Without modern cryptography techniques, the Internet as we know it would not exist. Secure communications enable virtually all online interaction. Encryption algorithms permit the secure exchange of data and confident verification of identity. Without these common cryptographic tools, our modern connected society could not function as it does today.
Symmetric Key Encryption Algorithms
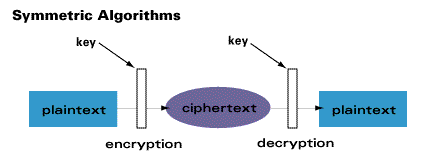
Symmetric key encryption algorithms rely on a secure password to act as the key. This is the oldest form of encryption. Symmetric keys form the basis of everything from combination locks to modern hard drive encryption. AES, DES, and Blowfish are all modern symmetric key encryption algorithms.
Because symmetric encryption requires a shared key, the key exchange must be performed securely. While modern techniques like the Diffie-Hellmen key exchange permit exchanging a shared secret over insecure lines, it requires significant communication overhead to do so as well as shared trust between communications. If a shared key cannot be exchanged securely, communication cannot be conducted.
While symmetric key encryption is used in online communications, it is almost always paired with public key encryption, allowing for secure communication over open channels.
Also read: PGP Encryption: How It Works and How You Can Get Started
Asymmetric Key (Public Key) Encryption Algorithms
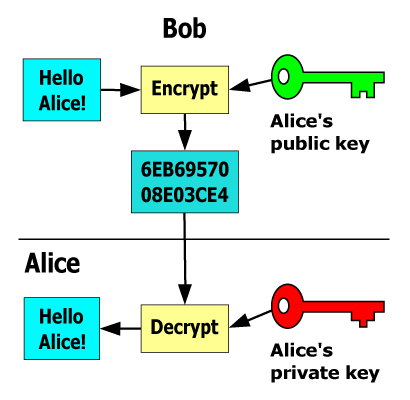
Asymmetric or public key encryption uses a pair of cryptographic keys. These keys relate to each other mathematically. The public key, shared widely, encrypts the message. The private key decrypts the message. As a result, any sender can encrypt a message with a recipient’s public key. Then they can be confident that only the intended recipient can decrypt the message because parties share no secret; they need no trust.
As a practical example, consider this analogy. What if Alice wants to communicate securely with Bob, but she doesn’t trust him?
- Alice purchases a padlock and key combination. She unlocks the padlock with her key and sends the unlocked padlock to Bob.
- Bob places his message in a box and uses Alice’s padlock to lock it.
- Bob returns the locked box to Alice, secured with Alice’s padlock.
- Alice opens the box with the padlock’s key, which only she possesses.
For ease of communication, Alice can duplicate the unlocked padlock and publish it widely. Anyone with the padlock can send her secure communications. With a sufficiently complex lock, an attacker cannot derive the key from the lock alone.
Security in (big) numbers
To remain secure, these algorithms rely on complex padlock/mathematical problems with no known efficient solution. These intractable problems define one-way functions: easy to compute in one direction but extremely difficult to compute backward. RSA, a commonly-used public key algorithm, relies on the difficulty in finding prime factors of integers with hundreds of decimal digits.
To start, an RSA user generates two very large prime numbers. These numbers are then multiplied together to create the product. The user keeps the prime factors which comprise the private key, a secret. The user publishes a public key derived from the product of the prime pair. The public key encrypts messages; the private key decrypts them.
Without knowing the prime factors, finding the prime factors of the product would take an infeasible amount of time. RSA-1024, the minimum standard, uses 1024-bit binary products made from 512-bit binary primes. According to the math, it would require 5.95 × 10^211 years to factor without the key. For perspective, the universe has only existed for a comparatively short 13.75 x 10^19 years.
Hash Functions
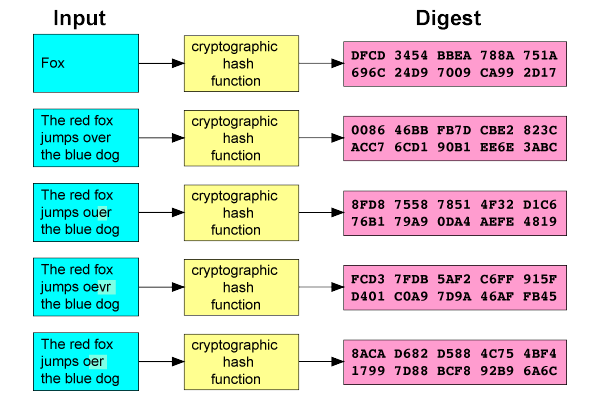
A hash function translates a message of arbitrary length to a fixed-length string called a hash or digest. Cryptographic hashes are deterministic: the same input always produces the same output. Even minor changes to the message will result in a dramatically different hash. Discovering two unique messages that produce the same hash value, called a hash collision, should be infeasible.
Digital signatures and password authentication both use hash functions like SHA. Rather than authenticating your plain text password, login servers use the hash of the password. The server compares this hash against the server’s stored hash. Same hash, same password.
Salted Hashes
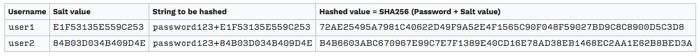
For password storage, companies typically add a “salt” before hashing. This randomly-generated string is concatenated with the password text before hashing, ensuring that even two identical passwords produce distinct hashes. This also defends against a dictionary attack on a stolen table of hashed passwords.
Conclusion
Up until the 1970s, encryption relied on symmetric keys. Only after the proof of public key encryption could two different keys — one encrypting, one decrypting — be used to communicate. This revolutionary change, which allows for communication without trust, is what allows the Internet to exist in the form it takes today. Everything from banking and shopping to messaging and web browsing relies on it.