It’s an undeniable fact that logs play an important part in uncovering software or system problems as well as malicious activities. However, with so many log files and a lot of information in each of them, it gets a bit difficult for system administrators to analyse them properly.
While there are many tools available that are capable of analysing logs and producing meaningful information, if you are looking for a good command line alternative, I’d suggest you use logcheck. In this article, we will discuss the basics of this command along with the features it provides.
Introduction
Although the official documentation of logcheck says that it scans system logs for “interesting lines,” it’s worth emphasizing that these “interesting lines” are actually the problems and security violations that the tool detects.
The tool basically supports three levels of filtering:
- Server: The default level that contains rules for many different daemons.
- Paranoid: A level suited for high-security machines running as few services as possible – don’t use it if you can’t handle its verbose messages.
- Workstation: A level suited for sheltered machines as it filters most of the messages.
By default, logcheck runs as an hourly cronjob just off the hour and after every reboot and sends the results to you in an e-mail.
Download and Install
Users of Debian-based systems, like Ubuntu, can easily install logcheck by executing the following command:
sudo apt-get install logcheck
This is the recommended way to install the command line tool as it will install the version that’s already there in the repository of your Linux distribution. Alternatively, you can also install the utility by downloading it from its project website.
Configuration
Before using the logcheck command for the first time, you should take a look at the “logcheck.conf” file located inside the “/etc/logcheck” directory as it contains variable settings that you might want to alter per your requirements.
Here are a couple of snapshots of this file:
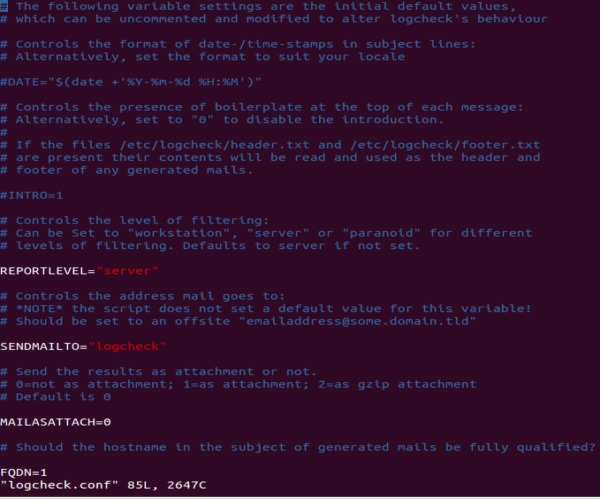
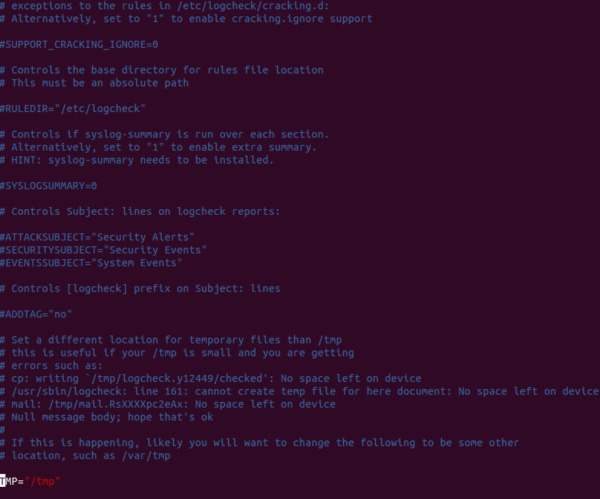
As you can see, some of the variables are active with their default values in place while others are commented. You can make the changes to suit your requirements. For example, I uncommented the DATE as well as the ATTACKSUBJECT, SECURITYSUBJECT, and EVENTSSUBJECT variables, and changed the value of SENDMAILTO variable to my email address.
Besides “logcheck.conf,” there is also a “logcheck.logfiles” file present in the same directory which contains a list of log files that will be checked by the logcheck command.
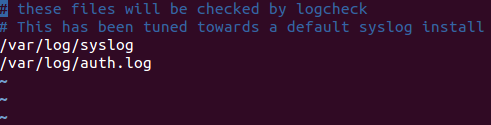
You can add more log files to this file, but make sure that each entry is added in a separate line.
Usage
Here are some examples of how the logcheck command can be used:
Note: all examples presented in this article are tested on Ubuntu 14.04.
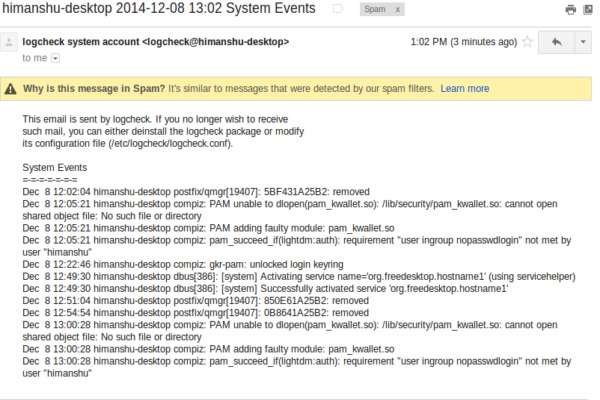
Send email immediately
While logcheck sends email periodically by default, you can use the -m option to force it to send one immediately. For example, when I executed the following command:
logcheck -m
The following email was delivered to my inbox:
Note:
1. You can use the -h option followed by a hostname to use that hostname in the subject of the email.
2. You can use the -o option to send the report to stdout, rather than email.
Override the default logfile and configuration file lists
As already discussed, by default, the logcheck command uses “/etc/logcheck/logcheck.logfiles” and “/etc/logcheck/logcheck.conf” files for reading the log files to be monitored and its own configuration settings, respectively. But you can change this behaviour and have the command read files located at any other location by using the -L and -C options.
For example, the following command would read “mylogcheck.conf” located in my home directory:
logcheck -C /home/himanshu/mylogcheck.conf
Similarly, the following command would read “mylogcheck.logfiles” present in my home directory:
logcheck -L /home/himanshu/mylogcheck.logfiles
Note: you can also use the -r command line option followed by a directory name to override the default rules directory.
Retain the logfile offsets using -t option
The logcheck command utilizes a program called “logtail” that remembers the last position it read from in a log file. But if you want to run the command in testing mode, i.e. without updating the logfile offsets, you can use the -t option.
The following command will report security concerns or violations but won’t update the offsets:
logcheck -t
For more information on this command, go through its man page.
Conclusion
Logcheck is not only simple to use, but it’s also extremely customizable. I’d say it’s a must-have tool for any system administrator primarily because of its capabilities. Have you ever used logcheck? How was your experience? Share your thoughts in the comments below.







