Portable Document Files (PDF) are the backbone of modern document distribution. With it, you can easily format any document and expect it to be readable on various devices.
The PDF standard also includes the ability to secure your documents through simple password-based encryption. However, this approach relies on you to keep track of every password for every PDF file that you have encrypted. This can be a problem if you want to maintain an archive of PDFs for a project or bookkeeping.
This tutorial shows how to remove the password of an encrypted PDF in Linux. In addition, we also show you how to recover a password for an encrypted PDF.
Tip: looking to add your signature in PDF while on the move? We have the solutions to sign a PDF document on your Android phone.
Removing the Password from an Encrypted PDF
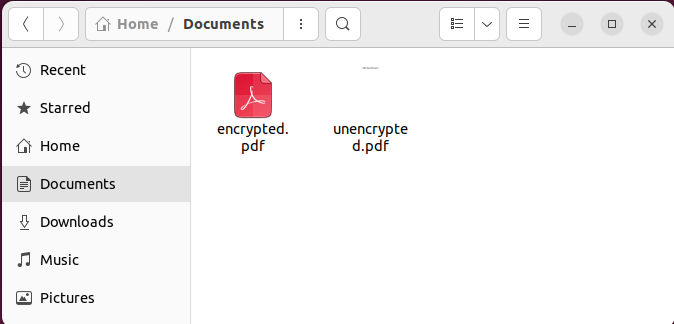
One of the easiest ways of removing the password from an encrypted PDF document is by “reprinting” a copy of it using your system’s document viewer. By default, the encryption algorithm that protects a PDF only works when the data is at rest.
This means that once the document is open, you can easily create an unencrypted duplicate of it by using your viewer’s “Print to PDF” option.
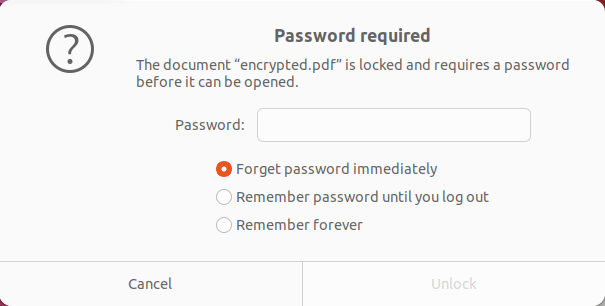
- Open the encrypted PDF with your PDF reader.
- The PDF viewer will ask you for the password of your document. Enter your password to open the document.
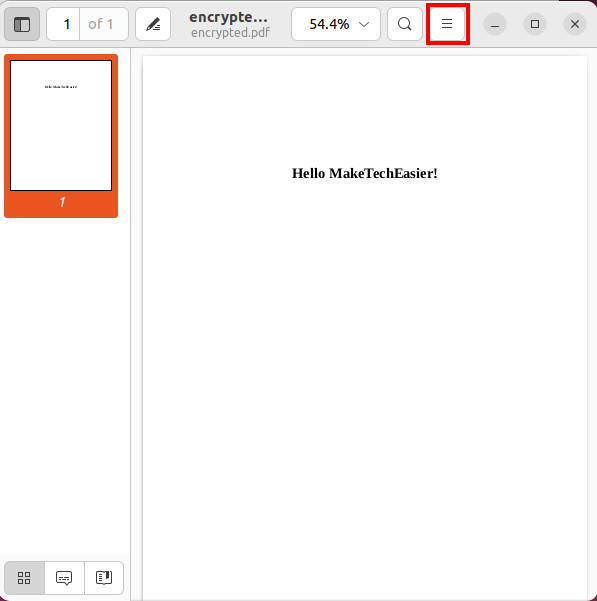
- Go to the Menu of the PDF reader.
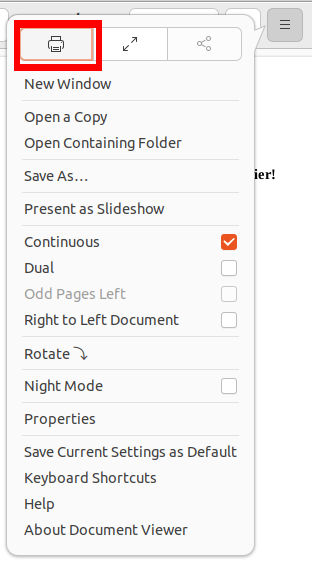
- Press the Printer Button (or Print option).
- Select the “Print to File” option on the Print Menu’s main window pane.
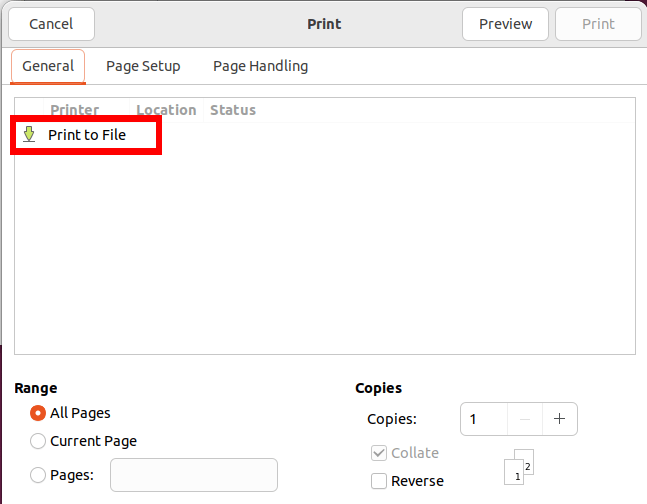
- Click the “PDF” radio button beside the “File” text box.
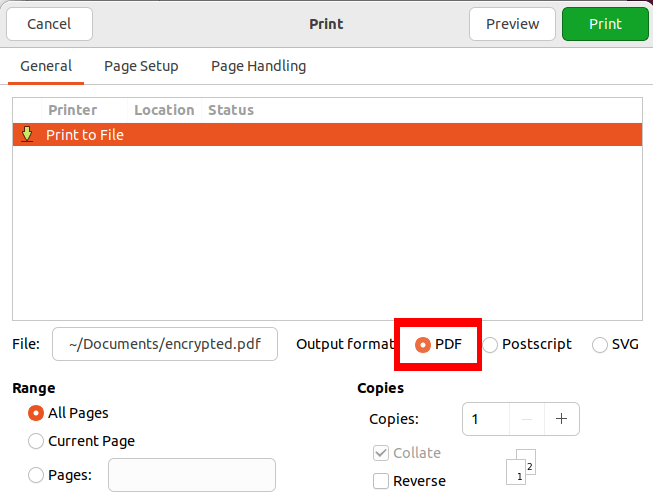
- Click the “Print” button to save your PDF document unecrypted.
Good to know: you can “print to PDF” from your Android phone, too.
Removing a PDF Password Using the Command Line
It is also possible to remove an encrypted PDF’s password straight from the command line. This can be useful if you want to create a script and automate the removal process.
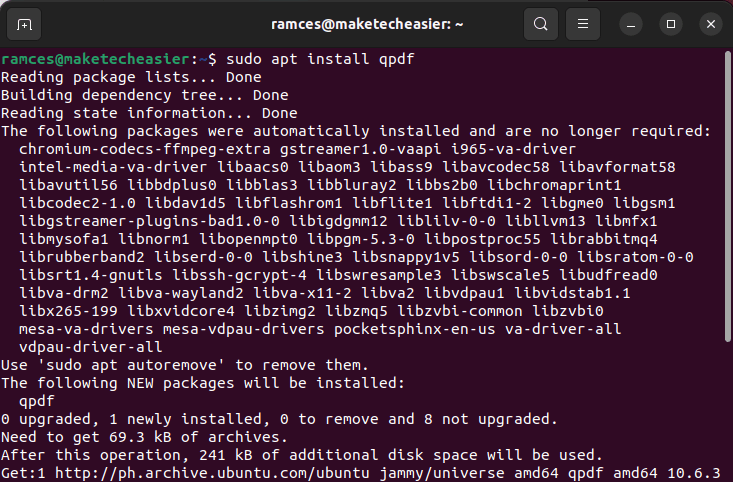
To do this, obtain qpdf. This is simple manipulation tool that can convert and edit a PDF’s internal properties. You can install qpdf in Ubuntu by running the following command:
sudo apt install qpdf
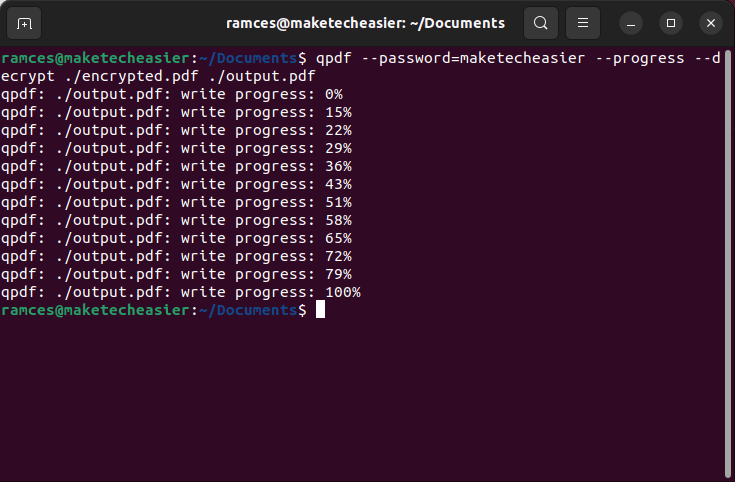
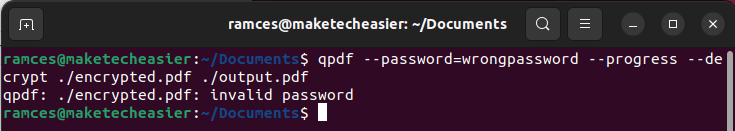
In the terminal, go to the directory of your encrypted PDF and run the following command:
qpdf --password=maketecheasier --progress --decrypt ./encrypted.pdf ./output.pdf
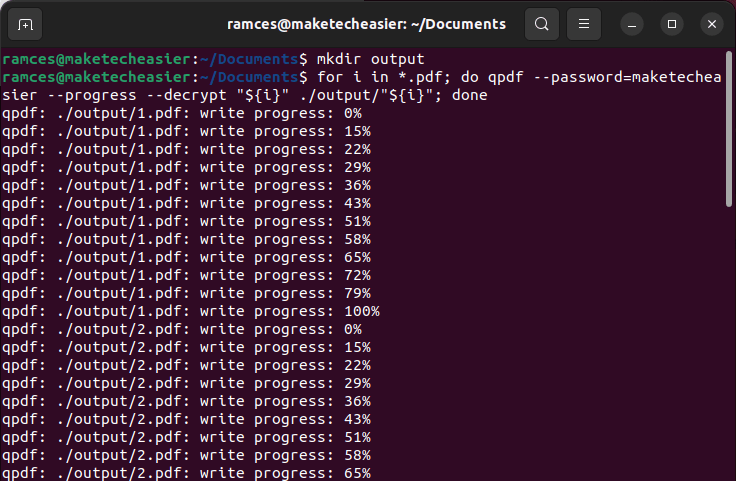
You can also create a simple shell script to automate the decryption of an entire directory:
mkdir ./output
for i in *.pdf; do qpdf --password=maketecheasier --progress --decrypt "${i}" ./output/"${i}"; done
Good to know: once you remove the password, you can easily combine multiple PDF documents into one.
Brute Forcing a PDF Password Using pdfcrack
While the previous methods will work on PDFs that you know the password to, there are instances where this is not the case. This can be a problem if you are dealing with an older PDF archive where you have lost the password.
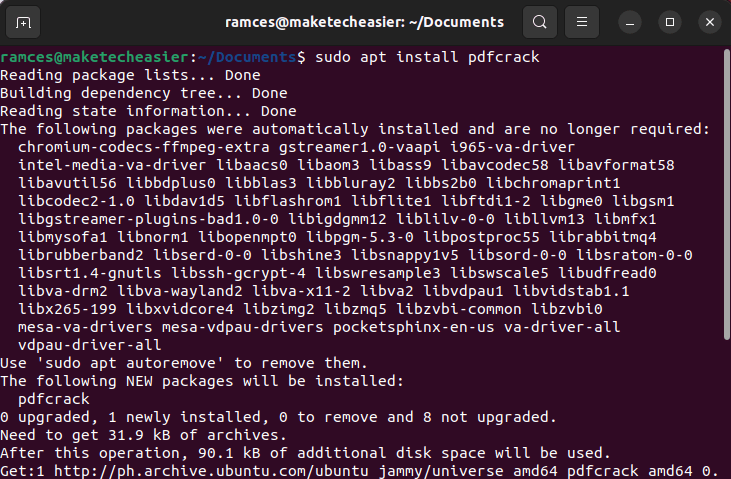
One way to fix this issue is to install and use the pdfcrack utility. This is a simple program that “cracks” a PDF document’s encryption by repeatedly guessing its password, either through a dictionary file or random text.
You can install pdfcrack in Ubuntu by running the following command:
sudo apt install pdfcrack
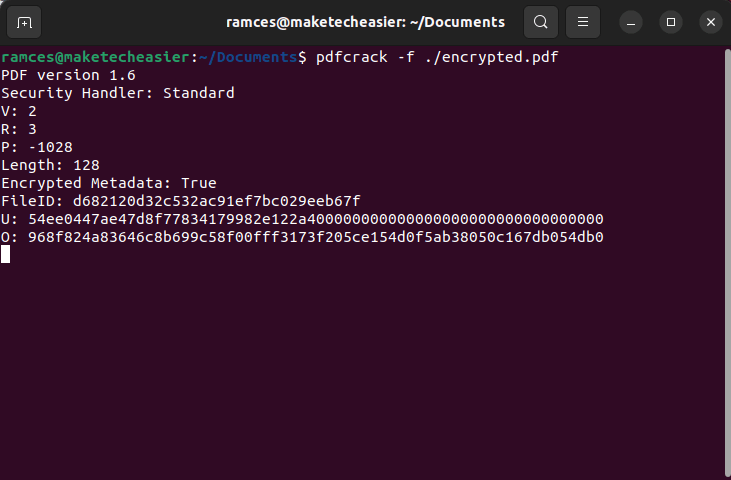
Go to the directory containing your encrypted PDF and run the following command:
pdfcrack -f ./encrypted.pdf
It is important to note that this process can take a long time to finish. For example, a long password with a mixture of symbols and letters can take up to an hour to crack.
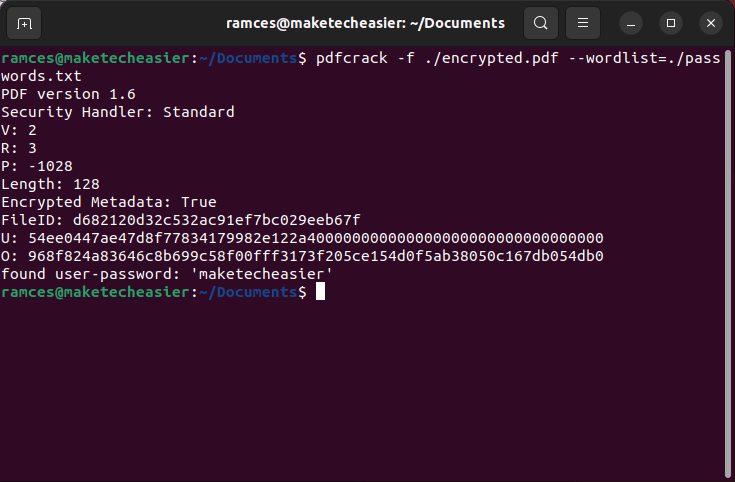
You can alleviate this issue by providing a dictionary file to pdfcrack. This is a plain text file that contains the common passwords that you might use in your documents.
You can run the following command to use a dictionary file with pdfcrack:
pdfcrack -f ./encrypted.pdf --wordlist=/home/$USER/Documents/passwords.txt
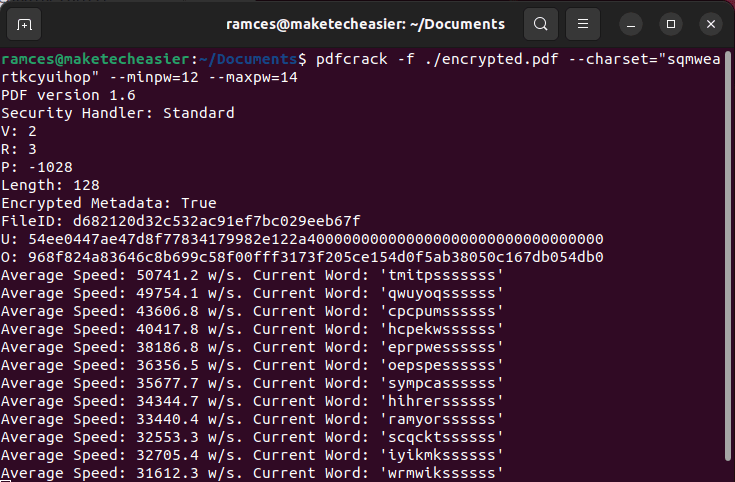
Lastly, you can restrict some of the parameters that pdfcrack uses while brute forcing. This is helpful if you have a vague idea of the length and type of your PDF’s password.
For example, the following command will tell pdfcrack to guess passwords that have the characters “sqmweartkcyuihop” and are either 12 or 14 characters long.
pdfcrack -f ./encrypted.pdf --charset="sqmweartkcyuihop" --minpw=12 --maxpw=14
Alternatively: if you want to generate hard-to-crack passwords, here are a few ways to do it online.
Frequently Asked Questions
Is it possible to duplicate the encryption of one PDF to another?
Yes. With qpdf, it is possible to “export” the encryption settings of one PDF to another. This is useful if you want to create a script that automatically encrypts a directory of PDF using the same password.
You can do this by running the following: qpdf ./new.pdf --copy-encryption-file=./encrypted.pdf --encryption-file-password=mysuperpassword ./output.pdf.
What are the downsides of using the “Print to File” function?
One of the biggest downsides of using this function is that it will remove any editable field and plain text inside the PDF. Your encrypted PDF will lose all text boxes inside it, and you will not be able to copy text from it.
I accidentally aborted pdfcrack. Is it possible to resume from the point where I left off?
By default, pdfcrack always creates a “state” whenever it exits accidentally. This is a file that contains the last password attempt that the program made as well as its progress through the current job. To resume your last session, run the following: pdfcrack -f ./encrypted.pdf --loadstate=./savedstate.sav.
Image credit: 123RF. All alterations and screenshots by Ramces Red.








