The more we rely on technology to conduct our everyday business, the more common data breaches are becoming. Hackers get this information by exploiting vulnerabilities in the website’s software, and they are getting better at it with time.
Have any of your email addresses been compromised? If you can’t answer that question for sure, you may want to check out one or more of these sites for the answer. Each site has a different method of checking your email, some of them offering more information than others or giving you help in keeping on top of the breaches.
Have I Been Pwned
Have I Been Pwned is the most popular site for email and password monitoring, having been in existence since 2013. To use the site, you enter your email, and the site will list any breaches your email has been part of.
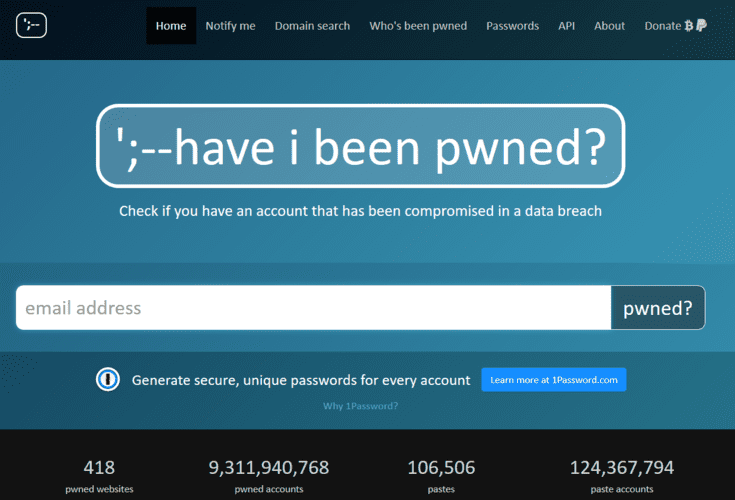
The site does offer its premium 1Password service to reduce your chance of having it compromised. It provides a variety of plans for individuals, families, and businesses beginning at $36.00 per year.
BreachAlarm
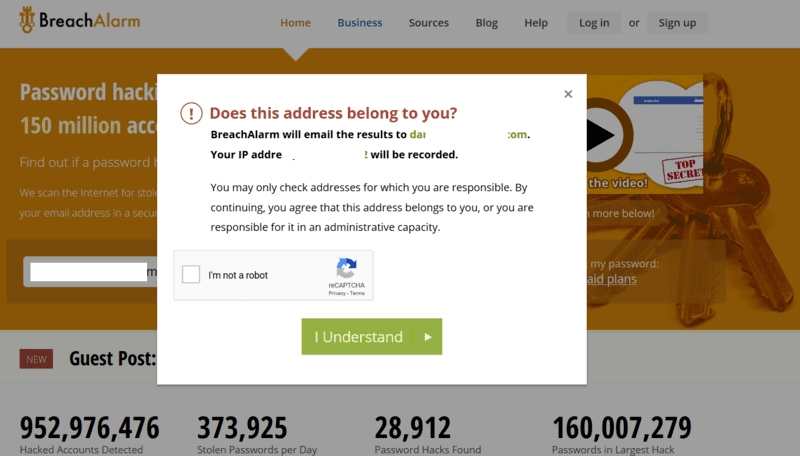
When you put in your email address, BreachAlarm sends you an email with the results. It also asks for verification that you are indeed the owner of the email. You have the option to activate their Email Watchdog for free.
Firefox Monitor
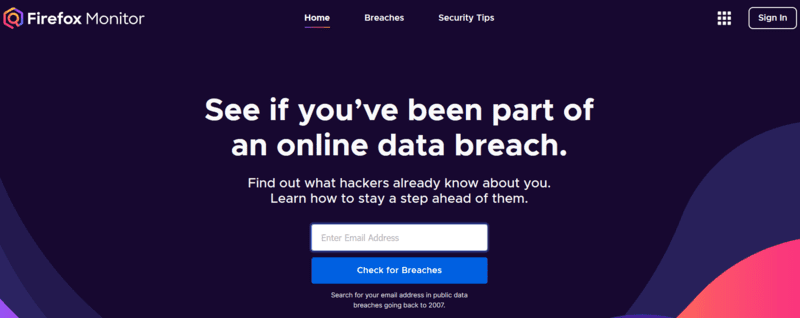
Firefox Monitor displays your information concerning breaches right on the screen after you enter your email. The site offers a way to get notified if your email is compromised again. Create an account, and you can monitor multiple email addresses for free. I also found this list to be the most comprehensive. It listed breaches the other sites did not.
Inoitsu Email Address Breach Analysis
The Inoitsu Email Address Breach Analysis site is plain and simple. Put in your email and find out if it’s been compromised. Your results are listed on the page. You don’t need an account, nor do you have to check your email to get your information.
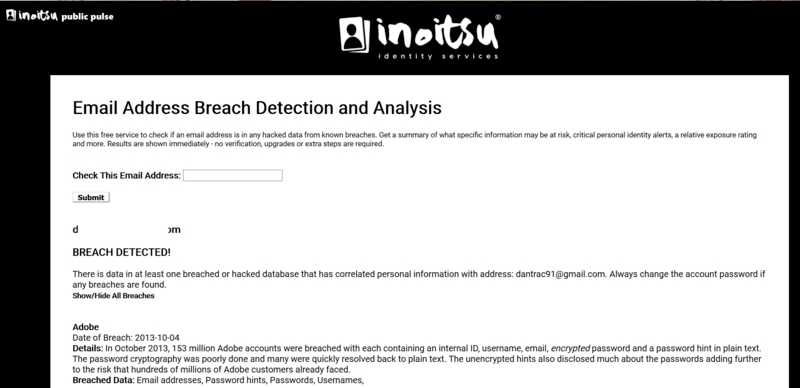
Also found on the home page is a list of recent breaches that you can scan through to look for any that may concern you or your loved ones.
Password Checkup by Google for Chrome
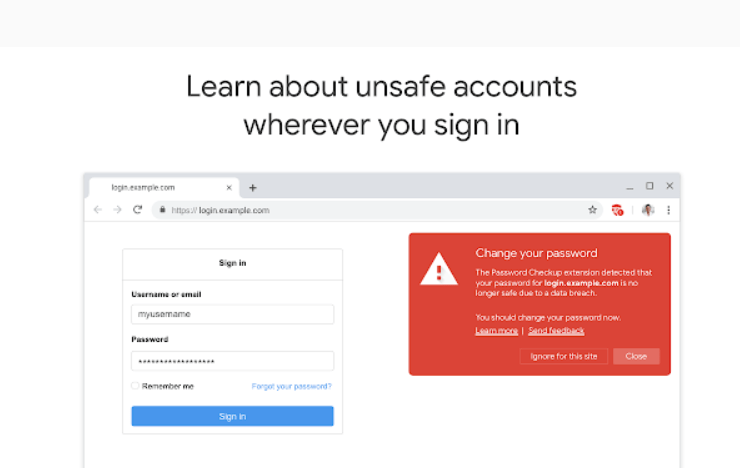
Password Checkup by Google for Chrome is not a site where you need to enter your email. It is an extension that alerts you of breaches that have occurred on a site you visit. When you try to log in to a website that has had a data breach, the extension will automatically notify you that you need to change your password.
Avast Hack Check
Put your email address into Avast Hack Check, and you receive an email they send to that address. This email shows the breaches where your information could have been compromised. You must use the email link within 24 hours, or it will be invalid.
Identity Leak Checker
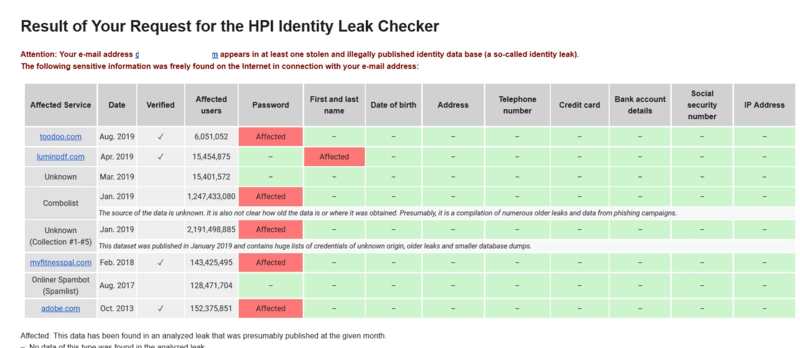
When you enter your email into Identity Leak Checker, it sends you an email message with the information concerning breaches of your data. You receive a chart that clearly shows what exactly has been compromised, whether it was a password, your name, or your address.
When dealing with data breaches, the best defense is a good offense. Always use strong passwords when creating accounts online, and don’t use the same password across different sites. Use two-step logins that require you to verify your identity using your cell phone to gain access to your information whenever possible.








