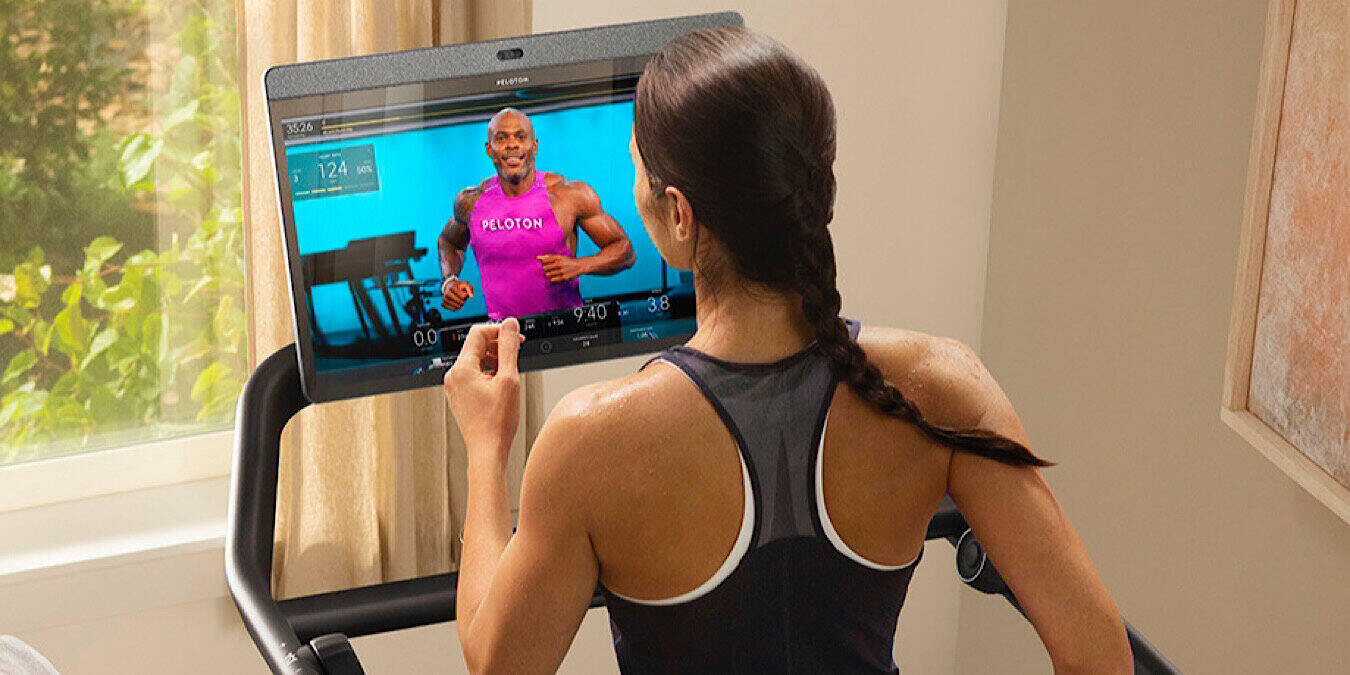
Fitness is supposed to be difficult – it’s how you know it’s working (or at least that’s what we’re told). But it shouldn’t be difficult in this way. A security researcher discovered that the user accounts of Peloton fitness bikes and treadmills were subject to data leaks, and the company took no action initially.
Peloton Potential for Data Leaks
With many gyms closed down during much of the pandemic, people were forced into home fitness. Some took that money they were saving and used it to get a Peloton stationary bike or treadmill. But the information that was shared in the Peloton accounts was left unprotected and subject to data leaks.
The Peloton fitness equipment initially fell under scrutiny when U.S. President Joe Biden was preparing to move into the White House. He has a Peloton stationary bike, and it’s equipped with a camera and mic, like most Internet-connected stationary bikes. There was talk of not allowing him to bring it to the White House or stripping the bike of its Internet connectivity.

It’s unclear whether President Biden was allowed to bring the Peloton bike with him. However, security researcher Jan Masters, with Pen Test Partners, was moved to look into the security of Peloton equipment. He learned he could make unauthorized access to the Peloton API for account data. The system allowed access to anyone.
The Peloton user data – such as age, gender, city, weight, and workout statistics – was open to data leaks, regardless of whether the accounts were set to private.
Masters reported his discovery of potential data leaks to Peloton. As with most security researchers, he gave the company 90 days to fix the issue before he would go public with his discovery. In that 90-day window, Peloton did not fix the potential for data leaks. The only action it took was to close down access to members. But anyone can sign up for an account and get that access.
Peloton eventually announced in a statement that it had fixed the security issue and admitted to its prion actions.
“It’s a priority for Peloton to keep our platform secure, and we’re always looking to improve our approach and process for working with the external security community. Through our Coordinated Vulnerability Disclosure program, a security researcher informed us that he was able to access our API and see information that’s available on a Peloton profile. We took action and addressed the issues based on his initial submissions, but we were slow to update the researcher about our remediation efforts. Going forward, we will do better to work collaboratively with the security research community and respond more promptly when vulnerabilities are reported. We want to thank [Pen Test Partners Founder] Ken Munro for submitting his reports through our CVD program and for being open to working with us to resolve these issues.”
After the Fallout
Munro said after the Peloton statement, “Peloton had a bit of a fail in responding to the vulnerability report, but after a nudge in the right direction, took appropriate action. A vulnerability disclosure program isn’t just a page on a website; it requires coordinated action across the organization.”

While Peloton eventually did the right thing, it’s concerning that it took so long to fix the vulnerability and that it wasn’t upfront when it did. Many, many companies have vulnerabilities – Peloton isn’t alone in that. But there needs to be accountability when an issue is brought to light.
If you are a Peloton user, your data is now safe. But know the company was lax with customer data, even when a public figure and national security was included in the mix.
Read on to learn about Facebook’s data leak affecting more than 500 million users.
Image Credit: Peloton Media Press Kit