Distributed denial of service (DDoS) is the most common way that hackers bring websites, gaming servers, and various other services that depend on the internet down abruptly. The severity of the attack could vary, ranging from a mild inconvenience to a total takedown of a server. Sometimes it’s more than just a server involved. Yes, for many years ambitious groups and individuals have had much larger targets in mind when planning their attacks. Some have even succeeded. Where do they draw the limit? Is there a limit at all to how large these attacks can get?
What We’ve Learned From History
The number of DDoS attacks, at the time of this article’s publishing, is rising. With such easy access to the tools that allow people to perform these attacks, the problem is probably going to get worse. The ripple effect of this increase in attacks can be felt with many high-profile attacks such as the downtime experienced by the Sony PlayStation Network in 2014 which caused panic for millions of people who were attempting to access the network.
Governments have also gotten in on the action. One example of this would be the March 2015 attack on GitHub by the Chinese government that led to two projects getting shut down.
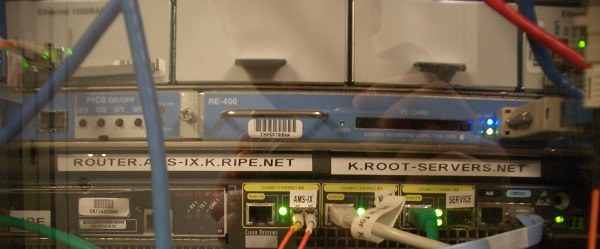
Other attacks include the DNS root server attack of 2007 which managed to cause a significant amount of trouble. When a root server is down, none of the domains under its control can be accessed making a very enormous amount of websites incapable of operating.
What Do We Measure?
There are two ways to measure a DDoS attack. You can either count the amount of bandwidth sustained during the attack or the number of people affected by it. The second metric is very difficult to assess since we don’t have any way to truly collect an accurate statistic on the number of people who are inconvenienced by any particular attack. However, we can measure bandwidth.
March 18, 2013, marked a day that would go down in history as the most unprecedented DDoS attack ever executed in terms of bandwidth until that point. Spamhaus, a website that tracks spammers, succumbed to an attack that eventually exceeded 120 gigabits per second. Such a large-scale attack, however, was dwarfed almost immediately by another attack in 2014 that managed to hit the 400 gigabit-per-second milestone, slowing down Internet connectivity for much of the European Union and part of the United States.
Those two attacks are by far some of the worst we’ve seen in history. The fact that hackers are finding it easier to find ways to gain more bandwidth makes it very possible that we will witness attacks that cause much more damage in the future. If this trend continues throughout the next few years we might as well call this the Golden Age of DDoS.
How We Can Stop It
Many companies are currently investing in solutions that mitigate DDoS for them, but it’s not always within a business’ budget to employ state-of-the-art hardware and software for this purpose. We will have to help them in this fight, and the best way we can do this is to be prudent about what we download and the websites we access. Attackers use other computers through viruses and shady scripts to execute a DDoS, making thousands of systems send connection requests to one particular server. Make sure that you download things only from trustworthy sources!
What do you think? Do you have any other advice for how we can help stop DDoS? Tell us more in a comment!







