol altogether.
Also read: How to Set Up an SFTP Server on Linux
SCP vs. SFTP: Which is Better?
A few similarities exist between the two file transfer programs. Both use TCP port 22 and run on SSH making them equal in terms of security. Additionally, both programs also support the transfer of large files, as they don’t have file size limits. The major differences between SCP and SFTP, therefore, can be seen in their specifications and functions.
Functionality
At its core, the basic purpose of SCP is to securely copy data between two machines. This is evident in the program’s basic syntax which requires you to provide a source and a destination for every file transfer. This makes it easier to work with for simple one-time file transfers.
Meanwhile, SFTP is a more complete file transfer client that provides a file browser along with multi-file downloads. These features make SFTP ideal for a user who needs to constantly transfer files to and from a remote host.
Winner: SFTP
Good to know: SCP and SFTP are not the only ones that can share files over the internet. Learn how to create your own cloud drive using ownCloud.
Speed
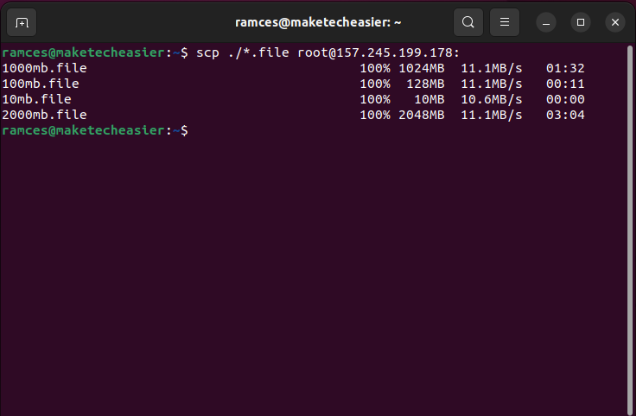
Since both SCP and SFTP use the SFTP protocol to encrypt and transport files, the two programs share the same raw transfer speed when either sending or receiving data. However, starting that transfer is a different story.
SCP is often faster at achieving the maximum raw transfer speed of a connection while SFTP lags behind as it tries to “spool up” its speed. Further, starting an SFTP transfer also requires you to go into a prompt and use FTP commands to upload and download files.
Winner: SCP
Security
Both SCP and SFTP rely on the SSH protocol for their base transport layer. This allows them to securely transfer data through a network using military-grade encryption.
Despite that, SFTP edges SCP out by providing the -f flag that allows you to immediately write any transferred data to the disk. Not only that, its command line interface also provides a number of utilities that allow you to update a file’s permission bits.
Winner: SFTP
Tip: Learn how to further secure your headless server by installing two-factor authentication on SSH.
File Size
Most modern versions of both SCP and SFTP in Linux are 64-bit binaries. This means that both utilities can hypothetically support up to 16 Exabytes of arbitrary data as long as the underlying filesystem also supports it.
That said, SCP can still present some problems with large files especially when working with older UNIX-like machines. This is mostly due to those systems running 32-bit versions of SCP which can only handle up to 4 Gigabytes worth of files at a time.
Winner: SFTP
Command Lines
SCP is non-interactive and can’t read command scripts, so everything has to be written on the command line. However, this also allows it to be run as part of larger shell scripts which can be helpful when automating system administration tasks.
SFTP, on the other hand, is interactive, so it can read commands from files. While this can also be useful for automation, it can be clunkier since it requires a set of commands that are different from a regular shell script.
Winner: SCP
Resuming File Transfers
SCP doesn’t support this function outright. This makes the program prone to repeating entire transfers on spotty and intermittent connections. Meanwhile, SFTP supports it on both the CLI prompt with its -a flag and through its command line client using the reget and reput subcommands.
Winner: SFTP
Which One Should You Use for File Transfer: SCP or SFTP?
While they have their similarities and differences, saying one is better than the other would not be fair. Both transfer files and have similar security features as they run on SSH. Ultimately, the utility you choose will be based on what’s best for your environment’s requirements.
Use SCP For
- When you want to transfer either a single file or directory between two remote hosts.
- When you want to automate transferring data over the network.
- When you are working with legacy UNIX-like systems with no SFTP support.
Use SFTP For
- When you are transferring multiple files across multiple directories from a single remote host.
- When you want to interact with a remote host’s filesystem without opening a new SSH session.
- When you want a reliable file transfer program that can work even in intermittent network conditions.
With that in mind, sending data between two systems is just the first step in understanding how computers communicate over a network. Learn how your Linux machine knows where to send its data by going through our hands-on DNS resolution guide using dig.
Image credit: Alejandro Escamilla via Unsplash. All alterations and screenshots by Ramces Red.








