Do you have files or messages you want to keep hidden? To keep them safe, you should be using GPG encryption keys. If you’re running Linux, encrypting your files using GPG is easy as long as you have the GnuPG installed.
Here’s how you can generate GPG keys in Linux with just a few simple terminal commands.
Installing GnuPG
You’ll need to start by installing GnuPG first. For Debian or Ubuntu-based distros, open a terminal and run:
sudo apt install gnupg
Linux distributions using DNF or YUM (like Fedora) should run the following:
yum install gnupg
or
dnf install gnupg
If you’re running Arch, install GnuPG with the following command:
pacman -S screen
You can also download the source code and compile it yourself if you’d prefer.
Generating Your GPG Key Pair
Once GnuPG is installed, you’ll need to generate your own GPG key pair, consisting of a private and public key. The private key is your master key. It allows you to decrypt/encrypt your files and create signatures which are signed with your private key.
The public key, which you share, can be used to verify that the encrypted file actually comes from you and was created using your key. It can also be used by others to encrypt files for you to decrypt.
To generate your key pair, open your terminal, and type the following:
gpg --gen-key
This will begin the key pair generation. You’ll be asked to enter your full name and email address. Do so and hit Enter.
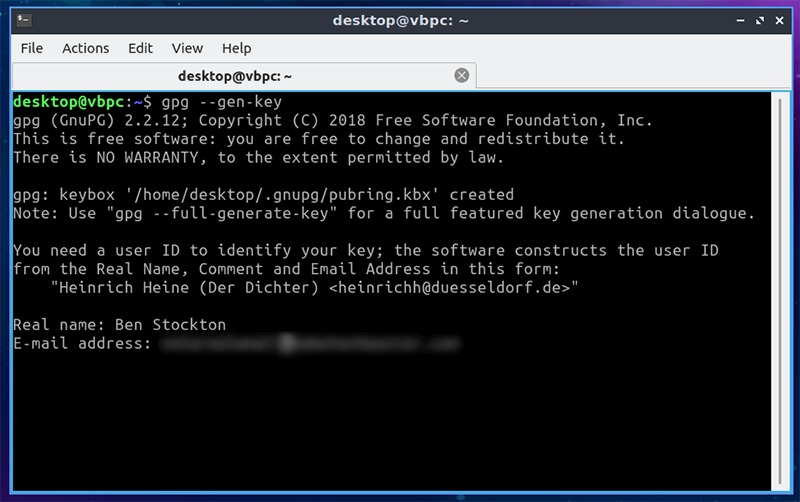
You’ll be asked to either confirm your choices, edit them or quit. Select your option and hit Enter.
Before the key is generated, you’ll need to provide a secure passphrase. Type it in and press enter.
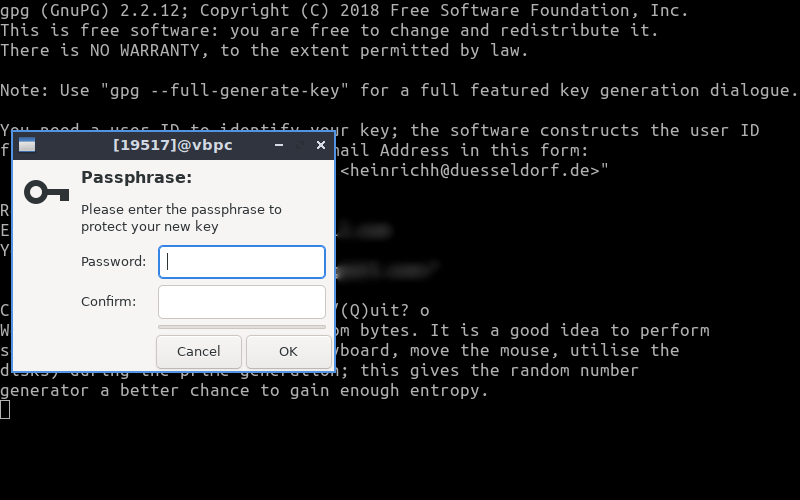
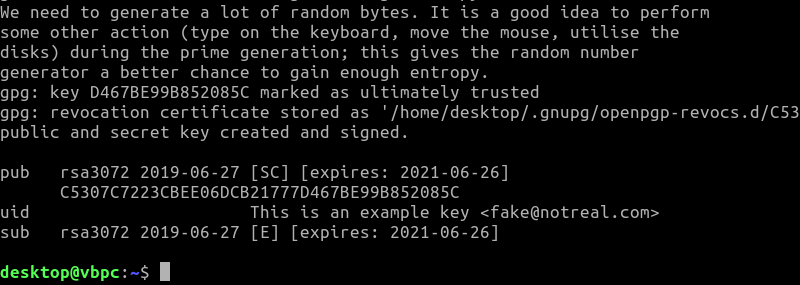
It may take some time for your key to be generated. Once it’s done, you’ll see confirmation.
Revoking Keys
If, for some reason, you need to revoke your key, run the following command:
gpg --output revoke.asc --gen-revoke uid
uid will be your key user id. For instance, you could use your email address here. This will generate a revocation certificate – you’ll need your passphrase to do this. You’ll need to give a reason, selecting from a numbered list ranging from zero to three.
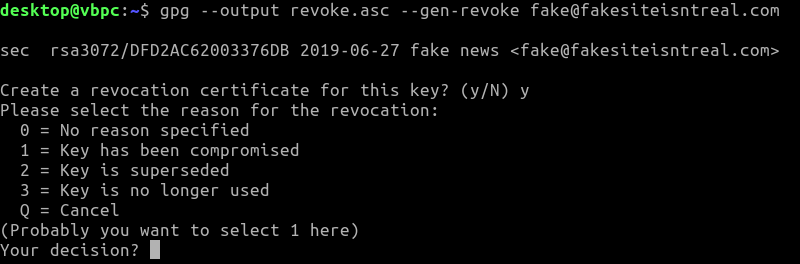
You can do this immediately after you generate your key. It’ll output your certificate to a file – in this case, a file named “revoke.asc.”
Exporting Your Public Key to a File
To share your files or messages with others, you’ll need to share your public key, which means exporting it from your machine. To export your public key to a file, open a terminal and type:
gpg --armor --export [email protected] > key.asc
If you want the key in a readable format (for example, as ASCII in a text file), run the following:
gpg --armor --output key.txt --export [email protected]
You can then open this file using any standard text editor.
Exporting Your Public Key to a Keyserver
You can make your public key easy to share and find by registering it to a keyserver, a public repository of keys. You could use the MIT repository, for instance, which will synchronize your key with other repositories.
First, find your key id by opening a terminal and typing:
gpg --fingerprint
Locate your key and take note of the final eight digits of your key user ID (your user ID fingerprint). For example, B852 085C.
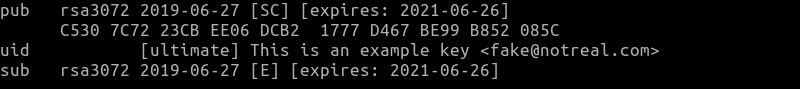
Using your eight-digit user ID and type the following, replacing B852 085C with your own:
gpg --keyserver pgp.mit.edu --send-key B852085C
Your public key will then be registered with the keyserver, where others can then find and import it. Remember, your public key is safe to share. It cannot be used to decrypt files or messages but can be used to encrypt them to send to you, where only you can decrypt them.
Encrypting and Decrypting Files
To encrypt a file, open a terminal and run the following:
gpg --encrypt --recipient '[email protected]' --output encryptedfile.txt.enc originalfile.txt
You could replace the recipient email with your key fingerprint if you’d prefer. Replace the output and input file names with the files you’re encrypting, as well as your output file.
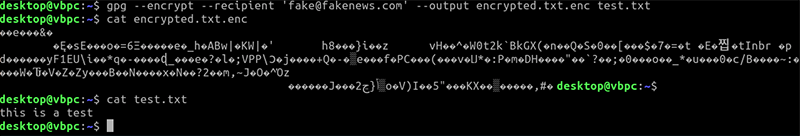
To decrypt the file, run the following command:
gpg --decrypt --output decrypted.txt encryptedfile.txt.enc
You’ll be asked to provide your passphrase to allow access to your private key to be able to decrypt the file. It’ll then output the decrypted contents as the file listed under the --output flag.
Peace of Mind with GPG Encryption
In an ideal world you wouldn’t need to worry about encrypting your sensitive files. The world isn’t ideal, however. If you’re worried about prying eyes, GPG encryption will keep your files, messages and emails safe.
If you’re using Windows, you could encrypt your files with Gpg4win instead. Have your own encryption tips to share? Leave them in the comments below.








