It seems nothing is safe from technology attacks these days. Attackers will find a way to attack any device or service that it is able to. A recent vulnerability, BLURtooth, attacks the component used for setting up authentication keys when pairing Bluetooth-capable devices. Yes, even that is something you need to worry about not being safe.
How the Component Works
First, we need to look at what this component – Cross-Transport Key Derivation (CTKD) -does. It sets up two different sets of authentication keys for Bluetooth Low Energy (BLE) and Basic Rate/Enhanced Data Rate (BR/EDR) standards.
This allows CTKD to have both keys ready so that paired devices can decide which version of the Bluetooth standard to use. Primarily, it’s used for the Bluetooth “dual-mode” feature.

The BLURtooth Vulnerability on Bluetooth
What is being referred to as the BLURtooth attack was discovered separately by two groups of academics from Purdue University and the École Polytechnique Fédérale de Lausanne.
The Bluetooth Special Interest Group (SIG) and the CERT Coordination Center at the Carnegie Mellon University published notices that an attacker can manipulate the CTKD component to overwrite other Bluetooth authentication keys on a device. It gives the attacker Bluetooth access to the other Bluetooth-capable services and apps on that device.
In some versions of the BLURtooth attack, the authentication keys can be overwritten completely, yet in other versions, the authentication keys are only downgraded to use weak encryption on the Bluetooth-capable device.
All devices that use the Bluetooth standard 4.0 through 5.0 are vulnerable to the BLURtooth attack. Bluetooth 5.1 has features that, when activated, can prevent the attack. Bluetooth SIG officials have started notifying vendors of Bluetooth devices about the BLURtooth attacks.
Patches are not available at this point. The only way to protect against BLURtooth attacks is to prevent man-in-the-middle attacks or pairings with rogue devices that trick the user. When patches are available, it’s expected they’ll be integrated as firmware or OS updates for the devices.
With the amount of devices that are Bluetooth-capable, they obviously all work on different timelines. Whether or not your device will get a patch will depend on how the manufacturer prioritizes security.
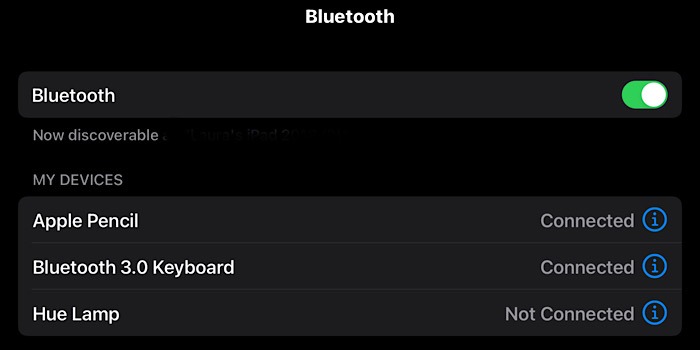
For instance, I looked up the specs of my iPad, and it uses Bluetooth 5.0. Apple would most likely be handling this in an iPadOS and iOS update. Apple is known to be security-focused, so I’m comfortable knowing it will be taken care of fairly soon.
BLURtooth is just another reminder of the importance of keeping your devices updated with the latest firmware and OS. Even if you don’t need the new bells and whistles of updates, they always include security enhancements that help keep you safe.
This was the reason behind a past Windows 10 update deliberately breaking unsecure Bluetooth connections.