If you ever managed a Linux server from Windows, you probably used PuTTY or at least heard about it. It’s an excellent utility and has been a favorite SSH client for years. However, in 2019 Windows 10 started to include an OpenSSH client out of the box, so PuTTY isn’t necessary anymore.
Why You Should Avoid Password-Based Logins
The OpenSSH daemon running on servers was battle-hardened, through years of use and abuse and software patches. It’s pretty rare for a server to be hacked because of a bug in the SSH daemon. However, many break-ins are facilitated by administrators who use weak passwords. Even passwords that seem to be complex, with letters and numbers, are often sensitive to brute-force attacks.
Enter SSH keys. These cannot be brute-forced – they are simply too complex. If you can, disable password logins in your “sshd_config” file (on the server) and use keys instead. In case you travel and can’t carry your laptop with you, just keep your private key on a USB stick and attach it to your physical keychain. Your server will be much safer this way.
Generate Public/Private SSH Key Pair
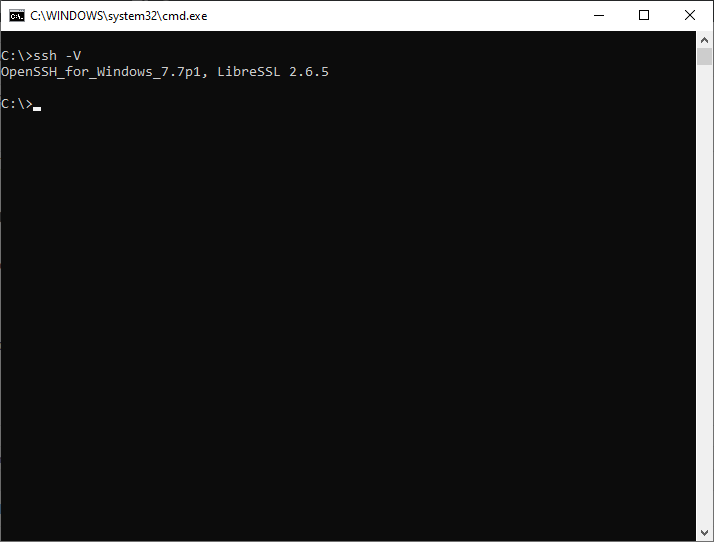
Open Command Prompt from the Start Menu and type:
ssh -V
You should get a result similar to the following image,
If you get a “command not recognized” error, just follow the steps here to install OpenSSH. This will only happen on old versions of Windows 10 that haven’t been upgraded in a very long time.
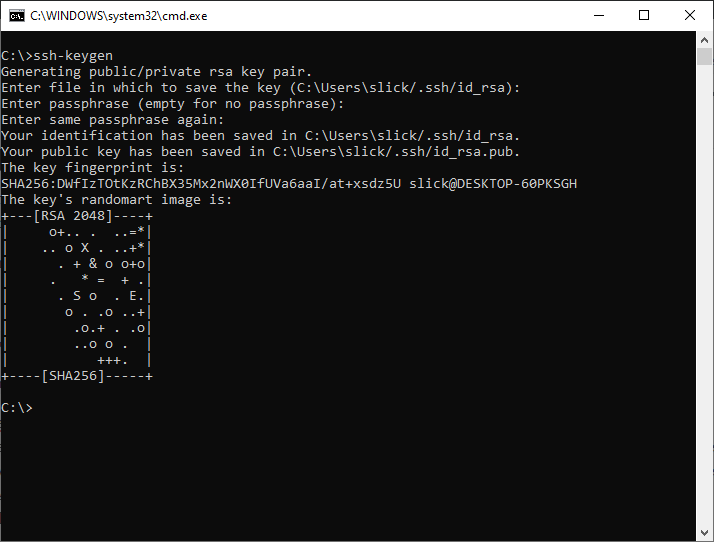
To generate the public/private key pair, enter this in the Command Prompt:
ssh-keygen
At the first prompt, “Enter file in which to save the key,” press Enter to save it in the default location.
At the second prompt, “Enter passphrase (empty for no passphrase),” you have two options:
- Press Enter to create unencrypted key. If you’re the only one that uses the computer, this is safe.
- Type a password. This will encrypt your key. It’s a good idea to do this if you share your computer with someone else. If you intend to carry the key on a USB stick, definitely use a password here. If you use a strong passphrase and someone steals the key from your USB device, they won’t be able to use it without the password.
When you’re done, you will see something similar to the below image.
Open Public Key
As the name suggests, the private key is meant for you and only you. Never copy/save this on a server!
The public key, however, is meant to be saved on the servers you intend to access, in the “~/.ssh/authorized_keys” file (or rather, pasted/added to this file). To open this key, to copy, and then paste, wherever necessary, enter the following in Command Prompt.
notepad %userprofile%\.ssh\id_rsa.pub
Most of the computer cloud (VPS) providers today give you an easy way to add your public key(s) through their web interface control panels. Once you start a server with this associated public key, you will be able to log in with your private key. Since the private key is in its default location, the command to log in to a server/VPS is as simple as:
ssh [email protected]
Conclusion
As you can see, it’s very easy to generate SSH keys on Windows these days. Basically, the ssh-keygen command does all the work. If you find it difficult to understand how to add the public key to the server, look up your provider’s documentation. They always have a page that describes, in detail, how to do this.








