We have seen how to fully erase the contents of your hard disk, but what happens if all you want is to permanently delete one, two or a dozen files? This guide shows you some of the most popular solutions for complete file deletion in Linux.
Note: Most solid-state drives on the market today support TRIM for managing their free space, a feature in their firmware that reallocates their contents. Combined with the journalling file systems in Linux, like Ext3/4 and Reiser FS, the deletion beyond recovery of individual files can’t be guaranteed. The only solution in those cases is, unfortunately, a full nuke of all contents in an SSD.
1. Bypass the Trash
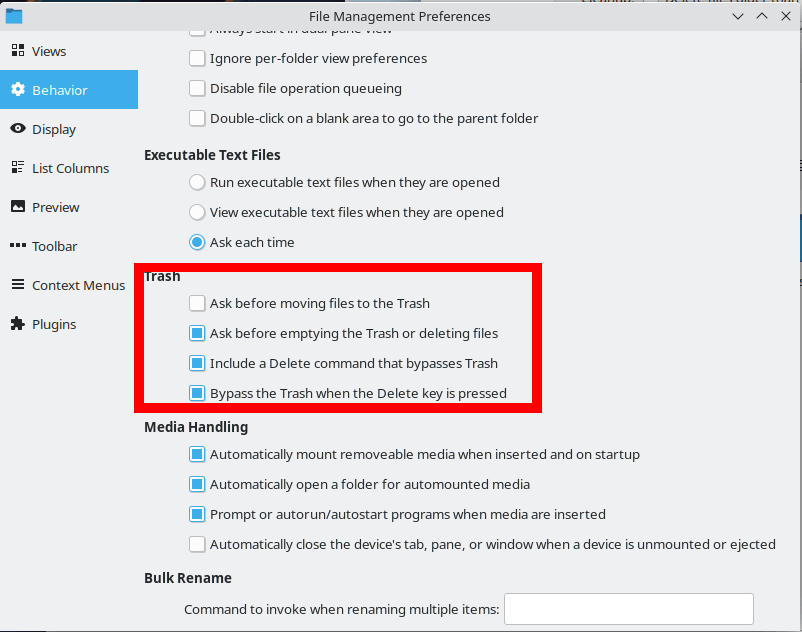
When you delete a file, it is moved to the Trash (aka Recycle Bin). If you wish, you can bypass the Trash folder. This way, your deleted files won’t linger in the trash and will be marked fully gone. While it is still recoverable, it is a step up from having them accessible (in the Trash).
Tip: if you still prefer sending your files to the Trash, you can still get the system to auto-empty your Trash on a regular basis.
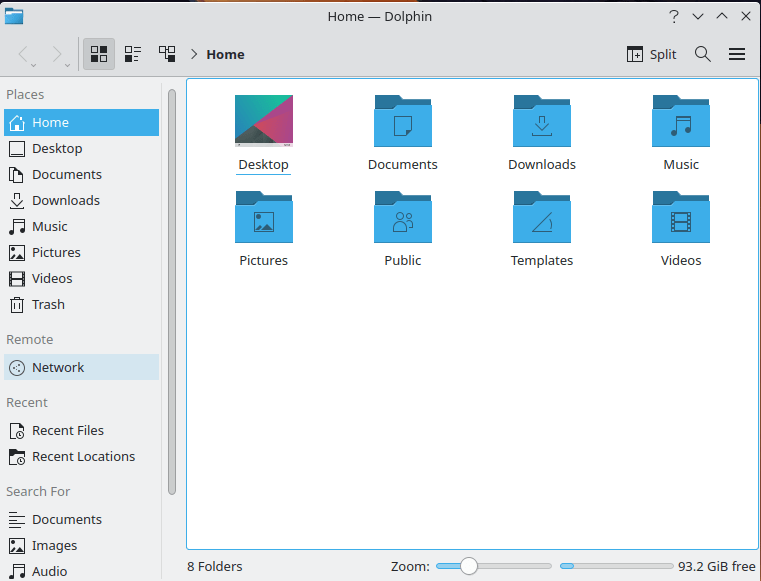
To delete files in a Linux distro like Kubuntu with KDE, run its default file manager, Dolphin. Click on “Menu -> Configure -> Configure Dolphin -> Trash” to reach the related preferences. There isn’t an option to fully disable the Trash, but you can use a neat trick that covers most bases: enable the Size limit and reduce it to the smallest value.
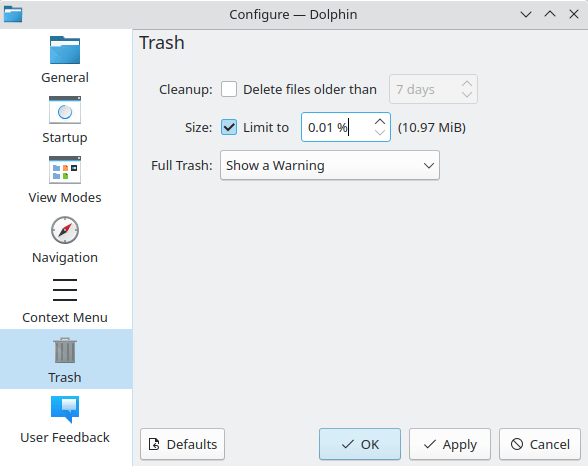
On our disk, this translated to 10.97 MiB. Dolphin will erase the contents of the Trash when it exceeds that value, and that would probably happen every other hour with typical desktop use. Other file managers like Nautilus or Nemo have options for you to bypass the Trash completely.
Pros
- Easy to do
- Gives you a grace period before permanently deleting files
Cons
- Does not remove any lingering metadata in the disk
- Does not scrub data from files
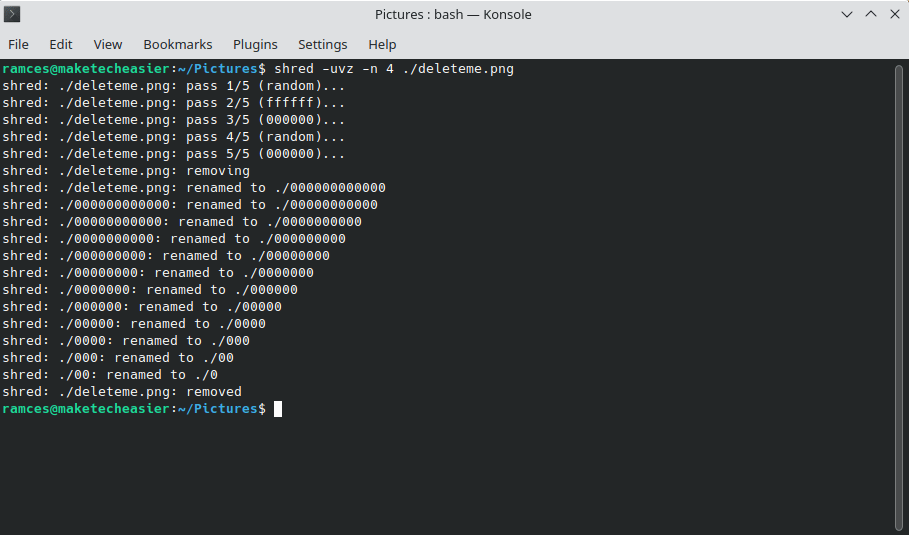
2. Using shred
If you’re running some variant of Ubuntu, shred is probably already a part of it. You can start using it immediately to fully delete any sensitive files in Linux that you want to send to oblivion.
If you wanted to permanently delete “image.png,” use:
shred -uvz -n 4 image.png
utells shred to remove the file before overwriting it.vdisplays verbose information.zfills the space that was taken by the data with zeros to further reduce any chance of recovery.-n 4translates to five deletion passes: shred does one pass by default, and with “-n,” you can specify how many additional passes you require for extra security. The general consensus is that five passes should be more than enough for most people.
To eliminate multiple files or the contents of a folder, use wildcards like:
shred -uvz -n 1 Pictures/images_0?.jpg shred -uvz -n 4 Pictures/*.*
In the first case, “?” would be a wildcard for a single character, and shred would delete files named “images_01.jpg” and “images_02.jpg,” for example.
In the second case, shred would wipe out all files in the directory “Pictures,” no matter their name or type.
Pros
- Will thoroughly delete a single file
- Can do glob matching to cover multiple files
Cons
- Some of the option flags are obscure
- Will take a long time to finish
Tip: learn how wildcards work by trying Regular Expressions on your machine.
3. Using dd in Single Files
The Data Definition (dd) program is another utility found in nearly every Linux distro today. However, unlike shred, one of the biggest advantages of dd is that it allows you to fine tune how you delete your files in Linux.
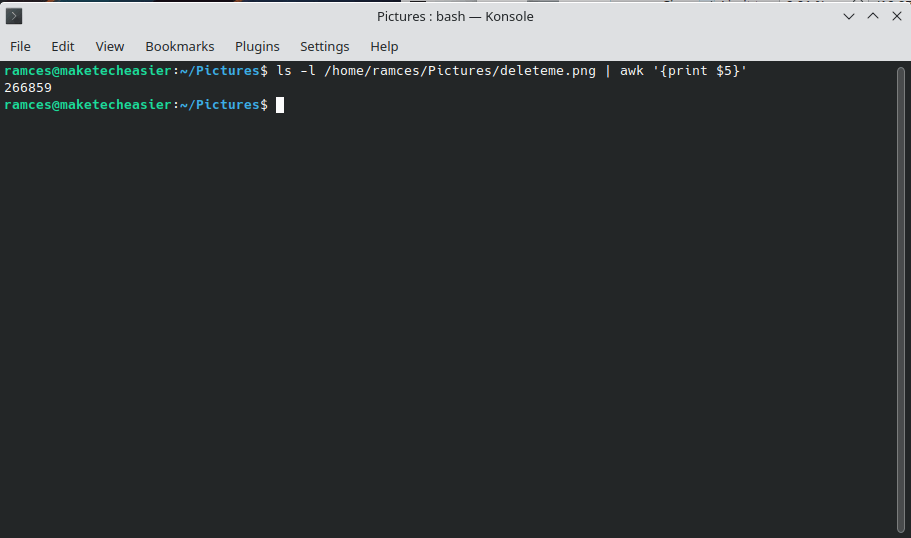
To use dd, you need to know the exact size of your file in bytes:
ls -l /path/to/your/file | awk '{print $5}'
You can run dd over your existing file. For example, this command will fill your file with null characters:
dd status=progress bs=your_file_size count=1 if=/dev/zero of=/path/to/your/file
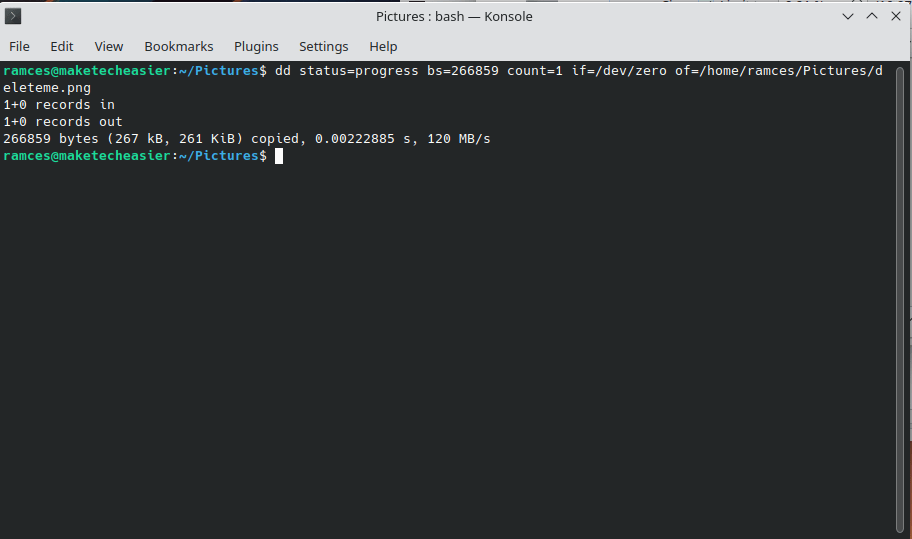
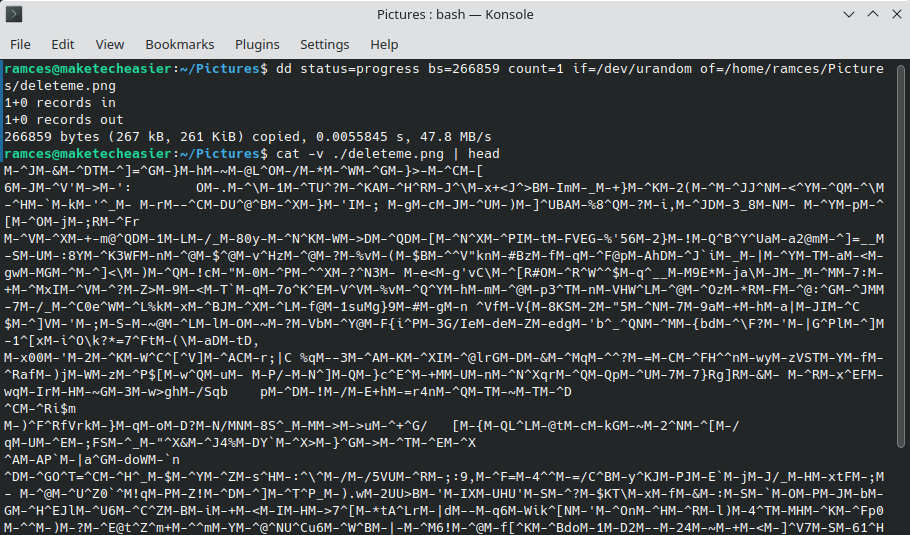
Aside from filling your file with null characters, you can also force dd to wipe your file with pseudo-random data:
dd status=progress bs=your_file_size count=1 if=/dev/urandom of=/path/to/your/file
You can now delete your file using the regular rm command:
rm /path/to/your/file
Pros
- Versatile – can do more than deleting files
- Can fine tune file deletion
Cons
- Syntax is antiquated, even for a command line program
- Requires a good understanding of block sizes
Good to know: if you regret deleting a particular file, learn how to recover deleted files in Linux.
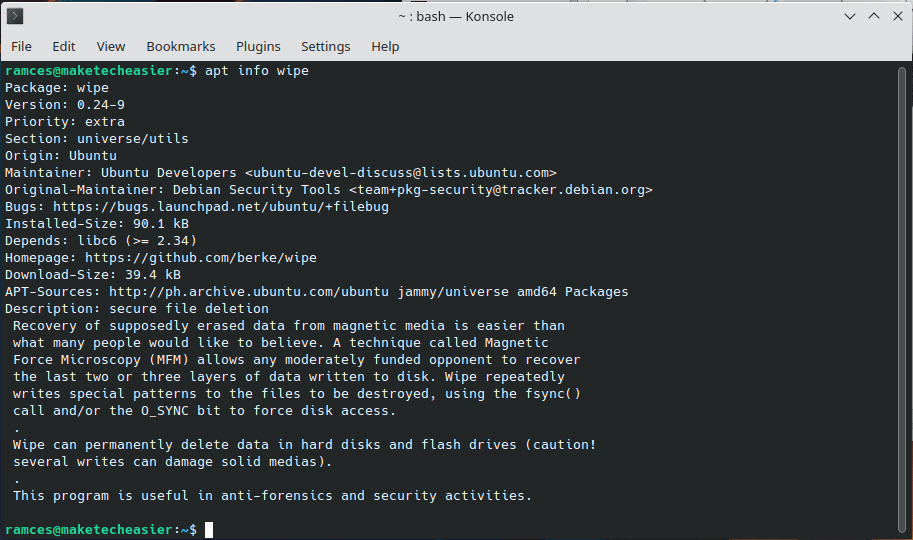
4. Using wipe
Wipe is another excellent alternative. Search for it in the software center of your distribution and install it from there or use:
sudo apt install wipe
Its use is almost as simple as shred’s, if not more so. To delete files in Linux using wipe, run:
wipe Pictures/deleteme.png
This can become annoying, as, by default, wipe uses too many time-consuming passes for extra security. Plus, it will request confirmation for the deletion.
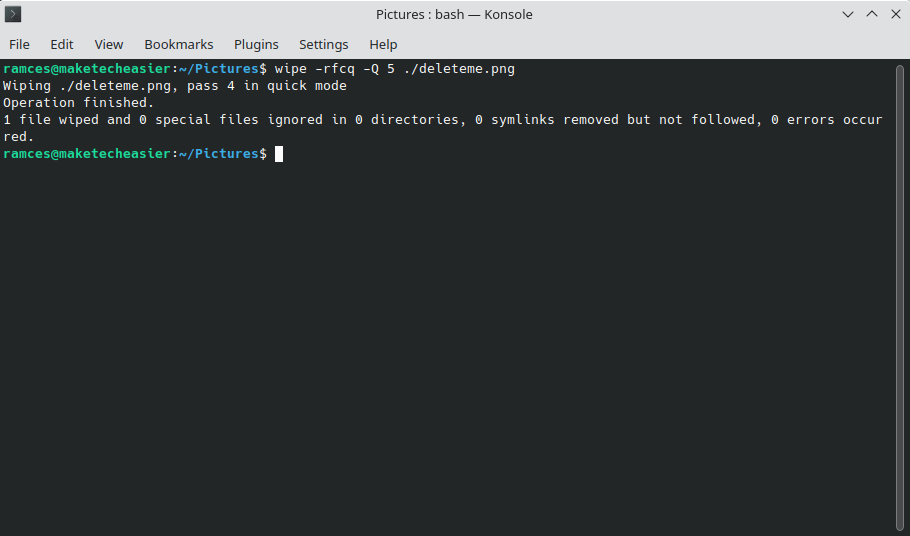
Use the f flag to get rid of the confirmation and r to recurse into subdirectories. c tells wipe to chmod if necessary (when a file or directory has no write permissions set), and q allows you to reduce the number of passes for a quicker deletion. When using q, notice that it’s lowercase. It can be followed by a capital “Q” specifying the number of passes you demand. For example, the previously simple command, with those tweaks applied, would change to:
wipe -rfcq -Q 5 Pictures/deleteme.png
Pros
- Easy to use, even with little command line experience
- Sensible and secure default parameters
Cons
- The default parameters could be too strict for most users
- May not work well with active journalling
5. Using Secure Delete
SRM is one of the tools in the Secure Delete suite that specializes in secure removal of data from your HDD. It’s held by many as the best tool for this job.
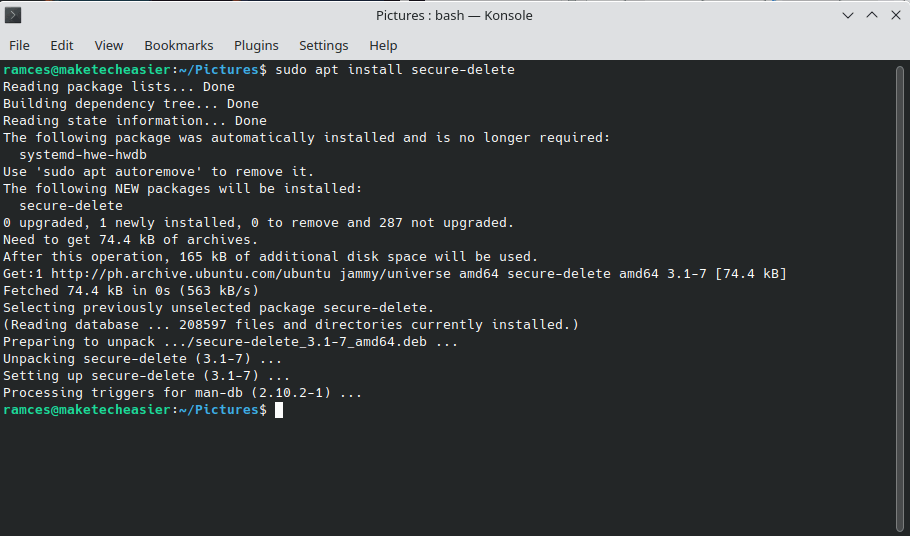
To install the full Secure Delete suite on Ubuntu and compatible distributions, use:
sudo apt install secure-delete
After, you can delete any file with:
srm Pictures/deleteme.png
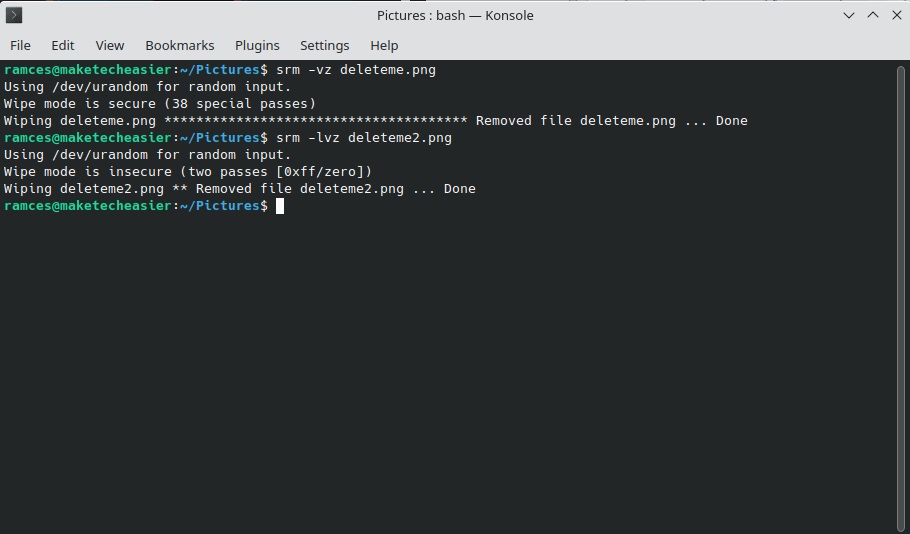
You’ll probably want to use the z flag that overwrites your file’s contents with zeros for extra security and v to get verbose information about the process. If dealing with directories and subdirectories, also include the r flag for recursive mode. If the 38 rewrites are too much for you, you can decrease the time required – as well as the security – by utilizing the l flag to reduce the number of passes to “only” two. This would turn the previous command to:
srm -rlvz Pictures/deleteme.png
Pros
- Options are simple to understand and intuitive
- Deleting a file is highly secure and thorough
Cons
- Will take a long time to finish
- Does not work well on systems that use RAID
6. Delete Files in Linux with Perl
Aside from using tools, you can also take advantage of simple programming languages, such as Perl, to delete files in Linux. For example, the following line of code will replace the contents of your file with the character “0:”
perl -i -pe 's/[^*]/0/g' /path/to/your/file
- The
-iflag tells Perl to process the file that you provided in the command. - The
-peflag tells the program to create an iterative loop for the contents of your file. 's/[^*]/0/g'is a substitution command. The[^*]operator matches every byte inside the file, and the0will replace each byte.
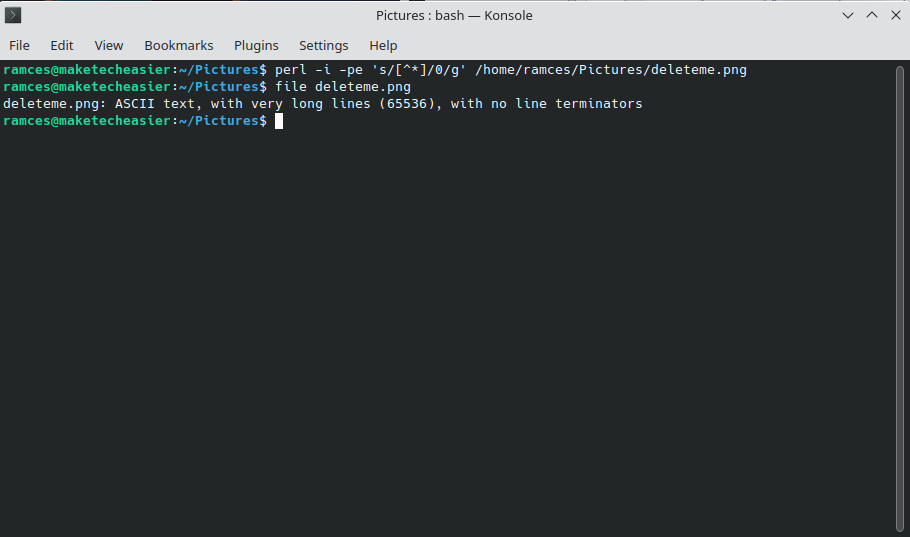
Once done, you can remove your modified file using rm:
rm /path/to/your/file
Pros
- You do not need to learn a new syntax if you know Perl
- Uses familiar abstractions such as sed substitution
Cons
- Command will only do a single pass on a file
- Replacing contents with arbitrary data can be insecure
Good to know: you can understand more about substitutions and file streams by using sed for basic system tasks.
7. The GUI way: Using Bleachbit
If you have an aversion to the command line, Bleachbit is one of the best solutions for securely erasing your data. (Bleachbit is more well-known for its ability to clean up your Linux system.) By default, the tool specializes in discovering and disposing “redundant files” that keep taking up space long after you’ve needed them. But it also incorporates the usually forgotten ability to manually “shred” any file beyond recovery.
Install it on your Ubuntu-compatible distribution through its software center or by using:
sudo apt install bleachbit
Click on “Menu -> Preferences” and enable the option “Overwrite contents of files to prevent recovery” for enhanced security.
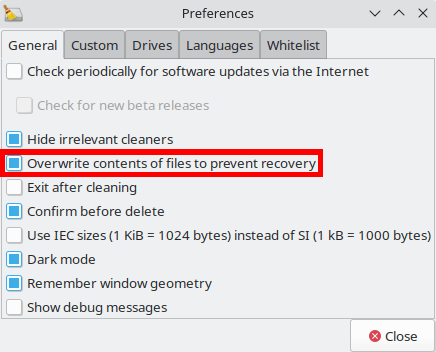
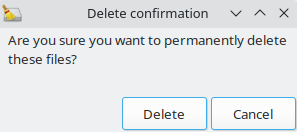
Go back to its main interface, click on “Menu -> Shred Files,” and from the request that pops up, choose the files you wish to beam to nothingness. Click “Delete” and reassure Bleachbit that you’re sure of what you’re trying to do.
You should always keep in mind that the use of journalling file systems and the fact that we don’t know how each HDD’s firmware “manages” its contents means that the best solution is wiping out the full HDD – or even better, physically destroying the device.
Pros
- Easy to use
- You can set it to be secure by default
Cons
- Cannot do disk wipes
- Will not wipe free space
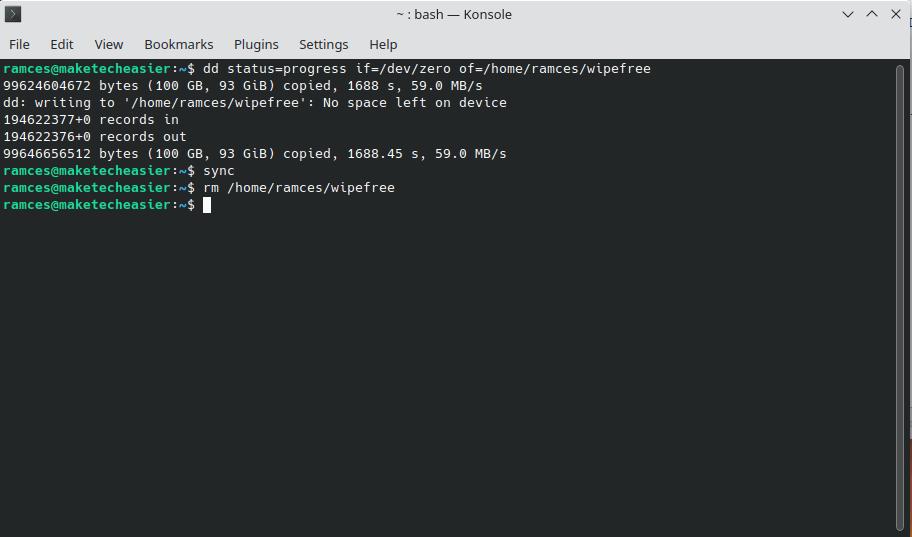
8. Wiping Free Space with dd
While secure deletion will make a file harder to recover, it is still possible to reconstruct it using metadata on your disk. Fix this issue by wiping all of the available free space in your machine.
The easiest way to do this in Linux is by using dd to create a file that will fill your entire hard drive:
dd status=progress if=/dev/zero of=/home/$USER/wipefree
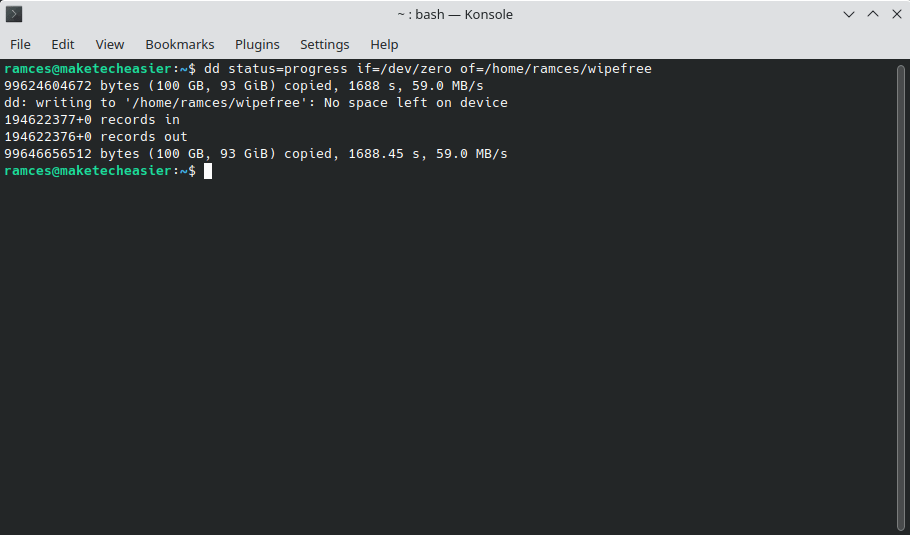
Once done, you need to tell your system to commit your “free space” file to disk:
sync
Lastly, remove your “free space” file using rm:
rm /home/$USER/wipefree
Pros
- Simple command that will not remove files
- Clears all lingering metadata
Cons
- Takes a long time to finish
- Does not delete files directly
Tip: to avoid seeing the “not enough storage space” message, regularly check and manage your disk space.
Frequently Asked Questions
Is it possible to securely delete remote files in Linux?
While it is possible to securely delete remote files, there is no guarantee that a remote Linux system will not back up the files inside their disks. It is better to assume that every remote disk and system is not secure.
Are my files completely gone after I securely delete them in Linux?
It is still possible that your system still holds on to some metadata from your old file. For example, your swap partition can contain information about a secure deletion in your system.
Mitigate this by rebooting and creating new files on your disk.
Are more passes better when deleting files?
Not necessarily. In most cases, five passes should prevent any data recovery tool from recreating your file. It is possible to recover a file beyond five passes, but require highly specialized tools and programs to work.
Image credit: Unsplash. All alterations and screenshots by Ramces Red.








