You know that little “Do you want to send a read receipt?” message you get every now and then when you open an email? You might reasonably assume that if you don’t see that message you’re not sending anything back. That’s not necessarily true. Thanks to the magic of something called a tracking pixel (a tiny image embedded in HTML and/or JavaScript), just opening the email can tell the sender not only when you did it, but your IP address (and, therefore, your location), email client, and operating system.

Tracking pixels have been around for quite a while now, both in emails and on webpages, and have periodically come under fire for being a very sneaky way to gather data, as the user is typically not informed that they’re sending any information. It’s not just companies, either: this technology is freely available for individuals to use, making it possible for anyone to find someone else’s location just by sending them an email with a clickbait subject line and a tracking pixel.
Also read: The 7 Most Secure Email Services for Better Privacy
What are tracking pixels and how do they work?
A tracking pixel is just a 1×1 image pixel (like a GIF, JPEG, PNG, etc.) that is embedded in an email or webpage the same way that any other image would be, except it’s hidden. Pixels are already pretty tiny, but by making the image transparent, blending it with the background, or manipulating some code, you can make the tracking element essentially invisible. However, it is still an image, so when you open something with the tracking pixel in it, your browser or email client will send a request to whatever server the tracking pixel is stored on.
When the server gets this request, it logs (at minimum) the time, date, and IP address of the device that requested the pixel. If it’s in an email, that log information can be used as an extra-detailed read receipt. If the pixel is on a webpage, it’ll fire your IP address (and possibly other behavioral information) back to whatever server it’s hosted on, where it will be used for traffic analytics and/or to help build a more detailed profile on you.
Tracking pixels in your email
Personal correspondence tracking is probably the most contentious application of tracking pixels, as it feels fairly creepy. Case in point: Superhuman, an email client startup, got some flak for building in an automatic tracking pixel system that told its users when and where their messages had been opened. They haven’t removed the feature, but did disable it by default and remove location data in response.
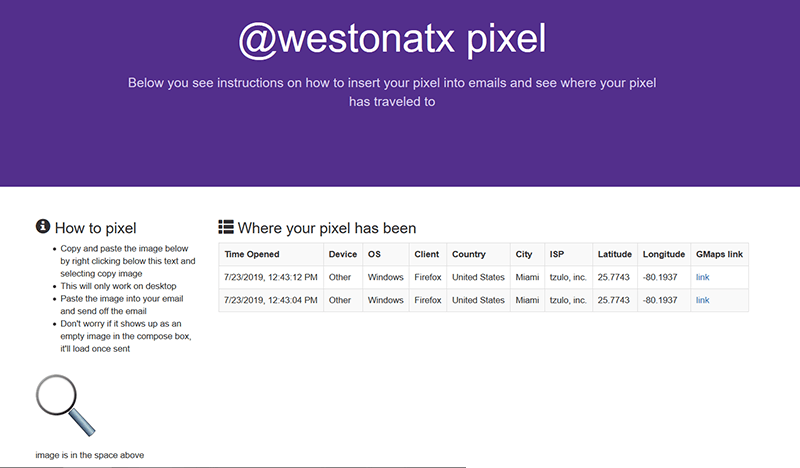
You don’t have to be a superhuman user to put a tracking pixel in your emails, though – a quick search will turn up plenty of services that will help you with your “marketing.”
Having personal correspondence tracked that way feels intrusive, sure, but marketing emails aren’t being used to stalk us or judge us for how long we wait to respond after opening a message. They’re mostly trying to optimize their communication strategies.
Are Windows or Mac users more likely to click through? Are your subject lines resonating with people in Wisconsin but flopping with Oregonians? If you’re trying to refine your email marketing (or find good spam targets), getting this kind of data from tracking pixels is honestly too good to pass up and companies probably aren’t going to stop.
Also read: How to Disable or Automatically Delete Google Location History
If you’re not keen on getting spam, though, be aware that loading images (or even other HTML elements, honestly) in spam emails will probably fire a tracking pixel that notifies the spam server that you’re an active email user who clicks on spam. Your prize issue … more spam! Also, the spammers know where you live now.
Tracking pixels on the web
Learning that our emails are giving up information may be a bit of a shock, but we’ve come to assume that webpages are tracking us pretty much all the time, so this is less surprising. Tracking pixels are just one of many tracking methods that sites use in addition to cookies, and you can find them being used in a lot of popular analytics and ad targeting tools.
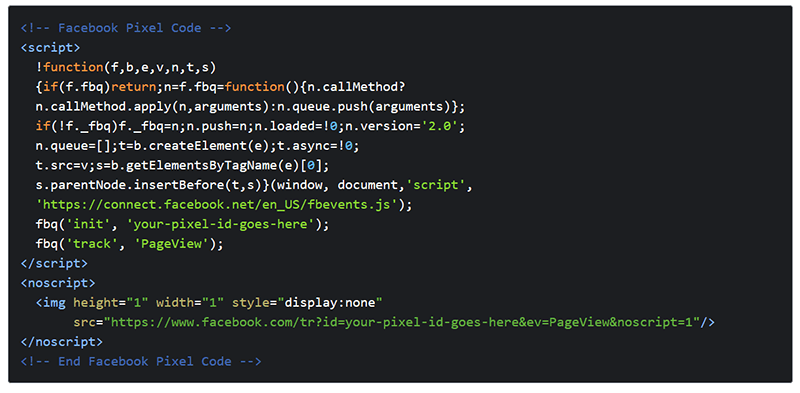
The Facebook pixel, for example, allows sites to connect to Facebook advertising functionality by embedding a tracking pixel that fires visitors’ IP addresses and browsing activity back to Facebook, which can use that data to find your profile and serve you ads. They’re hardly the only company doing this, though. Pixel tracking is widespread among ad-targeting and analytics firms that specialize in collecting and brokering user data.
Can they be stopped?
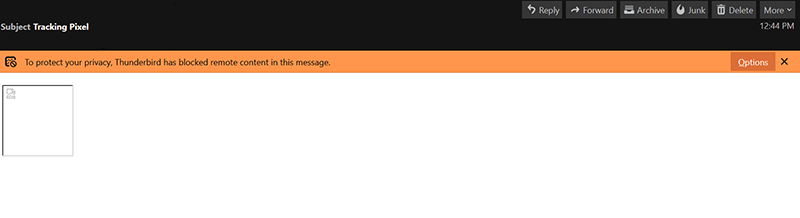
As far as email tracking goes, the main fix is to make sure your email client is set to ask before it loads external images. The catch is that you have to say no to all the images in the email, some of which you may actually want to see. If you want to go full nuclear, you can just disable HTML in your emails altogether. Some providers and clients allow you to do this, and there is something of a security/privacy argument to be made for plain-text emails.
Alternatively, if you use Gmail (and only Gmail), you can get Ugly Email or Pixelblock, which are Chrome extensions that detect and disable tracking in emails for you without blocking the other images.
On the web, things are more complicated. Web beacons are designed to be hard to find, and while privacy extensions like Ghostery and Privacy Badger can catch some of them, they probably won’t get them all. GDPR may require sites to ask your permission before tracking you, but compliance is scattered and varies by user region. In any case, some trackers are probably going to get through any screens you put up, so for truly private browsing you’ll need to go through, at minimum, a VPN and Tor.