VLC is a well-known media player of stored audio and video files, but did you know that you can do so much more with the program? For instance, you can record your screen or listen to podcasts. In this article we look at some of the most useful tips and tricks for VLC Media Player so that you can make the most out of using it.
Also read: How to Download Subtitles in VLC on Desktop and Mobile
Getting Started
Before we start showing you what VLC can do, we need to mention a few things. First, this article focuses on VLC Media Player for Windows, but it’s worth noting that the program is also available for Mac and Linux. Mobile versions for Android and iOS are offered as well, although it’s a watered down version which doesn’t always include the more advanced options VLC offers on desktop.
How to Convert to Different File Formats
You may want to convert your videos to other video formats for various reasons, including reducing the size of the videos while maintaining their quality or to use on select devices, such as TV or video players that only support certain formats. If you have VLC, you can do so very easily, by following these steps:
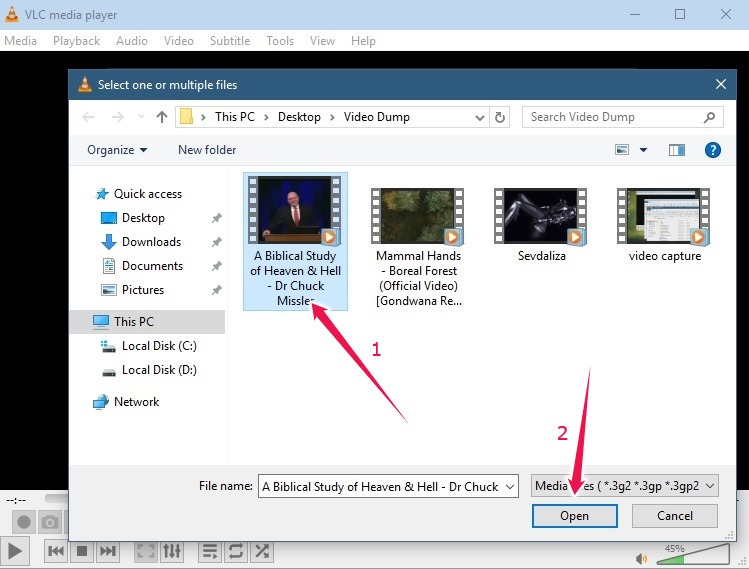
- In VLC, find the Media option in the menu bar above and click on “Convert / Save…” (or CTRL + R).
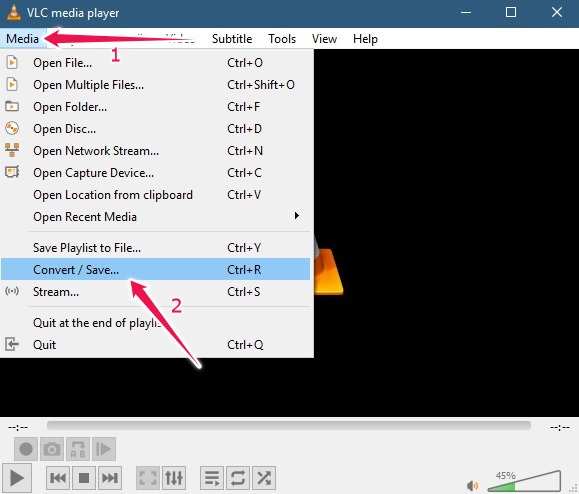
- Press the “Add” button to open the media you wish to convert.
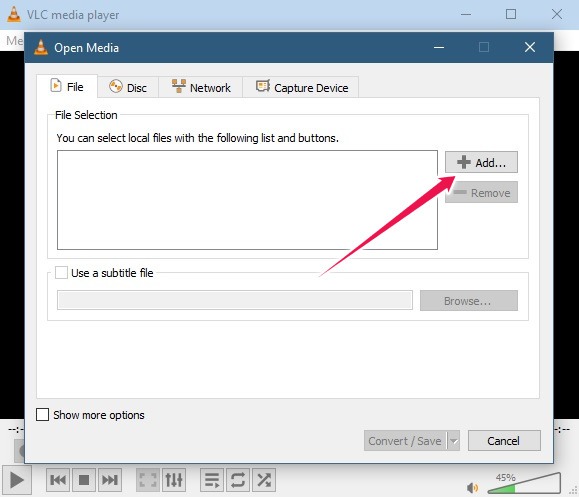
- Find the video in question and click on “Open.”
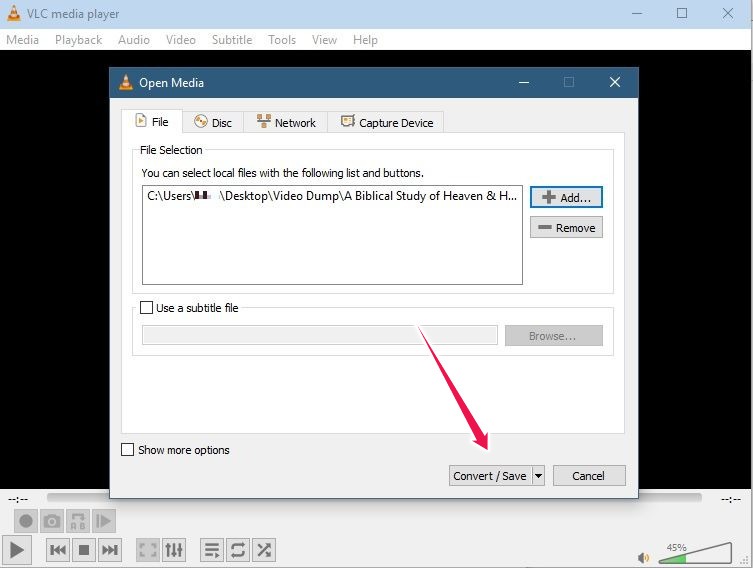
- Now press the “Convert/Save” button.
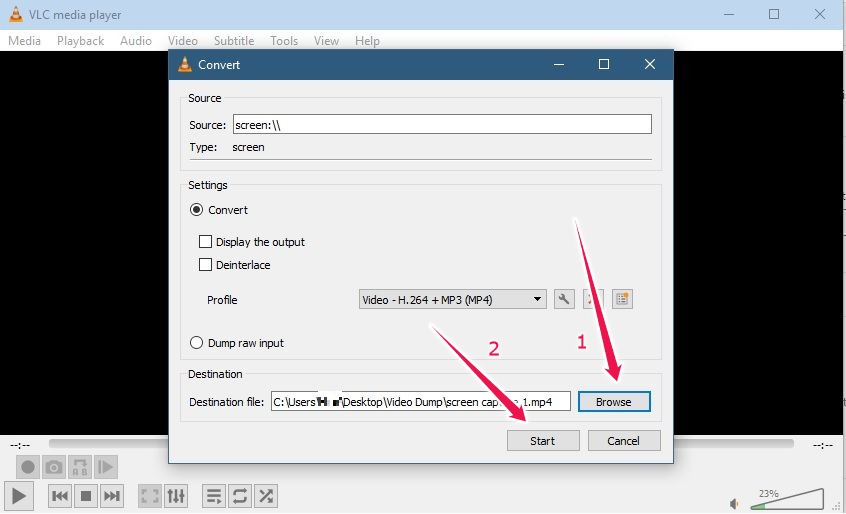
- When you’re presented with the conversion options, select the desired target file type in Profile: for example, H.264 with MP3 audio.
Note that you can create your own advanced custom profile by pressing on the “Create new profile” option.
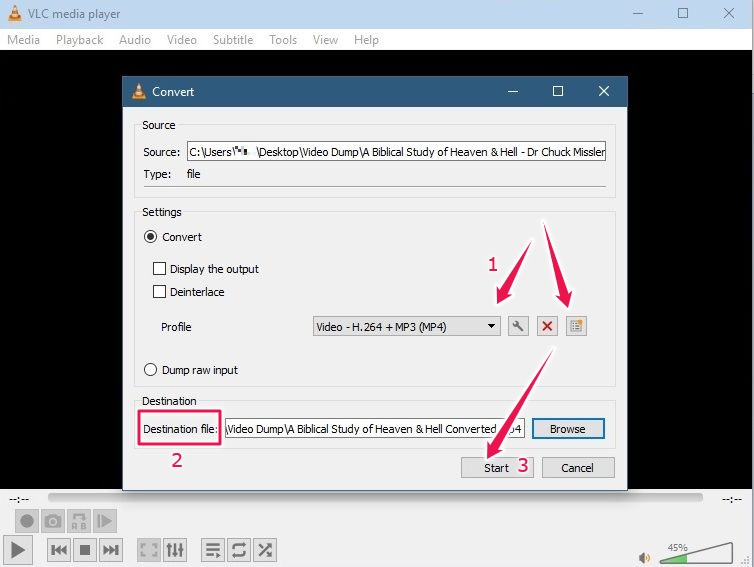
- Don’t forget to set the “Destination file,” then press “Start.”
VLC should start converting your file. Once the process is completed, the converted video will be waiting for you in the directory you’ve specified.
Note: If you’re converting from interlaced video formats, such as the 1080i and 720i formats displayed in televisions, make sure to check the “Deinterlace” option in Settings.
Also read: How to Rotate a Video in VLC (And Save It)
How to Stream from VLC to Chromecast
If you have a Chromecast device, an Android TV television, or a television that uses Android TV as its software, you can use VLC on your Windows-based PC to cast media to it. For this to work, you need to have VLC version 3.0.1 or higher, and both your Windows machine and Chromecast have to be connected to the same local network.
- Open the video you wish to cast to Chromecast with VLC.
- Click on the “Playback” option from the menu bar at the top and select the “Renderer” option.
- You’ll see the options for viewing listed on the next menu. The devices around your house to which you can cast to should automatically load. Just make sure they are powered on and connected to the same network as your computer. Select the device you wish to cast to.
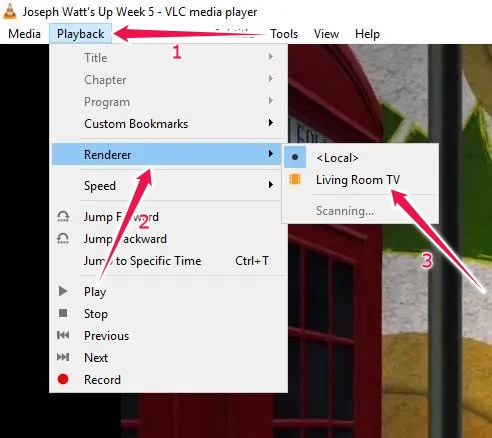
- If you’re using VLC to cast to your Chromecast for the first time, you’ll also need to permanently accept the safety certificate presented. Click on “View Certificate -> Accept permanently” to get the process started.
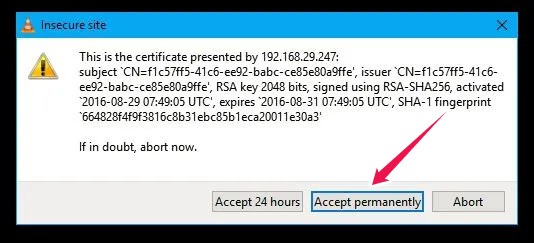
The next time you want to stream from your computer to Chromecast using VLC, you won’t have to worry about the certificate.
Also read: 9 of the Best Video Player Apps for Android
How to Easily Trim Videos with VLC
You can also use VLC to edit your videos. This way you eliminate the need of having a dedicated program for doing that on your PC.
- In VLC, got to “View,” then select “Advanced Controls.”
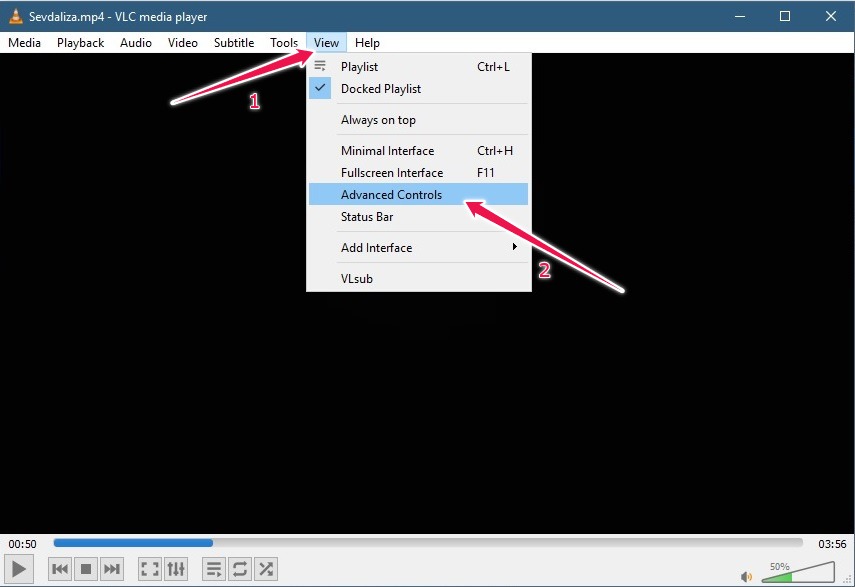
- A few new controls will be added at the bottom.
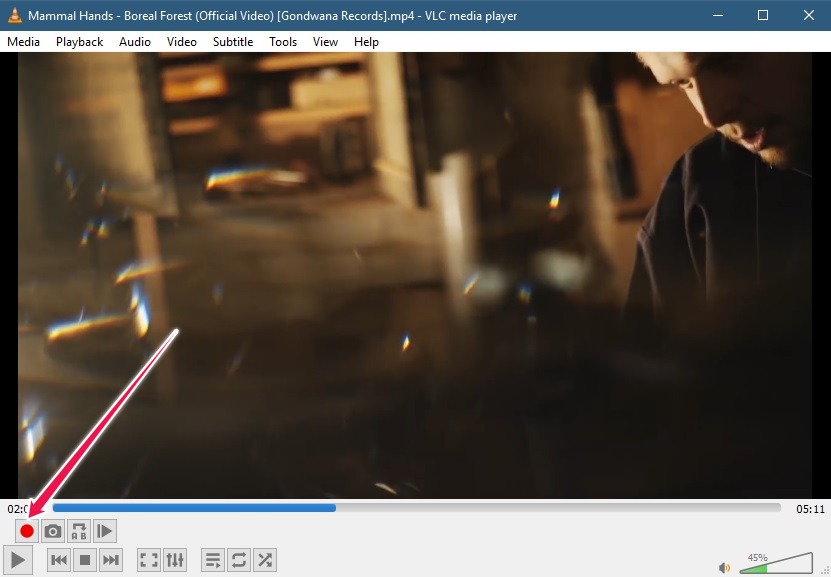
- To start trimming your video, go to the section that has to be cut out and press the Record button.
- Once the part you wish to remove plays out, click on the Record button once again to stop the process.
- If the section is small or you simply want to be accurate, you can opt for the “Frame by frame” option.
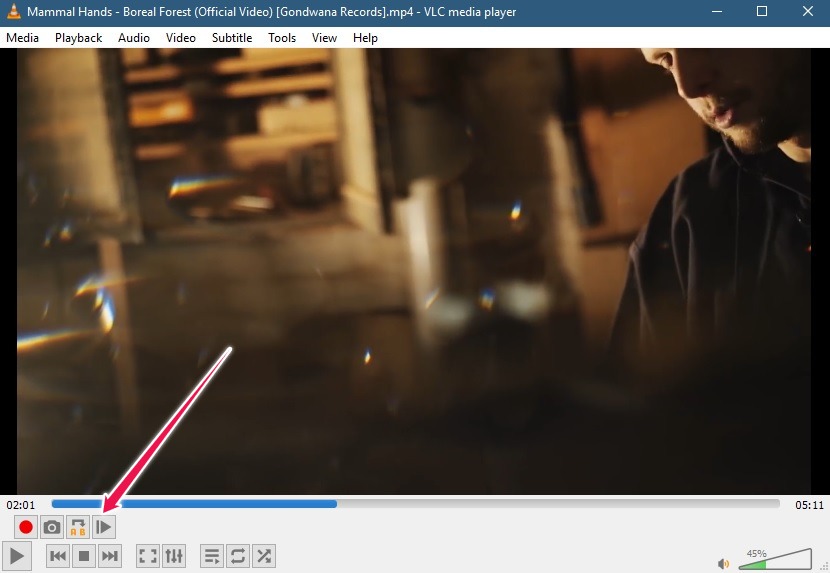
- The trimmed video will be saved automatically in the “My Videos” folder in Windows.
When it comes to editing videos, VLC has additional tricks up its sleeve. You can also alter a video’s coloring scheme by going to “Tools -> Adjustments and Effects.” In addition, you can remove a video’s echo and background noise in VLC or fiddle with brightness, contrast and gamma.
Check out this article for more video editing tricks with VLC.
Also read: 13 Apps to Watch Videos with Online Friends
How to Play/Download Streaming Videos with VLC
VLC also brings the ability to download videos from a variety of streaming platforms, including YouTube, Vimeo, DailyMotion and more. Follow these instructions to easily get your favorite videos to play in VLC, or even better, download them on your PC.
- Open VLC on your PC.
- Go to “Media -> Open Network Stream.”
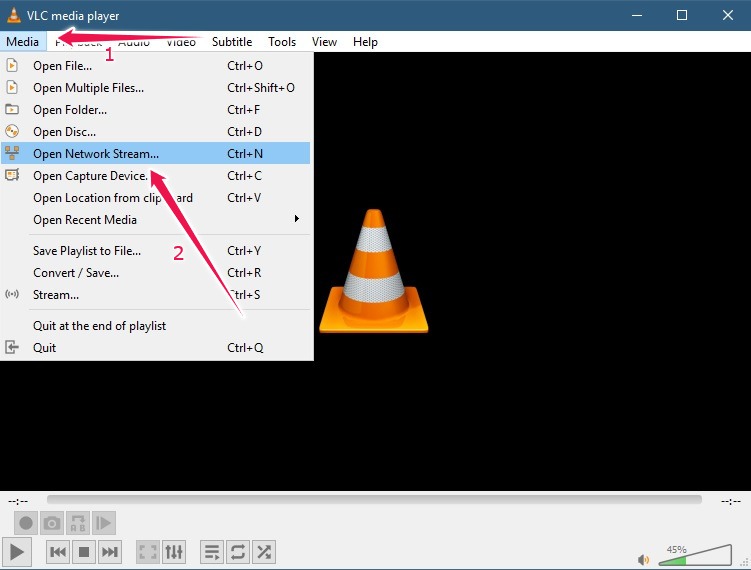
- Select the “Network” tab and enter the link in the Network Protocol URL section.
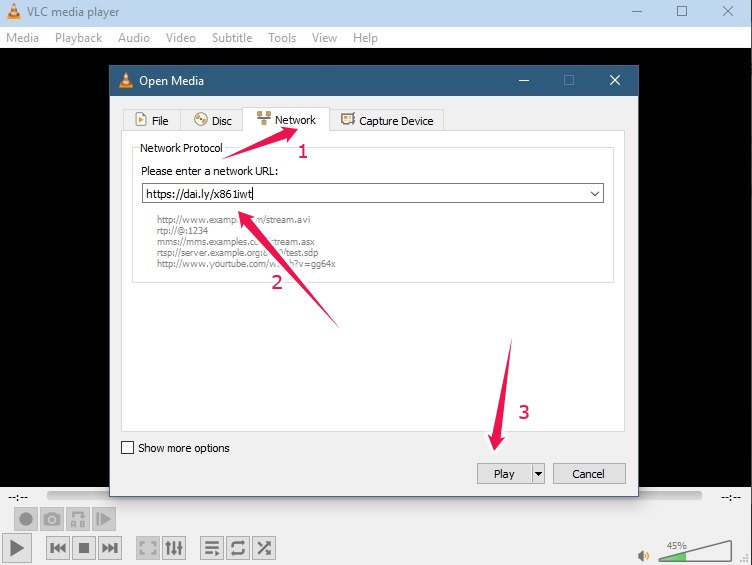
- Click “Play” and the video will start playing in VLC.
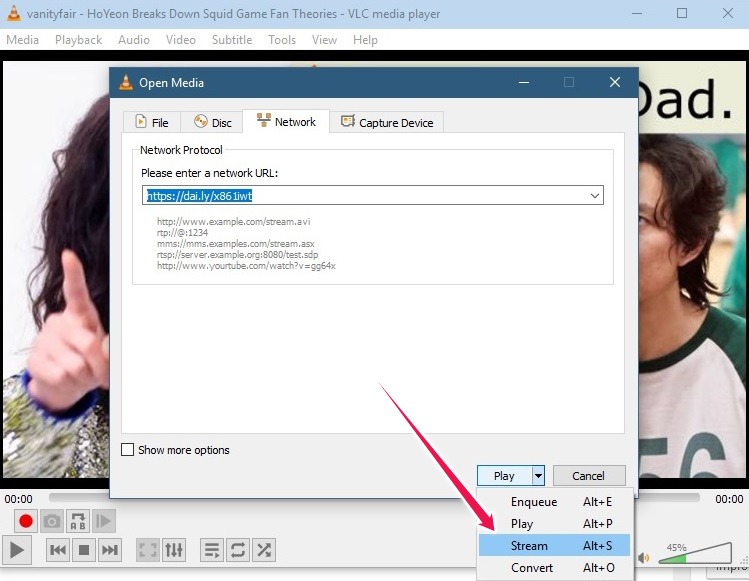
- If you wish to download the video, press on the downward arrow next to the Play button and select the option to stream.
- A new “Stream Output” window will open. Click the “Next” button.
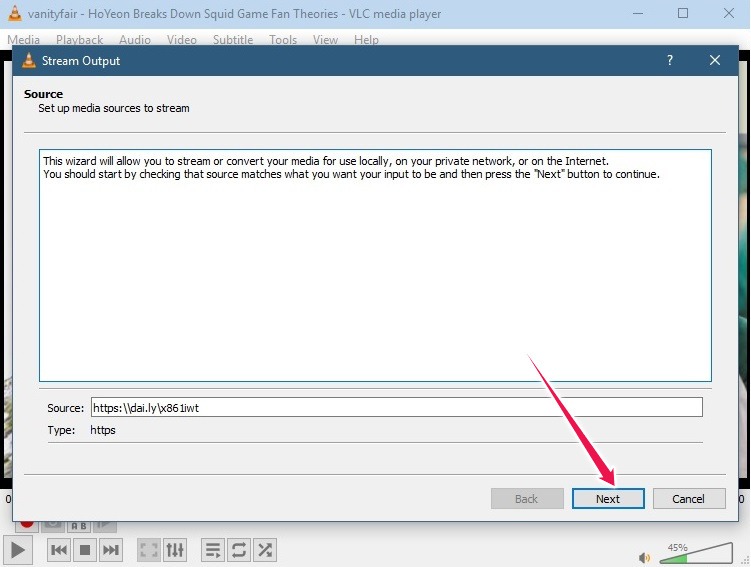
- In the “Destination Setup” window, click “Add” to select the downloaded video’s destination file.
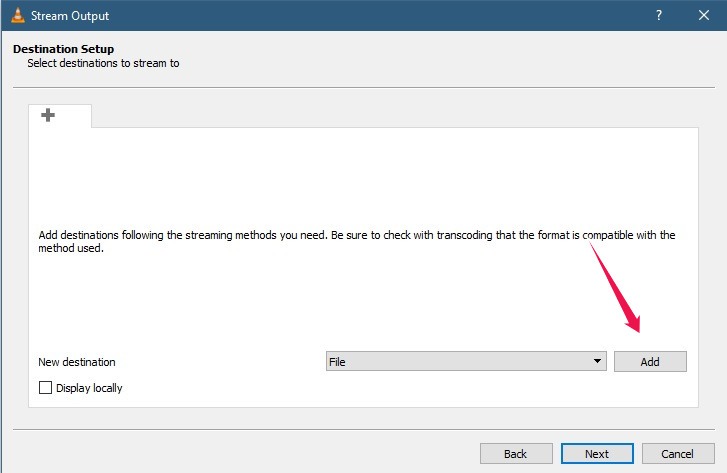
- Tap “Browse” and select the file you wish to save the video in, then press “Next.”
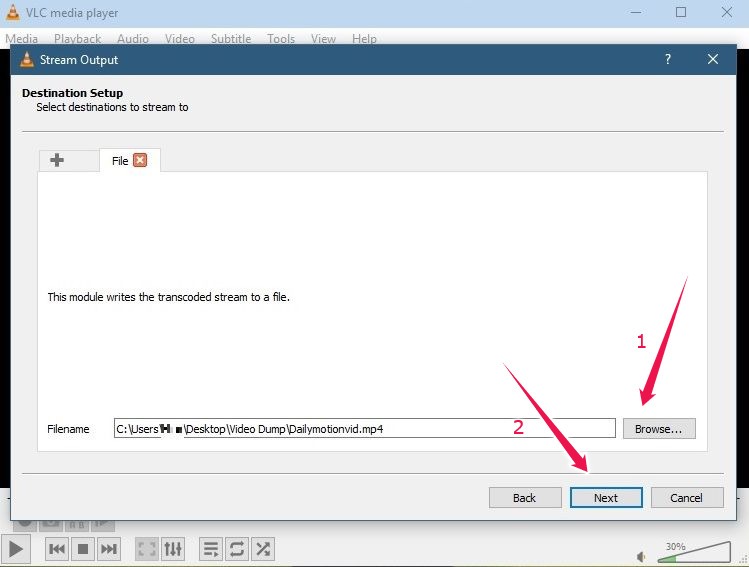
- In the “Transcoding Options” panel, check the “Activate Transcoding” option, select your preferred video format, then press “Next.”
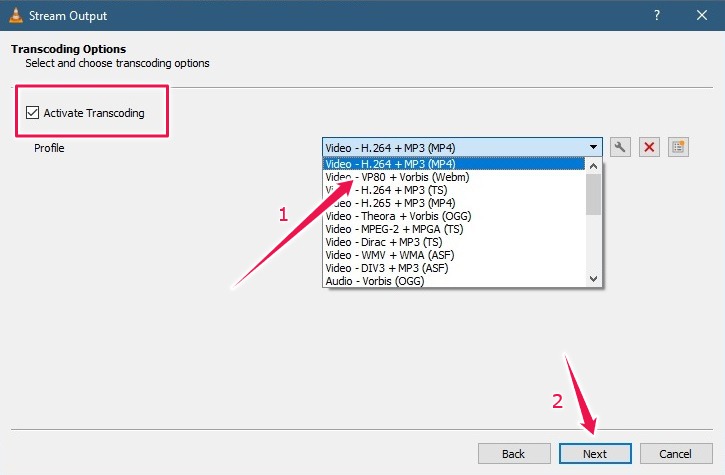
- Click “Stream” to start the downloading process.
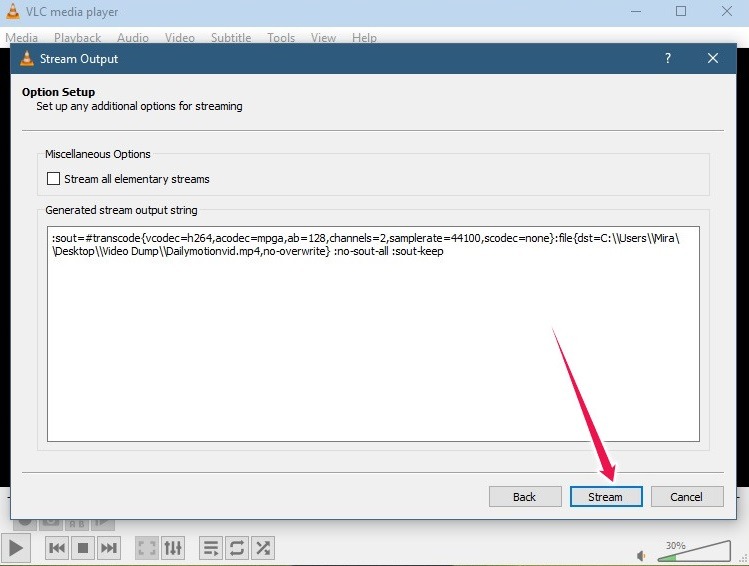
That’s it, your video should now appear in the specified location on your computer.
Also read: Which Roku Streaming Device Should I Buy?
How to Record Your Screen and Take Screenshots Using VLC
Another unique feature of VLC, which some users may not be aware of, is the ability to make screen recordings. Follow these instructions:
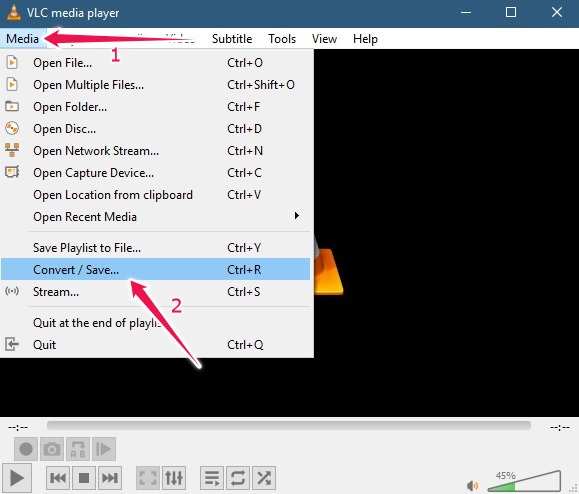
- In VLC, navigate to the “Media” tab, then select the “Convert/Save” option.
- Click on the “Capture Device” tab.
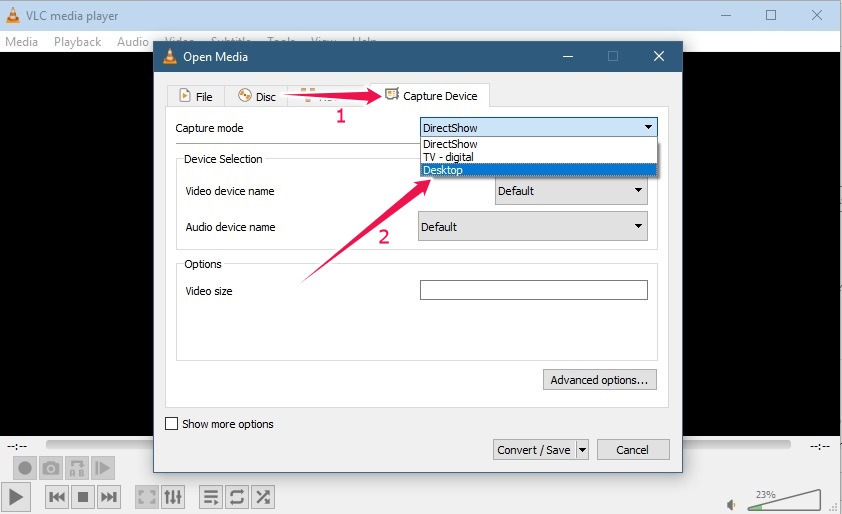
- Tap on the downward arrow next to “Capture mode” to bring up a list of options and select “Desktop.”
- Choose your desired frame rate. 10 f/s is a good choice for most videos featuring moving objects.
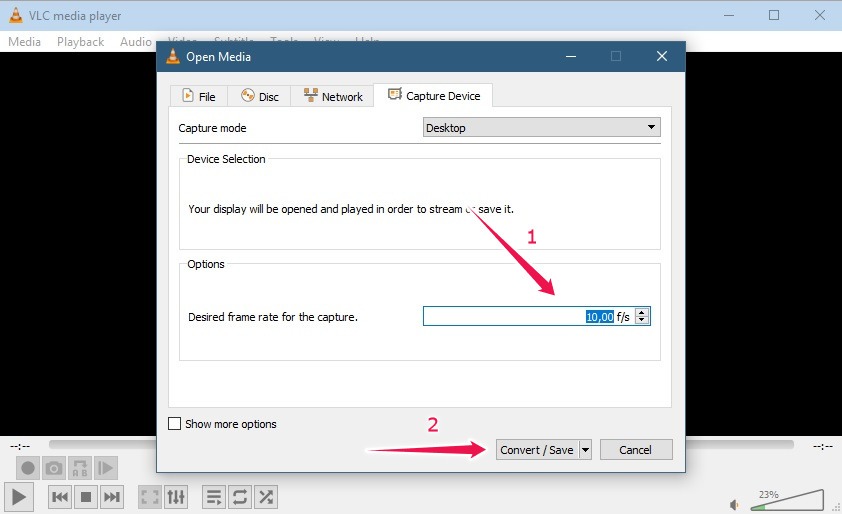
- Click on “Convert/Save” at the bottom.
- Select the directory where you want the resulting video to be saved. After choosing a name for it, press the “Save” button.
- Click “Start” to begin the process.
- Start doing whatever you want on your PC, and VLC will record it. Once you’re done, press the “Stop” button at the bottom in VLC to terminate the recording.
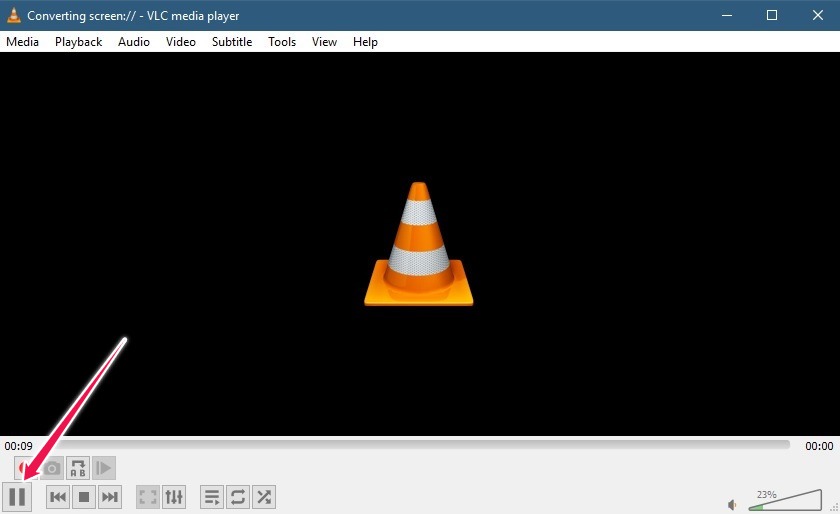
Check the folder where you instructed VLC to place the recording. You should find the video there.
If at some point you want to take a screenshot of content playing in VLC, use this combination from your keyboard: CTRL + S. You should find the resulting screenshots in the “My Photos” folder on your computer.
Also read: Which Amazon Fire TV Stick Should You Buy?
How to Subscribe to Podcasts and Listen to Internet Radio
VLC can keep podcast enthusiasts entertained by offering them the option to subscribe to podcasts and listen to radio from within the program. Follow the steps below.
- In VLC, go to “View” and select “Playlist” (CTRL + L).
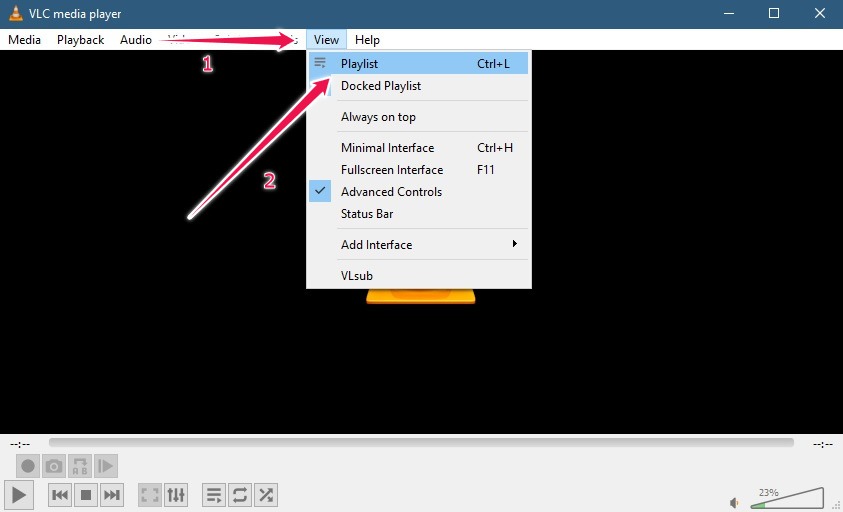
- On the left side of the display, scroll down until you reach the “Internet” section. Select “Podcasts.”
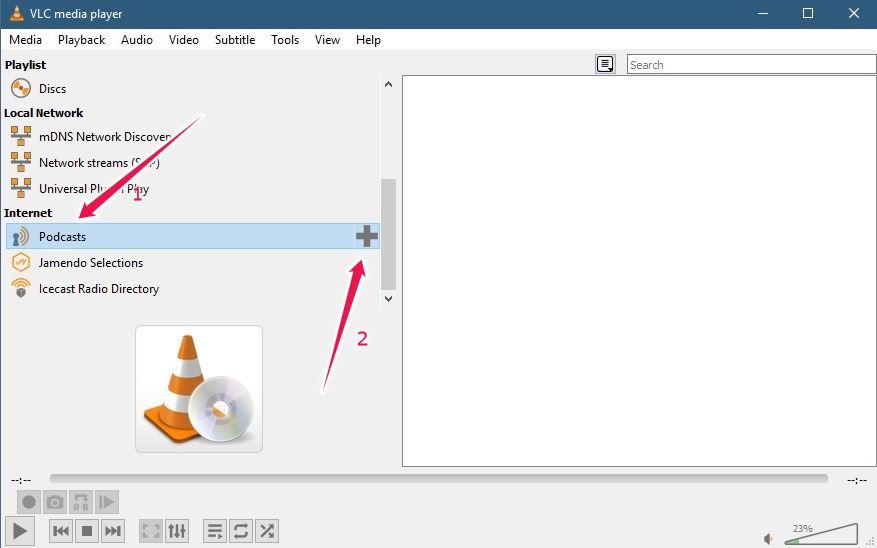
- Tap on the “+” button next to “Podcasts.”
- Paste the URL of the podcast you want to add in VLC.
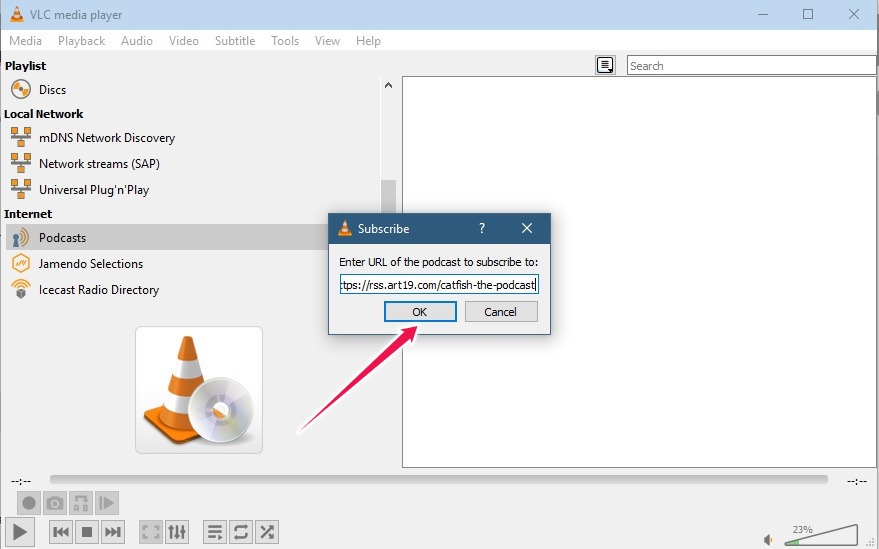
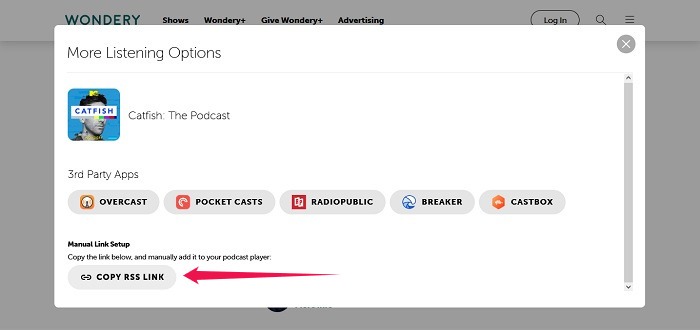
- You’ll need to paste the podcast’s RSS feed link in the “Subscribe” window. Find the feed by visiting a podcast’s official webpage rather than Spotify or similar apps.
For example, if you’re looking to listen to a Wondery podcast, you can find the RSS link right on the show’s page. These aren’t always available, mind you.
- Once you’ve added the RSS link, you should be able to see all the episodes that have been added to VLC.
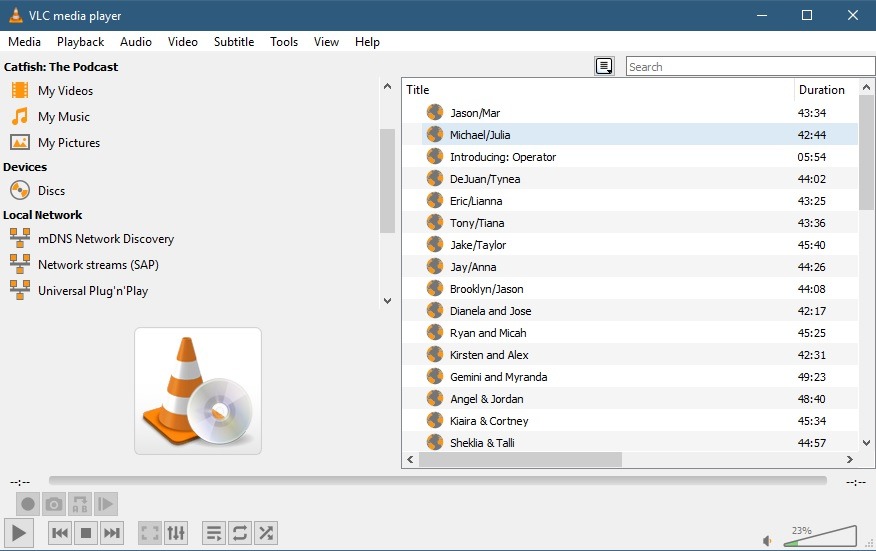
- Double-click on one, and VLC will start playing it.
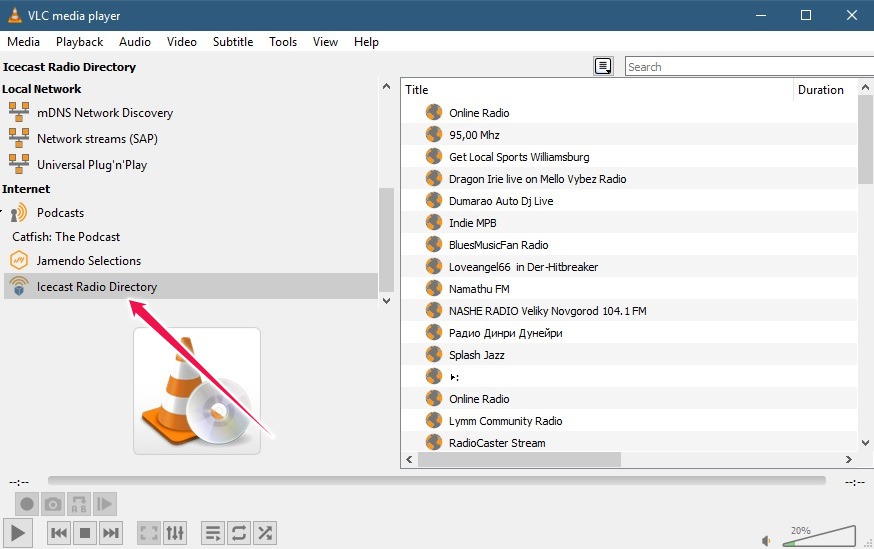
- Alternatively, to start listening to a radio station, look on the left side of the display once again, tap on “Icecast Radio Directory,” and select one of the options in the list.
- Double-click the station for it to start playing.
If you are looking to listen to TuneIn Radio in VLC, follow the guide here.
How to Run VLC via the Windows Command Line
More advanced users may want to try running VLC via the Windows (or Linux for that matter) command line. This way they can unlock special capabilities, such as playing VLC without an interface (or headless mode). If you’d like to give it a try yourself, continue reading below.
Making VLC Work from the Windows Command Prompt
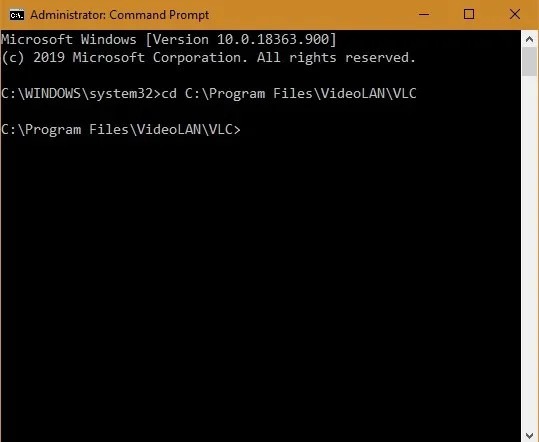
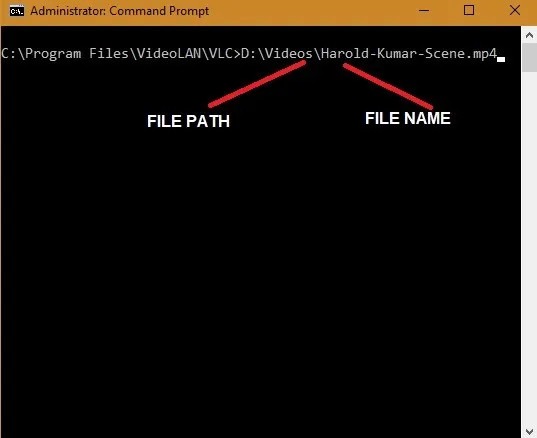
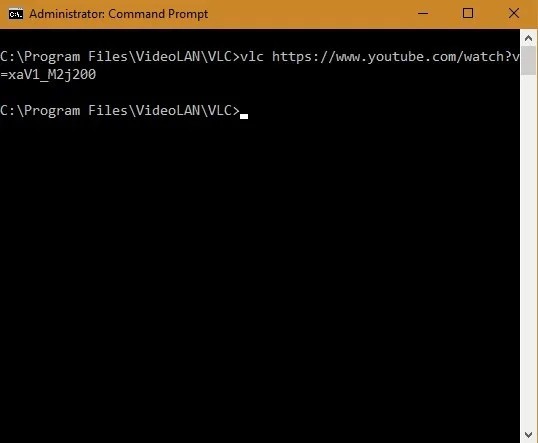
- Open the command prompt in Administrator mode from the Start menu to begin the process.
- To make VLC work from the Windows command prompt, you need to know its exact location on your Windows computer. You will usually find the path in “Program Files,” and you can copy it by right-clicking on “Properties.”
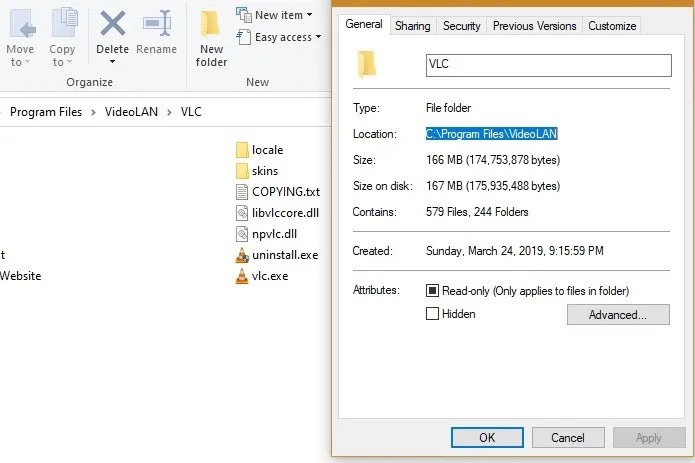
- Enter the following code to change the directory to your VLC folder path. Make sure you have enabled copy-paste in the Command prompt, otherwise you’ll need to type the whole folder path.
cd C:\Program Files\VideoLAN\VLC
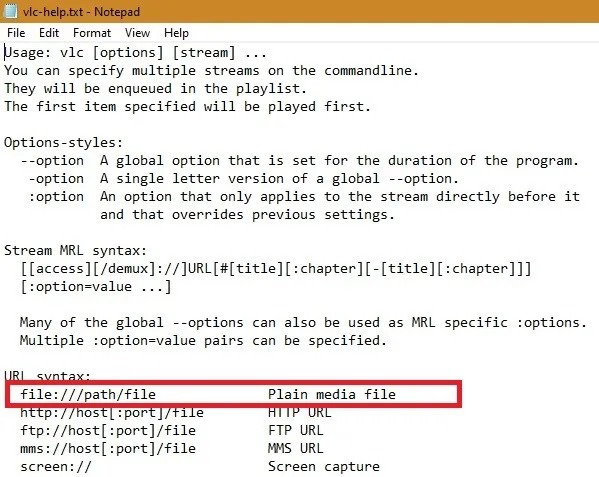
- Enter the following code to fetch a complete list of VLC commands applicable for Windows users.
vlc --help
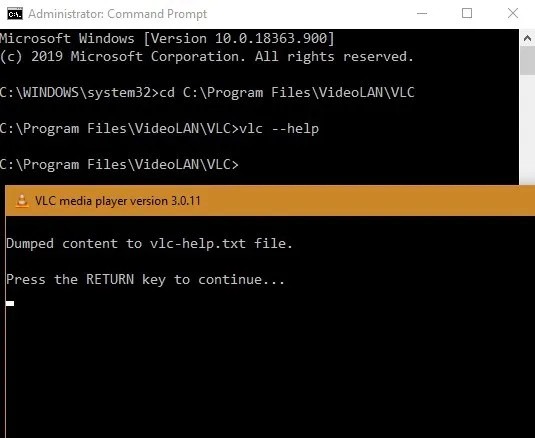
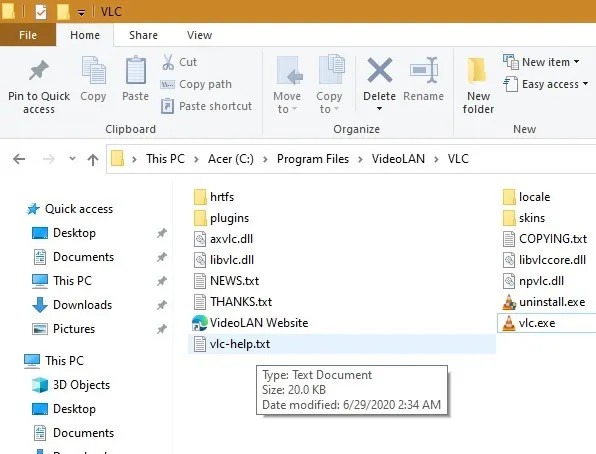
- The above command will save a notepad file, “vlc-help,” on the VLC folder.
How to Play VLC in Headless Mode
When you open the notepad file, you will be able to see a very long list of useful VLC commands. It ranges from video playback options to screen recording, saving video wallpapers, managing hot keys, adding plug-ins, bookmarking, and much more.
The very first option to stream a file on Windows 10 based on its file path in the command line is chosen here. This will play your VLC video in headless mode without the GUI. The syntax is as shown.
file://path/file
- Go to the target video you would like to stream in headless mode. Copy its path with a right-click on “Properties.”
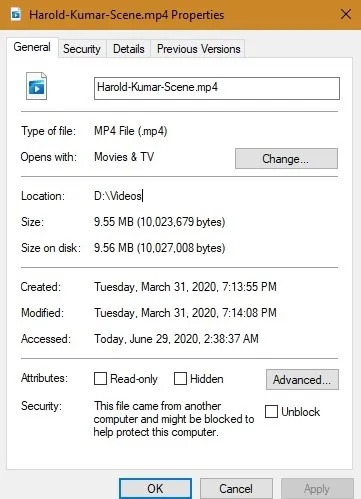
- Copy-paste the entire path as per the above syntax noted in the VLC help menu and hit “Enter.” You may use “CLS” first to clear the entire screen.
- The video will be automatically played in headless mode without the VLC widget occupying the extra space on your screen.
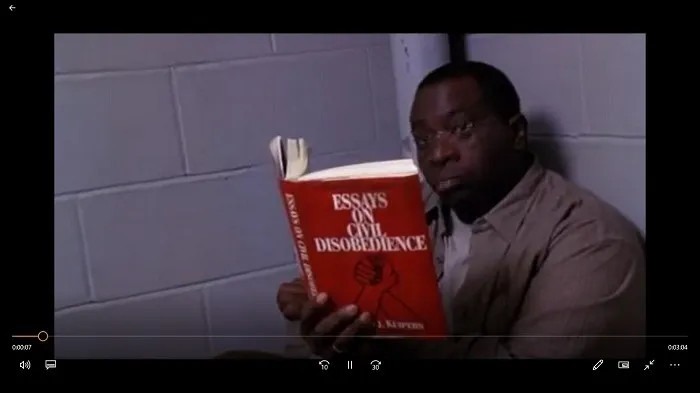
- Going headless from the command line is the best way to play your VLC videos in full-screen mode without any interfering text or graphics.
Playing YouTube Videos on VLC in Full-Screen Mode
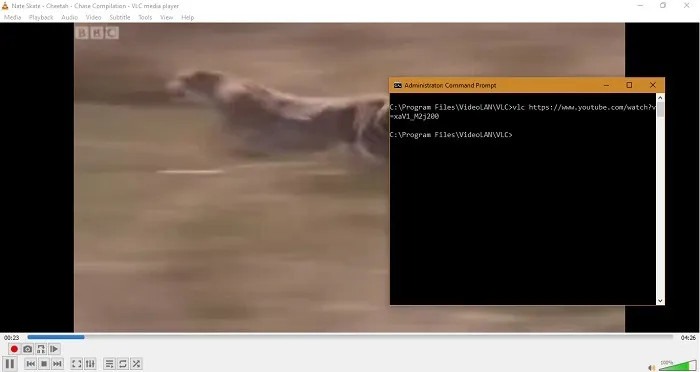
You can further utilize the headless capability to play YouTube (or any other online) videos directly from VLC.
- For this, go to the online video and copy its URL, then paste it as shown below.
vlc https://online-video-url
- The YouTube video will now start playing on your VLC app, but you don’t want the widget to interfere with your viewing experience, so you can use another command mentioned in an earlier VLC help notepad file to remove this distraction.
- Use the following code to convert any VLC YouTube video into fullscreen mode.
vlc https://online-video-url --fullscreen
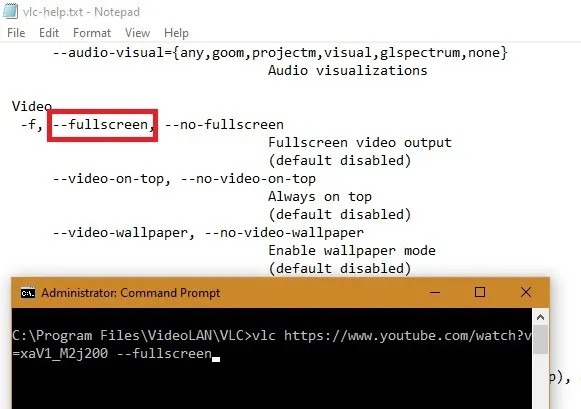
The YouTube video will now be viewable on VLC without ads, interruptions, or the annoying VLC widget.

The headless mode in VLC can be turned on and off at will. You can also hide the mouse cursor and fullscreen controller.
Frequently Asked Questions
1. I can’t play some podcasts even after successfully using the RSS link to load them in VLC. What can I do?
Try removing (-) the podcast in question and then adding it again or updating your VLC to the latest version to see if that fixes the issue.
2. How can I become more efficient when using VLC?
Learn all about using VLC shortcuts in this cheatsheet that details the best keyboard shortcuts you should know.
3. Are these features available for mobile devices?
Most of the features described in this article won’t be available in the mobile apps. You can, however, play a streaming video in the app.