The process of generating SSL/TLS certificates is a common task for many Linux system administrators. Luckily, even if you are not an administrator, it is easy to do so using OpenSSL, an open-source tool that is installed by default on many Linux distributions. Here we explain what OpenSSL is, how to install it, and most importantly, how to use it to generate SSL and TLS certificates on your system.
Also read: How to Set Up Leafnode as an Offline USENET Server
What Is OpenSSL?
OpenSSL is a library developed by the OpenSSL Project to provide open-source SSL and TLS implementations for the encryption of network traffic. It is readily available for a variety of Unix-based distributions and can be used to generate certificates, RSA private keys, and perform general cryptography-related tasks.
Limitation of Self-Signed SSL Certificate
When you use OpenSSL to generate a SSL certificate, it is considered “self-signed.” It means that the SSL certificate is signed with its own private key and not from a Certificate Authority (CA).
As such, the SSL certificate cannot be “trusted” and should not be used for any public facing site. If used, the users will likely see warnings from their browsers about the certificate.
A self-signed certificate is useful for local development or any apps running in the background that don’t face the Internet.
Alternatively, you can use LetsEncrypt or obtain a certificate verified by a trusted authority, such as Comodo CA.
Installation
Most Linux distributions already have a version of OpenSSL built in by default. If not, you can easily install it.
You can install it on Ubuntu and Debian by using the apt command:
sudo apt install openssl
On CentOS (or its alternative), you can install it by using the yum command:
sudo yum install openssl
You can also easily download it from its website as a “.tar.gz” file.
Also read: How to Use cURL for Command Line Data Transfer and More
Basic Usage
Now that you have OpenSSL installed, we can have a look at some of the basic functions the program provides.
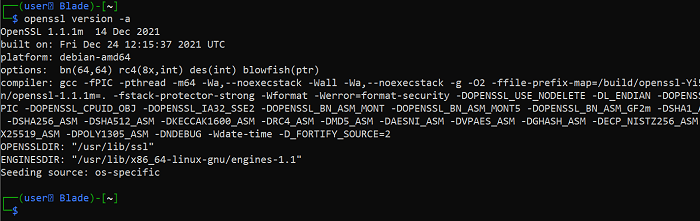
You can start by viewing the version and other relevant information about your OpenSSL installation:
openssl version -a
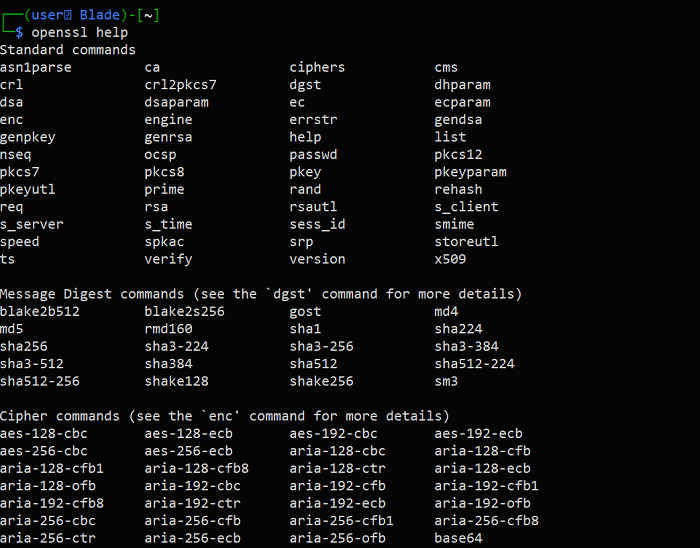
You can check out the manual provided:
openssl help
Also read: 8 Useful and Interesting Bash Prompts
Generating a Certificate Using a Configuration File
Generating a certificate using OpenSSL is possible in many ways. One of them is by using a configuration file which will specify details about the organization.
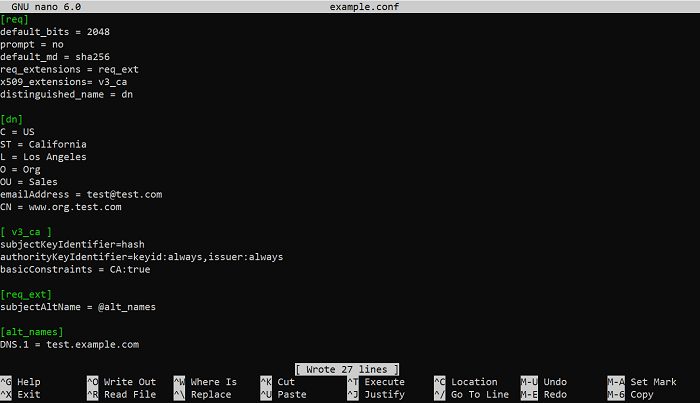
To start, you can create a configuration file called “config.conf” and edit it using Nano:
sudo nano example.conf
Here is an example of the content of the configuration file:
[req] default_bits = 2048 prompt = no default_md = sha256 req_extensions = req_ext x509_extensions= v3_ca distinguished_name = dn [dn] C = US ST = California L = Los Angeles O = Org OU = Sales emailAddress = [email protected] CN = www.org.test.com [ v3_ca ] subjectKeyIdentifier=hash authorityKeyIdentifier=keyid:always,issuer:always basicConstraints = CA:true [req_ext] subjectAltName = @alt_names [alt_names] DNS.1 = test.example.com
You can just copy and paste this into the file and make the necessary changes to reflect your organization’s information.
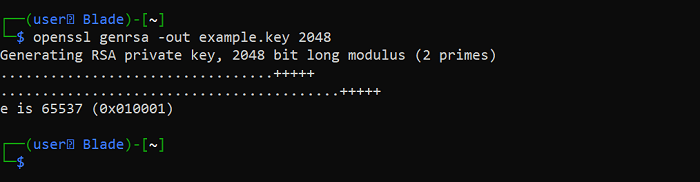
Next, you have to generate an RSA private key, which will then be used to generate a root certificate -:
openssl genrsa -out example.key 2048
The -out flag is used in this case to specify the name of the key that will be generated. A key size of 2048 bits is also specified, which is the default for RSA keys.
Also read: How to Use the dd Command in Linux
You will also have to generate a Certificate Signing Request (CSR):
openssl req -new -key example.key -out example.csr -config example.conf
In this case, the -key flag is used to specify the RSA key, the -out flag specifies the name of the CSR file and the -config flag is used to specify the name of the config file.
After this, you can generate a root certificate, which is used to generate our final certificate:
openssl req -x509 -sha256 -nodes -new -key example.key -out example.crt -config example.conf
In the process of generating this root certificate, the -sha256 flag is used to specify SHA256 as the message digest.
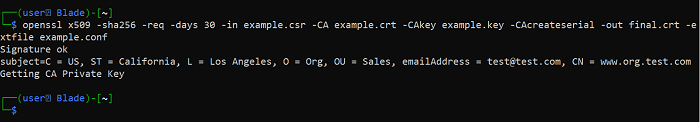
Now, as for the final step, we can finally type the following to generate our certificate:
openssl x509 -sha256 -CAcreateserial -req -days 30 -in example.csr -extfile example.conf -CA example.crt -CAkey example.key -out final.crt
The -CA flag specifies the root certificate, the -CAkey flag specifies the private key and -extfile specifies the name of the configuration file. The “final.crt” file will be the SSL certificate you want.
Also read: How to Set Up an SFTP Server on Linux
Generating a Certificate without a Configuration File
Alternatively, you can also generate a certificate using OpenSSL without a configuration file.
You can start by generating an RSA private key:
openssl genrsa -out example.key 2048
Next, you will have to generate a CSR:
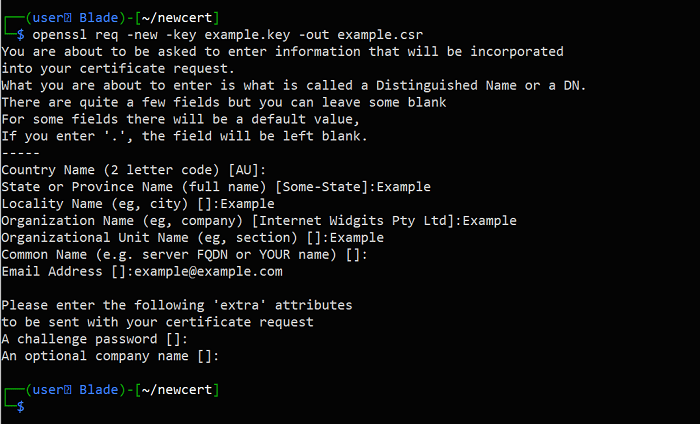
openssl req -new -key example.key -out example.csr
When generating a CSR, you will be prompted to answer questions about your organization.
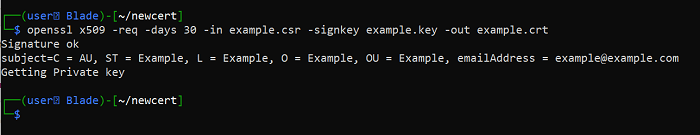
Finally, we can generate the certificate itself:
openssl x509 -req -days 30 -in example.csr -signkey example.key -out example.crt
Also read: How to Get a Free SSL Certificate for Your WordPress Website
Verification of Keys and Certificates
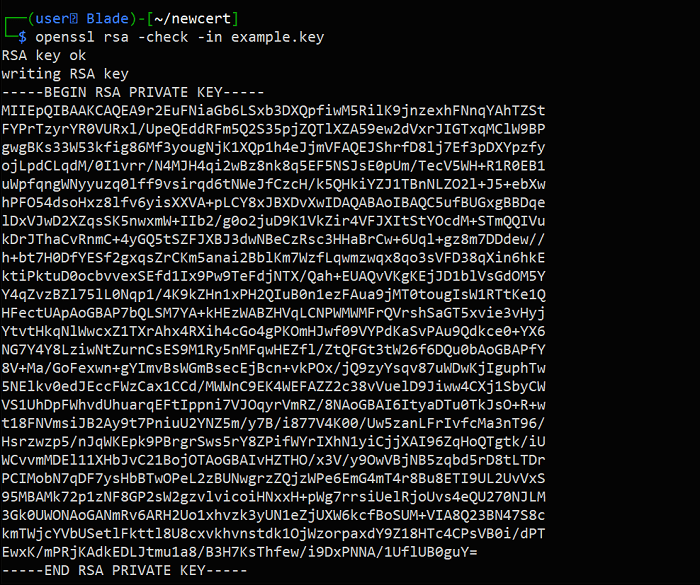
Keys and certificates are easily checked and verified using OpenSSL, with the -check flag:
openssl rsa -check -in example.key
You can check certificate signing requests:
openssl req -text -noout -in example.csr
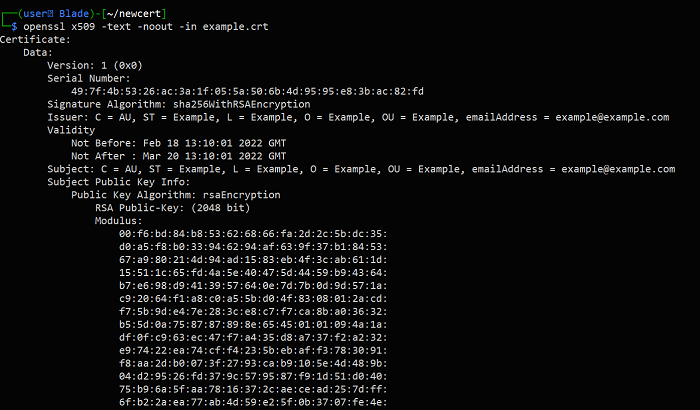
and certificates as well:
openssl x509 -text -noout -in example.crt
Frequently Asked Questions
1. Do I still have to worry about Heartbleed?
Heartbleed (CVE-2014-0160) is an old vulnerability found in OpenSSL in 2014. TLS-servers and clients running OpenSSL both were affected. A patch was quickly released a few days after its discovery, and this vulnerability isn’t something to worry about in 2022 as long as you are running a modern and up-to-date version of OpenSSL.
If you are using OpenSSL on Debian and Ubuntu-based systems, you can always update it by running the following commands:
sudo apt update && sudo apt upgrade openssl
2. How long do SSL certificates last before they expire?
This depends on the value you choose when generating the certificate. This can be specified by using the -days flag when generating a certificate.
Image credit: Sls written on wooden cube block by 123RF








