As we’ve covered in past articles, malware has become big money. With ransomware, keyloggers, bank trojans, and cryptojackers making their developers a lot of income, it’s important that they code their bugs to be as resistant as possible. With free antivirus rivalling (and even beating!) paid-for software, it raises the bar on security.
Hackers have one trick up their sleeve to skirt past security suites. Antiviruses depend on “signatures” to detect whether or not a program is malicious. When a new virus is detected, its signature is recorded and sent to everyone else’s antivirus software to help them detect it. In a way, the signature is the virus’s fingerprint on a police record; once it’s been “caught,” everyone else is informed to kick out this rogue software as soon as it appears.

But what if a developer can change the virus’s signature? That way it won’t be detected even if the antivirus has a log of the malware’s previous fingerprint. This means you don’t need to throw away code once it’s detected; it simply makes a new disguise. This is exactly what polymorphic and metamorphic malware does, and its future with AI could mean some nasty strains being spread around the Internet.
Polymorphic Malware
Polymorphic malware has a “core” that always does the same thing, no matter how many times it changes. It always performs the same actions and always attacks in the same way, but it keeps morphing the rest of its code to keep its tracks fresh. Polymorphic malware can be a little easier to identify than its metamorphic brethren, as the core can be sniffed out to identify the malware.
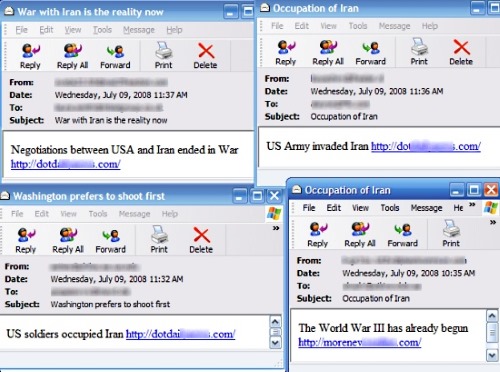
An example of polymorphic malware in the wild is the Storm Worm. It arrived on the scene in 2007 and got its name because its original method of attack was sending an email with the subject “230 dead as storm batters Europe.” Once the victim was infected, their computer would then generate a new strain of the malware every thirty minutes and send it out. The subject line would change over time (as seen above), but the core code of the worm stayed the same.
Metamorphic Malware
Metamorphic malware is a lot nastier. While polymorphic has a telltale core that can be detected, metamorphic malware tries to reorganise its entire code with each iteration. It reassembles the same logic and functionality that it had before but adds elements such as dummy code and reorganised functions in order to make it look different from its previous generations. This makes it a lot more difficult to nail and detect.
How AI Affects This
As we’re heading into a world where AI is getting better and better, a fight between the malware developers and the security programmers is underway. Both sides are using AI to enhance their side of their fight to get an edge over their competition.

With AI at the head of polymorphic and metamorphic malware, restructuring the code is quick and efficient. This means harder-to-detect malware that spreads further and evades more antiviruses.
Of course, with the security firms also having access to high-end AI, the fight goes both ways. Antivirus developers can program on-the-fly detection that doesn’t depend on signature detection. By using AI that makes logical decisions on how malicious software acts, it doesn’t need to rely on fingerprints – it just needs to spot the agent in action and quarantine it.
What Can Users Do?
It can be a little scary to hear about malware that dodges security, but it doesn’t change the fact that the best antivirus is your own common sense! Don’t download shady files, open suspicious emails, or click on strange links your friends on social media send you. Metamorphic malware can’t attack you if you never give it the chance to!
Mighty Morphers
With antivirus being prevalent across the Internet, malware developers need to up their game to bypass the security. Now you know about morphing malware and the threats it presents.
Do you think morphing code will get worse? Or will the security firms win the AI war? Let us know below.
Image source: Cybercrime wikifoto