Have you ever downloaded an application from the Web and wondered if it contains malware and whether you should open it? What about having the need to access a sensitive website, but you are not sure if your computer is safe? Hysolate creates an isolated container for Windows and allows you to run your applications in a sandbox environment. Even if the application contains malware, it will not affect your base system. Think of it like a virtual machine – but a well-integrated one with little technical skills required to start using it. Let’s see how Hysolate works.
This is a sponsored article and was made possible by Hysolate. The actual contents and opinions are the sole views of the author who maintains editorial independence, even when a post is sponsored.
Getting and Installing Hysolate
There are two versions of Hysolate: the free one for public use and the premium one for enterprise. The free version will set up an isolated container on your Windows system, but if you need remote control and/or advanced securities policies, you will need the enterprise version.
Note: we will only cover the free version in this review.
One thing to note is that the software requires a computer with decent specs. You need to have a Windows 10 machine with 8GB RAM, a CPU with virtualization technology (VTx/AMD-V – Intel Core i5 or later) and a solid-state drive with at least 10GB of free space.
To get started, download the free version of Hysolate. (Do note that Hysolate doesn’t provide a download link on its site. You have to fill in the form with your email address for the download link to be sent to you.)
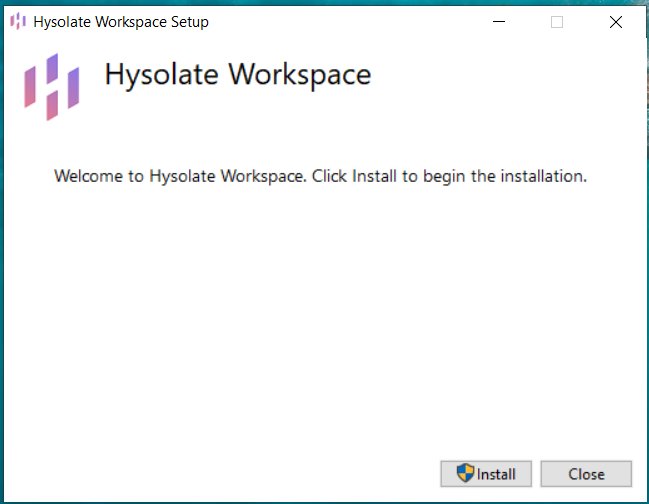
The installer file is about 334MB in size. Run and install it on your Windows 10 machine.
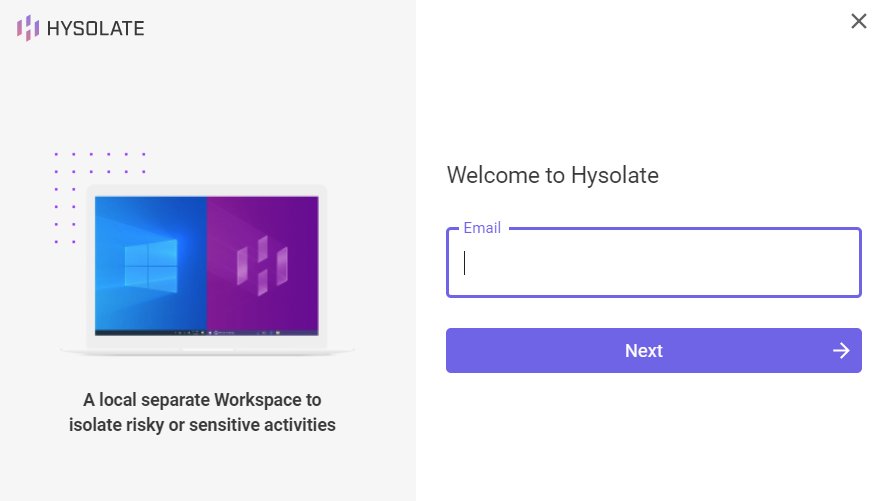
Once installed, it will prompt you to enter your email address followed by the verification code that was sent to your email address.
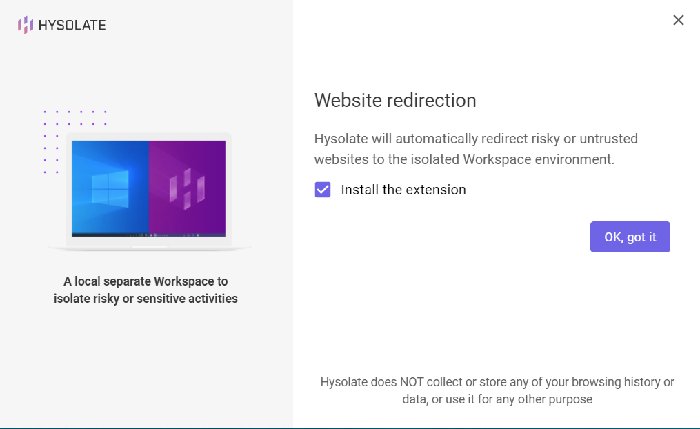
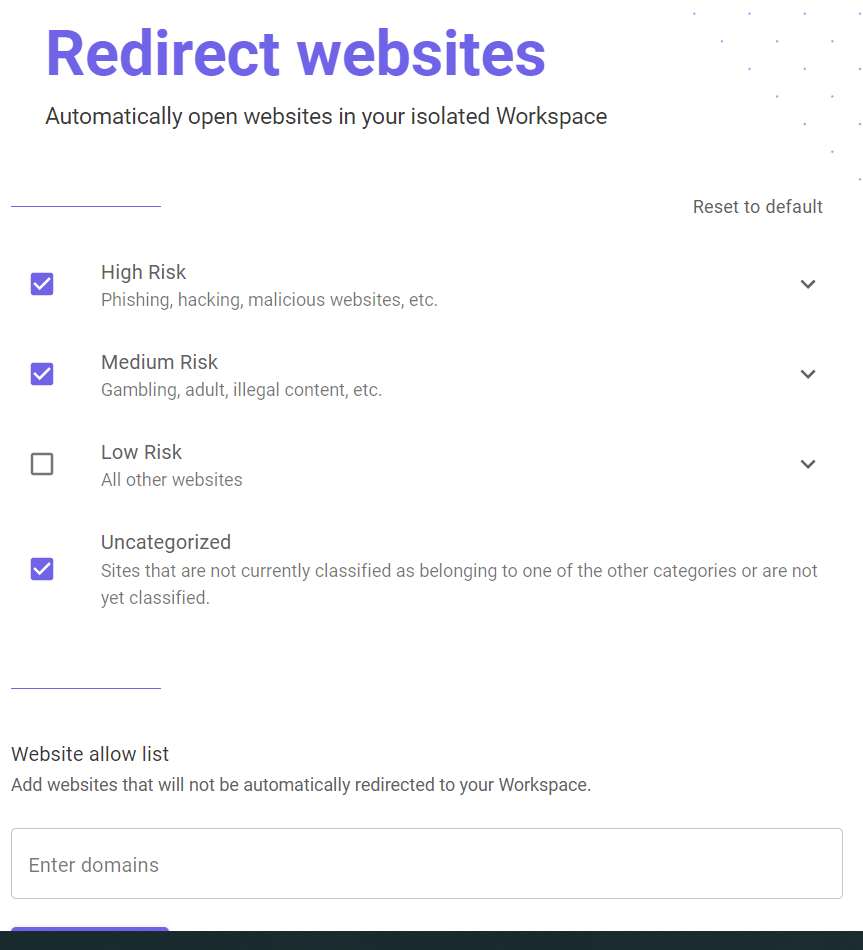
Next, it will prompt whether you want to install the browser extension that will automatically redirect risky or untrusted websites to the isolated environment. Do note that the browser extension only works with Google Chrome. If you don’t have Google Chrome on your computer, even though you check the “Install the extension” button, nothing will be installed.
After the installation, restart the computer.
Using Hysolate (Endpoint Threats Flavor)
Hysolate is set to auto-run during startup, so once you restart your computer, you should see the prompt in the taskbar. You can also choose to take a tour if you want.
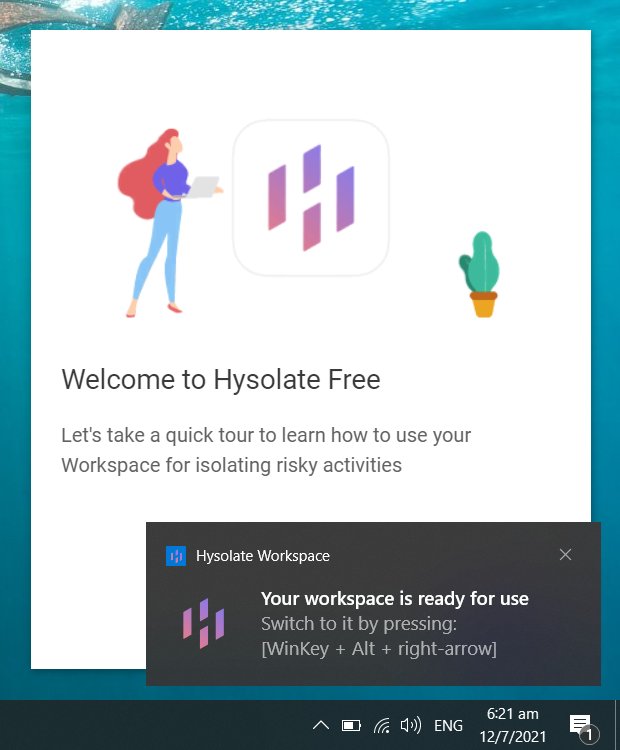
All you need to know is that from now on, you just have to press Win + Alt + the Left/Right arrow keys to switch to the isolated environment.

A few applications like Google Chrome – 7zip and Notepad++ – are preinstalled in the isolated environment, so you can start to browse the Web or download applications to install right away.
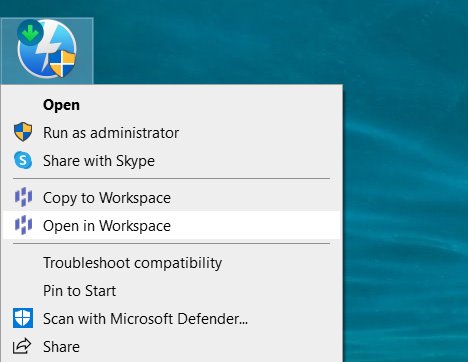
There are a few interesting and useful features that Hysolate integrates into your system. You can simply right-click on a file and have it open in the isolated environment. This is useful if you want to install software downloaded from an unknown source. Simply right-click on it, choose “Open in Workspace,” and it will run and install in Hysolate.
In addition, there is a shared clipboard between the host and the isolated environment. Simply press Ctrl + C to copy in one place, and you can use Ctrl + V to paste it to another environment. This works two ways between the host and the virtualized container.
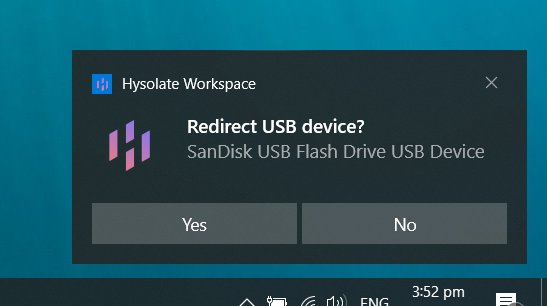
There has been many exploit cases involving USB drives, and now many people are worried about inserting USB drives into their computer. Hysolate comes with an option to redirect your USB drive when you plug it in. You can then view the USB drive content in the Hysolate workspace and copy the files over to the Host system after you have verified that they are safe.
Website Redirect
If you have installed the Google Chrome extension for Hysolate, it can watch your browsing URL and auto redirect you to the isolated environment when you are on a high-risk site. However, it doesn’t protect you if you still foolishly enter your credit card detail on the scam site in Hysolate.
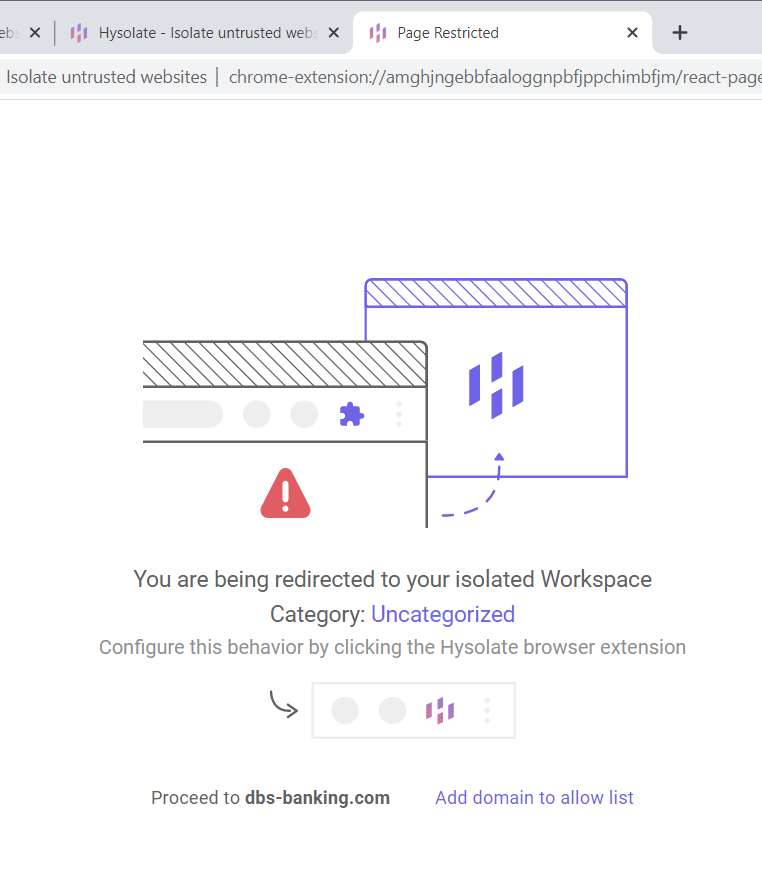
You can also customize the extension for the list of websites you want to allow/redirect.
Hysolate Sensitive Access flavor
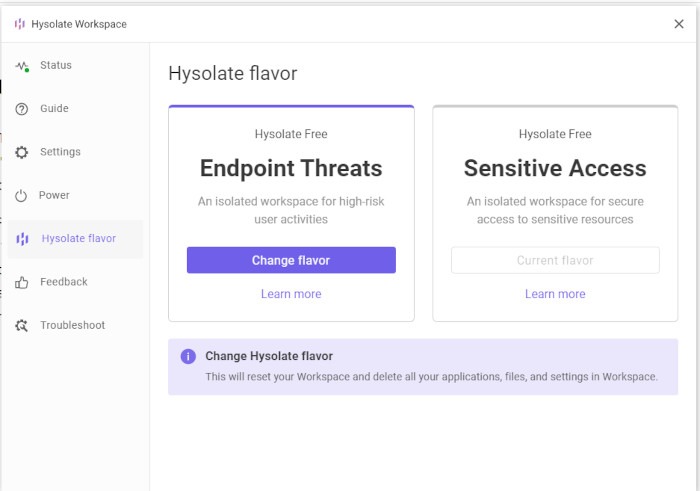
Hysolate also comes with another virtual machine that allows you to access sensitive websites or files. This Sensitive Access flavor is different from the Endpoint Threats flavor and the two are not interchangeable. When you switch from one to the other, Hysolate will destroy the current VM and create another new VM for your usage.
To explain further, the differences between the two flavor are:
- Endpoint Threats – This is mainly for you to run applications or websites that you don’t trust on a secure environment so that your host machine will not be affected by any malware or ransomware.
- Sensitive Access – For cases where you don’t trust your host machine and need to access sensitive websites or files. Hysolate will create a secure and encrypted environment for you to access sensitive information.
Usage
To switch to Sensitive Access flavor, open the Hysolate Settings and click on the “Flavor” tab. Click “Change flavor” under the “Sensitive Access” section. Once confirmed, it will destroy the current VM and create a new one.
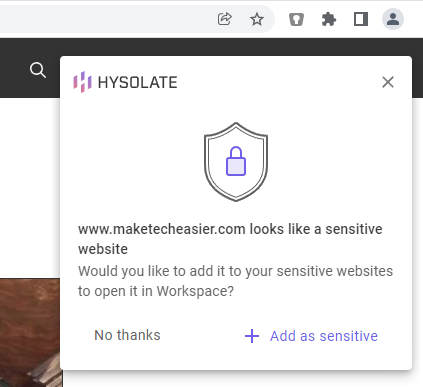
Remember the Chrome extension you installed earlier? Now whenever you surf, it will show a prompt to ask if the current URL is a sensitive site. If it is, you can click “Add to Sensitive” and have it auto-redirected to the VM. If you are accessing risky websites in the VM, you will be redirected back to the host machine to protect the VM.
Similarly, you can open your sensitive files in the new VM.
A few things that you need to know for this VM:
- User data in the sensitive VM is encrypted (including anything you download or open in the VM, your cached credentials, etc.) so that ransomware on the host cannot exfiltrate sensitive data for extortion purposes, etc.
- You don’t have admin rights in the sensitive VM. This is to prevent accidental installation of persistent malicious malware.
- The sensitive VM is protected against keystroke and screen capture.
- You cannot copy and paste sensitive content out of the sensitive VM.
- The existing malicious browser extensions on your host machine cannot access the browser running in the VM.
- There is no access to printers/USB devices on the VM to prevent accidental data leaks via these channels.
- The VM is non-persistent. It will reset to a pristine OS image on every restart.
Wrapping Up
The good thing about Hysolate is that it is easy to use and well-integrated with the host system. Even if you are not technically inclined, you can set it up easily and start running applications in the virtualized environment in minutes. That it’s free makes it an even better deal.








