Trying to come up with strong and yet easy to remember passwords can be a challenge. If you are like me when I need to enter a new password for an account, be it online or for a computer, my mind just goes blank! Luckily there are a number of password generators available for Linux, each with its own approach to generating secure passwords.
1. pwgen
pwgen creates passwords which are easy to memorize, while at the same time fairly secure. Technically, passwords which are easy to memorize won’t be as secure as a truly random password. However, that is an acceptable level of risk for most common usages, except for maybe online banking, etc. The advantage of a human-memorable passwords is that you will be less tempted to write them down or store them electronically in an insecure place.
To install pwgen, type the following into a terminal window:
sudo apt-get install pwgen
If you run pwgen without any parameters, it will generate a screenful of passwords. Just pick a single password from the list and then clear the terminal. This prevents anyone who happened to be looking over your shoulder from seeing which password you picked.
Run pwgen like this:
pwgen
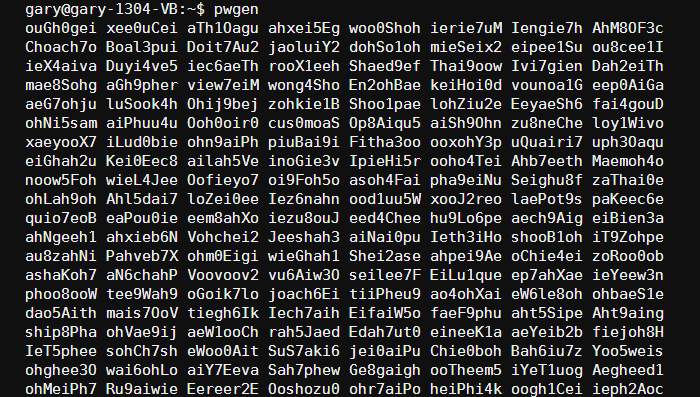
After you pick a password, type “clear” to erase the contents of the terminal window.
If you are sure that no one is looking over your shoulder, you can force pwgen to generate just a single password with the “-1” flag:
pwgen -1
![]()
To generate a completely random password, use the “-s” flag:
pwgen -1 -s
![]()
To make your password extra secure, you can force pwgen to create a password with at least one special character (e.g. exclamation mark, comma, quote, plus, minus, colon, etc.). To do this, use the “-y” flag:
pwgen -1 -s -y
![]()
A few more interesting flags for pwgen are:
-0: Don’t include numbers in the generated passwords.-B, --ambiguous: Don’t use characters that could be confused by the user when printed, such as ‘l’ and ‘1’, or ‘0’ or ‘O’.-v, --no-vowels: Generate random passwords that do not contain vowels or numbers that might be mistaken for vowels. This prevents the accidental creation of passwords with offensive substrings!
2. makepasswd
The makepasswd utility works in a similar way to pwgen, however it does not attempt to create passwords which are easy to remember. All of the passwords are generated randomly, with an emphasis on security over pronounceability.
To install makepasswd, type the following in a terminal:
sudo apt-get install makepasswd
To generate a single password, type:
makepasswd
To generate five passwords of at least 10 characters each, use:
makepasswd --count 5 --minchars 10
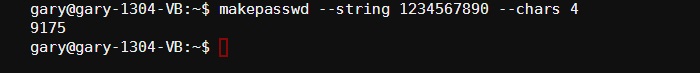
You can also specify a string from which to generate the random password. This can be useful for generating PIN numbers. For example, to generate a 4 digit PIN, use:
makepasswd --string 1234567890 --chars 4
3. passwordmaker
The passwordmaker program is a little different from the previous two examples. Originally, passwordmaker was an extension for popular web browsers like IE, Firefox, and so on. The passwordmaker-cli package installs the command line version of the tool. To install it, type:
sudo apt-get install passwordmaker-cli
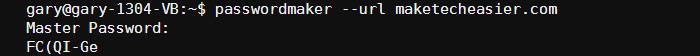
To use it, you need to specify a domain name (a URL) and a master password. The tool will take these bits of information and generate a unique password for that URL. For example:
passwordmaker --url maketecheasier.com
At the prompt, enter a secure but memorable password. The password produced in my example is “FC(QI-Ge”.
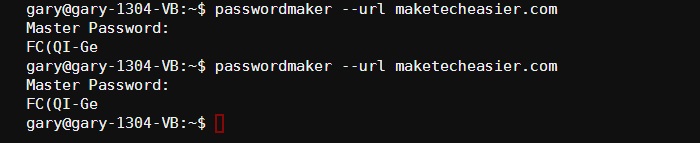
Now here is the magic of passwordmaker. If you run the program again using the same URL and the same master password, then the same password is generated. This means that you can generate a password for a certain site but you don’t need to remember it, nor do you need to store it somewhere. When you want to retrieve the password for that site, just run passwordmaker again using the same URL and the same master password and you will always get the same generated password.
Here is an example of running the program twice. Notice that the same password is generated.
Remember: Always keep your passwords safe, and don’t use obvious passwords like “password“, “123456” or “qwerty“. If you have any problems using the examples above then please use the comments section to ask a question, and we will see if we can help.







