Some people are, rather falsely, under the impression that just because they use Linux they don’t need to worry about security. Sure, Linux doesn’t suffer from the same types of security issues and prevalent malware that Windows does, but that doesn’t mean that Linux users can neglect their systems and expect to be secure.
These five tools are absolutely essential for Linux desktop users. If you’re running a server, there are more. This guide doesn’t present them in any particular order because they all serve different and arguably equally important functions. Plus, they are all free and open-source software. So if you aren’t using any of these on your Linux desktop, start now.
1. ClamAV
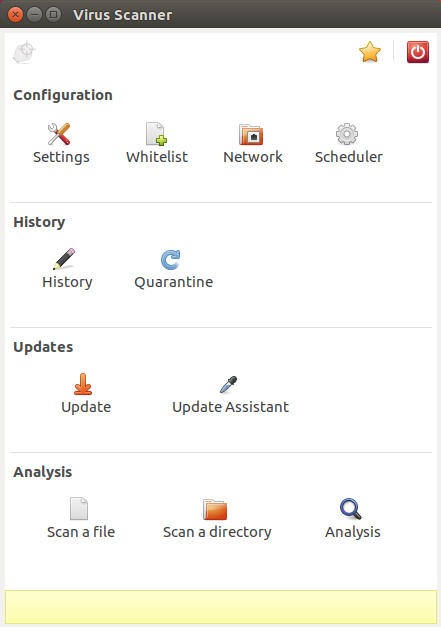
ClamAV is a traditional antivirus program like you’d expect to find for Windows. Actually, there is a version of ClamAV available for Windows. You can use ClamAV by itself from the command line, or you can couple it with its graphical interface, ClamTK for a more familiar experience.
ClamAV has the ability to run as a daemon that you can use to automate scans and/or allow other programs like mail servers to automatically scan files on use. You can automate ClamAV via cron without the daemon, too. That may be the better option if you’re just running it on a desktop.
2. Chkrootkit
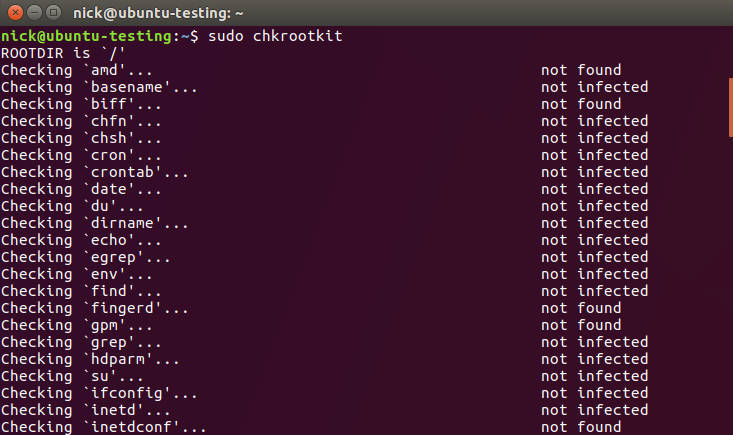
Rootkits are a special type of malware specific to Unix-like operating systems, Linux included. As their name implies, they attempt to get root access to a system. From there they can allow an attacker to do nearly anything.
Chrootkit is a simple command line utility that scans your system for known rootkits. Chkrootkit doesn’t remove rootkits. Chances are, if you’re infected with one, you’re going to be doing a fresh install unless you get lucky enough to be able to remove it manually. That said, it’s still an amazing tool for detecting potential breaches.
3. LUKS
LUKS isn’t really an independent program, but it needs to be mentioned. LUKS actually stands for Linux Unified Key Setup, but it tends to be synonymous with the full stack that supports Linux disk encryption. Cryptsetup is the actual utility that encrypts disks and that uses a Linux kernel module called dm-crypt.
Clearly LUKS is tightly integrated into the inner workings of Linux, and that makes it an excellent candidate for encrypting your hard drives on Linux. It’s important to encrypt your hard drives for a wide variety of reasons. First off, encrypting your drives is one of the only ways to protect your data once someone has gained physical access to your computer. So if your computer is lost or stolen, the thief can’t get your data. It’s also a great way to protect storage that isn’t automatically mounted.
LUKS also works on USB volumes, so you can encrypt the flash drives that you only use on Linux systems.
4. Wireshark
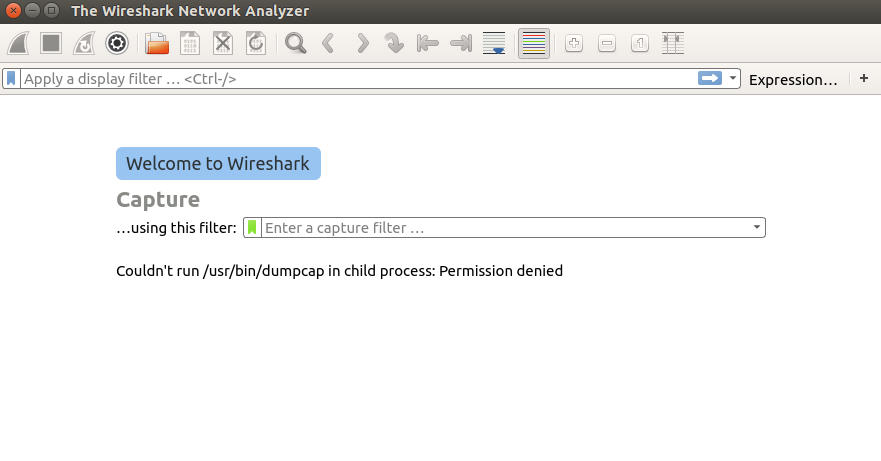
People often think of Wireshark as a hacking tool, and it definitely can be, but Wireshark is an insanely powerful tool for analyzing network traffic.
Wireshark lets you monitor the traffic on your network at a packet level. It provides loads of valuable information on what information computers are sending and where they’re sending it. You can narrow it down and monitor specific ports and protocols as well.
Malware can be sneaky, and human intruders can be even more crafty. Sometimes even the best security and antivirus checks fail. At that point you need to check for symptoms. Wireshark can see any shady activity on your network and tell you exactly how it’s operating so you can fix it. Wireshark can also help you asses any potential gaps in your security before a problem arises.
5. Firejail
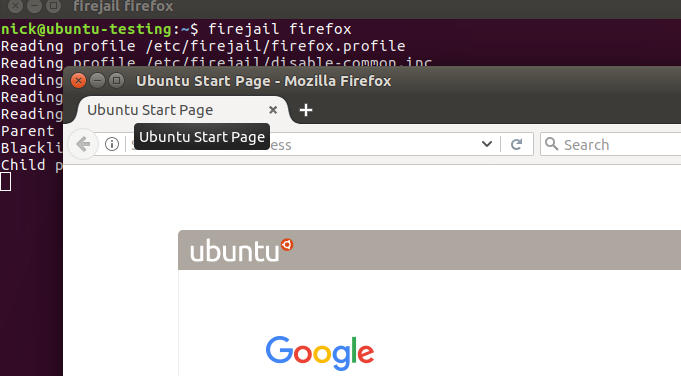
Firejail sounds like some kind of crazy new maximum security prison, but it’s actually a tool for running programs in self contained Linux namespaces. There was a recent Reddit thread that demonstrated the need for Firejail perfectly. Sure, the individual in this instance ran Firefox as root, which is an absolutely terrible idea, but web browsers are the largest and most easily accessible attack surface on desktop Linux systems.
Firejail can contain programs like web browsers, email clients, and torrent clients to ensure that the potentially harmful content that they’re interacting with doesn’t leak out and damage the rest of the system. It provides an important additional layer between your system and the Internet.
Additional Thoughts
You can’t sum up security with a handful of tools. There are loads more tools and precautions that you can add to harden your Linux system. Alternatives to the programs listed here, like Veracrypt, can provide similar functionality.
There are other tools that are tightly integrated into the Linux ecosystem like the iptables firewall and SELinux that can add even more security. Those two weren’t mentioned here because they also impose restrictions that desktop users might find annoying or difficult to work around. They’re worth considering, though.