When someone imagines an attack on their computer, they think of some remotely-installed virus that could do all kinds of nasty stuff on a software level. They’d never guess that the CPU itself can end up functioning in all sorts of weird and unpleasant ways. What does this mean for people who have computers with Intel CPUs, and how could this affect us all in the future? And, much more importantly, what can you do to protect yourself?
How Does the Attack Work?
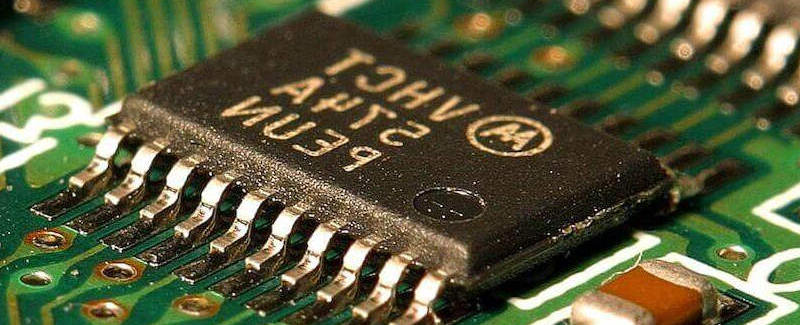
The target is not the CPU, per se, but the infrastructure that supports it via Intel’s Management Engine (ME). The Skylake and Kaby Lake processors have an exclusive system of chips known as the “Platform Controller Hub” (PCH), which are kind of like another system running in the shadows of what you see in front of you. It has its own (rudimentary) operating system called MINIX, its own little CPU, and other supporting components that help corporate administrators gain access to the computers in their offices and control them in a limited capacity.
Here’s the kicker: MINIX isn’t actually owned or licensed by Intel. They simply put it into their chips’ support structures without the knowledge of its creator. The microkernel operating system’s original purpose was to educate college students on its inner workings so that they can better understand how to build their own low-level software.
So, why did Intel go through all this trouble and implement this ME running in parallel with whatever you’re using to run your programs?
The PCH is particularly helpful for large businesses with thousands of computers, which might cease to function at any time and would otherwise need a sysadmin to visit each one and solve each problem individually. This just lets an administrator make sweeping changes when systems cannot even boot.
The problem with this is that non-administrators (e.g. hackers) can do the same thing.
Accessing the Joint Test Action Group (JTAG) interface to administer Intel’s ME requires one simple BIOS change, a USB dongle, and a couple of little tricks on top of that to gain low-level access to the computer’s hardware. Once you’re in, you’re basically in God Mode, able to execute code at your whim without alerting a single anti-malware application.
This could spell disaster for the thousands upon thousands of businesses that use Intel products.
Why Should I Be Concerned About CPU Hacking?

Everything that runs on your computer, from your operating system to the browser you’re using to view this article, has to boss someone around in order to function. That “someone” is the CPU. For a computer to work at all, it needs to send instructions to that big old chip that takes the spotlight from every other piece of hardware.
Once you gain control of the peripheral system that administers the chip, you have carte blanche to do whatever you want to do to that computer, including stealing its most sensitive data (unless it’s encrypted). The worst part about it is that there’s nothing you can do about it once someone gains access.
How to Protect Yourself

To completely rid yourself of the ME, you will have to do things that could end up damaging your computer. If you’re trying to protect your personal devices, just don’t allow any unknown person to plug in anything to your USB ports.
On the other hand, if you are trying to protect your business, point your IT staff to this source repository containing the primary removal utility provided by a group of researchers that found the vulnerability in Intel’s ME. You should also point them to this, which will remove as much of the firmware as it can without breaking the computer.
Please note: you’re still taking a risk in using these, and as such, we cannot be responsible for any damage done to your computers as a result of running this code.
The more comfortable thing to do, in both situations, is to just monitor who has access to your computer through your USB ports. To properly exploit this vulnerability, someone has to have physical access to your computer. Easy enough, right?
If you have any more ideas to share regarding protecting your systems from this exploit, lend a hand in a comment!