Yet another industry appears to not be as concerned as we may like in keeping our data safe. When you make hotel reservations and they email you the booking details, you may not be the only person with access to the documents. Symantec found flaws on many hotel websites that showed they were leaking sensitive information.
Hotel Reservation Data Breach
Before we go any further, we need to take a look back a few decades ago and realize how much easier the Internet has made booking travel. Remember when you had to call a travel agent to book a hotel room or a flight?
You could book a hotel if you knew of its existence, but without the Internet, you didn’t know which hotels were located on a certain beach or close to the airport, had you never traveled to the area before. And there was no other way to book flights. Not only did the Internet make booking travel easier, but it left us with so much more control to be able to research all these choices ourselves.
But Symantec tells us that freedom has come with a price. Hundreds of hotel websites have flaws that leak sensitive information, including your name, phone number, address, confirmation email, and even your passport number. Realize that with this information hackers know your address and when you’ll be gone for an extended period of time.
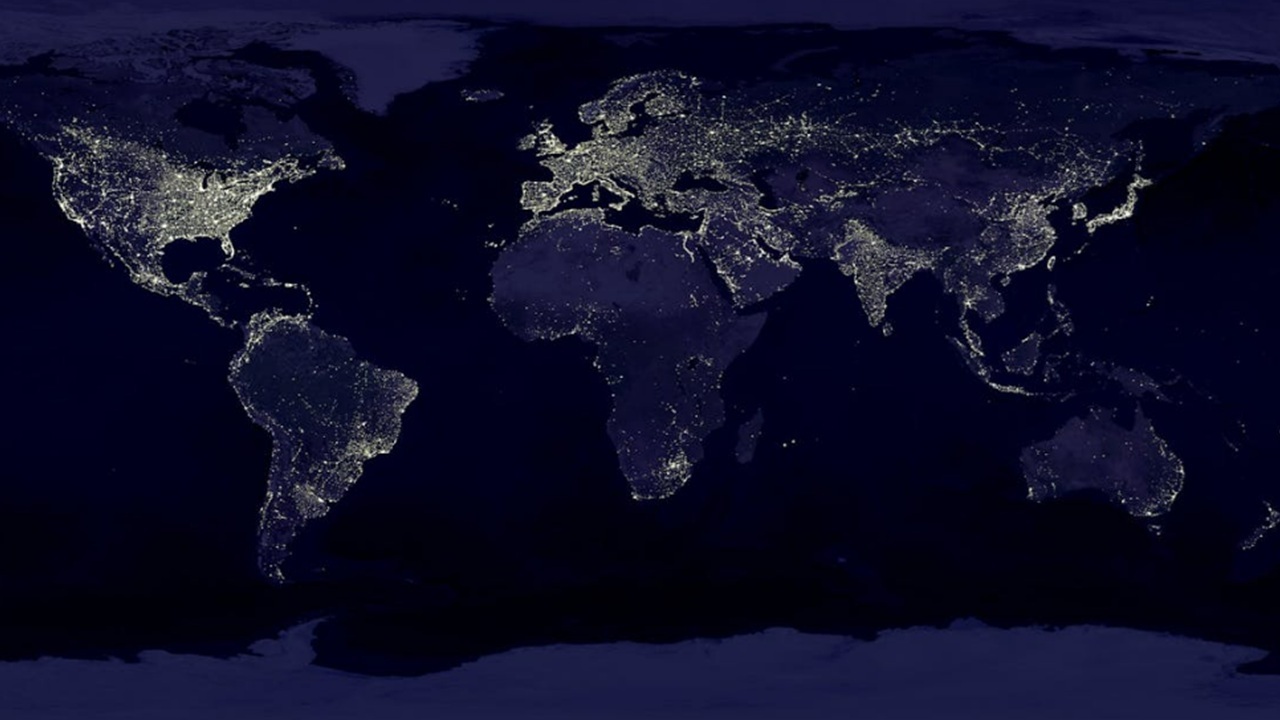
Symantec threat researcher Candid Wueest looked at more than 1,500 hotel websites in more than 50 countries. He found two-thirds of them had security issues.
The Marriott hotel chain has been open about their cyberattacks recently, as has Sheraton, Westin, Starwood, and Wyndham hotels. Marriott admitted last November that hackers had stolen the records of up to 383 million guests. It became one of the largest personal data breaches in history.

One common security flaw among hotels is a URL they email to guests. Around 850 hotel websites don’t require authentication to see the details on that URL. Astonishingly, Wueest notes that one-third of the hotels include the booking number within that URL.
Advertisers and third-party analytics tools are embedded on these pages, meaning they get the URL as well, leaving it open to potential cyberattackers. Wueest found a Google Analytics request for a hotel booking confirmation page included a URL as well as a reservation number.
Many of the hotel websites are also vulnerable to brute force attacks. A machine could guess every possible combination of an eight-character password in less than three hours. On one particular hotel website, Wueest used brute force to view every active reservation.
Hotel Responsibility
Unfortunately, it just doesn’t get much better at this point. The responsibility will be up to hotel chains to improve the way they do things.
Disappointingly, Wueest reports that when he reached out to hotels to show them the issues with their security measures, a quarter of them ignored the warnings for more than six weeks. He recommends they stop including booking information in the URL and start using authentication on confirmation pages.
Do you book travel frequently? Does this news concerning hotel reservation data being leaked concern you? Comment below with your thoughts and concerns.