Ever been curious about the different stages of Linux, an open-source operating system? Knowing the entire boot process can help you troubleshoot issues – especially if you’re the administrator.
What happens behind the scenes when you power your device on? Read on to find out.
BIOS
The Basic Input/Output System (BIOS) is a piece of low-level firmware stored on a small memory chip in your computer’s motherboard. This firmware aids the start-up process and manages data flow between your machine and other connected devices, such as a mouse, printer and video adapter.
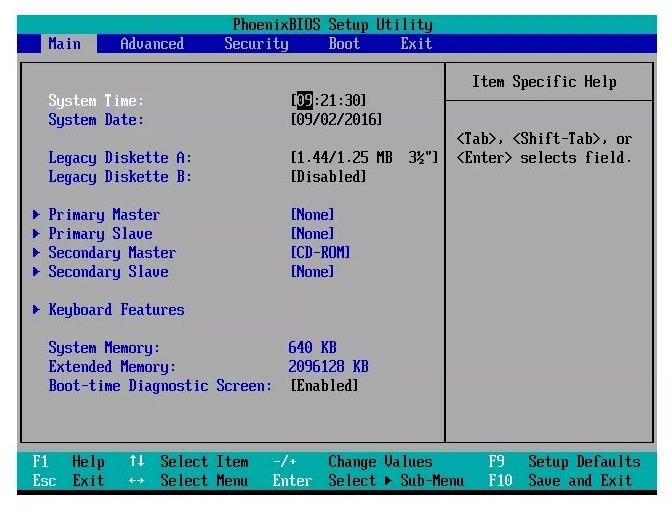
The primary function of BIOS, shown above, is to run the Power-On Self Test (POST). This test verifies the operability of system hardware and finds the boot sector, which contains the software necessary for the rest of the process. If the POST is successful, the BIOS will load the next step, the Stage One Boot Loader, into the system’s RAM.
If the POST isn’t successful, the BIOS will return a code you can use for troubleshooting.
Stage One Boot Loader
The first stage of the boot loader — called the Master Boot Record (MBR) or Guided Partition Table (GPT) — is designed to get the program online.
The MBR is a simple piece of software with no built-in understanding of file systems. As a result, you will always need to store the stage two boot loader between the MBR and the first partition on the hard drive.
Once the MBR detects the stage two boot loader, it hands over control.
Stage Two Boot Loader
The job of the stage two boot loader is to find the kernel and load it into memory.
Most Linux divisions will use one of three different boot loaders — GRUB, GRUB2 or LIL. You’ll most likely see GRUB2, depicted below, as it’s the newest.
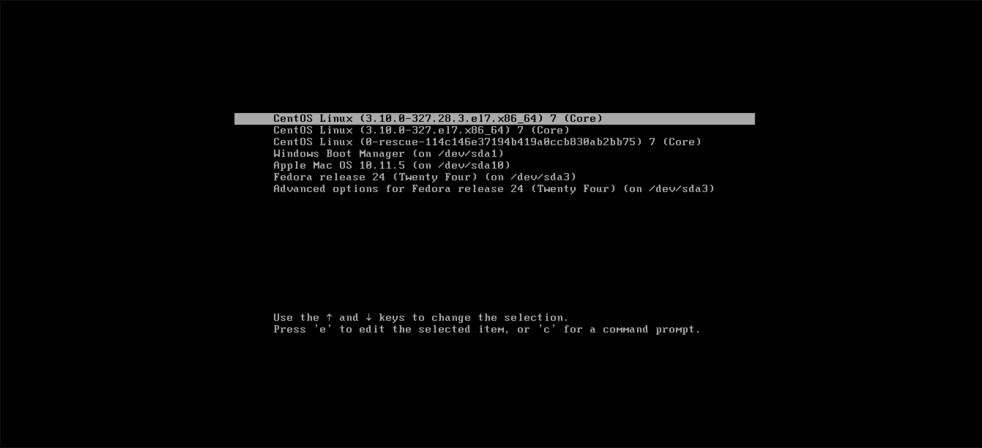
Once the boot loader has found a kernel and loaded it into RAM, it passes over control. It also sends an image of your device’s file system the kernel can use to find modules.
Kernel
Because all kernels exist in a compressed format to save hard drive space, the first thing it will do once given control is self extract. Then it will mount the image version of the file system it received from the boot loader.
The kernel will detect the system’s hardware and swap over the image to the root file on disk.
init (systemd)
Next, the kernel will start the initialization (init) system – the first process which spawns all processes necessary for the booting process. On most systems, this will be systemd.
Systemd’s primary function is to launch all of the daemons – background processes and services – needed to run the system. These services will continue to run after initialization and manage essential system processes like logging various system messages, keeping track of devices and ensuring that the file system is synchronized with system memory.
If you’re curious about which services systemd is running, running the systemctl command by itself will return a full list.
You can also use systemd to start other services on boot by using a combination of the systemctl command and the service you want to start. For example, if you want the system to check the status of the NFS, you can type systemctl status nfs-server.service. You can also start, stop, enable or disable a service with a combination of systemctl and one of those commands.
Runlevel
The run level is a state of INIT, and your system defines what services are running. The standard Linux kernel supports seven different runlevels:
- 0: System halt, ready to be powered off
- 1: Single user mode
- 2: Multiple user mode, no network file system
- 3: Multiple user mode using the command life interface instead of the graphical user one
- 4: User-defined
- 5: Multiple user mode, using the graphic user interface that most Linux systems will boot into by default
- 6: Reboot
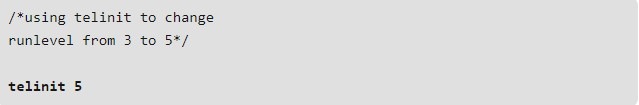
If you need to change the runlevel for any reason, INIT will be responsible for altering it using the telinit command, shown above.
Breaking Down the Boot Process
This breakdown is merely an overview of the Linux boot process and leaves out some of the finer details. However, it should give you the information you need to troubleshoot any problems you may face.