Don’t let the name “Pretty Good Privacy” mislead you. PGP encryption is the gold standard for encrypted communication and has been used by everyone from nuclear activists to criminals since its invention in 1991. While the execution is complex, the concept is simple: you can encrypt text, making it unreadable to anyone who doesn’t have the key to decode it.
Also read: Why Encryption Is Not Working on Windows 11 Home, and How to Fix It
How Does PGP Encryption Work?
Imagine you want to send someone a letter but don’t want anyone except the recipient to be able to read it. The best way to do this is to write the letter in code, but you can’t send the code key along with the letter, as that’s not very secure.
PGP encryption gets around this problem using public key encryption. Everyone is assigned two keys: a public one that you can share with everyone and a private one, which you keep to yourself. What makes this system possible is that the codes only work one way. If Key A encrypts a file, Key A cannot reverse the process and decrypt it. Only its pair, Key B, can do that. Here’s how it usually works:
- Write down your message.
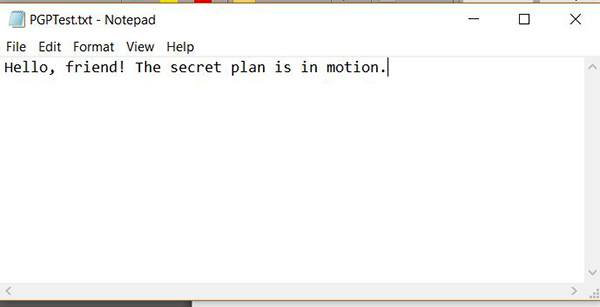
- Find your friend’s public key. He can email it to you, have it listed on a site, etc.

- Run a computer program that uses the public key to convert the message to code.

- Send the message. Anyone who intercepts it will only see gibberish.
- Your friend receives the message and runs it through his private key to decode it, restoring it to plain text.
This is a vastly simplified explanation of the process, but it covers the basics behind PGP encryption. If you want a more technical, mathematical explanation, Hackernoon breaks it down in much more detail.
What Can I Use PGP Encryption For?
PGP is most often used for encrypting emails, and there are many services to help you do that. ProtonMail is one great example of an encrypted email service that uses full end-to-end encryption. Beyond that, you can use your imagination: PGP can encrypt any text you need and can even be used on whole directories and drives. Investigative journalists often list their public keys online to make it easier for anonymous sources to get in touch with them, and sellers on darknet markets often use it to ensure their customers’ personal information stays secret.
Also read: How to Set up PGP Encryption in ProtonMail
How Do I Get Started?
Getting your own key pair is actually much easier than it sounds. You don’t need to understand anything at all about cryptography. You just have to figure out a few simple programs.
Install Encryption Program
- Download Gpg4win. This is a free (though you can donate or just choose $0 when prompted) set of encryption packages and tools. For macOS, check out GPG Suite. You can also add PGP to Linux. As I use Windows, I’ll go through the Windows process.
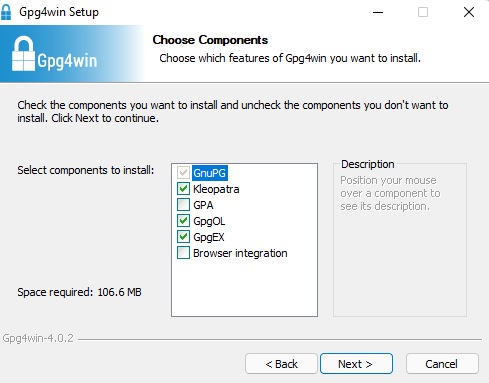
- Install Gpg4win. Make sure GnuPG (the actual encryption package) and Kleopatra (a nice user interface) are installed. The other components are optional, but it can’t hurt to have them.
Also read: How to Use Bitwarden to Send Encrypted Text or Files
How to Generate Encryption Keys
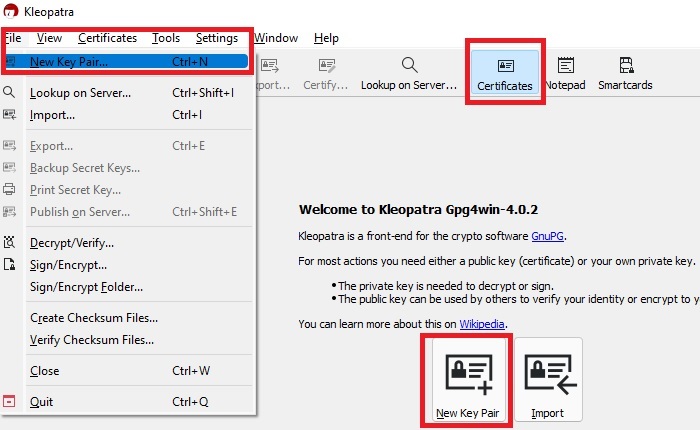
- Once everything is installed, find the Kleopatra program on your computer and open it.

- Go to the “File” tab and select “New Key Pair.” Or, choose “New Key Pair” under the “Certificates” tab. The second option is available only the first time you use the tool.
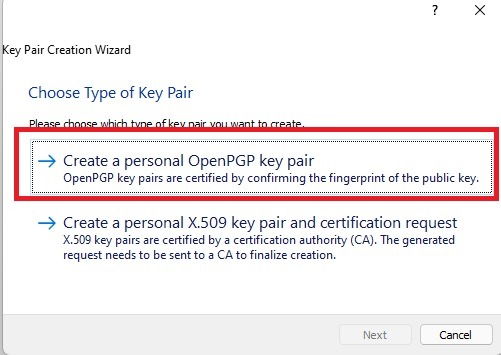
- Since you want PGP keys, select “Create a personal OpenPGP key pair.”
- If you want to attach your key to your identity, real or fake, you can enter that information here. Otherwise, you can skip this step. If you want to protect your key with a passphrase (which is more secure), check the “Protect the generated key with a passphrase” box.
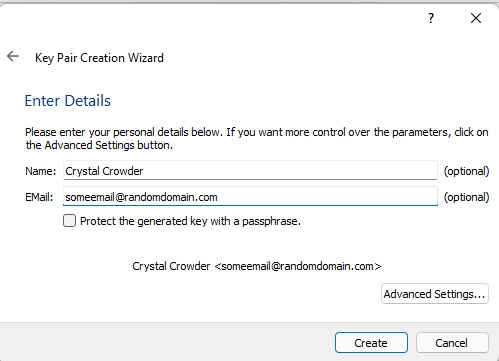
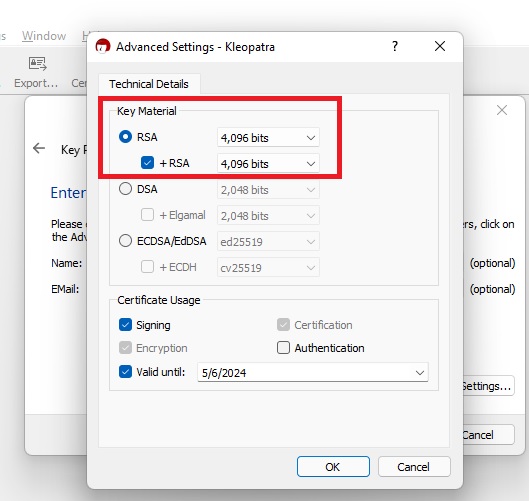
- From the same dialog box, visit “Advanced Settings” and make sure “RSA” is selected. Change the default 2048 to 4096; this level of encoding makes your encryption pretty much impenetrable and doesn’t really slow you down during normal use.
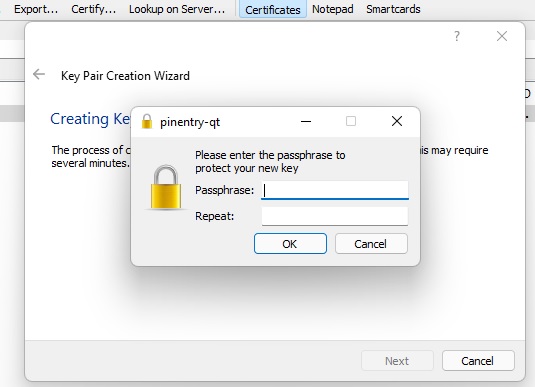
- Click “OK” to exit this settings menu, then click “Create” to start creating your key. The program is now generating thousands of random characters to make your keys and will ask you for a passphrase. It’s unrecoverable, so don’t forget it! It’s best to use a password manager to back up the passphrase.
If you didn’t check the passphrase box in Step 4, you won’t be asked for a passphrase.
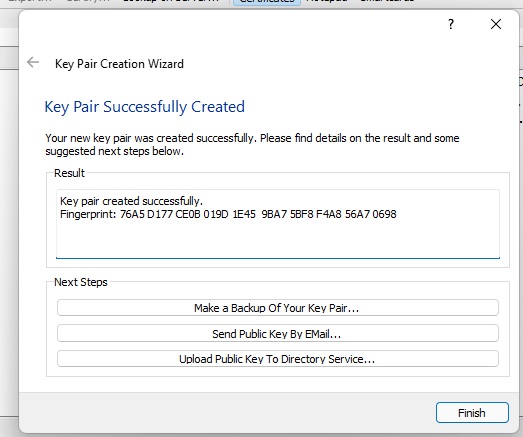
- You now have a public and private key! If you want, you can back these up in a separate file somewhere, or you can email/publicly upload your public key.
Also read: Cubbit Cell Review: Distributed, Secure and Encrypted Storage
How to Back Up and View Your Keys
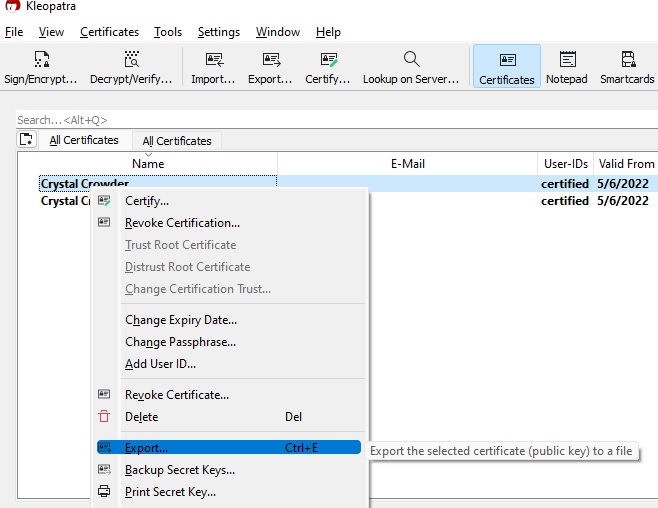
- You can generate a file with your public key in it by right-clicking the key and clicking “Export.” There are several ways to view your public key, but this makes it easy to access it whenever you want, without the need to use Kleopatra.
- Choose where to save the file (it will save as an .asc ASCII file.)
- Open any text-editing app, like Notepad. Any application that supports .asc files will work.
If you’re using Notepad, go to “File” and select “Open.” Navigate to your file to view it. You may need to select “All Files” at the bottom right. Alternately, navigate to your file in File Explorer, right-click it, and select “Open with.” Choose the application you want to use.
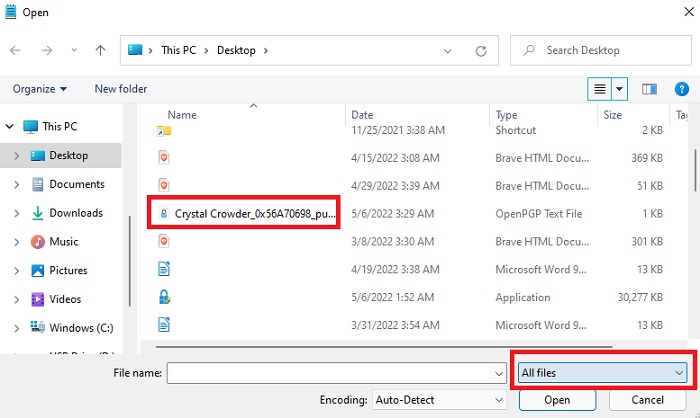
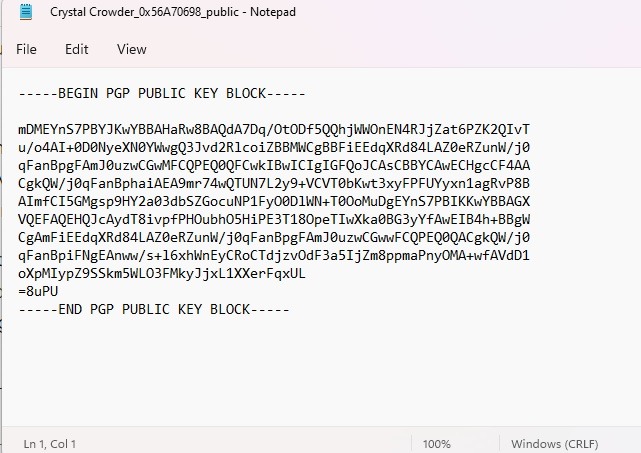
- Open the file with your text editor to see your public key! Beautiful, isn’t it?
- You can export your private key by following the same process, except select “Backup secret keys” instead of “Export” in Step 1. Make sure you store this in a safe location or just keep it inside Kleopatra; it’s perfectly accessible there.
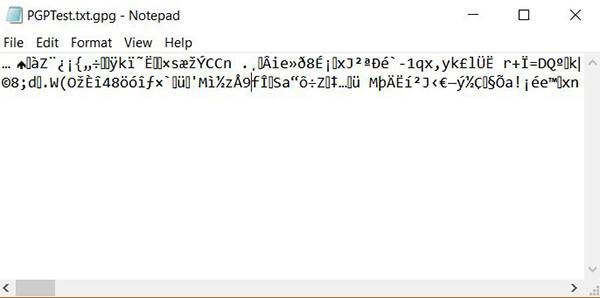
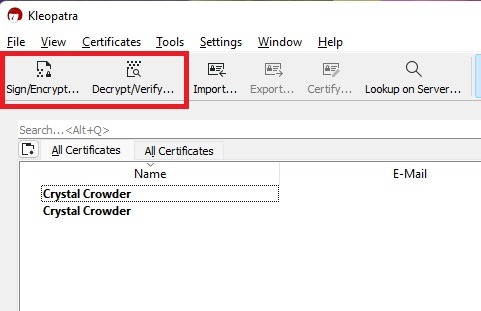
These public and private keys can be used with any program that works with PGP, and Kleopatra itself can actually encrypt and decrypt files using your keys. If you want to take them for a test run, try encrypting a text file with your public key and decrypting it with your private key. Use the “Sign/Encrypt” and “Decrypt/Verify” options in Kleopatra.
Also read: 9 WhatsApp Alternatives That Respect Your Privacy
Frequently Asked Questions
Can I change my passphrase once set?
Yes. You’ll need to know your original passphrase to do so. In Kleopatra, double-click the key you want to change and select “Change Passphrase.” You can also use this option to set a passphrase if you didn’t do so during the creation phase.
How do I revoke a key once created?
If your private key has somehow become public knowledge, you may want to revoke it so it can’t be used to access a file any longer. Double-click the key/certificate you want to revoke and select “Generate Revocation Certificate.” Once you do this, it can’t be undone.So, if you have an encrypted file you need to access with the key, make sure you decrypt it before revoking access. Otherwise, the file will remain encrypted unless you already have a decrypted backup.
How can I safely backup my key(s) once created?
Ideally, you’ll want to store them off your device. This ensures if anyone gains access to your device, they can’t access your keys. Plus, if your device becomes corrupted, you want a backup elsewhere. Consider using a secured USB device or external drive. For extra security, encrypt or password protect the drive.
Can I encrypt files to store in the cloud?
Yes. You can manually encrypt files using the method above. You can also use something specifically designed to encrypt cloud drives, such as Rclone.
Image credit: geralt via Pixabay