There is no such thing as perfect security in the computing world. There’s not even one “best” approach. Operating systems have to balance usability, user expectations, and simple operation with security concerns and do their best to make an appealing blend. Security is often the opposite of usability and flexibility, so finding the right balance is important to building a user base and maintaining longevity.
Different developers have different approaches to operating system security, from challengingly secure to problematically open. These distinctions often come down to philosophical choices expressed through security policies. You can understand how an OS sees itself, its purpose, and its users by examining how the OS handles security.
Highest Security, Lowest Usability: Tails

Tails is an extreme take on operating system security. It’s likely the most secure operating system available to the public. However, it’s extremely difficult to use for general-purpose computing. Tails is a “live” operating system, meaning it can be run on a computer from a DVD or USB drive. Tails has no save state and must start from “zero” on each boot. This fresh start erases any traces of previous user activity or possibly malicious software. When paired with the built-in security programs found in Tails, it creates an extremely secure operating system.
The limitations of this strategy are immediately obvious. Such an operating system is all but unusable for most general purpose computing. So who is it for then? Users who, for whatever reason, require that level of security. You’d only be willing to suffer through this approach if you had an extremely good reason to deal with the downsides. If your personal or professional safety depends on high security, Tails is a good tool. Such strong security can enable hackers and ne’er-do-wells, but it’s also crucial for the safety of whistle-blowers, investigators, and journalists.
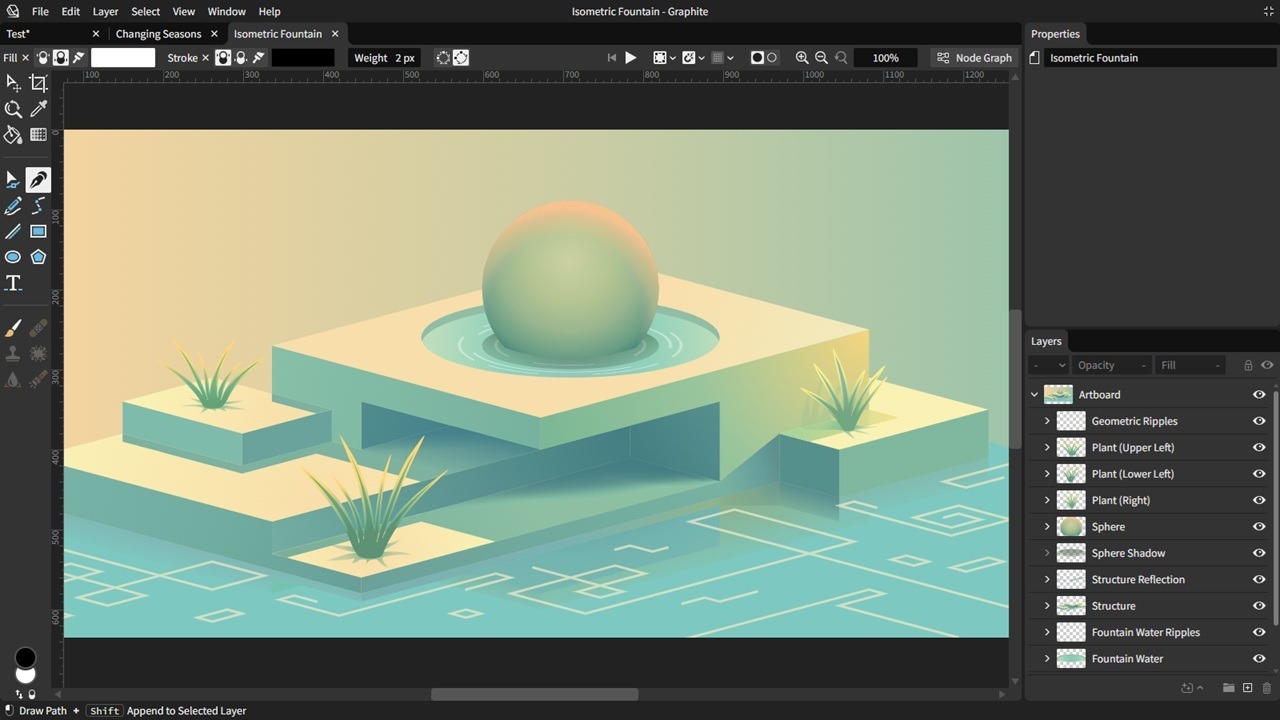
High Usability and Security: iOS
Apple’s iOS offers high usability and high security but virtually no options for serious customization of the operating system. It’s a largely inflexible system. If you’re not happy with Apple’s design decisions, you had better hope they change it for you or consign yourself to a life of useless grumbling.
Apple often attracts criticism for its “walled garden” approach to software design on iOS, especially from users accustomed to greater freedom. This criticism is accurate, as any dispassionate user can admit. The choice undeniably restricts users and limits developer freedom, but it is not without its benefits. Designers leverage these restrictions to improve security and usability. When it’s hard to access system data or make changes to the system’s core functionality, less can go wrong, either accidentally or maliciously.
Take a recent example for illustration. Within the last month, some Android users discovered that their Facebook app had quietly hoovered up years of phone call metadata. iOS users, however, had no such problem. And it’s not thanks to the iOS users’ diligence: they’re just as lazy as everyone else. The iOS operating system simply prohibits such data collection.
Of course, this does limit the types of apps available on iOS, restricting user choice and limiting app developers. However, these limitations repay the user with fewer opportunities to break the system or decrease security. This choice represents a fundamental philosophical distinction in operating system security design when compared with more open systems like Windows and Android.
Moderate Usability and Security: Windows

Windows attempts to strike a practical balance between security and usability, permitting users to make major changes to the operating system while still preventing serious attacks. It’s a delicate balance, and Windows walk its tightrope carefully. A misstep in either direction often means a bad user experience or security problems down the line.
Fortunately, the adoption of Windows-as-a-Service in Windows 10 means that Microsoft can make major updates to the OS over the course of its life. And, in a controversial move, they can also force sufficiently important updates on users whether they want them or not.
It hasn’t always been a smooth road. Windows has sometimes suffered security flaws and software vulnerabilities. The attack surface is immense, and near-universal adoption makes discovering attacks and zero-days well worth the trouble. But considering that the vast majority of computing devices in the world run Windows, it’s a clear indication of the philosophy’s popularity. Perfection is not essential to success. Windows has proven that good-enough security and reliable functionality is an acceptable compromise for most personal and corporate users.
High Usability, High Security: macOS

Just like iOS, macOS offers an attractive combination of high usability and high security. However, users also get the major downside of iOS: limited user control. Apple tightly controls their software and hardware ecosystem, freeing them from the many security and support obligations that Microsoft labors under. As such, they have the freedom to create a highly usable and highly secure operating system, though there have been some embarrassing security black eyes in the most recent version of macOS. The system also benefits from some security through obscurity: with such a small segment of the desktop market, macOS doesn’t represent an appealing target for attackers.
Variable Usability, Variable Security: Linux
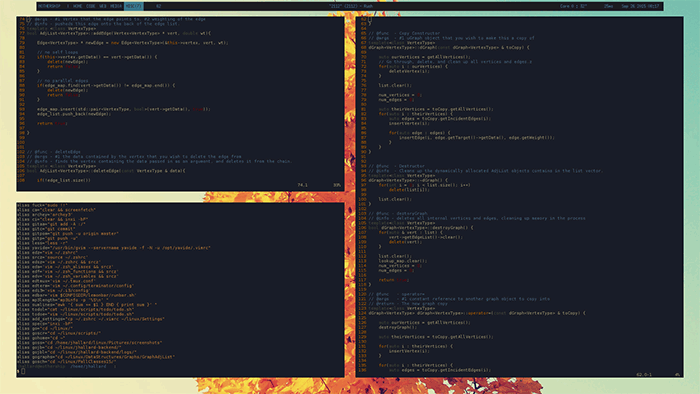
Linux might be the most flexible operating system architecture around, meaning it’s hard to say for certain what kind of security or usability the operating system has. It’s not a monolithic entity like macOS or Windows but a common feature in countless distros, ranging wildly in quality, scattered across the world. Thus, to talk about “Linux security” is to paint with an extremely broad brush.
In general, the Linux kernel is secure, but it’s just the core around which you build your own distribution. It’s theoretically easy to add packages that compromise that security, creating flaws where none previously existed. It’s also easy to build an operating system that only you would ever want, offering a degree of customization and control that’s simply impossible on other platforms.
Working with the most popular distros, like Ubuntu and Debian, will limit exposure to security bugs, but it’s a problem that infects all free and open-source software. Free software simply gets less coding attention than paid software, which we all learned to our detriment in the Heartbleed OpenSSL bug. Similar issues could be lurking in other popular open-source utilities, and we might not know until its too late. Like many things in Linux, it’s up to the user to manage their own security, ensuring they have a combination of usability, flexibility, and security that they’re comfortable with.
Moderate Usability, Low Security: Android

Android offers the user far more customization via flexibility. But as a trade-off, it’s far less secure than competing operating systems. This is almost entirely thanks to the distribution strategy rather than any inherent flaw or oversight in the operating system. Android isn’t “broken” or “bad,” but the way it exists in the market creates opportunities for exploitation.
The incredibly open system offers massive flexibility, so it’s cheap, widespread, and familiar to consumers. But from a security perspective, it’s a patchwork of vendor-specific implementations, slow-motion updates and near non-existent support from manufacturers after devices are sold.
Essentially, the only “true” Android experience comes from Google devices, but that represents an incredibly small segment of the market. Android in its purest stock form doesn’t have an inherent or design-based security problem. However, the way fragmentary and variable Android is implemented by vendors creates a potential minefield of security issues.
Conclusion
Perfect security is an illusion. There is no “best” operating system or a “right” approach to security. It’s about finding a balance between what you need and what you want in an operating system. Different strokes for different folks, and different ways to solve the same problem. This is why diversity in the marketplace is so crucially important: sometimes there isn’t a “best” solution, and you want a solution to a problem that best fits your philosophy and needs.
In a broad analysis, Windows manages the most popular balance between usability, security, and flexibility. Users have a significant degree of freedom to customize and even break their systems, but usability and design could be better managed. The many inter-operating parts of the Windows operating system provides fertile ground for security holes and a high incentive for attackers to find those bugs before Microsoft. But with constant patches and updates, Microsoft has done good work staying ahead of the curve.
iOS represents a different but also successful model. The iPhone rules the high-end smartphone market, remaining an extremely popular device year after year with users of all stripes. The usability and security improvements that iOS’ user restrictions enable are apparently well worth it for many users, and the system is well-designed enough that the inflexibility of iOS is barely noticeable.
Image Credit: Jhallard