You may have noticed that some software in your distribution is not the latest available. Most people are not even aware of this because, often, it’s not an issue. It’s only when you need some very recent features when it becomes an issue. Let’s say your favorite video editor had some code changes that improve rendering time by 20%. That may be something you want.
Long story short, most distributions that are considered “stable” or “long term support” will have (at least partially) older software in their repositories. But “rolling distros” have much newer software included, as they constantly pull in updates from upstream developers. Debian Unstable (codenamed Sid) is such a distribution. With some command-line magic, you can run Debain Sid inside your current installation of Debian Stable or Ubuntu.
Why Do this When I Can Just Add PPAs or Backports?
Personal Package Archives are very popular among users that want to add newer software to Ubuntu. But PPAs, backports (on Debian), and other similar methods interfere with your main installation. That means that they may upgrade bits and pieces of your main system. This increases the risk of something going wrong, incompatibilities between new and old software, new bugs introduced in the operating system and so on.
In contrast, the method in this tutorial isolates software in a separate space and doesn’t interfere with your main installation in any way. It’s somewhat similar to a container (minus the strong security features). Furthermore, Debian Sid includes much more software than you will find in PPAs or backports. However, everything has its limitations, so keep in mind the notes from the Debian Unstable page.
Create a Minimal Debian Sid Installation with debootstrap
Open a terminal emulator and install “debootstrap:”
sudo apt install debootstrap
Change to your home directory;
cd $HOME
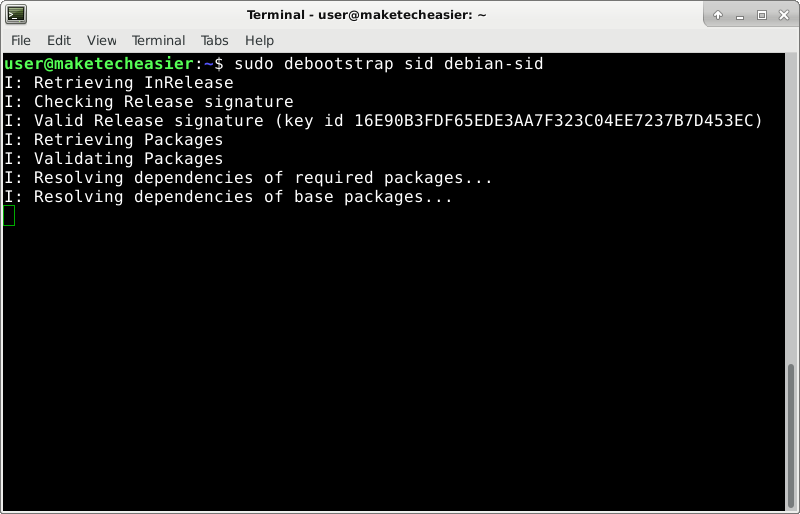
Start to bootstrap a new Debian Sid installation in the “debian-sid” directory:
sudo debootstrap sid debian-sid
The process will take a while, so wait a few minutes.
Prepare Your Debian Sid Installation
First, install a new package.:
sudo apt install systemd-container
Now, use a newly installed utility to “step into” your Debian Sid distro:
sudo systemd-nspawn -D debian-sid/
If you ever get stuck in this container, you can press Ctrl + ] three times in a row to forcefully exit. Use it only as an emergency method.
Add a new user. In this example the user is simply called “user,” but you can replace it with your desired username, although what this is called has no importance.
adduser user
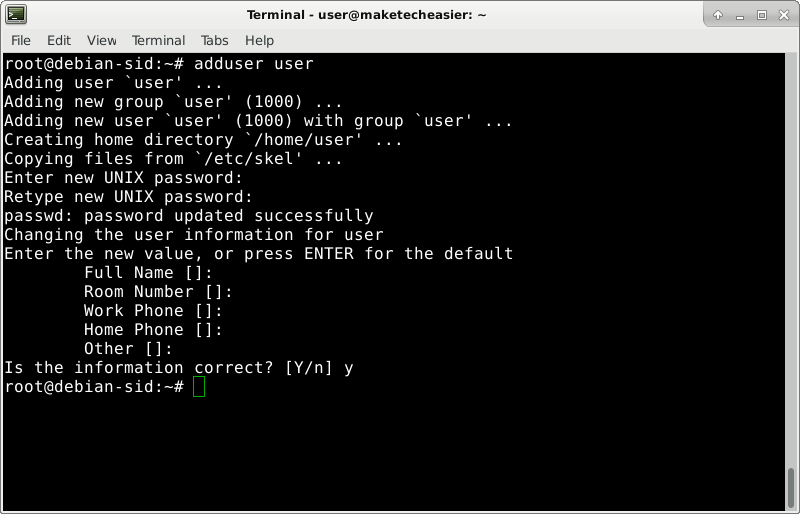
Choose a password for this user. No text will be displayed when you type. After you press Enter, type the same password again when prompted. The next details, such as “Full Name,” are not required, so you can simply press Enter at these prompts. Finally, type “y” when asked if the information is correct, and press Enter.
Install sudo:
apt install sudo
Add the user to the sudo group:
adduser user sudo
Set the hostname for your container. This will help you on the terminal, making it clearer when you are logged in to the container and when you are on your main system. It will help avoid mistakes.
echo debian-sid > /etc/hostname
Exit from your Debian Sid container:
exit
Virtually Boot Debian Sid Container with systemd-nspawn
A simple chroot command could have been used to step into this container, but systemd-nspawn has stronger isolation methods. This better prevents the container from “leaking out” into your main system accidentally. Furthermore, the utility includes a virtual boot switch. What this does is simulate a real boot of your Debian Sid installation. This launches some background processes that some applications may require to function properly (for example, dbus).
“Boot” your Debian Sid installation:
sudo systemd-nspawn --boot -D debian-sid/
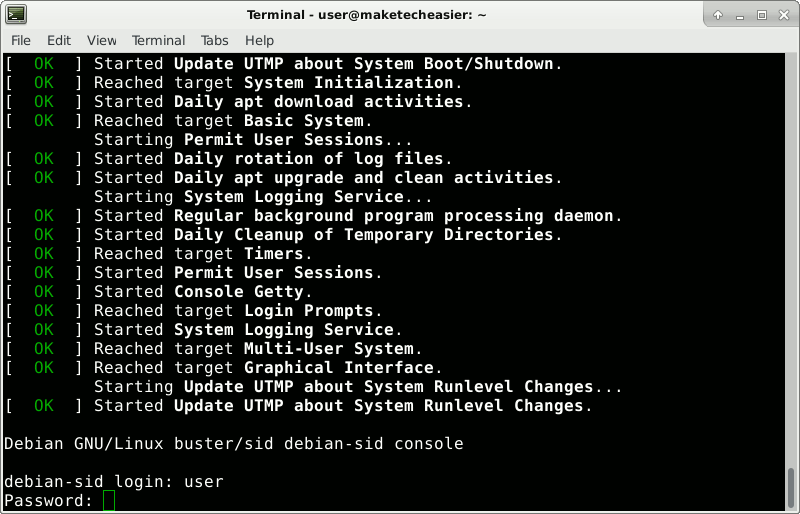
Log in with the username and password chosen earlier.
Install and Run Desired Software
Say you want to install the GIMP image editor:
sudo apt install gimp
Shutdown your container so you can reboot with all the new stuff it installed (dependencies like dbus):
sudo systemctl poweroff
Whenever you are done working with the container, this is the command you should use to quit.
GIMP is a graphical application, so it needs a graphical server. For technical reasons, this is not running in your container but is running on your main system. Run this on your main operating system (not in the container):
echo $DISPLAY
You may get an answer such as :0.0.
Boot the container again:
sudo systemd-nspawn --boot -D debian-sid/
After you log in, tell the container where it can find the display.
export DISPLAY=:0.0
Replace :0.0 if you had a different answer.
Also read: How to Switch to Xorg from Wayland in Linux
This only works with the Xorg graphical server. If you’re using Wayland, you may need to do the above with the WAYLAND_DISPLAY variable instead of DISPLAY. If that doesn’t work, temporarily use Xorg through your login manager’s options.
Now you can run gimp:
gimp
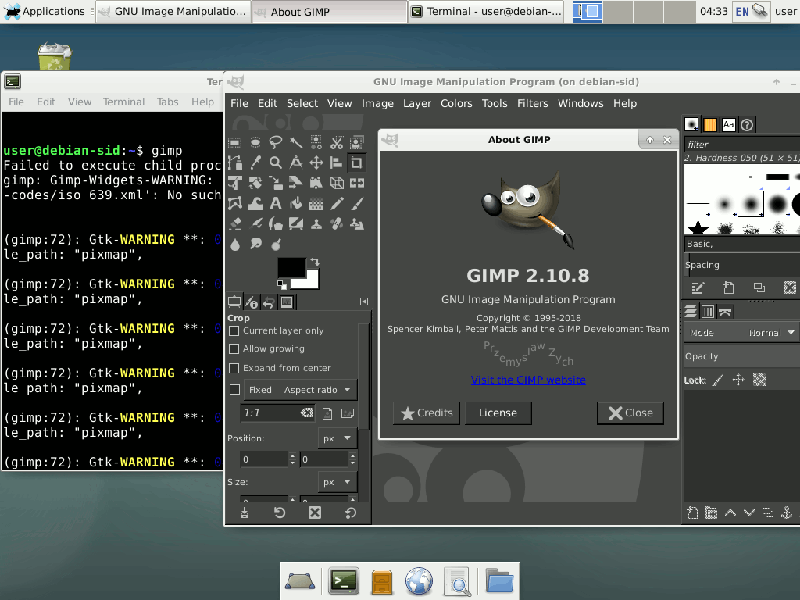
Don’t mind the warnings in the terminal. You get those on any system when you run a graphical app from the terminal. It’s normal output. You just don’t usually see it since you normally start applications from a graphical launcher.
Conclusion
It may be hard to get to this point, but once you’re done, it’s easy to install new software. Just boot the container, apt install, export display, run app. Once you have everything you need, you just have to upgrade occasionally. Do that with apt update && apt upgrade. Sometimes you may also have to use apt update && apt full-upgrade after the previous command.








