If you are using SSH frequently to connect to a remote host, one way to secure your SSH server is to use a public/private SSH key so that no password is transmitted over the network. It can prevent against brute force attack too.
In Linux, creating a public/private SSH key is easy.
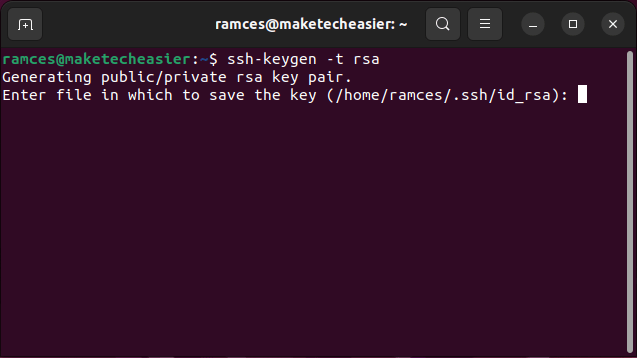
- Open a terminal. Type:
ssh-keygen -t rsa
Alternatively, you can also use the DSA (Digital Signing Algorithm) technology to create the public/private key.
ssh-keygen -t dsa
Note: there has been much debate about the security of DSA and RSA. In my opinion, unless you are very particular and love to delve into the technical detail between the two technologies, it doesn’t matter which of the two you choose. Both will work fine.
- In the next screen, you should see a prompt that asks for the location to save the key. The default location is the .ssh folder in your Home directory. Press Enter to accept the default setting.
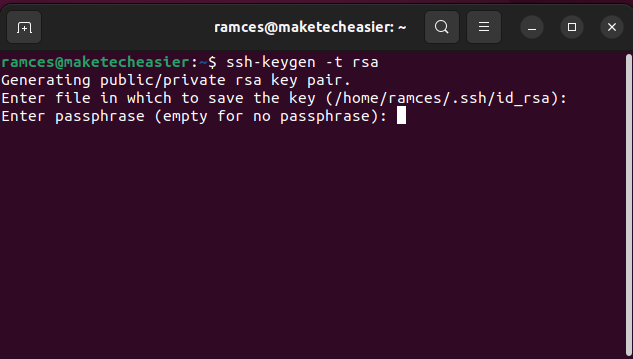
- You will be prompted to enter a passphrase – NOT the passphrase to connect to your remote host, but the passphrase to unlock the private key so that no one can access your remote server even if they got ahold of your private key. The passphrase is optional. To leave it blank, just press Enter.
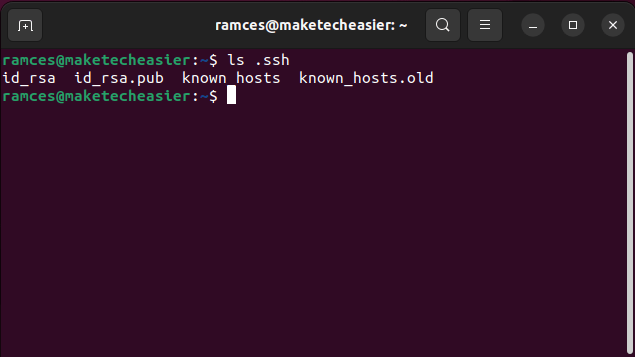
- Your public and private SSH key should now be generated. Open the file manager and navigate to the .ssh directory. You should see two files: id_rsa and id_rsa.pub.
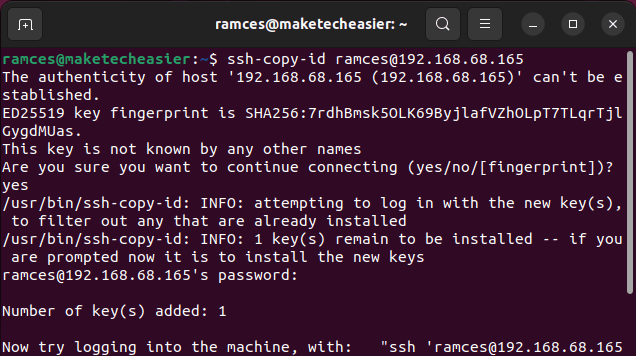
- Upload your new SSH public key to your remote host by running the following command:
ssh-copy-id username@remote-host-ip-address
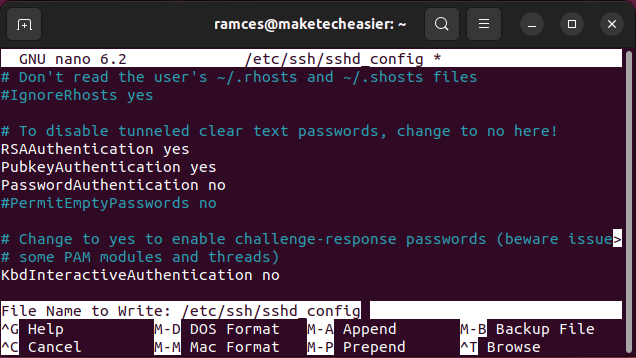
- Log in to your remote host and edit your SSH config file:
ssh username@remote-host-ip-address sudo nano /etc/ssh/sshd_config
Scroll down the config file and make sure the following attributes are set correctly:
RSAAuthentication yes PubkeyAuthentication yes PasswordAuthentication no
Press Ctrl + O to write and save the file, then Ctrl + X to close the file.
- Restart the SSH server in the remote host:
sudo systemctl restart ssh
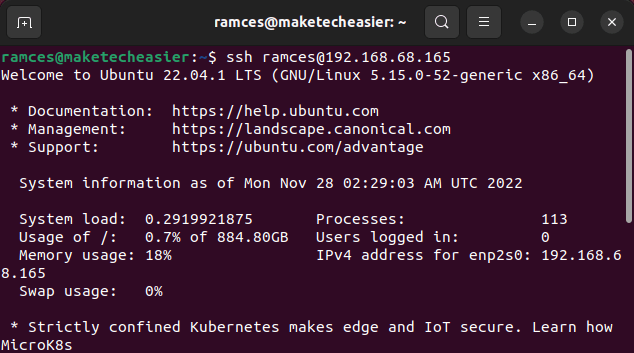
That’s it. You can now connect to your remote host with the following command:
ssh username@remote-host-ip-address
Frequently Asked Questions
I copied my SSH key to my remote server and am getting a “Permission Denied” error.
This problem is most likely due to an issue with your remote host’s “.ssh” folder. By default, the SSH daemon rejects any incoming connections if its configuration folder and “authorized_keys” file does not have the right permission bits.
To change the file and folder permissions, access a local console for your remote machine, thrn go to your “/home” directory and run: chmod 700 /home/$USER/.ssh && chmod 600 /home/$USER/.ssh/authorized_keys. Lastly, restart the daemon to apply your new settings: sudo systemctl restart ssh.
Is it possible to create multiple SSH keys for the same remote server?
Yes! However, you need to make sure that each SSH key in your machine has a unique file name by running: ssh-keygen -f /home/$USER/.ssh/filename.
Aside from that, make sure that you specify the key you want to use to log in to your remote host by running: ssh -i /home/$USER/.ssh/filename [email protected].
Is it possible to import a new SSH key to a remote host with an old working key?
Yes! First, import your new key to the SSH authentication agent: ssh-add. Next, log in to your old machine and import its key to the same authentication agent: ssh -A old.machine.ip.address && ssh-add -c.
Lastly, leave the old machine by pressing Ctrl + D and connect to your remote host with both your new and old keys.
Image credit: Unsplash. All alterations and screenshots by Ramces Red.