Windows processes play a significant role in the proper running of your PC or laptop. Some, like csrss.exe and winlogon.exe, are so crucial that if you mistakenly decide to terminate them, you may end up crashing your device. Malware authors take advantage of such a criticality to infect healthy Windows systems. The premise is that viruses, adware, spyware and Trojan’s can be labeled anything – even named after standard Windows system processes.
Below are a few leading Windows 11 and 10 processes often confused for their namesake malware. Learn how to spot the fakes if they show up on your system.
Also read: How to Format a Drive in FAT32 in Windows
How to Find Out Whether a Windows Process is Legitimate
There are two ways to verify whether a Windows process is legitimate or a malware source: through its Application Properties and using external tools such as CrowdInspect by CrowdStrike.
1. Verifying the Legitimacy of a Windows Process through Its Properties
All authorized Windows process files are connected to the Microsoft Corporation, the official program/app developer or a built-in Microsoft account such as TrustedInstaller.exe, which governs folders like WindowsApps.
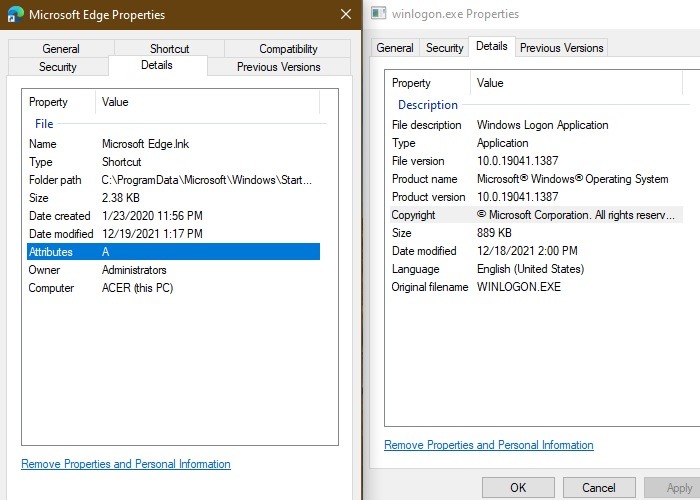
To determine whether a Windows 11 or 10 process is legitimate and not a source of malware, you need to look under the hood in its Application Properties. Go to the “Details” tab and find the official copyright owner of the process. If it is Microsoft, an app developer, or TrustedInstaller, you’re good to go.
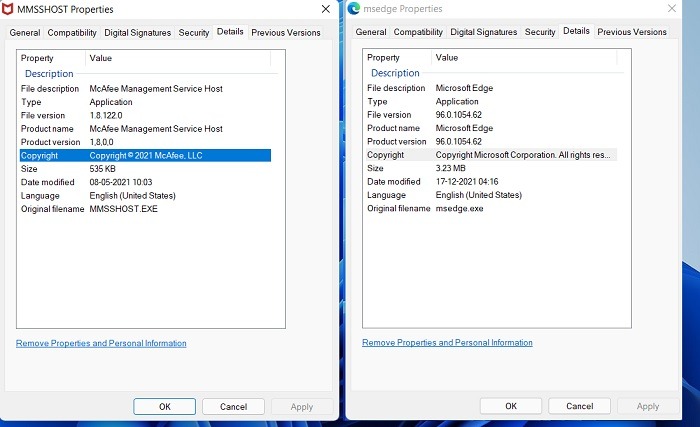
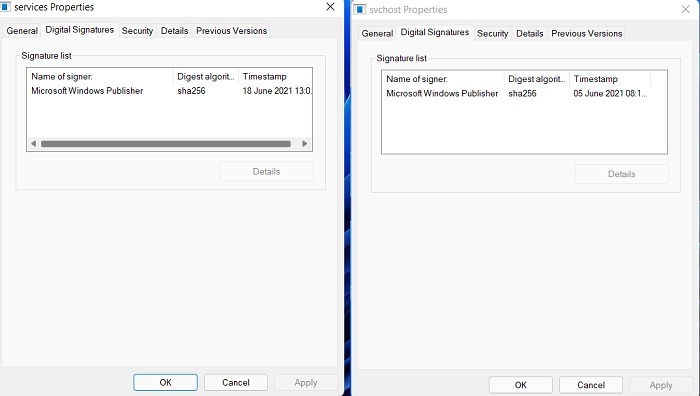
Also in Windows 11/10, you can check the “Digital Signatures” tab of a process’s Properties. Here you will find the official digital signatures with the latest timestamps giving you an additional layer of assurance.
As signing a driver for these processes requires standard Microsoft permissions (moreover, any unauthorized access to the device root is prevented by UEFI secure boot), it is now impossible for malware authors to fake the digital signatures in Windows 11.
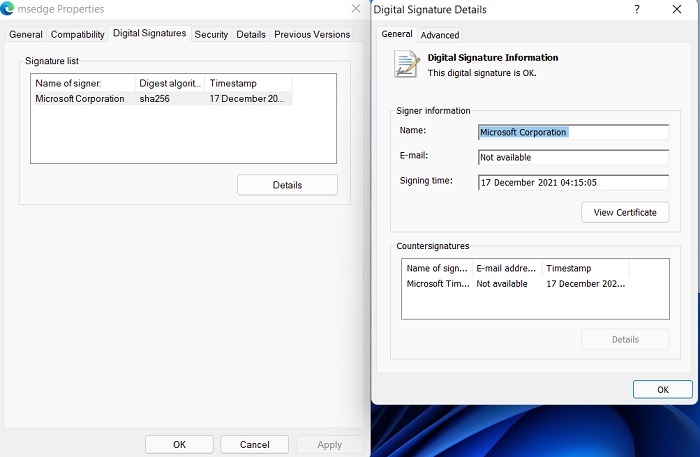
From the mundane to the critically important, such as “services.exe” or “svchost.exe,” all Windows 11 processes are digitally signed with timestamps. With each successful Windows update, this authentication is reverified.
On the other hand, Windows 10 Process Properties could have the Digital Signatures tab missing entirely. Also, some of the processes may not display the copyright information correctly.
However, even in Windows 10, mission-critical internal system processes like Winlogon.exe always display this info. You can verify the software authenticity through other means. Plus, if you install unsigned drivers in Windows 10 or 11, they will not show any digital signatures upon subsequent reboot.
Also read: 11 Legitimate Windows Processes that Can Look Like Malware
2. Verifying the Legitimacy of a Windows Process Using CrowdInspect
On both Windows 10 and Windows 11, you can verify the authenticity of a process file through an external software application: CrowdInspect by CrowdStrike. CrowdInspect is a free host-based and real-time process inspection tool that scans for background malware using detection engines such as VirusTotal.
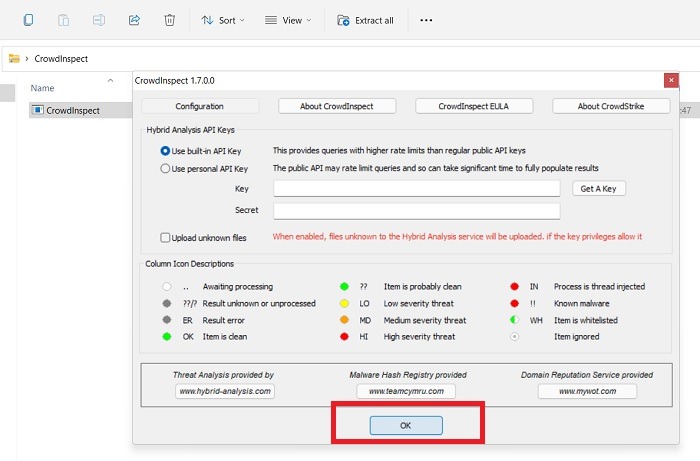
- Download the CrowdInspect ZIP file from the official link and click the unzipped program to launch it. You don’t have to install anything.
- Accept a license agreement and proceed to the screen where you can do a hybrid analysis of all the background processes on your Windows device. Use the built-in API key and click “OK.”
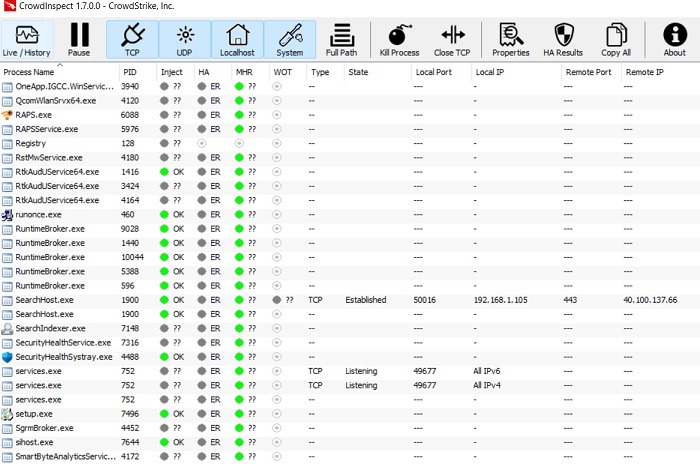
- Wait until CrowdInspect populates your screen with the entire set of background programs and processes on your Windows device.
You can verify the status of programs through color symbols. Any item that is clean is indicated by a green icon. If there are doubts, you will see question marks next to the icon. For those items with a low severity threat, there’s a yellow icon. Items with high severity threat are indicated by a red icon. You’re not going to see any yellow or red icons if your device is healthy.
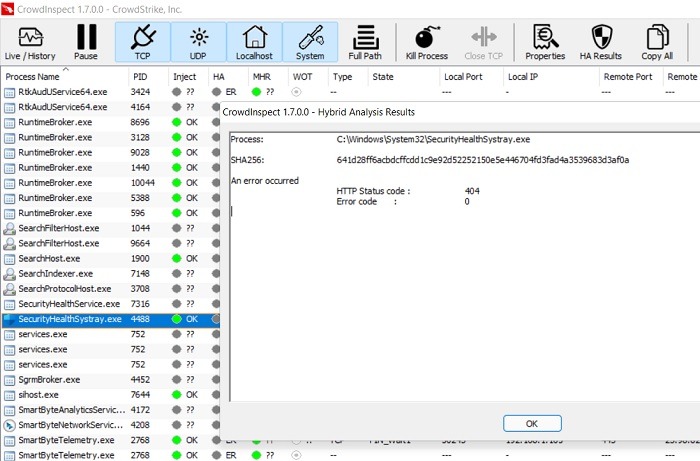
- To further verify there are no malware concerns, right-click the process and click “View HA Test Results.” You should not notice any errors, a safe indication that you’re not dealing with any malware.
Also read: How to Schedule Windows Shutdown and Startup
List of Common Windows 11/10 Processes that Resemble Malware
1. Explorer.exe
The universal Windows File Explorer program, explorer.exe, is easily accessible from the taskbar and desktop. Its primary purpose is to serve as a file manager for all the files and folders of your Windows 11/10 device. Because of its vital importance, the explorer.exe program is a favorite target of attackers.
Virus Detection: explorer.exe malware usually show up as Trojans, ransomware (especially email), and Adobe Flash files. The legitimate program is always found in “C:\Windows,” and the duplicates may show up in D drive, Program Files, hidden folders, or any other PC location.
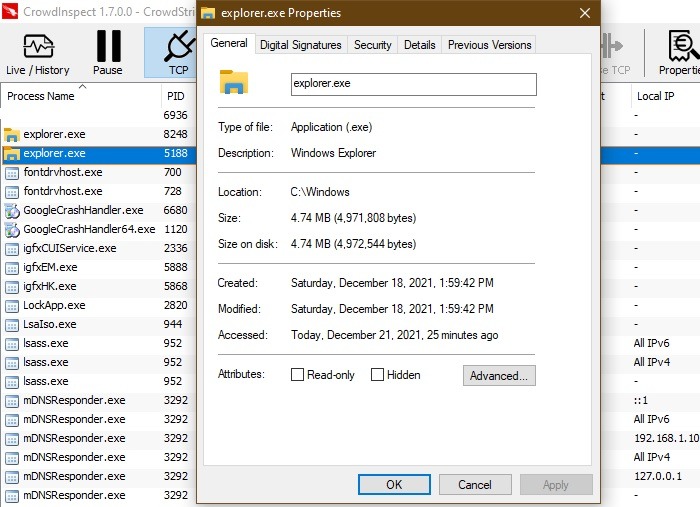
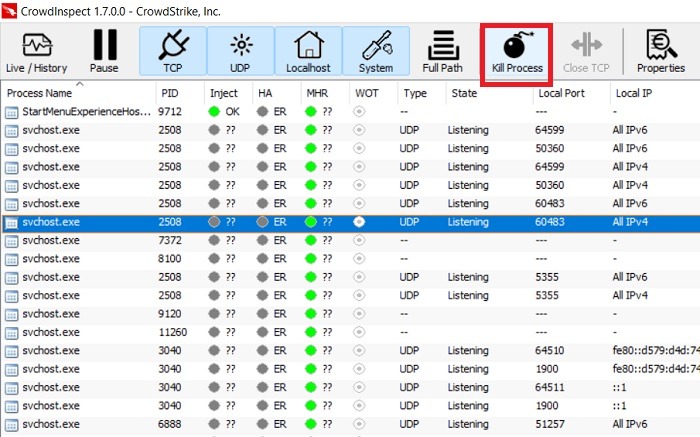
Action: if there are two to three instances of explorer.exe on your device, there’s nothing to worry about as long as they all have valid digital signatures and locations. When there are multiple processes consuming CPU, identify the bogus ones in CrowdInspect, then right-click to “kill the process.”
2. lsass.exe
lsass.exe stands for Local Security Authority Subsystem Service, which goes on behind your Windows user authentication. Apart from the malware, you should not terminate the original processes, as it will result in your system losing access to Admin and local accounts, prompting a device restart.
Virus Detection: a common way malware authors disguise lsass is by substituting the lowercase “l” with an “i” in the uppercase, or an uppercase “L.” Watch out for any intentional misspellings. Also, any invalid digital signatures and files located outside of the “C:\Windows\System32” folder is an obvious giveaway.
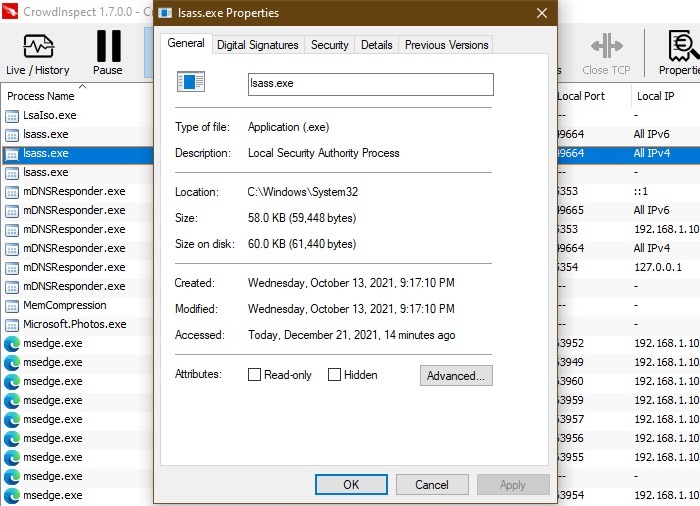
Action: terminate the bogus lsass processes from the task manager. If you’re not sure whether it’s an “l” or an “i,” do the same from CrowdInspect. Multiple valid lsass instances are fine and should not be tampered with.
3. RuntimeBroker.exe
RuntimeBroker.exe is a safe Microsoft process whose job it is to manage permissions for any apps downloaded from the Microsoft Store. It verifies the authenticity of programs such as the Photos app. If any app does not belong on your Windows device, Runtime Broker alerts you by consuming a lot of extra memory.
Virus Detection: if your Windows device is infected with the RuntimeBroker.exe virus, you will see its presence in other PC locations apart from “C:\Windows\System32.” As the program is not legitimate, the memory leaks will skyrocket, burdening your CPU. You will also notice an invalid digital signature for the bogus instances.
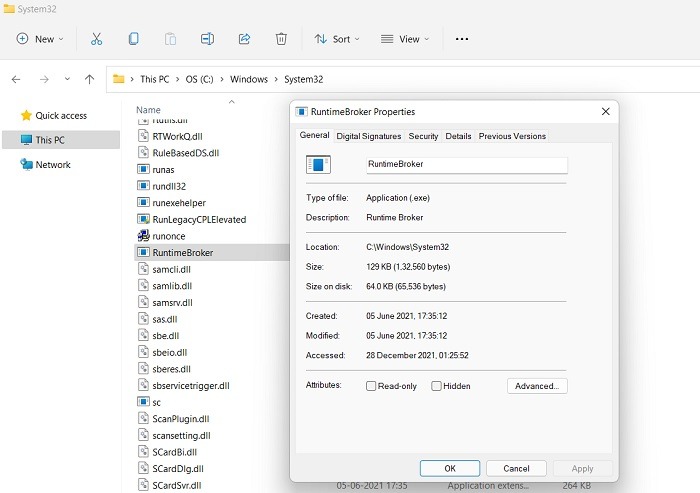
Action: open the task manager. Click multiple valid instances of Runtime Broker and click “End Task.” This will end any problems with a given app. For the bogus RuntimeBroker.exe entries, terminate them from CrowdInspect.
4. Winlogon.exe
When it comes to Windows background processes, there’s nothing more important in the scheme of things than winlogon.exe. Not only does it govern the login process, it also loads user profiles, controls the screensaver, and connects with multiple networks. It is located at “C:\Windows\System32.”
Virus Detection: usually a spyware or a keylogger tool, winlogon.exe is a very dangerous malware that can cause systems to start crashing, which is easy to recognize. If you have Windows Defender on, it will warn you to immediately delete the file and terminate any vectors used (email, web browser).
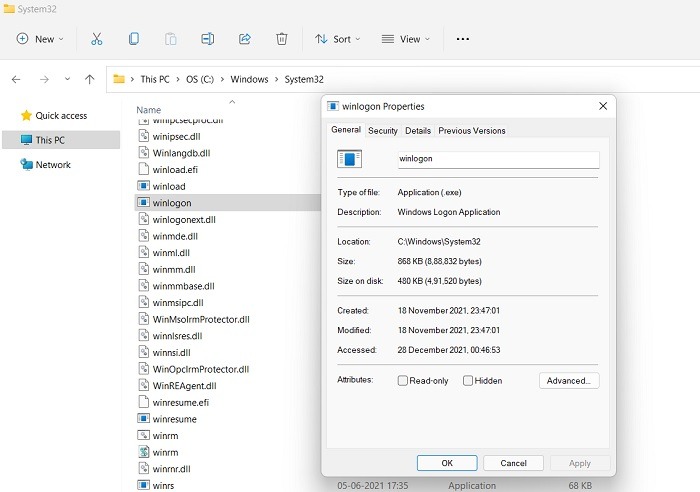
Action: the safe winlogon.exe executable will not have more than one instance in CrowdInspect. The other bogus instances should be deleted on arrival using Windows Defender suggestions.
5. Svchost.exe
Svchost.exe refers to Windows “service host,” a shared service process that serves as a shell for loading various Windows services. Depending on the number of open applications, there are usually many svchost.exe instances that run as individual processes.
Virus Detection: you will come across a svchost.exe malware episode when you find a protected folder or program blocked by a duplicate process or with spelling variants such as “svhosts.exe.” They’re mostly ransomware or banking fraud tools. Their source vectors include PDF files, ZIP files, and JavaScript.
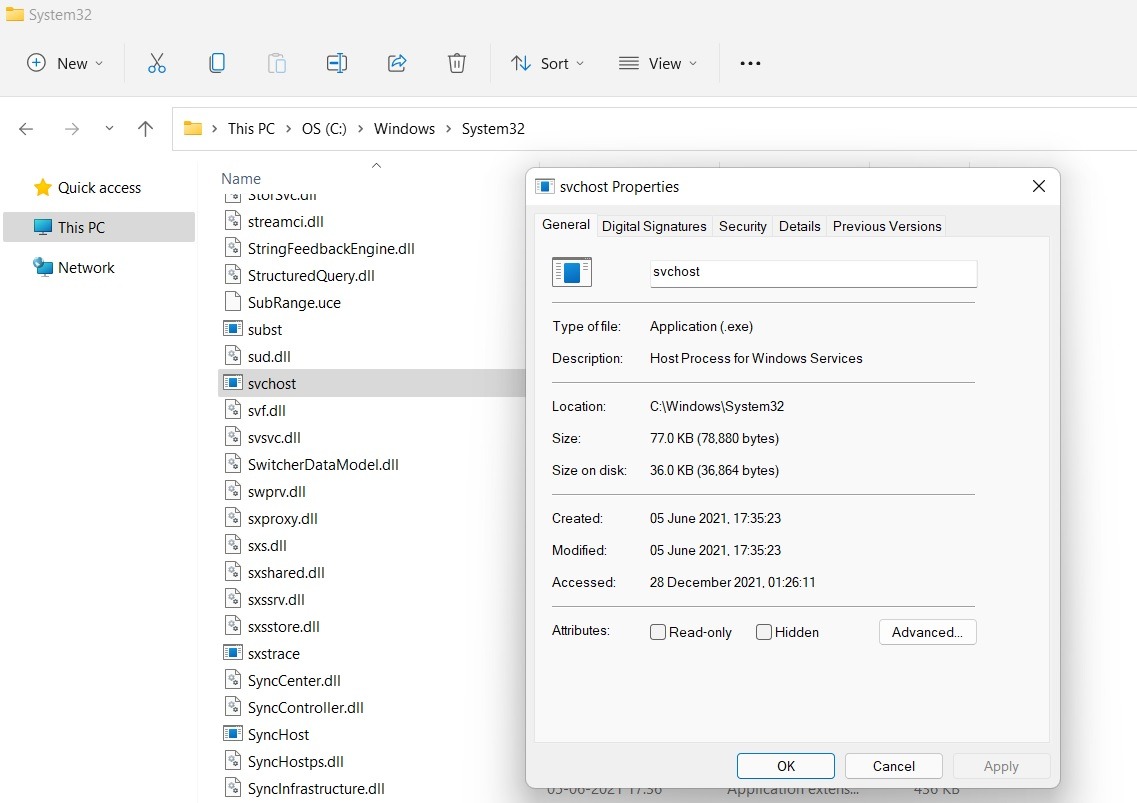
Action: these Trojans are usually a low level threat but should be removed at your earliest convenience. Standard anti-virus tools and Windows Defender are equipped to delete any service host instances not found in “C:\Windows\System32.”
Also read: Latest Windows Update Problems and How to Fix Them
6. OfficeClickToRun.exe
If you’ve been using Office tools – such as Word, Excel, or PowerPoint – you have come across an executable called OfficeClickToRun.exe. Its job is to run the latest Microsoft Office versions on your device and handle the updates. Even when it’s not a malware, OfficeClickToRun.exe can be memory-intensive on your CPU. However if you periodically delete temporary files, it’s much less of a burden.
Virus Detection: is the executable present in any other location apart from Program Files in Microsoft Shared folder? The extra file is unhealthy for your system. Also, your Windows device should only have one instance of OfficeClickToRun.exe running. Check the digital signatures for any others.
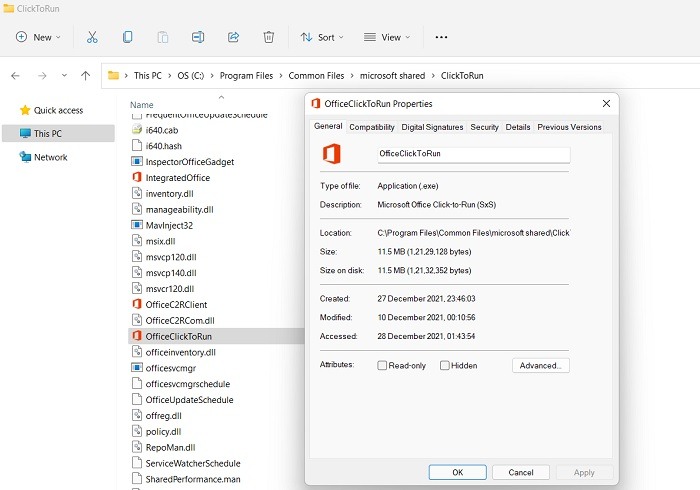
Action: although not harmful by itself, the bogus instances of OfficeClickToRun.exe can clog your system memory. They usually come through infected files and documents, which should be promptly deleted.
7. igfxem.exe
igfxEM.exe is a little-known background process that is crucial to managing the Intel Graphics card and is therefore very important to the video card display. It comes preinstalled on your device and should be left alone, as it doesn’t burden the system at all.
Virus Detection: if you have more than one instance of igfxEM (and its misspellings as shown), validate its digital signatures. If it shows Intel and Microsoft, there is no malware. Otherwise, you don’t have a genuine igfxEM file, and that process has to be removed.
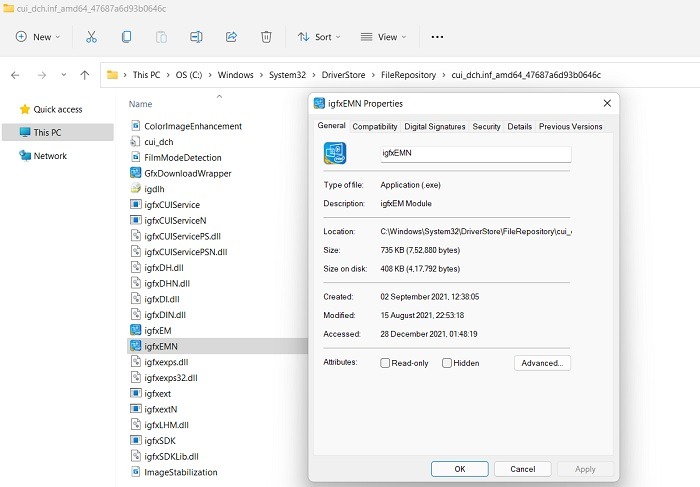
Action: no action should be taken fi you have valid digital signatures – even with multiple Intel instances. If your original Intel Graphics card seems corrupted, try to reinstall the driver from “devmgmt.msc,” Device Management, in the Start menu.
8. Csrss.exe
Csrss.exe stands for Client Server Runtime Subsystem, a legitimate user process intended to manage Windows Graphics activities, such as GUI shutdown and system console services. It is very commonly mistaken for malware. Terminating it can be fatal to your system, leading to an assured crash.
Virus Detection: Like other programs in “C:\Windows\System32,” csrss.exe remains quietly in the background, and you will find only one or two instances in CrowdInspect. Any suspicious files will have invalid digital signatures and Copyright Details missing.
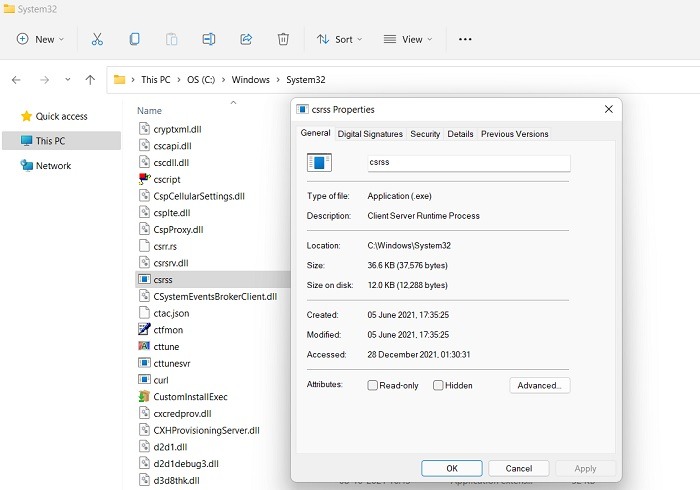
Action: csrss.exe is often used by rogue security software companies and tech scammers as “proof” that a device is infected. This is not real malware, so you should never terminate the existing process because of wrong tech advice.
Also read: How to Reinstall DirectX in Windows
9. GoogleCrashHandler.exe
If you have any Google programs on your Windows device, including Google Chrome, you will find an executable called GoogleCrashHandler.exe, a part of the Google Updater packages. This is not a critical Windows component and can be safely and easily removed, but it’s not always malware either.
Virus Detection: if the digital signature of Google CrashHandler.exe is invalid, that is, it wasn’t signed by Google, then we are looking at a possible sign of spyware or rootkit infection, as the normal process is safe.
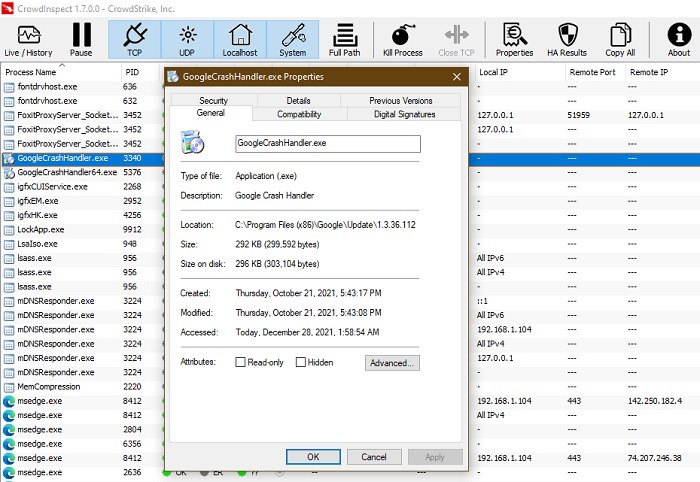
Action: remove any or all instances of GoogleCrashHandler.exe from your system task manager even though it’s not always malware. You don’t want to burden the CPU unnecessarily unless you want to send crash reports to Google.
10. Spoolsv.exe
Spoolsv.exe is a genuine Windows process, integrated with the Printing Spooler service, translates fonts and graphics to printer hardware and any virtual printers. This is a core Windows process that has existed from the very beginning of MS-DOS. Terminating any valid spoolsv.exe process entry will lead to a machine failure and system reboot.
Virus Detection: although it resembles some malware, spoolsv.exe is a safe legitimate Windows process. Any extra processes will lack digital signatures from Microsoft. If malware authors use a similar name to target your system, Windows Defender should alert you to it.
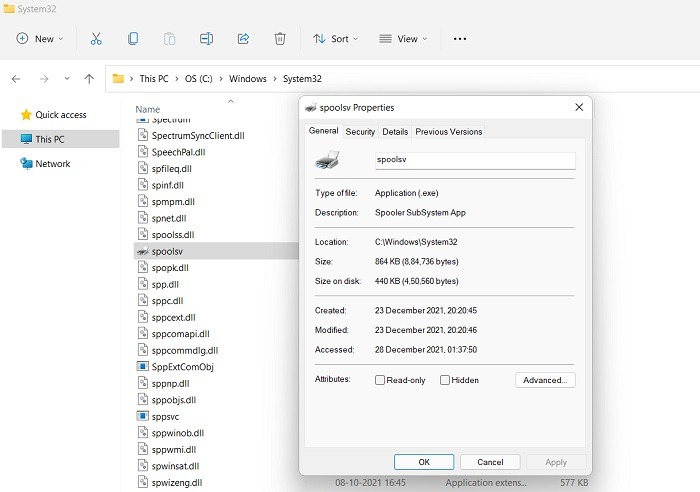
Action: no action should be taken if the spoolsv.exe process has been validated by a Microsoft digital signature. Otherwise, go to task manager to end the process.
11. Task Manager
Windows Task Manager (taskmgr.exe) is a very important program that controls all the core Windows processes as well as the applications. Shutting down this essential program and its derivatives, such as taskhostw.exe can be fatal to your system, and malware authors realize this.
Virus Detection: If you feel a task manager-related program is not behaving correctly, check its file location, which should be in “C:\Windows\System32.” Restart your device to see if the problem has disappeared. If the suspicious task manager instance continues, we are looking at potential malware. Another sign is its digital signature which would be invalid.
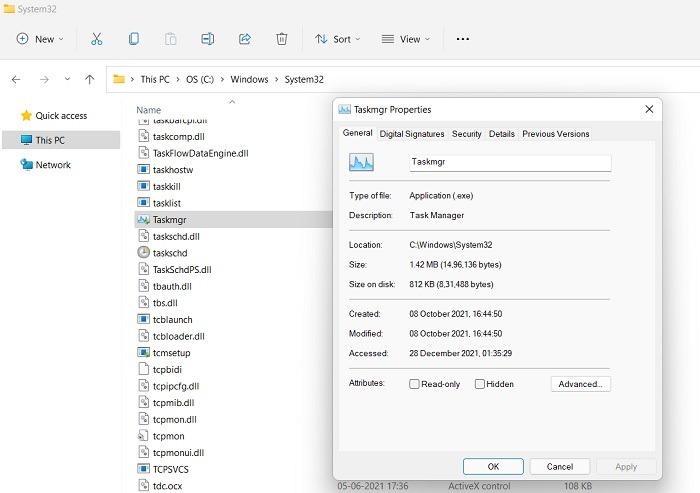
Action: any malware-infected “task manager”-like executable can be identified and terminated from the task manager itself. If, however, you’re facing TaskSchedulerHelper.dll error in Windows 10, take corrective steps as shown.
Summary: Warning Signs of Malware Resembling Windows Processes
Here is a quick summary of how to deal with any suspicious processes that resemble standard Windows system processes. You may or may not be dealing with any malware, but it is important to keep track of these warning signs.
- Check the Application Property Details for correct copyright: each and every program in Windows 11 and Windows 10 has a file location. From there you can access the “Details” in the Properties tab. Make sure the copyright belongs to Windows, TrustedInstaller, or legitimate process owners, such as Google, Intel, NVIDIA, etc. If not, then we’re looking at a potential source of malware that should be removed from the system.
- Check the CPU usage of Windows Process programs: it is normal for Windows CPU usage to shoot up when several systems are running together. However, many instances of the same program slowing down the system is a cause of concern. The unnecessary programs should be identified and shut down immediately.
- Check the suspicious Windows processes for digital signatures: this is the most important and easiest way to validate the authenticity of a process. If the digital signature of a process is invalid and does not come from trusted sources, then there is a good chance it is malware.
- Check the file location of suspicious processes: most Windows file processes have a well-defined location on your PC. It can either be “C:\Windows\System32,” the Program Files, or some other well-defined location. You should not find instances of this process in other areas, such as D drive, as it indicates the chance of malware.
Also read: How to Set Up OpenVPN in Windows
Frequently Asked Questions
1. What should be done if a certain Windows process is indeed harmful?
No legitimate Windows process can harm your system. However, if there are duplicate instances of such processes that contain malware, go to CrowdInspect, right-click that process, and click “Kill Process.” If you have Windows Defender turned on, it will take care of such malware instances. Also read on to learn why Windows Defender is the only antivirus you need.
2. What happens when you terminate a valid Windows process and how do you recover from there?
If you accidentally terminate a valid Windows process, the consequences will depend on how critical the process is for your system. If it’s a non-critical software process, there will be no impact on a Windows device.
For high impact processes such as winlogon.exe and csrss.exe, Windows has a built-in mechanism to prevent their accidental termination. However, if you persist and try to end the system from task manager, your device will power off on its own, requiring a restart. In the worst case, it can lead to a complete blackout and permanent damage due to crash.
If it’s a low impact process integral to the scheduled operation and maintenance of Windows, then the system will report a critical failure and automatically shut down. After a startup, the problem will be gone.