Everyone uses WiFi. It’s a fact of modern life, but it does come with some serious security risks and concerns. Home WiFi may just be the most insecure part of your connection to the Internet. It potentially opens you up to attacks from the Internet as well as right next door.
While no security measure is perfect, there are some simple steps that you can take to improve the security of your home WiFi and make it more difficult for attackers to access.
Change the Name (SSID)
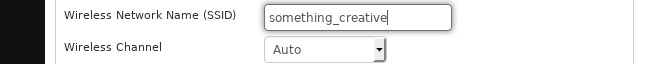
This one is very simple. Change the name of your network. Attackers know the default names that router manufacturers and ISPs use. If they can figure out what type of router you’re using just by looking at the name of your network, they can tailor their attack to your exact router much more easily. It saves them both time and effort.
Plus, this kind of information opens the door for more sophisticated exploits that attack your router’s specific firmware. An attacker can exploit that firmware directly and potentially gain even more access more discreetly than if they were just to figure out your password.
Change the Admin Username and Passphrase
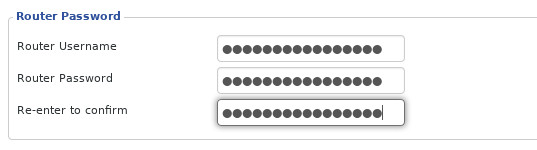
The logic here follows the same line as the previous section. You need to change the username and password of your network admin user.
Attackers know the defaults, and they’re going to try those first. Don’t think that you’re clever by just changing the password or changing it to be one character off. Attackers have a tool that can test thousands of possible password and username combinations very quickly.
Change the admin username to something somewhat difficult to guess. The password should be a passphrase. That means that it should be a short phrase containing at least one more obscure word. It should also make use of capitalization, numbers, and a couple of special characters.
Use Strong Encryption
If you’re not using encryption on your wireless network, you’re doing it wrong, big time. Actually, if you are using encryption, you still might be doing it wrong. Not all encryption is created equal. Make sure you’ve chosen the right settings.
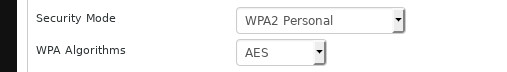
Choose “WPA2 Personal” for your network. If you can set up the enterprise version and know how, that’s a little better, but it’s really not easy unless you already have some experience with it.
For the encryption algorithm itself, choose AES. Do not include TKIP. AES provides much stronger encryption and is much harder to exploit. TKIP is only included as an option for backward compatibility, and now, if you actually need TKIP, update your devices.
Choose a Better Passphrase

The passphrase that you use to sign in to your network needs to be strong, too, and it needs to be different than the one for your admin account. Pick something several words long. Include at least one less commonly used word and a few numbers and special characters. Your passphrase should be at least fifteen characters long.
Rotate Your WiFi Passphrase
Even if your WiFi passphrase is incredibly strong, you need to change it. Like with any passphrase, it’s a good idea to rotate in new ones every so often. That doesn’t mean you need to change your passphrase every other day, but every couple of months is a good idea.
Disable Your Guest Network
Guest networks can be a double-edged sword. Sure, your guests aren’t signing on and getting access to your entire network, and they aren’t using your passphrase. If your guest network doesn’t have a password, though, you’re still opening yourself up to anyone who wants to connect. Essentially, you’re giving attackers a foot in the door.
The only exception here is if you can create a separate guest passphrase for your guest network. If your guest network has the same level of security as your main network, it’s okay. Otherwise, disable it, and if you don’t trust your friends, change the passphrase when they leave.
Enable a Firewall
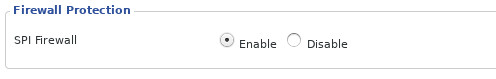
Not every router has a built-in firewall, but if yours does, enable it. A firewall can serve as your first line of defense. They’re specifically designed to manage and filter traffic entering and exiting your network and can lock down attempts to gain access through unused ports.
Even if you have firewalls enabled on your devices, it’s a good idea to add a second layer of security. Do you really want to risk an intruder making it into your network only to try to stop them after? It’s much easier for an intruder to launch an attack from inside your network than outside. Plus, they can monitor your traffic.
Use a VPN
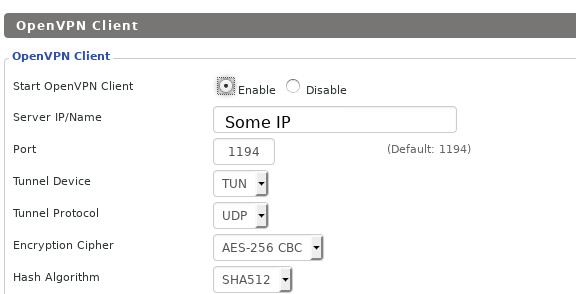
You’re not going to stop your neighbors from breaking into your network with a VPN, but you can help stop attacks from outside your immediate area that way.
When using a VPN, connect first to the VPN server, then to the outside Internet. All of your traffic appears to be coming from the VPN. That includes any information about your local network because VPNs create virtual local networks. While you’re connected to them, your computer is on both your physical local network and the virtual one. The Internet can only see the virtual one.
VPNs have the added benefit of partially anonymizing your traffic. No, a VPN alone won’t make you completely anonymous online, but it certainly helps.
Disable WPS

WPS stands for Wifi Protected Setup. It’s a system for connecting to an encrypted WiFi network without entering a passphrase. There are a few different implementations of it, but they all do relatively the same thing.
While WPS might sound good on paper, it’s not nearly as good in practice. WPS has known exploits and security holes. What’s worse, it’s enabled by default on most routers. If you can keep track of our passphrase, there’s no need for WPS. Disable it and close those security holes.
Manage Your Router Firmware
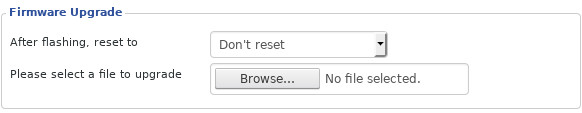
Like your computer, your router has an operating system. Unlike your computer, security updates aren’t pushed to it automatically. You need to manually update it.
Some routers can download their firmware updates from the Internet. For others, you have to download them and load them onto the router manually from your computer. Either way, you need to stay on top of it.
Like with computers, updates often include important security fixes. If you leave your router without those fixes, you might be allowing your router and network to remain open to proven exploits.
You don’t have to do this very often. Just check for updates every month or so, and you’ll be able to stay ahead.
If you’re more technically skilled, you might want to consider using custom open-source router firmware. There are a few really great aftermarket firmwares that you may be able to load on your router, and they tend to see faster updates and a lot more features. If you’ve never done this sort of thing before, be careful. You can destroy your router.
Disable Remote Management/Unnecessary Services
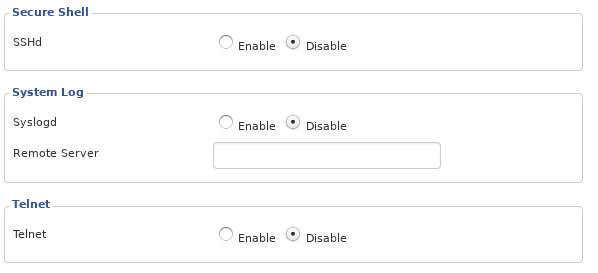
Many routers have remote management services. In some routers, those services are enabled by default. Don’t be mistaken here. This isn’t the web interface that you use to manage your router from within your network. Remote services allow you to manage it externally. That means that an attacker from the open Internet may be able to gain access to your router’s management interface.
There are not many practical reasons why you’d want to be able to manage your router from outside your network, so you won’t be missing out on much by disabling this potentially dangerous service.
There are other services that routers come with that aren’t strictly necessary. For example, some routers come with SSH or the less-secure Telnet enabled by default. There’s no reason for either, especially because you can use your router’s web interface.
Some routers even have FTP and Samba enabled by default for file sharing. Both of these have more than earned their notoriety for being easy to exploit. If you have them, turn them off.
Closing Thoughts
If you pay attention to security topics or you’ve read an article like this one in the past, you may be wondering why some things aren’t covered. There’s a very good reason.
Static IP addresses, MAC filtering, and hiding your SSID were all omitted because they’ve been proven not to work. Sure, you might be able to discourage some minor meddling, but against the right tools, none of these tactics are effective. You’re better investing your time and effort where it counts, like encryption and strong passphrases.
Your home network is the barrier between the contents of your computers and the rest of the world. Be smart and do your best to make sure that your router is protecting you.








