The Internet has literally put the world at our fingertips. It has changed the way we communicate, learn, and conduct business. Unfortunately, the Internet has also made it easier for shady individuals to take advantage of you.
While there may still be a few Nigerian Prince phishing scams floating around, today’s cyber criminals are using more sophisticated methods. Ransomware is one of the more serious threats lurking on the Internet. However, there are other more subtle dangers, like Cryptojacking.

Ransomware infects a computer and essentially locks the victim out until he or she pays a ransom, hence the name. It is obtrusive and compromises your entire computer, rendering it useless. However with Cryptojacking, you could be a victim and not even be aware of it.
What is Cryptojacking?
Cryptojacking is the unauthorized use of a computer’s CPU to mine cryptocurrency like Bitcoin, Ethereum and others. We won’t get into the nitty gritty of cryptocurrency mining here, but the process relies on a computer’s processing power. This makes cryptocurrency mining expensive due to hardware requirements and electricity costs.

Industrious miners (credit where credit is due) have compiled code that allows them to essentially hijack your computer to mine coins when you visit certain websites. When this occurs, your PC’s CPU usage spikes. This can cause performance issues, increased electricity consumption and even damage due to overheating. In addition to never seeing the fruits of your PC’s labor, you could fall victim and not even be aware of it.
How to Detect Cryptojacking on Your PC
Fortunately, there is a way to see if your PC is being used to mine cryptocurrency. As we mentioned above, crypto mining is CPU intensive, so if your PC is being used, you’ll see a significant spike in CPU usage. Luckily, there are a few simple, easy ways to check your CPU usage.
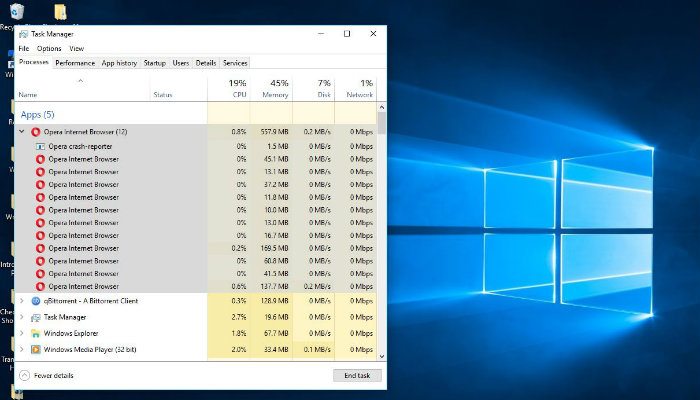
If you’re using a Windows-based PC, you’ll want to consult the Windows Task Manager.
1. To open it, simultaneously hit Ctrl + Alt + Delete. This will cause a blue screen to appear. Here, you want to select “Task Manager.”
2. In Task Manager have a look at the “Processes” tab and find your browser.
3. Click the arrow next to your browser to expand all of the tabs that you currently have open. This will break down the CPU usage of each tab. If you see one that uses significantly more CPU power than the others, chances are that site is using your PC to mine coins.
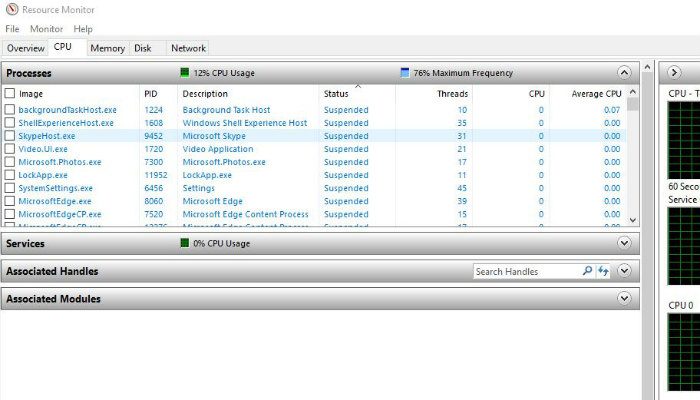
Alternatively, you can use the Resource Monitor tool bundled with Windows.
If you have a Mac, you can do the same thing by running Activity Monitor.
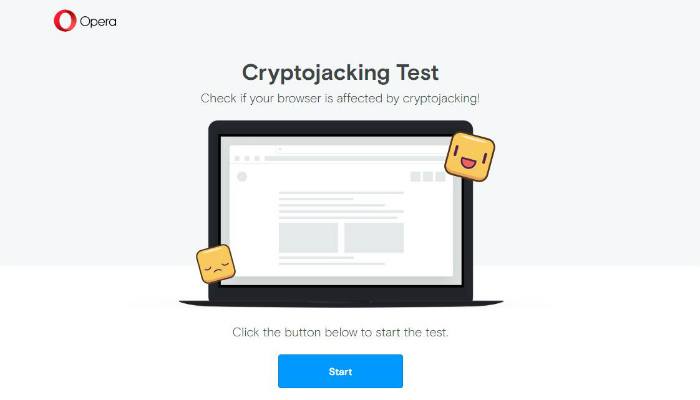
To do so, simply press Command + Space and search for “Activity Monitor.” Furthermore, if Chrome is your browser of choice, you can check its built-in task manager by going to “Menu -> More Tools -> Task Manager.” Finally, if all of this seems too complicated, the folks behind the Opera web browser have developed a web tool that can diagnose potential cryptojacking on your PC.
How to Prevent Cryptojacking
If you detect cryptojacking, it’s all well and good, but what can you do to stop it? Fortunately, there are a few potential solutions you can try. Cryptojacking occurs when you visit a website that runs a malicious script that hijacks your CPU. Luckily, you can install browser extensions that prevent this from happening.
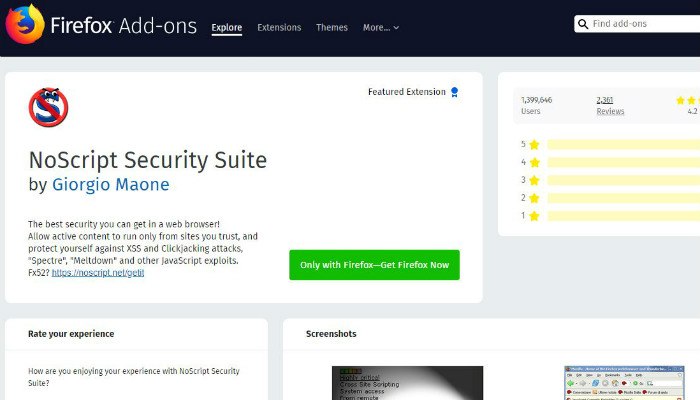
If you use Google Chrome, you can install the NoCoin or minerBlock browser extensions. Firefox users can install the NoScripts browser add-on. If the idea of using browser extensions isn’t appealing, you can use advertising blocking software like AdBlock to block the websites that you have identified as running cryptojacking scripts.
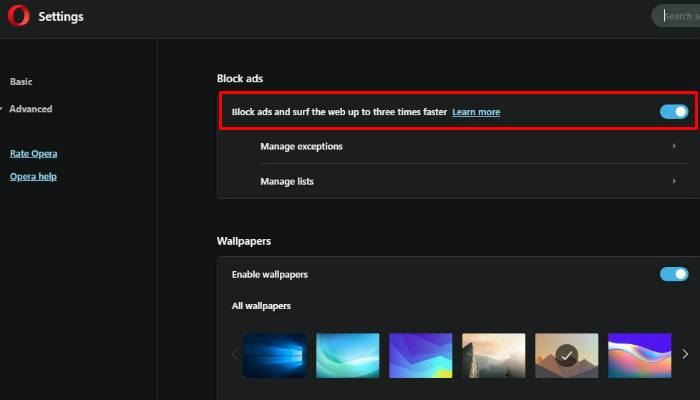
If you’re already using Opera as your browser (or don’t mind switching) you’re in luck. Version 50 and above of Opera’s web browser has built-in cryptojacking protection. All users have to do is enable the browser’s built-in ad-blocking tool.
Have you fallen victim to cryptojacking? What have you done about it? Are you aware of any other methods to prevent cryptojacking? Let us know in the comments!








