Windows 10 is as secure a Windows OS as has ever existed. With a constant stream of automatic updates (even if they do come with their fair share of problems), and one of the best PC security suites built right into it, it’s fair to say that you don’t generally have anything to worry about when using the OS.
But that doesn’t mean you should get complacent, and staying aware of the extant security threats in Windows 10 is the best way to avoid them. Here are some of the most severe Windows security vulnerabilities that continue to affect users today.
CVE-2017-11882: Microsoft Office 2016
This one was published in 2017, but worrying existed for 17 years until that point!
It exploits a vulnerability in Microsoft Office to seize your computer for cryptocurrency mining, DDoS attacks, and other nefarious purposes. It’s not something that can affect you simply by owning Microsoft Office, however. In order to expose your PC to attack, you’d need to open a malicious file posing as a Microsoft Office document. As soon as you open it, it executes a Powershell script that infects your PC.
Microsoft patched this vulnerability back in 2017, so Windows 7 to Windows 10 users who are up to date should be secure. If you’re on an older Windows OS, you could be at risk. So update and don’t download any dodgy files.
CVE-2018-8174: Internet Explorer
This vulnerability, menacingly nicknamed Double Kill, lies dormant in Microsoft VBScript and can execute itself through Microsoft’s deprecated Internet browser, Internet Explorer. It can work on any version of Windows, although in May 2018 Microsoft patched it out of operating systems it continues to support.
Double Kill exploits a bug in the vbscript.dll, which lets the attacker into the PC’s virtual memory. This is known as a use-after-free (UAF) vulnerability, which is capable of remotely executing malicious code due to the fact that it gains read/write access to your PC’s virtual memory.
Need we say that no one should be using Internet Explorer at this point, anyway?
CVE-2016-0189: Internet Explorer
Speaking of which, here’s an older security vulnerability lingering around in Microsoft’s deprecated browser. It sprung to notoriety in 2016 when it was used to attack a number of organisations in South Korea.
Similarly to the last vulnerability, this one exploits a bug in a non-updated VBScript.dll file in Windows. What’s particularly sneaky about this one is that it doesn’t necessarily require a file to be downloaded but can actually infect your computer if you end up on a compromised website (usually by being redirected from a hacked legitimate website).
The vulnerability has been fixed in IE 9, 10 and 11, but it remains an alarmingly prominent means of attack due to users not updating their browsers.
CVE-2018-4878: Adobe Flash
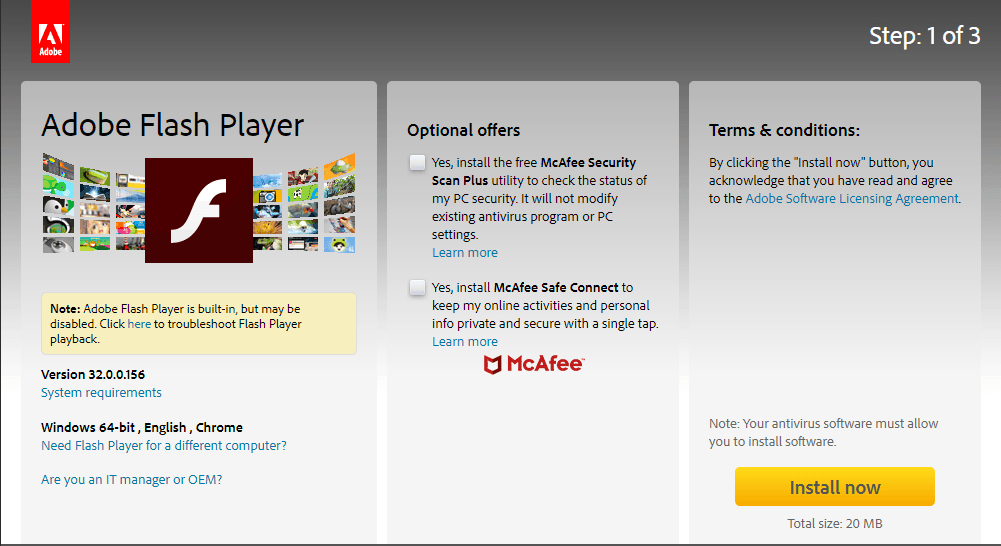
Another dangerous UAF vulnerability, this was uncovered in early 2018 and resides in the historically flaky Adobe Flash Player (before version 28.0.0.161). Like other UAF vulnerabilities, this one can potentially grant the attacker arbitrary code execution, which essentially lets them execute malicious commands on your system.
So what should you look out for? Obscure websites with Flash content and emails asking you to watch videos in the Flash format. This was patched by Adobe soon after it was discovered, but it remains widely used in Exploit kits, which attests to the fact that it still achieves results for attackers.
The lesson here is to always keep your Adobe Flash Player updated.
Conclusion
These are just some of the major Windows 10 security vulnerabilities that you should be wary of. The important thing is not to panic because as long as your keep your OS and software up to date and aren’t using severely outdated programs like Internet Explorer, you should be fine. There are many smaller Windows 10 security vulnerabilities, of course, but there’s only a small chance they’ll ever concern or target you.
If you insist on staying up to date with the latest threats, you can do so at CVE Details.