While at one point Apple devices were considered safe from vulnerabilities, one large reason they were considered “safe” is that hackers weren’t targeting them as much, as they weren’t as popular. Now that they’re more popular, they’re more vulnerable. Additionally, researchers have discovered that iPhones aren’t even safe when turned off. The chip that controls Bluetooth leaves iPhones vulnerable to malware even when powered down.
Also read: Emotet Malware Sending Emails Disguised as IRS
Research Shows iPhone Vulnerability
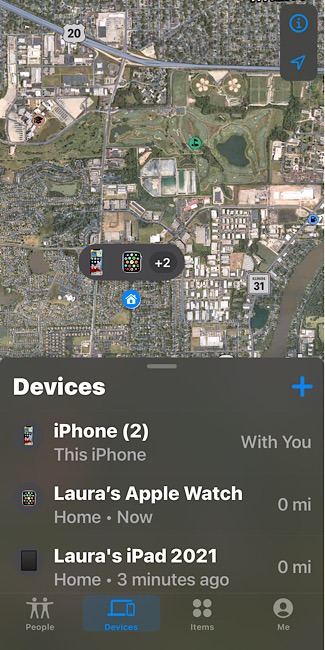
You were likely happy to find that an iOS 15 change allowed you to use the Find My feature even when your phone is powered down. But when you stop to think about it, how can your phone be discovered when it’s turned off? The answer is that it’s not really shut completely off, so it’s still vulnerable.
The Bluetooth chip inside an iPhone allows it to use Find My and other features even when it’s shut down. But the chip doesn’t have a way to digitally sign or encrypt the firmware.
Researchers at the Technical University of Darmstadt in Germany have figured out how to exploit the iPhone feature. They devised a way to run malware on iPhones when they’re shut down. An attacker running the malicious firmware can track an iPhone’s location and run other features, all while the chips are in a low-power mode.
It should be noted that the low-power mode being discussed here is different than the low-power mode that conserves your battery in iOS. The chips’ low-power mode (LPM) allows near field communication (NFC), ultra wideband, and Bluetooth to run even if you turn your phone off or it dies. It will run for another 24 hours.
“The current LPM implementation on Apple iPhones is opaque and adds new threats,” wrote the researchers in a paper that was recently published. “Since LPM support is based on the iPhone’s hardware, it cannot be removed with system updates. Thus, it has a long-lasting effect on the overall iOS security model.”

“Design of LPM features seems to be mostly driven by functionality, without considering threats outside of the intended applications,” added the researchers. “Find My after power off turns shutdown iPhones into tracking devices by design, and the implementations within the Bluetooth firmware is [sic] not secured against manipulation.”
In other words, the researchers believe Apple added this to iOS 15 to allow users to find their iPhones when they’re turned off and other functions without considering the added vulnerability.
Beyond the Research
Now that the research has worried you, you can rest a little easier knowing that they had to use jailbroken iPhones to make the malware attacks effective. So you don’t have a concern with this particular exploit, yet it’s still worthwhile to know that chips in iPhones are leaving them vulnerable to malware, even when powered down.
After all, there may be other vulnerabilities these researchers didn’t discover. And these types of malware infections are difficult to detect.

It’s just important to know your iPhone isn’t as safe in iOS 15 as you thought it was. While it’s helpful that you can find it even if the battery dies after you misplaced it, this feature is also making it less safe.
If you’re not using an iPhone, your device could still be vulnerable: “Hardware and software attacks simialr to the ones described have been proven practical in a real-world setting, so the topics covered in this paper are timely and practical,” said firmware securuity firm Eclypsium senior vice president John Loucaides. “This is typical for every device. Manufacturers are adding features all the time, and with every new feature comes a new attack surface.”
This isn’t the only problem with iOS 15. Read on to learn about user photos being deleted from iCloud.