Windows Defender is pretty lightweight and provides good basic protection while running silently in the background. You can increase the protection levels and harden Windows Defender with a few changes to the Group Policy Editor or to the Registry Editor. Here’s how to do it.
Before making any changes, backup Windows Registry or create a system restore point. It helps you to revert back if you don’t like the changes or if anything bad happens while editing or changing system settings.
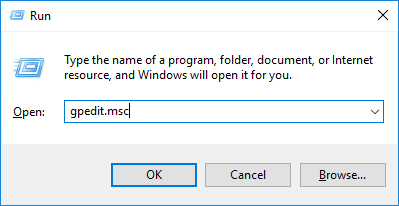
Using Group Policy Editor
Group Policy Editor provides an easy and straightforward way to strengthen Windows Defender. To open Group Policy Editor, press Win + R, type gpedit.msc and press Enter.
In the Group Policy Editor navigate to “Computer Configuration -> Administrative Templates -> Windows Components -> Windows Defender Antivirus -> MAPS.”
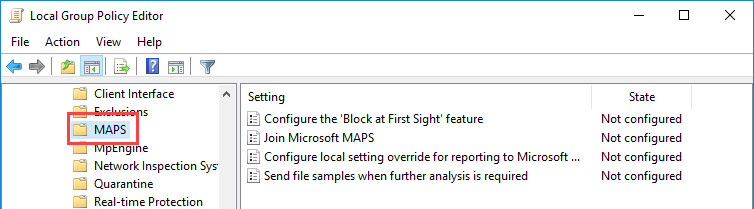
On the right panel you will see four different policies. Configure them as instructed below, following the below order.
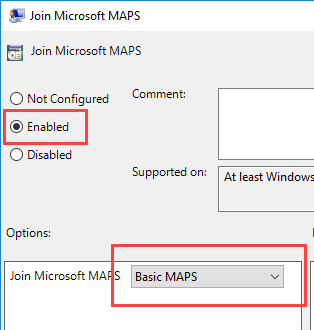
Join Microsoft MAPS: The first thing you need to do is join Microsoft’s MAPS (Microsoft Advanced Protection Service) program. MAPS is an online community that is aimed at quickly detecting lesser-known threats and can even stop new malware infections.
Double-click on this policy, select the “Enabled” radio button, select either “Basic MAPS” or “Advanced MAPS” from the drop-down menu and click on the “OK” button to save the changes. You can find the difference between the Basic and Advanced options under the Help section appearing on the right panel.
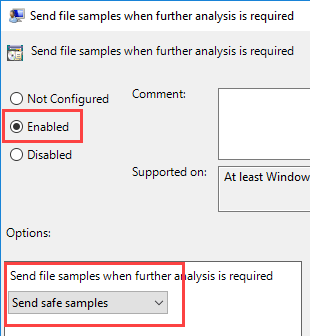
Send file samples when further analysis is required: For MAPS to work properly you need to submit file samples so that it can scan and check with the online community. Open the policy and select the “Enabled” option. Under the Options section you can select between three options: send safe samples, send all samples, and always prompt.
If you select the fourth option, “Never send,” the Block and First Sight feature will not work. Select one of the three options discussed above and click on the “OK” button to save the changes. In my case, I’m selecting the “send safe samples” option from the drop-down menu.
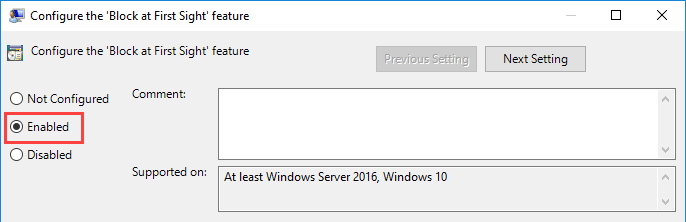
Configure “Block at First Sight” feature: This feature allows real-time MAPS monitoring and only runs certain content after scanning it with MAPS. To enable this feature, open the policy, select the “Enabled” radio button and click on the “OK” button to save the changes.
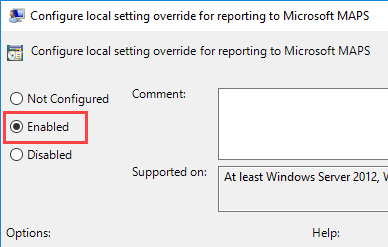
Configure local setting override for reporting to Microsoft MAPS: This setting ensures that the local preference will take priority over Group Policy. To enable this feature, open the policy, select the “Enabled” radio button and click on the “OK” button to save the changes.
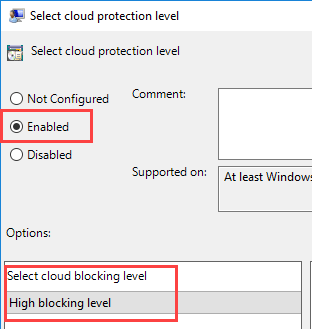
To make things a bit more secure, you can modify cloud protection settings. On the left panel select the “MpEngine” folder. On the right panel double-click on the policy “Select cloud protection level.”
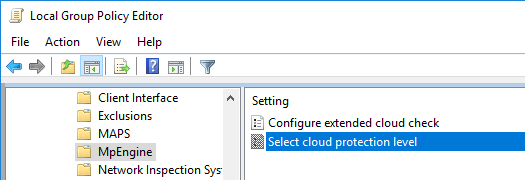
In the policy settings window select the “Enabled” radio button and then select the option”High blocking level” from the drop-down menu under the Options section. Click “OK” to save the changes.
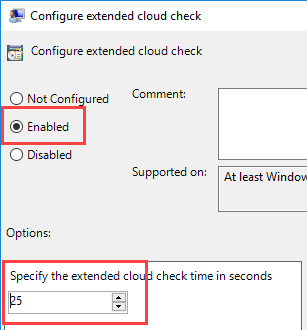
Generally, Windows Defender blocks any suspicious file and scans it in the cloud. By default, the time-out is set to ten seconds. If you want to you can extend the time-out up to sixty seconds.
To do that open the “Configure extended cloud check” policy, select the “Enabled” radio button and then enter the number of seconds under the Options section. You can extend the time up to fifty seconds. So if you enter fifty seconds, then the total time-out for cloud check is sixty seconds when combined with the default ten seconds.
That’s it, just restart your system.
Using Windows Registry Editor
If you are a Windows Home user, then you will not have access to the Group Policy Editor, but you can use Windows Registry to achieve the same result.
You should create two files: “MPEngine Key.reg” and “Spynet Key.reg.” Their content are as follows.
MPEngine Key.reg:
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\MpEngine] "MpBafsExtendedTimeout"=dword:00000019 "MpCloudBlockLevel"=dword:00000002
Spynet Key.reg:
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Spynet] "DisableBlockAtFirstSeen"=dword:00000000 "SpynetReporting"=dword:00000002 "LocalSettingOverrideSpynetReporting"=dword:00000001 "SubmitSamplesConsent"=dword:00000001
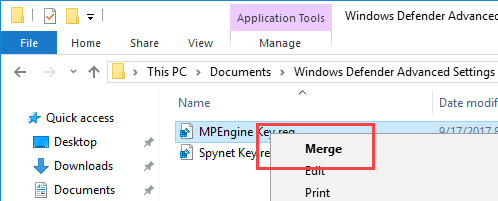
Right-click on the reg key and select the “Merge” option.
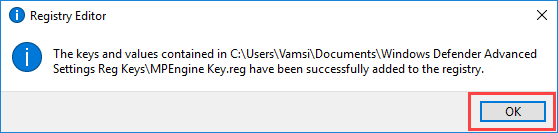
You will receive a warning message; click on the “Yes” button to continue.
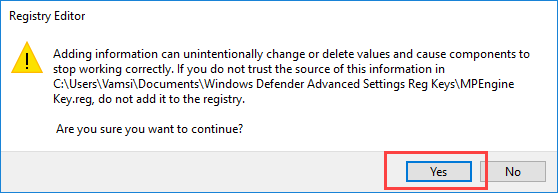
The above action will merge the selected reg file with your Registry. Do the same thing with the second registry file.
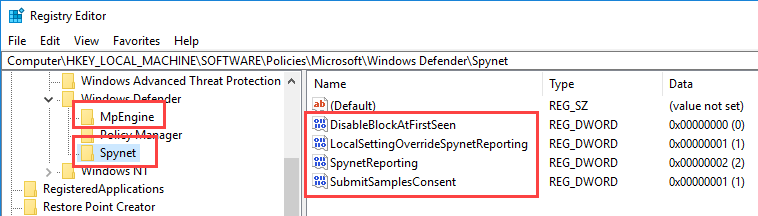
Once you are done adding, restart your machine. If you want to see what values and keys are added to Windows Registry, open Registry Editor and navigate to the following location:
HKEY_LOCAL_Machine\Software\Policies\Microsoft\Windows Defender
Here you can see the newly-created keys Spynet (MAPS) and MpEngine. By selecting the keys, you can see values associated with that key.
Comment below sharing your thoughts and experiences using the above method to harden Windows Defender.