Code injection, often referred to as remote code execution (RCE), is an attack perpetrated by an attackers ability to inject and execute malicious code into an application; an injection attack. This foreign code is capable of breaching data security, compromising database integrity or private properties. In many instances, it can bypass authentication control, and usually these attacks are associated with applications that depend on user input for execution.
Generally, applications are more vulnerable if the code is executed without first passing through validation. A simple case of a vulnerable code is shown below.
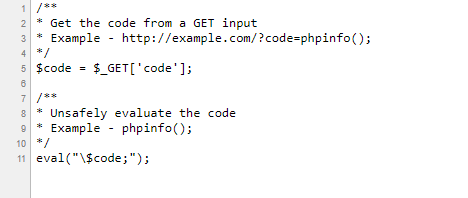
In the above example the PHP info page is vulnerable and will be displayed if the URL http://example.com/?code=phpinfo(); is run.
Due to the fact that user interaction with applications is more and more a necessity in today’s online world, code injection has grown and has become a real threat to many online resources.
Types of code injections
There are mainly four types of code injections: SQL injection, Script injection, Shell injection, and Dynamic evaluation. All of these have the same working principle, that is, the code is introduced into and executed by applications, but the two I will pay focus on are SQL injection and Script injection.
How SQL injections work
In the case of SQL injection, the attack is aimed at corrupting a legitimate database query to produce falsified data. The attacker first has to locate an input within the targeted web application that is included inside of an SQL query.
This method is only effective if the web application has user input included within an SQL statement. A payload (a malicious SQL statement) can then be inserted and run against the database server.
The following server-side pseudo-code is a simple example of authentication that can prove vulnerable to SQL injections.
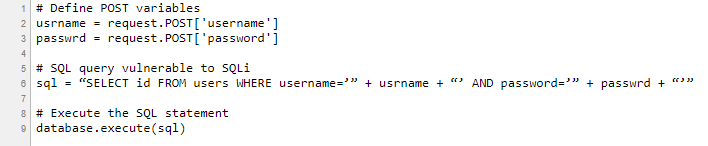
In the above code the attacker could insert a payload that would change the SQL statement executed by the database server. An example would set the password field to:
password' OR 1=1
This automatically causes the following statement to be run against the database server:
SELECT id FROM users WHERE username='username' AND password='password' OR 1=1
What SQL injection can do
This is the most common type of code injection. Considering the fact that SQL is the language used to manipulate data stored in Relational Database Management Systems (RDBMS), an attack with the power to give and execute SQL statements can be used to access, modify and even delete data.
It can give the attacker the ability to bypass authentication, have full disclosure of data stored in the database, compromise data integrity and cause repudiation issues, altering balances and voiding transactions.
How to prevent SQL injections
There are a few steps to make your applications less vulnerable, but before any of these steps, it is best to assume all user-submitted data is evil and to trust no one. Then you could consider the following:
- Disable the use of dynamic SQL – this means don’t construct database queries with user input. If required, sanitize, validate and escape values before making a query with user input data.
- Make use of a firewall – A web application firewall (software or application based) will help filter malicious data.
- Purchase better software – This simply means coders will be responsible for checking and fixing flaws.
- Encrypt or hash passwords and every other confidential data you have, this should include connection strings.
- Avoid connecting to your database with admin privileged accounts unless you absolutely need to.
Script injection
This security vulnerability is a threat that allows an attacker to inject malicious code straight through the web forms of data-driven websites via elements of the user interface. This attack is often referred to as Cross-Site Scripting or XSS. The , , , , , , ,
How to prevent script injections
The steps to prevent script injections are dependent on the programming code you are using. Generally, you will want to:
- validate and sanitize user input (any form of input fields) by striping out or escaping potentially malicious content
- clean up query strings in URLs
- validate and sanitize all forms of data, arrays and objects before executing in the server
Conclusion
Simply said, prevention is better than a cure. With new updates in technology, there are more threats our systems are going to be exposed to. To stay on top of things, it’s important to have the latest patches and updates and to keep an ear out for best practices. This makes it harder to fall victim to these malicious attacks.